Malicious actors are increasingly leveraging specialized internet infrastructure, specifically the .arpa top-level domain (TLD) and IPv6 reverse DNS mechanisms, to orchestrate advanced phishing campaigns that effectively bypass conventional email security protocols and domain reputation checks. This novel approach exploits foundational elements of the Domain Name System (DNS) that are typically reserved for network operations, transforming them into stealthy conduits for delivering deceptive content.
The Foundational Role of .arpa in Internet Infrastructure
To comprehend the sophistication of this attack vector, it is essential to understand the intended purpose of the .arpa domain. Unlike commercial or country-code TLDs such as .com or .org, .arpa stands as a unique, special-use domain explicitly designated for critical internet infrastructure functions. Its name is a historical nod to ARPANET, the precursor to the modern internet, underscoring its deep-rooted role in network architecture. Primarily, .arpa facilitates reverse DNS lookups, a crucial process that enables systems to translate an IP address back into its associated hostname. This functionality is vital for various internet operations, including mail server verification (a common spam prevention technique), network logging, and diagnostic tools.
Within the .arpa hierarchy, two specific subdomains are central to reverse DNS: in-addr.arpa for IPv4 addresses and ip6.arpa for IPv6 addresses. When a system performs a reverse DNS lookup, it constructs a specialized DNS query. For IPv4, the IP address is reversed, octet by octet, and appended to in-addr.arpa. For example, an IP address like 192.0.2.1 would be queried as 1.2.0.192.in-addr.arpa. Similarly, for IPv6, the 128-bit address is broken down into 4-bit nibbles, reversed, and each nibble is separated by a dot, then appended to ip6.arpa. This intricate process resolves a Pointer (PTR) record, which provides the canonical hostname associated with that specific IP address. This design ensures that these infrastructure domains are typically populated only with PTR records, maintaining their integrity for their intended network management roles.

The Evolution of Reverse DNS and IPv6 Adoption
The transition from IPv4 to IPv6 has been a gradual but persistent shift in the internet’s addressing scheme. IPv4, with its 32-bit addresses, offers approximately 4.3 billion unique addresses, a pool that has been largely exhausted. IPv6, by contrast, utilizes 128-bit addresses, providing an astronomically larger address space (approximately 3.4 x 10^38 unique addresses). This vast expansion addresses the growing demand for internet-connected devices and services. However, the complexity of IPv6 addresses and their management also introduces new challenges and potential vulnerabilities if not meticulously secured. The sheer scale of IPv6 makes comprehensive monitoring and threat detection more arduous, creating fertile ground for threat actors to exploit less-understood or less-scrutinized aspects of its implementation, particularly within its reverse DNS infrastructure.
The core principle of reverse DNS is to provide a layer of trust and verification. For instance, many email servers check the PTR record of an incoming mail server’s IP address to ensure it matches the sending domain, a measure against spam and spoofing. This reliance on reverse DNS for legitimacy is precisely what attackers are now subverting.
Unveiling the Phishing Campaign: Abuse of ip6.arpa
Recent investigations have uncovered a sophisticated phishing campaign that deliberately misuses the ip6.arpa reverse DNS TLD. Traditionally, this domain is exclusively populated with PTR records mapping IPv6 addresses back to their legitimate hostnames. However, threat actors have discovered a critical vulnerability in how some DNS management platforms handle these special zones.
