
Sophisticated threat actors are increasingly leveraging the inherent trust associated with established application development platforms to host and deploy deceptive web applications, effectively bypassing conventional email security measures and facilitating the compromise of sensitive credentials, particularly those pertaining to widely-used enterprise accounts like Microsoft 365. This emerging strategy represents a significant evolution in the cyber threat landscape, demonstrating adversaries’ persistent innovation in circumventing defensive mechanisms by exploiting the very infrastructure designed for legitimate business operations.
The foundation of this advanced phishing methodology lies in the strategic abuse of popular no-code application builders, which empower users to create functional web applications without writing traditional programming code. By constructing malicious web applications on these platforms, threat actors capitalize on the inherent legitimacy of the underlying domain infrastructure. When an email security gateway encounters a link pointing to a reputable service provider’s domain, it is significantly less likely to flag it as a potential threat, thereby granting malicious content an unimpeded path to an unsuspecting user’s inbox. This initial bypass is critical, as it allows the subsequent redirection to a credential harvesting site to proceed with a veneer of trustworthiness that traditional phishing attempts often lack.
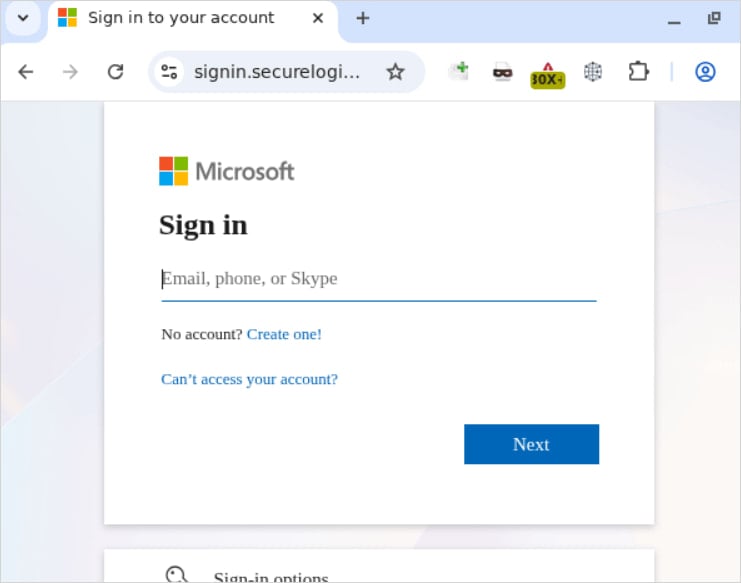
Security researchers have meticulously documented instances where these maliciously crafted applications serve as an initial redirection point, guiding users toward meticulously replicated login portals. These deceptive interfaces often mimic well-known services, such as Microsoft’s ubiquitous authentication pages, sometimes further obscured by intermediate security checks like those provided by Cloudflare. The integration of such legitimate security layers into the attack chain adds another layer of complexity, making it exceedingly difficult for users and automated systems alike to discern the fraudulent nature of the interaction. Any information entered into these counterfeit login forms, particularly usernames and passwords, is instantaneously exfiltrated to the attackers, enabling unauthorized access to a vast array of associated services including email, calendars, cloud storage, and other sensitive data within compromised Microsoft 365 environments.

The platform in question, an AI-powered no-code builder, simplifies application development by allowing users to describe their desired functionality, after which the system automatically generates the requisite backend logic and frontend interface. Applications developed through this method are hosted within the platform’s infrastructure, typically under a subdomain like *.bubble.io. This domain is widely recognized as legitimate and benign, rendering it an unlikely candidate for flagging by most email security solutions or web filtering systems. This trust is precisely what threat actors exploit.
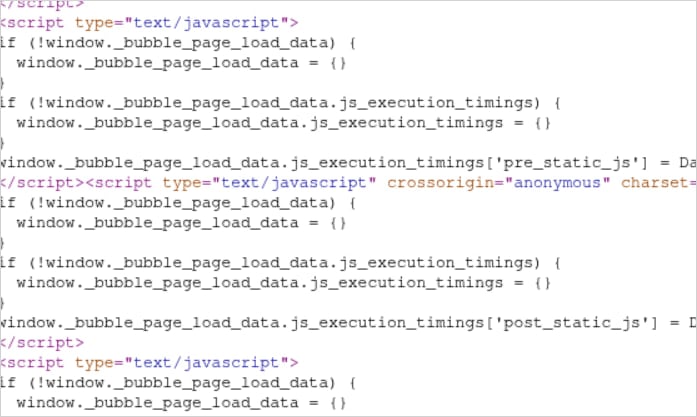
A key technical challenge for security systems in detecting these attacks stems from the intricate architecture of the applications generated by such no-code platforms. These applications often feature extensive, convoluted JavaScript bundles and heavily utilize Shadow DOM (Document Object Model) structures. Shadow DOM is a web standard that allows developers to encapsulate styling and markup within a web component, isolating it from the main document DOM. While beneficial for component reusability and maintainability, this isolation also makes it significantly harder for automated static and dynamic analysis tools to inspect and understand the true intent of the embedded code.
