The United States Federal Bureau of Investigation (FBI) has issued a significant advisory to network defense professionals, underscoring a persistent and evolving threat from Iranian state-affiliated cyber actors. These groups, operating under the purview of Iran’s Ministry of Intelligence and Security (MOIS), are systematically leveraging the Telegram messaging platform as a command-and-control (C2) mechanism within sophisticated malware operations. These campaigns are primarily directed at individuals and entities critical of the Iranian government, including journalists, political dissidents, and various opposition factions globally, signaling an aggressive posture in the digital domain.
This recent flash alert from the FBI highlights the strategic adaptation of established communication channels for clandestine operations. The use of Telegram, a platform lauded for its end-to-end encryption and widespread global adoption, provides a seemingly innocuous facade for orchestrating malicious activities. The bureau’s assessment explicitly links these ongoing cyber incursions to several prominent Iranian threat groups: the pro-Palestinian Handala hacktivist collective (also identified as Handala Hack Team, Hatef, and Hamsa) and the state-sponsored Homeland Justice organization, which maintains direct ties to Iran’s Islamic Revolutionary Guard Corps (IRGC). These entities are employing social engineering tactics to deploy Windows-specific malware, facilitating the illicit exfiltration of sensitive data, including screenshots and files, from compromised systems.
The Modus Operandi: Exploiting Trust and Technology
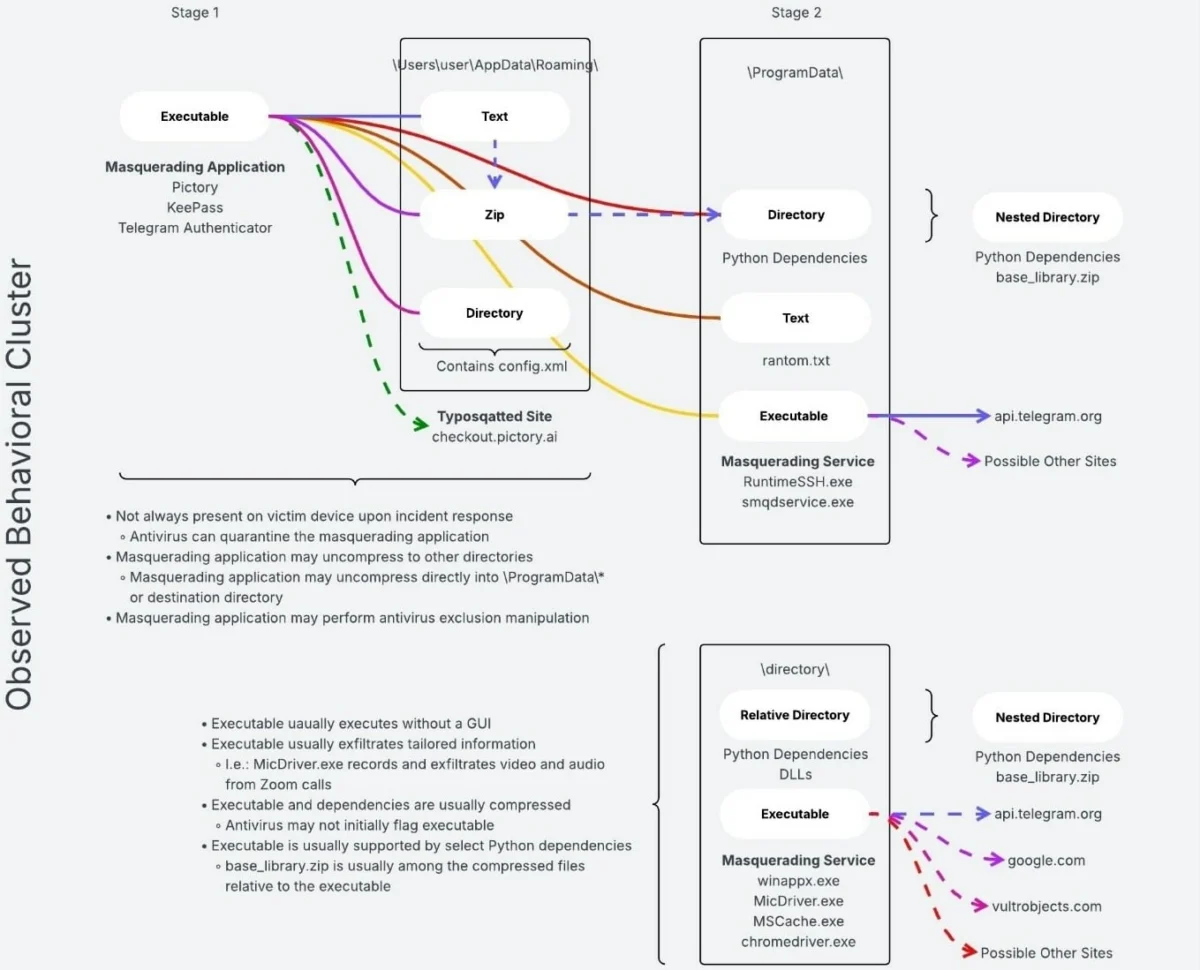
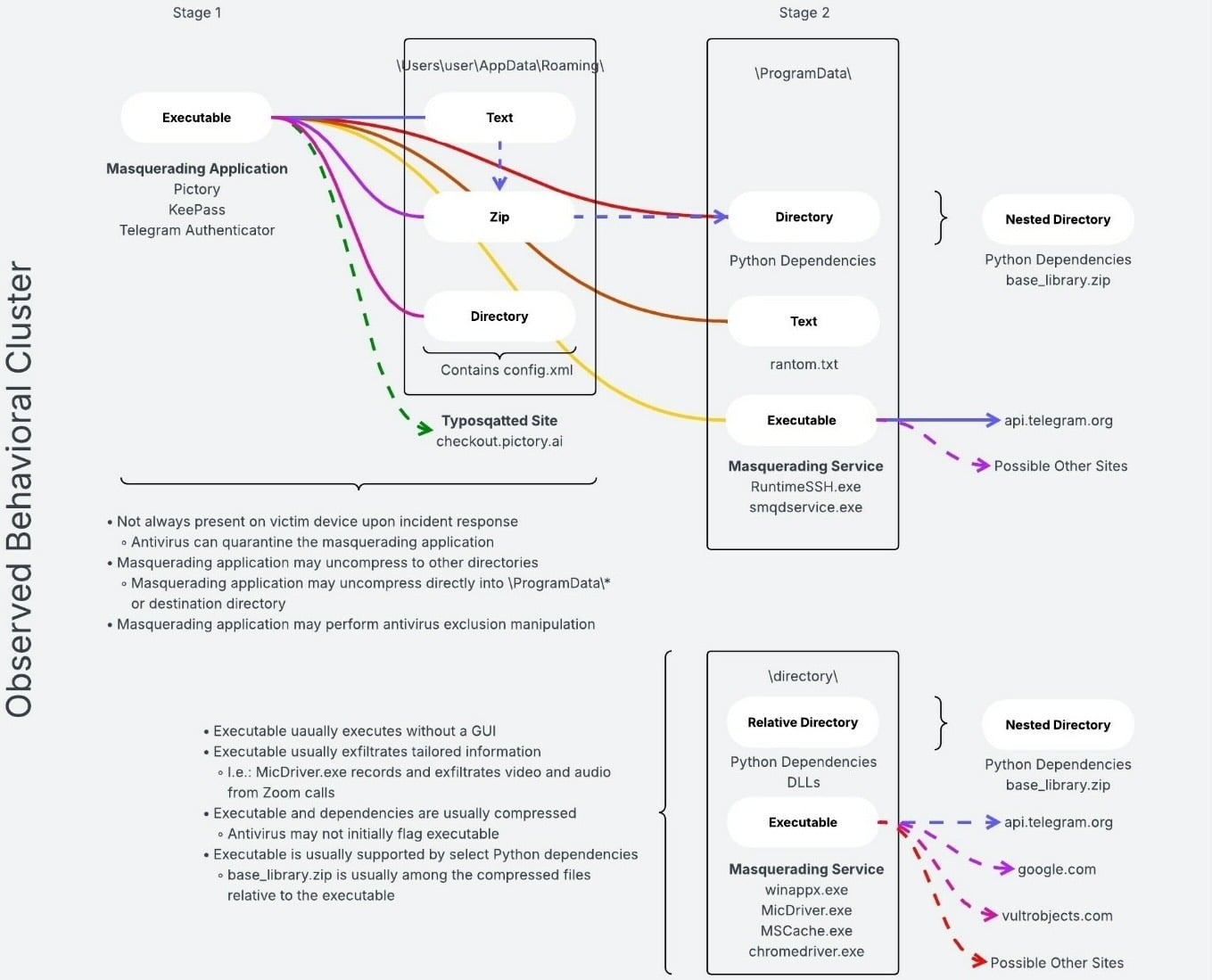
The operational methodology employed by these Iranian groups is characterized by a blend of social engineering and technical sophistication. Attackers initiate contact with targets through various pretexts, often leveraging highly personalized lures designed to exploit trust or curiosity. Once a target is enticed to interact with a malicious link or attachment, a Windows-based malware payload is delivered. This malware then establishes a covert communication channel with its operators, utilizing Telegram’s infrastructure as a seemingly benign conduit for C2 communications. This method allows the threat actors to issue commands, receive status updates, and orchestrate data exfiltration without immediately raising suspicion from traditional network monitoring tools that might flag connections to known malicious domains.
