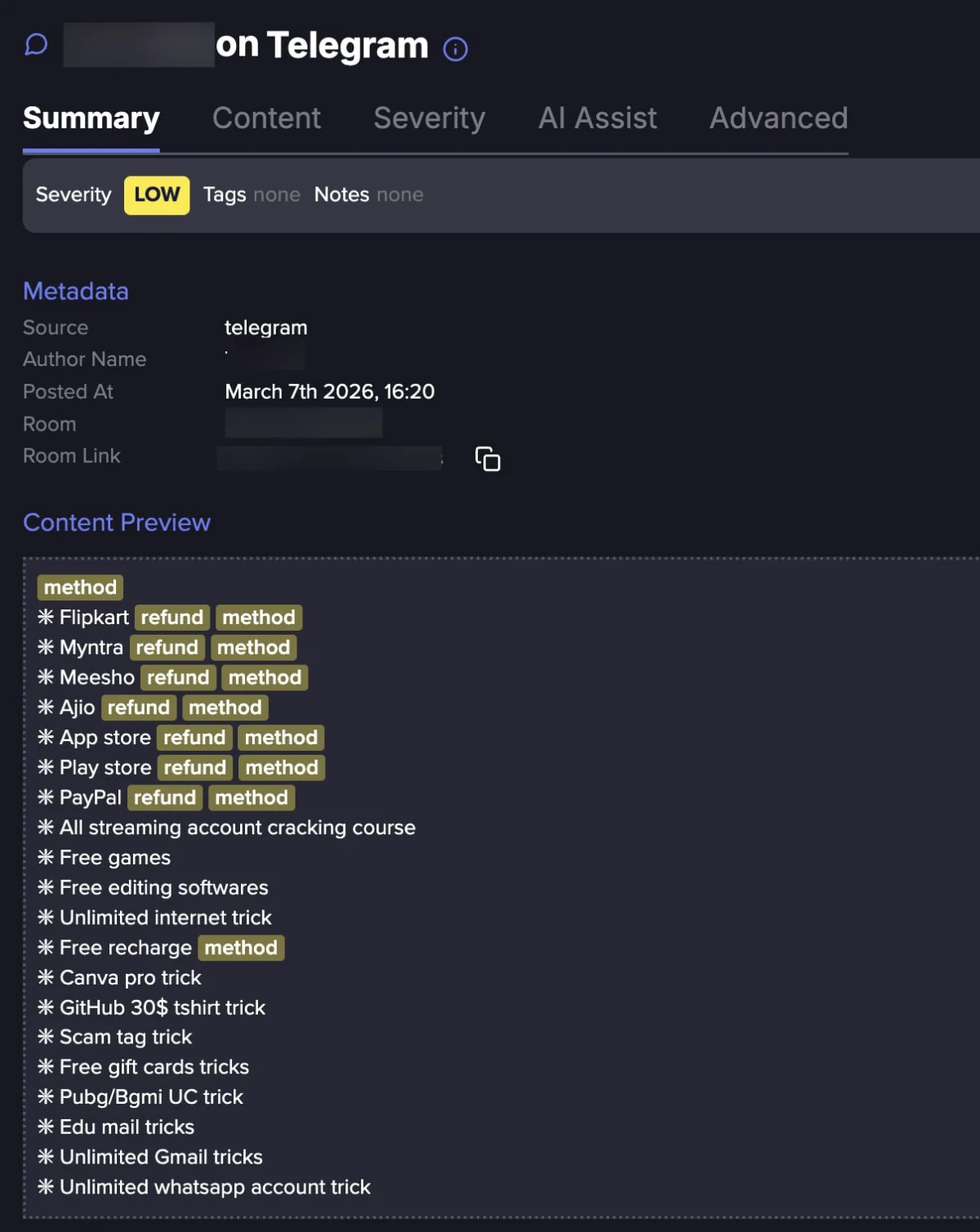
Aura, a prominent purveyor of digital identity protection and online security services, has officially disclosed a significant data breach stemming from a sophisticated voice phishing incident that compromised an internal employee, leading to the unauthorized access and subsequent exposure of an extensive database comprising approximately 900,000 marketing contacts and various proprietary corporate files. This incident underscores the persistent efficacy of social engineering tactics and the complex cybersecurity challenges inherent in managing legacy data from corporate acquisitions, even for organizations specifically tasked with safeguarding digital identities.
The breach was initiated through a targeted voice phishing (vishing) attack, a sophisticated form of social engineering where attackers impersonate trusted entities or individuals over the phone to manipulate victims into divulging sensitive information or performing actions that compromise security. In this instance, an Aura employee was reportedly targeted, leading to unauthorized access to critical systems. Vishing attacks are particularly insidious as they leverage human psychology, often exploiting urgency, authority, or helpfulness to bypass technical security controls that might thwart other attack vectors. The success of such an attack against an organization specializing in digital safety highlights the universal vulnerability of the human element in even the most robust security architectures.
The compromised information is extensive, encompassing full names, email addresses, residential addresses, and telephone numbers. Furthermore, subsequent analysis by independent security researchers revealed the exposure of customer service comments and Internet Protocol (IP) addresses, adding layers of context that could be exploited by malicious actors. While Aura has emphasized that highly sensitive data such as Social Security Numbers (SSNs), account passwords, and financial information were not compromised, the exposed data types are far from innocuous. This combination of personally identifiable information (PII) creates a rich dataset for targeted phishing campaigns, advanced social engineering schemes, and potentially even synthetic identity fraud, where fragments of real identities are combined with fabricated information to create new, fraudulent identities. The availability of customer service comments could provide threat actors with insights into individuals’ past issues or concerns, enabling them to craft highly convincing and personalized attacks.

