
A concerted effort by Russian state-sponsored threat actors to compromise secure communication channels, particularly those leveraging end-to-end encryption, has been definitively linked to Moscow’s intelligence services by a recent advisory from the United States’ primary federal investigative agency. This advanced campaign bypasses cryptographic protections not by technical decryption, but through cunning social engineering tactics designed to seize control of user accounts on widely adopted commercial messaging applications (CMAs), affecting thousands globally and primarily targeting individuals possessing access to sensitive national security information.
Definitive Attribution and Strategic Implications
The issuance of a public service announcement (PSA) by the Federal Bureau of Investigation (FBI) marks a significant escalation in the transparency surrounding these digital intrusions. For the first time, an official U.S. government body has directly attributed these widespread account hijacking operations to specific Russian intelligence services, moving beyond previous, more generalized descriptions of "state-backed" or "state-sponsored" adversaries. This explicit naming convention underscores a heightened level of confidence in intelligence assessments regarding the origin and intent of these campaigns, signaling a more direct diplomatic and strategic posture against such cyber espionage. The attribution is critical, providing clarity to governments, organizations, and individuals about the specific nation-state threat actor responsible for these sophisticated operations. It frames these attacks not merely as opportunistic cybercrime but as deliberate components of a broader intelligence-gathering strategy executed by a hostile foreign power.
The Mechanism of Subversion: Bypassing Encryption Through Trust Exploitation
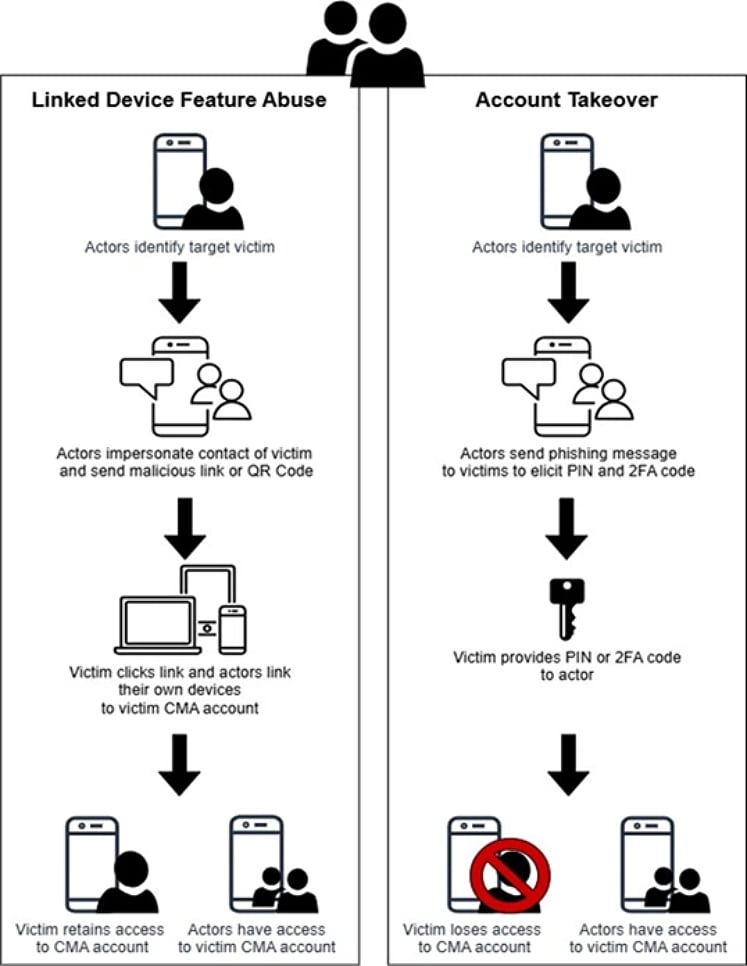
Contrary to common misconceptions that such high-stakes espionage necessitates the cracking of advanced cryptographic protocols, the Russian intelligence campaigns demonstrate a more insidious and equally effective approach: human exploitation. The FBI’s analysis confirms that the end-to-end encryption inherent in platforms like Signal and WhatsApp remains uncompromised. Instead, the attackers exploit fundamental aspects of user interaction and trust. Their primary modus operandi involves account hijacking, where malicious actors trick users into inadvertently granting them access to their existing messaging profiles or linking attacker-controlled devices to their legitimate accounts. This method, leveraging social engineering rather than cryptographic vulnerabilities, highlights the enduring truth that the human element often represents the weakest link in even the most robust security chains. By gaining control of an account, adversaries can seamlessly integrate into ongoing conversations, access historical message data, obtain contact lists, and perpetuate further deception, all while operating under the guise of the legitimate user.

A Global Target Profile: High-Value Intelligence Assets
The scope of these attacks is not random; it is meticulously calculated. The FBI specifies that the campaigns are directed at "individuals of high intelligence value," a category that includes current and former U.S. government officials, military personnel, political figures, and journalists. This selective targeting underscores the strategic intent behind these operations: to acquire classified, sensitive, or politically influential information that can serve Russia’s geopolitical and strategic interests. Such individuals frequently utilize secure messaging platforms for both professional and personal communications, making their accounts repositories of potentially critical intelligence. The compromise of a single high-value target can yield a cascade of benefits for an adversary, including access to internal discussions, future plans, sensitive contacts, and even leverage for future influence operations. The global reach of these attacks, impacting thousands of accounts worldwide, suggests a well-resourced and persistent campaign designed to cast a wide net for valuable intelligence.