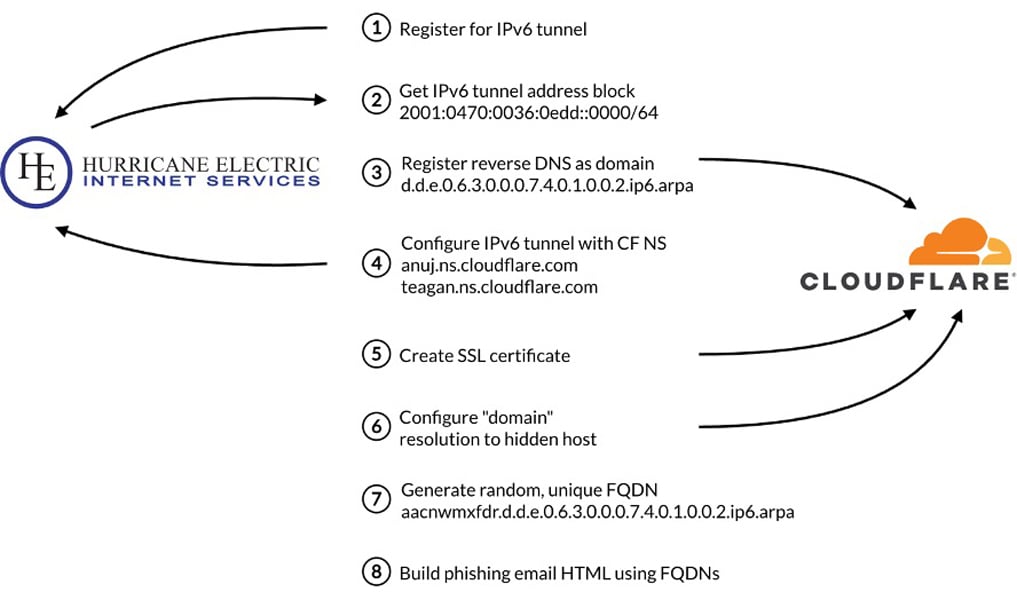
The attack methodology begins with adversaries acquiring blocks of IPv6 address space. This can be achieved through various means, including IPv6 tunneling services or directly from internet service providers. The pivotal step involves gaining authoritative control over the reverse DNS zone for their newly acquired IPv6 range. While legitimate use dictates that only PTR records should be configured in these zones, the observed campaigns reveal that some DNS providers permit the creation of other record types, such as A (Address) records, within these infrastructure-specific .arpa domains. This deviation from standard practice is the linchpin of the attack.
The Attack Chain Deconstructed:
- IPv6 Address Acquisition: Attackers obtain a block of IPv6 addresses. This is often done via services that facilitate IPv6 connectivity, sometimes through tunnels or virtual private servers, allowing them to control a segment of the IPv6 address space.
- Reverse DNS Zone Control: Once an IPv6 block is secured, the attackers establish control over its corresponding reverse DNS zone. This means they become the authoritative entity for resolving IP addresses within that range back to hostnames.
- Malicious Record Creation: Instead of limiting themselves to the expected PTR records, the attackers exploit a configuration loophole in certain DNS management platforms. They create A records within their controlled
ip6.arpazone. These A records map specifically crafted, seemingly legitimate, reverse DNS hostnames (e.g.,d.d.e.0.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa) directly to the IP addresses of their phishing infrastructure. - Leveraging Reputable DNS Providers: A key strategic element is the use of widely respected DNS providers, such as Cloudflare or Hurricane Electric, to host these malicious records. By doing so, the attackers inherit the robust infrastructure and high reputation of these legitimate services. When a victim’s device queries one of these attacker-controlled reverse DNS names, the resolution process involves these reputable providers, further masking the malicious intent and lending an air of legitimacy to the DNS responses.