The choice of Telegram as a C2 channel offers several advantages for state-sponsored actors. Its popularity ensures a large user base, providing ample cover for malicious traffic. The platform’s robust encryption protocols, while beneficial for legitimate users seeking privacy, can also inadvertently obscure the activities of malicious actors from external scrutiny, making detection and analysis more challenging for defenders. Furthermore, the ability to operate within public or private Telegram channels allows for flexible C2 topologies, potentially distributing command responsibilities and making infrastructure takedowns more complex.
Targeting Dissidence: A Strategic Imperative
The explicit targeting of journalists critical of the Iranian government, Iranian dissidents, and various oppositional groups worldwide is not incidental. It aligns with a broader strategic imperative of the Iranian regime to suppress dissent, monitor perceived threats, and gather intelligence on activities that could challenge its authority. By compromising the digital assets of these individuals, the MOIS and IRGC-linked groups can achieve several objectives:
- Intelligence Collection: Gaining access to communications, documents, and networks of dissidents provides invaluable intelligence on their plans, contacts, and vulnerabilities.
- Disinformation and Disruption: Stolen information can be weaponized for disinformation campaigns, sowing discord, or discrediting opposition figures. Access to accounts can also enable direct disruption of organizational activities.
- Intimidation: The very act of being targeted, regardless of data exfiltration success, serves as a powerful deterrent, fostering an environment of fear and self-censorship among those who might otherwise speak out.
- Reputational Harm: Leaking sensitive or fabricated information can severely damage the credibility and public standing of targeted individuals and organizations.
The FBI’s alert specifically noted that this malware activity has "resulted in intelligence collection, data leaks, and reputational harm." This confirms the multi-faceted impact of these operations, extending beyond mere data theft to encompass broader psychological and strategic objectives.

Geopolitical Context and Escalation
The FBI’s decision to highlight this specific MOIS cyber activity is directly attributed to the "elevated geopolitical climate of the Middle East and current conflict." This contextualization is crucial. Regional tensions, particularly those involving Iran and its proxies, frequently manifest in increased cyber activity. Cyber operations serve as a cost-effective and deniable means of projecting power, gathering intelligence, and exerting influence without necessarily crossing thresholds that would provoke direct military confrontation.
Iran has a well-documented history of employing cyber tools as a component of its national security strategy. Its state-sponsored groups, often operating with a blend of hacktivist fervor and direct government directives, have been implicated in a range of activities from espionage to destructive attacks against critical infrastructure. The groups mentioned – Handala and Homeland Justice – exemplify this hybrid model, blending overt political messaging with sophisticated cyber capabilities. Handala, known for its pro-Palestinian stance, often aligns its cyber actions with broader Iranian foreign policy objectives, while Homeland Justice is a more direct instrument of the IRGC, focusing on strategic targets.
Law Enforcement Countermeasures and Their Efficacy
The FBI’s warning arrives on the heels of significant law enforcement action. Just a day prior to the flash alert, the bureau announced the seizure of four domains directly associated with these Iranian threat groups: handala-redwanted[.]to, handala-hack[.]to, justicehomeland[.]org, and karmabelow80[.]org. These domains served as critical infrastructure for Handala, Homeland Justice, and a third group identified as Karma Below, facilitating their attacks and acting as platforms for leaking stolen data.
Domain seizures represent a tangible and often effective tactic in disrupting cyber campaigns. By taking down these critical assets, law enforcement agencies can immediately sever C2 channels, prevent further data exfiltration, and deny the groups their preferred platforms for publicizing stolen information. This action forces the threat actors to expend resources on re-establishing infrastructure, potentially delaying future operations and increasing their operational costs and risks. However, such measures are often temporary, as determined state-sponsored groups are adept at reconstituting their infrastructure under new domains or using alternative communication channels. The continuous cat-and-mouse game between law enforcement and state-sponsored actors underscores the persistent nature of this threat.
