A sophisticated and evolving supply-chain campaign, dubbed GlassWorm, has resurfaced with a highly coordinated assault, compromising more than 400 distinct components across critical developer platforms including GitHub, npm, and the Visual Studio Code/OpenVSX extension registries. This latest wave represents a significant escalation in both scope and complexity, targeting the foundational elements of modern software development.
The digital landscape, particularly within open-source ecosystems, has become a fertile ground for malicious actors seeking to exploit trust and interconnectedness. Supply-chain attacks, where adversaries compromise legitimate software components or distribution channels to spread malware, represent one of the most insidious threats facing contemporary software development. Unlike direct attacks on end-users, these campaigns leverage the integrity of trusted vendors and widely used libraries, allowing malicious code to propagate deep within the software supply chain before detection. The GlassWorm campaign epitomizes this threat model, demonstrating a persistent and adaptive strategy to infiltrate developer environments and exfiltrate sensitive data.
Initial intelligence regarding the GlassWorm operation emerged in October of the preceding year, revealing a cunning methodology that leveraged "invisible" Unicode characters to embed and conceal malicious code. This initial phase primarily focused on harvesting cryptocurrency wallet data and developer credentials, setting a precedent for the campaign’s financially motivated objectives. The threat actor, displaying remarkable agility, swiftly expanded their reach through multiple subsequent waves. This included targeting Microsoft’s official Visual Studio Code marketplace and the OpenVSX registry, a vital resource for various integrated development environments (IDEs) not directly supported by Microsoft. These expansions highlighted the attacker’s intent to broaden their victim pool beyond niche targets, aiming for the core of the developer community.

A notable diversification in the campaign’s tactics was the introduction of macOS-specific payloads. This shift involved distributing trojanized clients for popular hardware cryptocurrency wallets such as Trezor and Ledger, indicating a direct assault on the digital assets of developers. Subsequently, the threat actors adapted to target macOS users specifically through compromised OpenVSX extensions, further illustrating their comprehensive approach to platform targeting and payload delivery. This continuous evolution from basic obfuscation to platform-specific exploits underscores a well-resourced and strategic adversary.
The latest iteration of the GlassWorm campaign, however, dwarfs its predecessors in sheer scale and intricacy. Multiple security research entities, including Aikido, Socket, Step Security, and the collaborative OpenSourceMalware community, have collectively identified a staggering 433 compromised components within the current month alone. This collaborative effort has been instrumental in piecing together the full scope of the attack, revealing a sophisticated network of interconnected compromises.
Compelling evidence points to a singular, highly organized threat actor orchestrating the GlassWorm campaigns across these disparate open-source repositories. This attribution is supported by several key forensic indicators: the consistent use of the same Solana blockchain address for command-and-control (C2) activities, the deployment of identical or functionally analogous payloads, and the reliance on shared infrastructure for hosting and communication. The choice of Solana, a decentralized and high-performance blockchain, for C2 operations is particularly noteworthy. It provides the attackers with a resilient and difficult-to-trace communication channel, complicating efforts by security researchers and law enforcement to dismantle their infrastructure. Traditional C2 servers are often centralized and can be taken down through coordinated efforts, but blockchain-based C2s offer a level of resilience and anonymity that is increasingly attractive to advanced persistent threats.