Experts analyzing these complex structures highlight the difficulty even for human specialists to rapidly ascertain the full scope and purpose of the code. The sheer volume and intricate layering of JavaScript, combined with the encapsulated nature of Shadow DOM elements, can obscure redirection scripts or malicious payloads, causing automated web-code analysis algorithms to misinterpret the application as a legitimate, functional website. This inherent complexity provides an effective cloaking mechanism, allowing malicious components to reside undetected within a seemingly benign application. The challenge for security analysts becomes akin to sifting through a densely packed, multi-layered digital environment where malicious elements are intentionally camouflaged amidst legitimate code.
The broader implications of this tactic are profound, signaling a significant shift in the operational methodologies of cybercriminal groups. It is highly probable that this method of leveraging AI-powered app builders for evasion will be rapidly integrated into sophisticated Phishing-as-a-Service (PhaaS) platforms and readily available phishing kits. These commercially offered attack frameworks are continuously evolving, already providing advanced capabilities such as session cookie theft, Adversary-in-the-Middle (AiTM) layers designed to bypass multi-factor authentication (MFA), geo-fencing to target specific regions, anti-analysis tricks to evade security researcher scrutiny, and even AI-generated email content for crafting highly convincing lures. The incorporation of legitimate platform abuse into these offerings will only serve to elevate the stealth and efficacy of future attacks, making detection and prevention increasingly challenging.
The commoditization of these sophisticated attack vectors through PhaaS platforms democratizes access to advanced cyber capabilities, enabling lower-tier cybercriminals to execute highly effective campaigns that would otherwise require significant technical expertise. This trend accelerates the arms race between attackers and defenders, compelling security practitioners to adapt their strategies and technologies at an unprecedented pace. The shift from exploiting vulnerabilities in obscure software to weaponizing the trusted infrastructure of widely adopted development tools represents a formidable challenge that demands a reevaluation of traditional security paradigms.
Organizations must understand that the threat landscape is no longer confined to overtly malicious domains or executables. The erosion of trust in seemingly legitimate URLs presents a critical security vulnerability. This necessitates a multi-faceted approach to cybersecurity that extends beyond perimeter defenses. Enhanced vigilance, both human and technological, is paramount. End-user education must evolve to teach critical scrutiny of URLs, even those that appear to reside on trusted domains, focusing on the specific path and content rather than just the root domain.
From a technical perspective, advanced email security solutions must develop more sophisticated behavioral analysis capabilities, moving beyond simple domain reputation checks to deep content inspection and dynamic analysis of web application behavior. This includes robust sandboxing environments that can execute and observe complex JavaScript and Shadow DOM structures to identify malicious intent, even when obfuscated. Furthermore, the widespread implementation of strong multi-factor authentication, particularly hardware-backed FIDO2 keys, is crucial to mitigate the impact of credential compromise, as even stolen passwords become useless without the second factor.
For organizations leveraging cloud services like Microsoft 365, implementing conditional access policies that restrict access based on user location, device health, and application context can significantly reduce the attack surface. Endpoint detection and response (EDR) solutions are vital for identifying post-compromise activity, as even if initial credential theft occurs, robust EDR can detect anomalous login attempts, data exfiltration, or lateral movement within the network. Proactive threat hunting and continuous monitoring for indicators of compromise (IOCs) are also essential components of a robust defense strategy.
For platform providers like Bubble, the responsibility to safeguard their infrastructure from abuse is paramount. This includes implementing more rigorous content scanning and behavioral analysis of applications deployed on their platform, using AI/ML-driven anomaly detection to identify suspicious development patterns or application functionalities. Establishing clear and enforceable abuse policies, coupled with rapid response mechanisms for reported instances of misuse, is critical to maintaining the integrity and trustworthiness of their services. A collaborative approach between security researchers, platform providers, and the wider cybersecurity community is indispensable in addressing this evolving threat.
In conclusion, the exploitation of legitimate no-code AI app builders for sophisticated phishing campaigns marks a significant escalation in the ongoing cyber conflict. By weaponizing trusted platforms and leveraging complex technical evasion techniques, threat actors are effectively bypassing established security controls and increasing the success rate of credential harvesting operations. As cybercriminals continue to innovate, adapting their tactics to exploit the very tools designed for productivity and efficiency, a dynamic and adaptive defense posture, combining advanced technology with comprehensive user education and stringent security protocols, remains the most effective strategy to safeguard digital assets in this increasingly complex threat landscape. The future of cybersecurity will heavily rely on anticipating such novel abuses of legitimate infrastructure and developing proactive countermeasures.