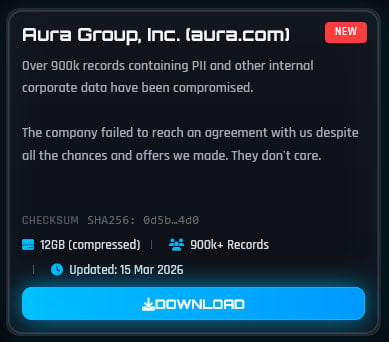
The responsibility for this breach has been claimed by ShinyHunters, a notorious cyber extortion group with a documented history of breaching companies and leaking stolen data on underground forums and dedicated data extortion sites. The group asserted that they exfiltrated approximately 12 gigabytes of files containing not only customer PII but also a significant volume of corporate operational data. ShinyHunters publicly released the stolen information, alleging that Aura "failed to reach an agreement" despite negotiation attempts, a common tactic employed by data extortionists to pressure victims into paying a ransom. The public release of data serves as both a punitive measure for non-payment and a means for the threat group to maintain its reputation within the cybercriminal ecosystem, signaling their capability and resolve to prospective victims.
A notable discrepancy emerged between Aura’s initial reporting of approximately 35,000 affected current and former customers and the significantly larger figure of over 900,000 records identified by independent breach notification services. Aura clarified that the larger dataset originated from a marketing tool utilized by a company it acquired in 2021. This explanation brings into sharp focus the complex cybersecurity challenges associated with mergers and acquisitions (M&A). When companies integrate, they often inherit legacy IT systems, databases, and third-party tools that may not adhere to the acquiring company’s more stringent security standards. This "supply chain" risk, where vulnerabilities in an acquired entity or third-party vendor become entry points for attackers, is a growing concern across all industries. The continued retention of extensive marketing contact lists, even years after an acquisition, also raises questions about data minimization principles and data lifecycle management, which are fundamental tenets of modern data protection regulations such as GDPR and CCPA.
In response to the incident, Aura has initiated a comprehensive internal review, collaborating with external cybersecurity experts to thoroughly investigate the extent and nature of the compromise. The company has also confirmed that it has engaged with law enforcement authorities, indicating the severity of the incident and its commitment to legal and regulatory compliance. Aura has stated its intention to send personalized notifications to all affected individuals in the near future, a critical step in enabling them to take proactive measures to protect themselves against potential follow-on attacks. However, the company has declined to comment publicly on ShinyHunters’ specific claims regarding the nature of the corporate data stolen or any alleged compromise of its Okta Single Sign-On (SSO) system, maintaining a focus on the validated aspects of the breach.
The implications of this breach for Aura are multifaceted and significant. As a company whose core business revolves around providing digital safety and identity protection, a data breach of this scale inherently erodes customer trust and can inflict substantial reputational damage. Customers rely on such providers precisely to prevent the very type of exposure that has occurred. The incident may also lead to increased scrutiny from regulatory bodies, potentially resulting in fines or other punitive actions depending on the geographical reach of the affected individuals and the specific data protection laws applicable. Operationally, Aura faces considerable costs associated with incident response, forensic investigations, enhanced security measures, and potential legal expenses.
For the nearly one million affected individuals, the exposure of their PII heightens their vulnerability to a range of malicious activities. While SSNs and financial details were not exposed, the combination of names, email addresses, physical addresses, and phone numbers is sufficient for highly effective spear-phishing campaigns, SMS phishing (smishing), and vishing attacks. These sophisticated attacks can trick individuals into divulging login credentials for other online services, financial information, or even enabling direct access to their devices through malware installation. The presence of customer service comments could allow threat actors to craft narratives that appear highly credible, leveraging prior interactions to build rapport and trust with victims. The long-term risk extends to potential identity profiling, where criminals aggregate exposed data with other publicly available information to build comprehensive dossiers on individuals for future exploitation.
This incident serves as a stark reminder for all organizations, irrespective of their industry or security posture, of the perpetual and evolving nature of cyber threats. It underscores several critical lessons:
- The Enduring Power of Social Engineering: Despite advanced technical defenses, the human element remains a primary vulnerability. Continuous and sophisticated security awareness training, particularly against vishing and phishing, is paramount for all employees.
- M&A Cybersecurity Integration: Thorough cybersecurity due diligence and meticulous integration planning are essential during corporate acquisitions to prevent inherited vulnerabilities from becoming critical attack vectors. Legacy systems and data from acquired entities must be rigorously assessed and secured.
- Data Minimization and Retention: Organizations must adopt strict data minimization policies, collecting only necessary data and retaining it only for as long as legally and operationally required. Regular auditing and secure purging of old or unnecessary data can significantly reduce the attack surface.
- Third-Party Risk Management: Any external tool or service, especially marketing platforms, represents a potential entry point. Robust vendor risk management programs are crucial to ensure that third-party providers meet stringent security standards.
- Robust Incident Response: A well-defined and frequently tested incident response plan is vital for rapid detection, containment, eradication, recovery, and communication following a breach.
Looking ahead, Aura will need to demonstrate a clear and sustained commitment to enhancing its security protocols, particularly those related to employee training and the management of data from acquired assets. The company’s ability to rebuild trust will depend heavily on its transparency, the efficacy of its remediation efforts, and its ongoing dedication to safeguarding customer data. This incident reinforces the broader industry trend that even leading digital security providers are not immune to sophisticated attacks, emphasizing the continuous need for vigilance, adaptive security strategies, and a holistic approach to risk management that addresses both technological and human vulnerabilities. The digital landscape remains a battleground where proactive defense and resilient recovery mechanisms are not just best practices, but existential necessities.