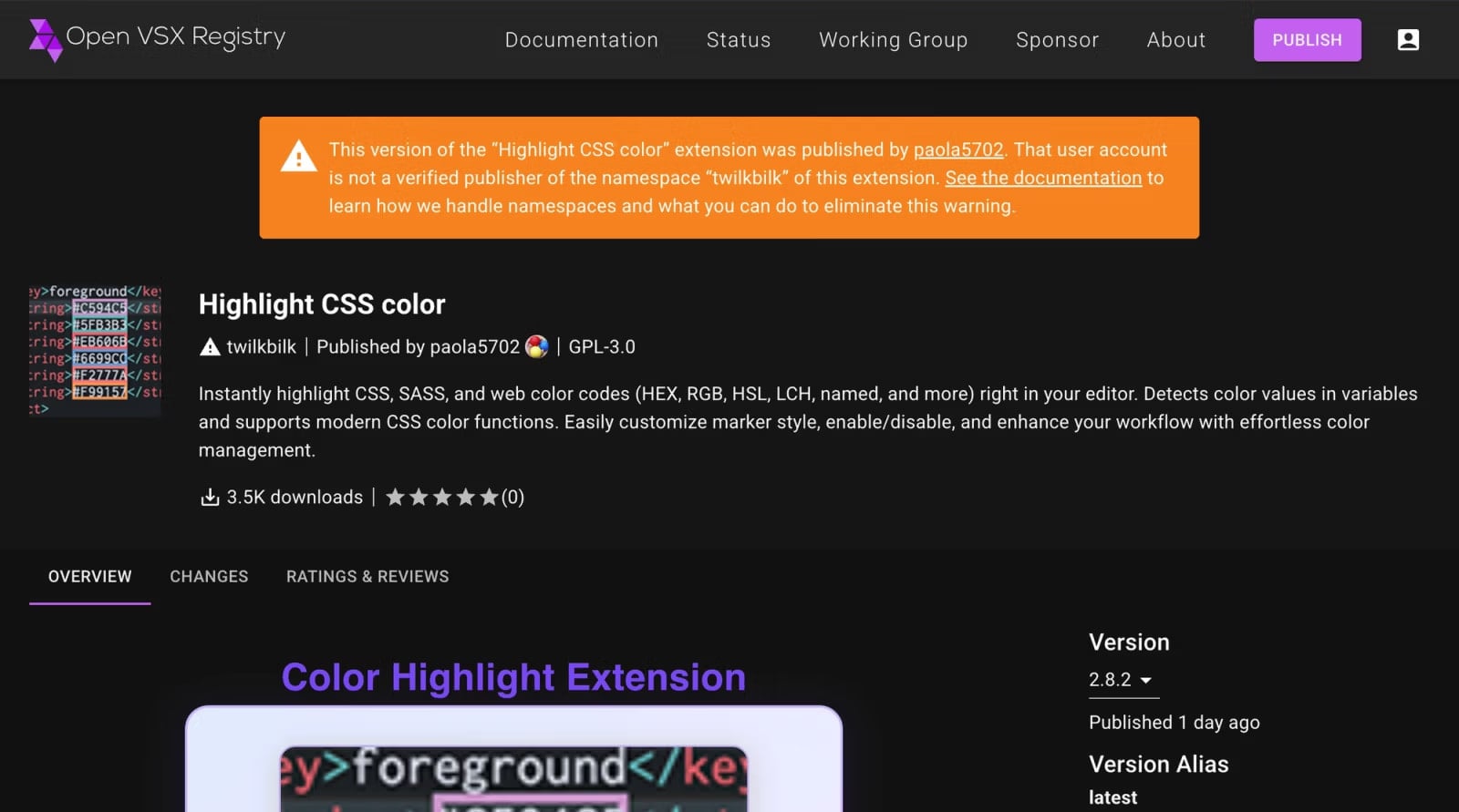
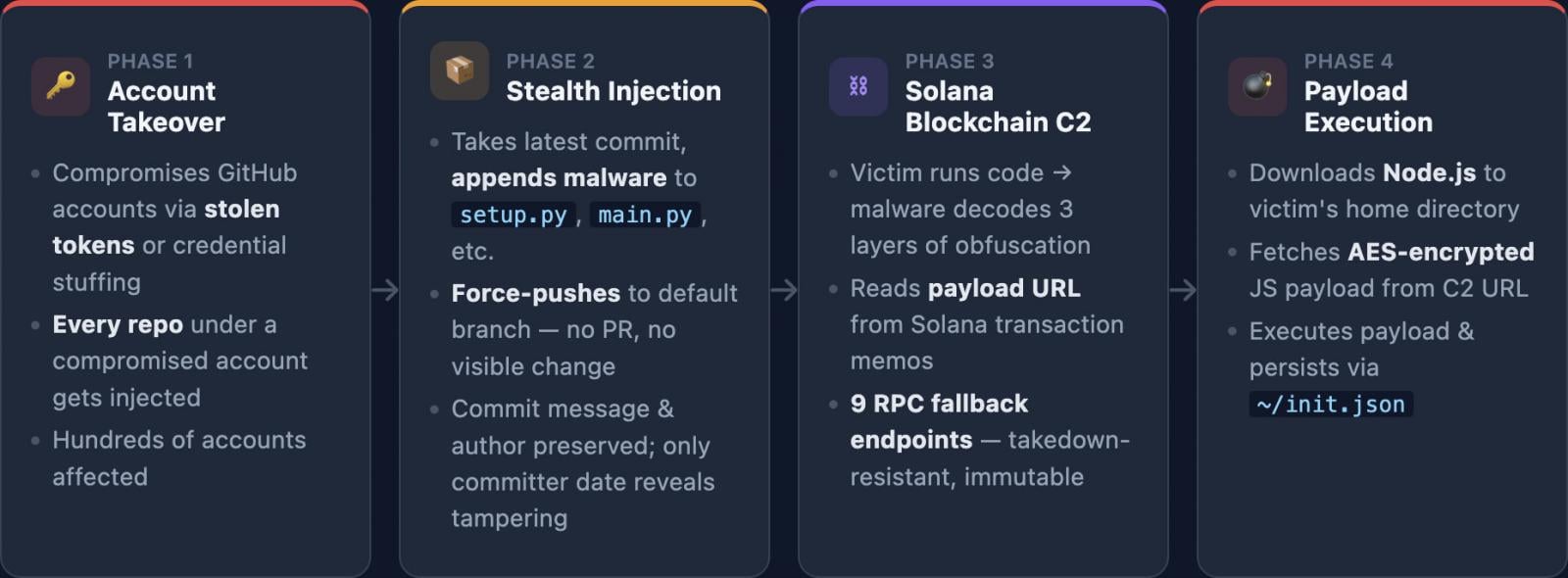
The attack chain for this expanded GlassWorm campaign initiates with the compromise of developer accounts on GitHub. This typically involves unauthorized access to legitimate user accounts, which is then leveraged to "force-push" malicious commits into existing repositories. Force-pushing is a Git command that overwrites commit history, allowing attackers to inject their malicious code while potentially erasing traces of their activity or overwriting legitimate code. This method is particularly dangerous as it exploits the trust associated with existing, legitimate projects and authors. Once the malicious code is integrated into GitHub repositories, it is subsequently published as tainted packages or extensions on platforms like npm and VSCode/OpenVSX. The obfuscation techniques, primarily the use of invisible Unicode characters, are employed at this stage to evade automated detection mechanisms and manual code reviews, ensuring the malicious components appear innocuous upon initial inspection.
A critical aspect of the GlassWorm malware’s operational methodology involves its C2 communication. Across all compromised platforms, the malicious code is engineered to query the Solana blockchain approximately every five seconds, searching for new instructions. These instructions are cleverly embedded as "memos" within Solana transactions, a feature typically used for small notes or messages. This innovative C2 channel allows the threat actor to dynamically update the malware’s behavior, most frequently observed as updates to the payload download URL. Between November 27, 2025, and March 13, 2026, a period spanning just over three months, researchers observed 50 such transactions, underscoring the active management and adaptability of the campaign. Upon receiving new instructions, the malware proceeds to download a Node.js runtime and execute a JavaScript-based information stealer.
The information stealer component is highly effective and designed to target a comprehensive array of sensitive data from compromised developer environments. This includes, but is not limited to, cryptocurrency wallet data, various credentials (such as those for cloud services, internal systems, and code repositories), access tokens (which can grant unauthorized access to APIs and internal networks), SSH keys (critical for secure remote access), and a broad spectrum of developer environment data. The exfiltration of such data poses a severe risk, potentially leading to widespread organizational compromise, intellectual property theft, and further supply-chain attacks if the stolen credentials are used to access other development infrastructure.
While definitive attribution remains challenging in the cyber realm, analysis of code comments within the GlassWorm malware has revealed indications that the operation is orchestrated by Russia-speaking threat actors. Furthermore, the malware incorporates a mechanism to skip execution if a Russian locale is detected on the compromised system. While these clues offer strong suggestions, security experts caution that such indicators can be easily faked or used as false flags to mislead investigators, thus requiring further corroboration for confident attribution. The geopolitical context often influences the motivations and targets of such groups, but technical evidence must always be scrutinized meticulously.