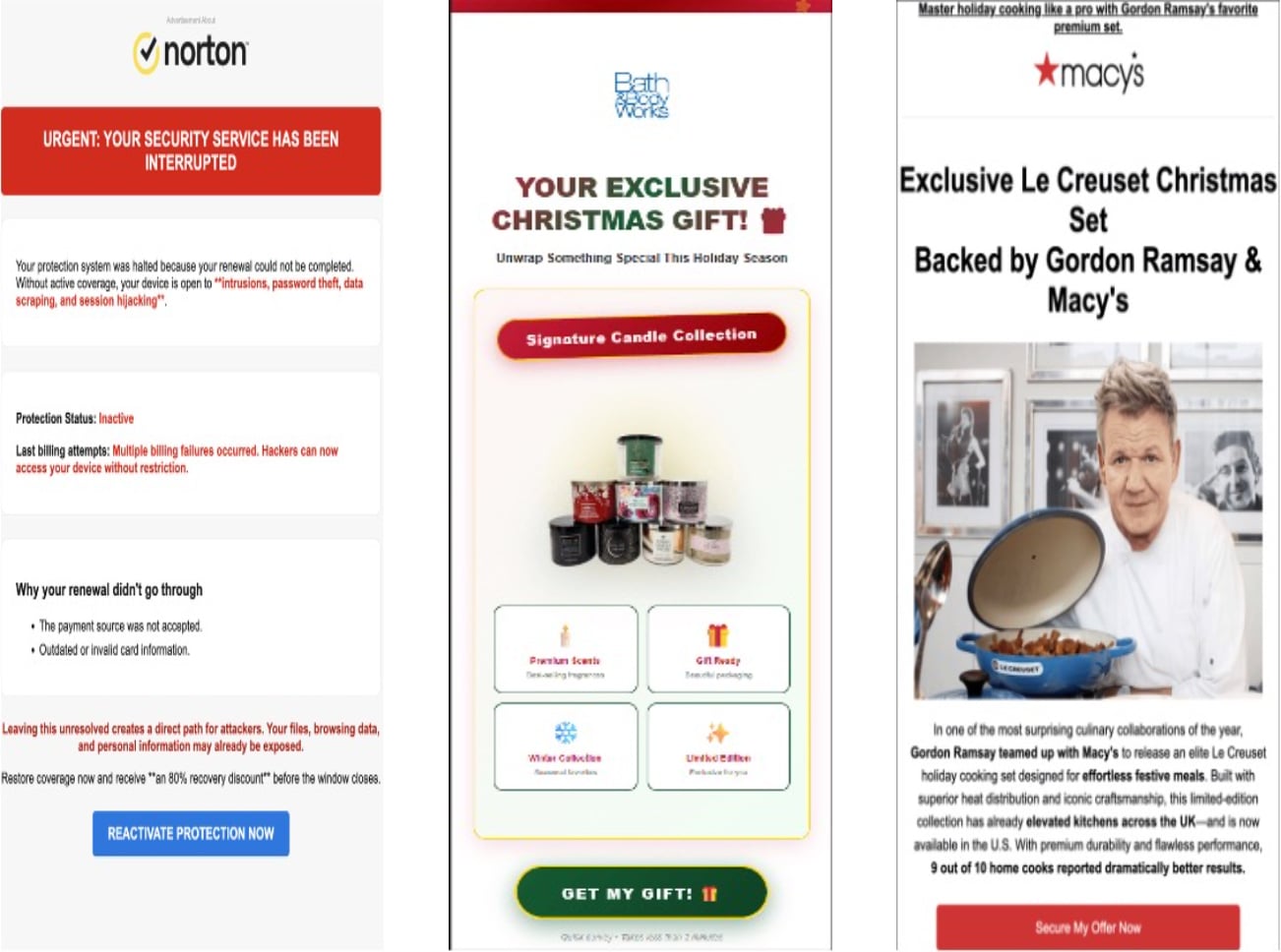
- Phishing Email Delivery: The phishing emails are meticulously crafted, employing social engineering lures like prize notifications, survey rewards, or urgent account alerts. Crucially, the malicious link embedded within these emails does not appear as a typical, suspicious-looking domain. Instead, the link is often hidden behind an image or a seemingly innocuous text, and the underlying HTML points to one of the attacker-controlled
ip6.arpahostnames (e.g.,<img src="http://d.d.e.0.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa/image.jpg" />or<a href="http://d.d.e.0.6.3.0.0.0.7.4.0.1.0.0.2.ip6.arpa/login">Click Here</a>). This obfuscation ensures that the peculiar.arpadomain is not immediately visible to the recipient, reducing suspicion. - Traffic Distribution System (TDS) Integration: Upon clicking the malicious link, victims are first routed through a Traffic Distribution System (TDS). This sophisticated intermediary analyzes various parameters, including the victim’s IP address, geographic location, device type, and referrer headers. If the victim is deemed a valid target (i.e., not a security researcher or automated scanner), they are redirected to the ultimate phishing landing page. Otherwise, they are typically shunted to a benign, legitimate website or an error page, thereby frustrating analysis and detection efforts.
- Ephemeral Infrastructure: The phishing links and their associated infrastructure are designed to be short-lived, often active for only a few days. After this brief operational window, the links are either deactivated or redirect to unrelated, legitimate sites. This ephemeral nature significantly complicates forensic analysis, incident response, and takedown procedures, allowing threat actors to operate with agility and evade sustained scrutiny.