A Broader Landscape of State-Sponsored Cyber Threats
The Iranian activity highlighted by the FBI is not an isolated phenomenon but rather indicative of a broader trend of state-sponsored cyber espionage and disruption. The FBI’s recent alerts also include warnings about Russian intelligence-linked threat actors targeting users of secure messaging applications like Signal and WhatsApp through sophisticated phishing campaigns. These Russian operations, which have reportedly compromised thousands of accounts, specifically target individuals deemed to be of "high intelligence value," including current and former U.S. government officials, military personnel, political figures, and journalists.
The commonality across these different state-sponsored campaigns – whether Iranian or Russian – is the strategic targeting of influential individuals and the exploitation of popular communication platforms. This suggests a shared understanding among advanced persistent threat (APT) groups regarding the value of human intelligence and the effectiveness of social engineering combined with readily available, encrypted communication tools. While the specific geopolitical motivations and operational nuances may differ between Iranian and Russian actors, the overarching goal of intelligence collection and influence projection through cyber means remains consistent.
Implications for Cybersecurity and Mitigation Strategies
The FBI’s detailed alert serves as a critical call to action for network defenders and individuals at risk. The implications are far-reaching:
- Elevated Threat Landscape: Organizations and individuals associated with journalism, human rights, government, or critical infrastructure must recognize that they are potential targets in an increasingly volatile geopolitical cyber environment.
- Evolving Attack Vectors: The reliance on social engineering and legitimate platforms like Telegram means that traditional perimeter defenses alone are insufficient. User education and awareness are paramount.
- Data Sovereignty and Privacy: The exfiltration of screenshots and files highlights the constant threat to sensitive information, necessitating robust data protection strategies.
To mitigate the risk of compromise, the FBI and cybersecurity experts recommend a multi-layered defense strategy:
- Employee Training: Conduct regular and comprehensive training for all personnel, especially those in high-risk roles, on identifying social engineering tactics, phishing attempts, and suspicious communications. Emphasize the dangers of clicking on unsolicited links or opening unexpected attachments, even from seemingly legitimate sources.
- Strong Authentication: Implement multi-factor authentication (MFA) across all accounts and services, particularly for email, social media, and internal network access. This significantly reduces the impact of compromised credentials.
- Endpoint Security: Deploy and maintain up-to-date endpoint detection and response (EDR) solutions on all devices. Configure them to monitor for unusual activity, suspicious process execution, and unauthorized data transfers.
- Network Segmentation: Segment networks to limit the lateral movement of attackers in the event of a breach. Implement strict access controls based on the principle of least privilege.
- Regular Backups: Maintain offline, encrypted backups of all critical data to ensure business continuity and data recovery capabilities following a ransomware or destructive attack.
- Software Updates: Ensure all operating systems, applications, and security software are regularly patched and updated to remediate known vulnerabilities that attackers frequently exploit.
- Monitoring and Logging: Implement robust logging and monitoring solutions to detect suspicious activity on networks and endpoints. Analyze logs for indicators of compromise (IoCs) provided by intelligence agencies.
- Incident Response Plan: Develop and regularly test a comprehensive incident response plan to ensure a swift and effective reaction to any cyber incident.
- Threat Intelligence Integration: Integrate threat intelligence feeds, such as those provided by the FBI, into security operations to proactively identify and block known malicious indicators.
Future Outlook: A Persistent and Adaptive Threat
The ongoing cyber activities attributed to Iranian state-sponsored groups, coupled with similar campaigns from other nation-states, indicate a future where digital espionage and influence operations remain a core component of geopolitical strategy. These actors will continue to adapt their tactics, techniques, and procedures (TTPs) in response to defensive measures and law enforcement actions. While domain seizures offer temporary disruption, the underlying capabilities and motivations of these groups persist.
The reliance on encrypted messaging platforms like Telegram is likely to continue, as these platforms offer a degree of anonymity and a ready-made infrastructure that is difficult to monitor and dismantle. Defenders must therefore focus on a holistic approach that combines technical safeguards with enhanced human vigilance. The challenge for the global cybersecurity community will be to foster greater international collaboration in threat intelligence sharing and coordinated defensive actions, while simultaneously upholding the principles of privacy and open communication that platforms like Telegram aim to provide. The FBI’s alert serves as a stark reminder of the continuous need for vigilance and adaptation in the face of an ever-evolving state-sponsored cyber threat landscape.