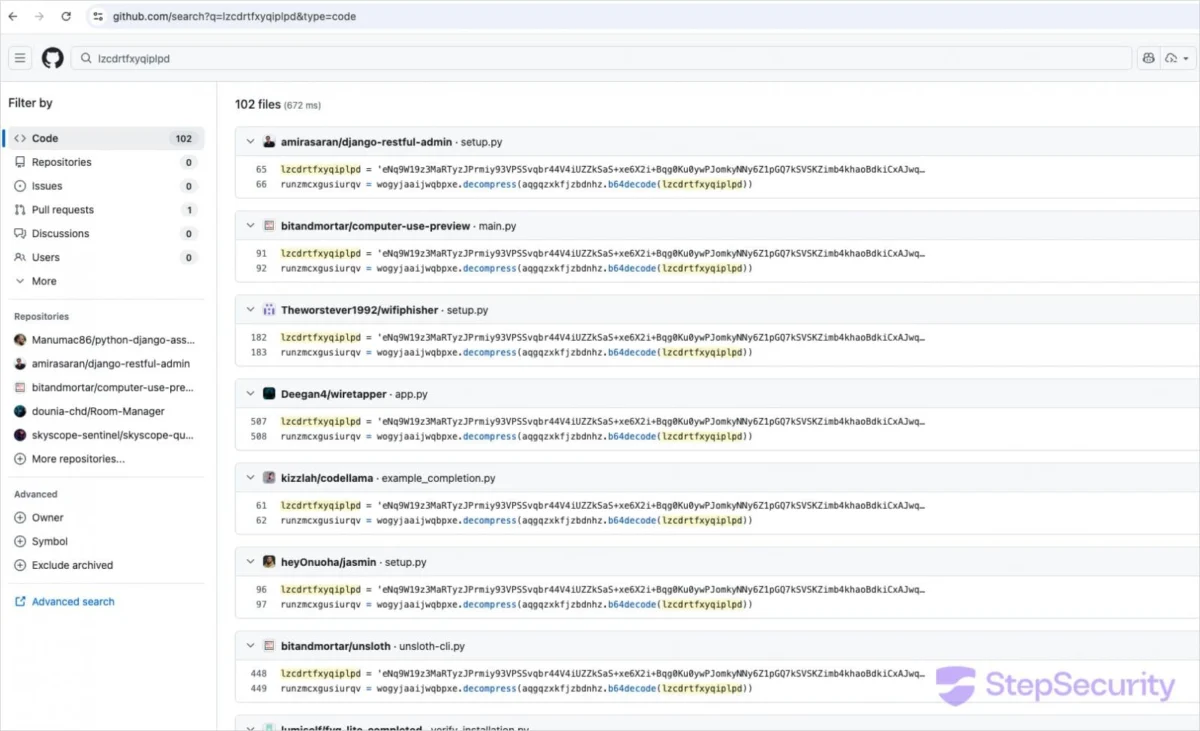
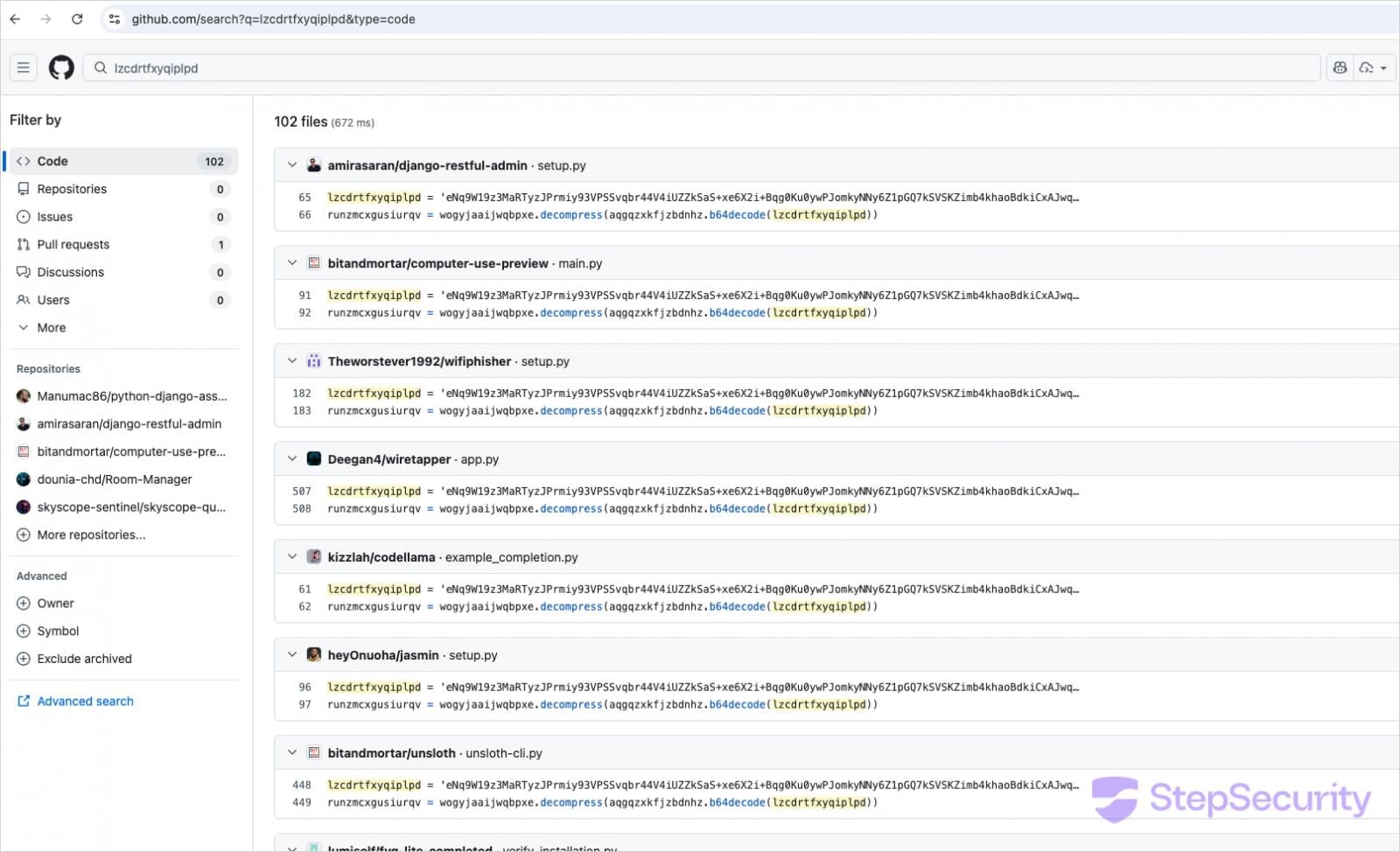
Given the pervasive nature of this threat, developers are strongly advised to implement robust security measures and diligently scrutinize their development environments for signs of compromise. Step Security has provided specific Indicators of Compromise (IoCs) to aid in detection. Developers who install Python packages directly from GitHub or run cloned repositories should actively search their codebase for the marker variable lzcdrtfxyqiplpd, which serves as a telltale sign of GlassWorm infection.
Beyond code-level indicators, developers should inspect their systems for the presence of the ~/init.json file, which the malware utilizes to establish persistence, ensuring it re-executes across system reboots. Furthermore, the unexpected presence of Node.js installations within the home directory (e.g., ~/node-v22*) should raise immediate red flags, as the malware downloads its own runtime. Suspicious i.js files in recently cloned projects also warrant immediate investigation. A crucial defensive practice involves a thorough review of Git commit histories for anomalies, particularly looking for instances where the committer date is significantly newer than the original author date, indicating a potential force-push by an unauthorized party.