Evasion Mechanisms and Their Implications
This abuse of .arpa domains and IPv6 reverse DNS presents several formidable challenges for existing security defenses:
- Circumventing Domain Reputation: Traditional email security gateways heavily rely on domain reputation, age, and WHOIS information to assess legitimacy. However,
.arpadomains are reserved for internet infrastructure and do not possess standard WHOIS records, domain registration dates, or typical reputation scores. This absence of conventional metadata renders many automated reputation-based filters ineffective. The domains appear as fundamental network components rather than newly registered, suspicious entities. - Exploiting Trust in Infrastructure: By leveraging reputable DNS providers to host their malicious A records, attackers benefit from the inherent trust placed in these providers’ infrastructure. Security systems might interpret DNS responses from Cloudflare or Hurricane Electric as inherently benign, overlooking the anomalous record types within the
ip6.arpazone. - Difficulty in Detection: The generation of reverse DNS hostnames from IPv6 addresses results in long, complex strings (e.g.,
4.0.0.2.0.0.0.0.0.0.0.0.0.0.0.0.2.0.8.0.8.0.0.4.0.b.8.f.7.0.6.2.ip6.arpa). While unusual, these are structurally valid within the reverse DNS context. Security tools not specifically configured to flag A records inip6.arpazones or to analyze the context of such hostnames might allow them to pass unchallenged. - Obfuscation through Embedding: The strategy of embedding
.arpalinks within images or non-obvious HTML elements in emails significantly reduces the likelihood of human detection. Users are less likely to scrutinize the underlying URL when clicking an image, especially if the email itself appears to be from a trusted source. - Analyst Evasion: The short operational lifespan of the phishing links, coupled with the TDS filtering mechanism, directly targets security researchers and automated scanners. This makes it challenging to gather sustained intelligence, analyze the full scope of the campaign, and implement effective countermeasures before the attackers pivot to new infrastructure.
Beyond this specific .arpa abuse, threat actors are also incorporating other sophisticated techniques. Observations indicate the concurrent use of hijacked dangling CNAME records and subdomain shadowing. In the former, attackers identify CNAME records pointing to non-existent or expired resources and then register those resources themselves, effectively taking over a subdomain of a legitimate organization. Subdomain shadowing involves creating malicious subdomains under a compromised legitimate domain, leveraging the parent domain’s established reputation. These tactics, when combined with the .arpa abuse, create a multi-layered attack infrastructure that is exceptionally resilient and difficult to dismantle. The reported instances of hijacked CNAMEs belonging to government agencies, universities, telecommunication companies, and media organizations underscore the breadth and potential impact of these combined strategies.
Strategic Implications and Mitigation Strategies
This emergence of .arpa and IPv6 reverse DNS abuse signifies a critical shift in the phishing landscape. Attackers are moving beyond superficial trickery to exploit fundamental internet protocols and infrastructure design. This necessitates a corresponding evolution in defensive strategies:
- Enhanced DNS Monitoring and Analytics: Organizations must implement advanced DNS monitoring solutions capable of detecting anomalous record types (specifically A records) within
.arpazones. This requires deep packet inspection and contextual analysis that goes beyond simple blacklisting. Security operations centers (SOCs) should actively query their DNS logs for such anomalies. - Refined Email Gateway Rules: Email security gateways need to develop more sophisticated rulesets that specifically inspect for
.arpadomains within all embedded content, including image links and hidden HTML attributes. These rules should flag any non-PTR record usage withinin-addr.arpaorip6.arpaas highly suspicious. - Adaptive Reputation Systems: Domain reputation services must adapt to the unique characteristics of infrastructure domains. Instead of relying on traditional metrics, they should incorporate behavioral analytics, real-time threat intelligence, and a deeper understanding of standard
.arpausage to identify deviations. - DNS Provider Responsibility: Internet infrastructure providers, particularly those offering DNS management services, have a critical role to play. They must review their configuration policies to ensure that A records and other non-PTR records cannot be created within
in-addr.arpaandip6.arpazones, thereby closing the foundational loophole exploited by these attackers. - Proactive Threat Intelligence Sharing: Collaboration among security researchers, DNS providers, and internet governing bodies is paramount. Rapid sharing of intelligence regarding new abuse vectors and compromised infrastructure can accelerate detection and remediation efforts.
- Robust User Education: While technical defenses are crucial, user education remains a cornerstone of cybersecurity. Employees must be continually trained to exercise extreme caution with unexpected links, regardless of how legitimate the email appears. The golden rule of navigating directly to official websites rather than clicking embedded links is more pertinent than ever.
- Comprehensive IPv6 Security Audits: As IPv6 adoption expands, organizations must conduct thorough security audits of their IPv6 implementations, including reverse DNS configurations, to identify and mitigate potential vulnerabilities before they are exploited.
The exploitation of .arpa domains and IPv6 reverse DNS represents a sophisticated evolution in cyberattack methodology, leveraging the very foundations of internet communication for malicious purposes. As threat actors continue to probe and exploit the intricate layers of internet infrastructure, a dynamic and multi-faceted defensive posture, combining technical innovation with vigilance and education, is essential to safeguard digital assets and user trust.