The implications of the GlassWorm campaign extend far beyond individual developer workstations. A compromised developer machine can serve as a beachhead for attackers to infiltrate an organization’s entire development pipeline, access sensitive intellectual property, or even inject malicious code into production systems. This highlights the critical need for comprehensive supply-chain security strategies that encompass everything from developer workstation hygiene to rigorous code review processes and automated security scanning. Platform providers like GitHub, npm, and the various VSCode registries also bear a significant responsibility to enhance their detection capabilities, implement stricter account security measures, and expedite the takedown of malicious packages.
Looking ahead, the GlassWorm campaign exemplifies the ongoing arms race between cybercriminals and the cybersecurity community. The continuous evolution of attack techniques, from stealthy obfuscation to resilient C2 infrastructure and multi-platform targeting, suggests that supply-chain attacks will remain a prominent threat. The increasing value of developer credentials and access within the digital economy ensures that such campaigns will persist and grow in sophistication. Collaborative intelligence sharing among security researchers, platform providers, and the wider developer community will be paramount in mitigating these evolving threats and safeguarding the integrity of the global software supply chain. Developers must cultivate a culture of security vigilance, adopting multi-factor authentication, carefully vetting external dependencies, and regularly updating their security practices to stay ahead of determined adversaries like GlassWorm.