International Consensus on Evolving Threats
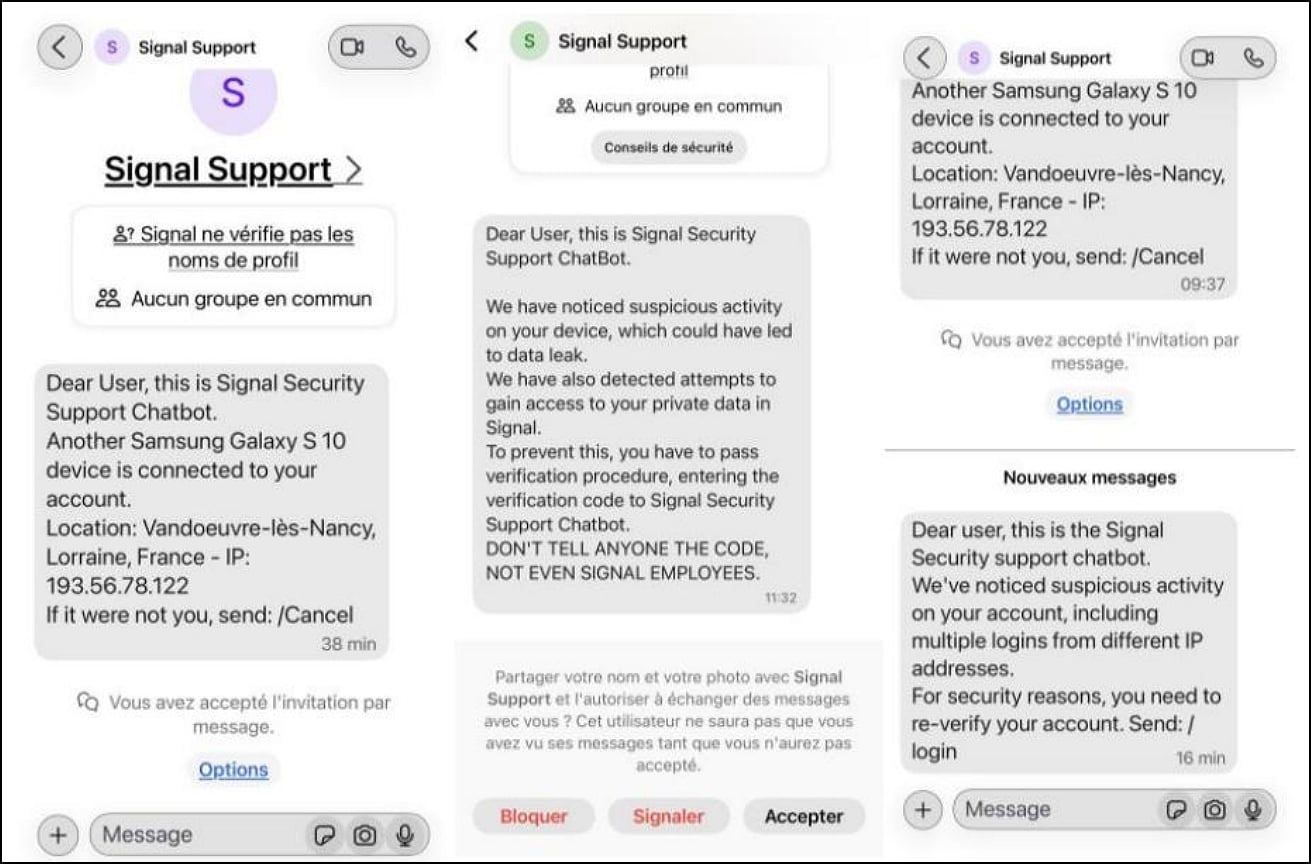
The FBI’s recent warning is not an isolated pronouncement but rather converges with earlier advisories issued by leading cybersecurity authorities in Europe, highlighting a shared understanding of this evolving threat landscape. Both Dutch intelligence agencies and France’s Cyber Crisis Coordination Center (C4) had previously published warnings describing strikingly similar account-hijacking operations targeting secure messaging platforms. The consistency across these international reports — from the identification of state-backed actors to the specific technical and social engineering tactics employed — reinforces the veracity and widespread nature of the threat. The Dutch advisory, for instance, detailed how attackers manipulated users into allowing unauthorized device linking, while the French C4 report emphasized the ongoing and pervasive nature of these campaigns across multiple nations. This international consensus provides a robust framework for understanding the adversary’s methods and underscores the necessity of a coordinated global defense strategy against such sophisticated digital espionage.
Deceptive Tactics: The Art of Digital Impersonation
The core of these phishing campaigns lies in their ability to convincingly impersonate trusted entities, primarily platform support services. Attackers craft messages that appear legitimate, often urging targets to take an immediate action, such as verifying their account, updating security settings, or resolving a supposed technical issue. These messages typically contain malicious links or instruct users to scan QR codes or enter verification codes. When a user scans a malicious QR code, they inadvertently link an attacker-controlled device to their account, granting the adversary full access. Similarly, sharing a verification code, often prompted by a fabricated "security alert," effectively hands over control of the account. These techniques are highly effective because they exploit a user’s natural inclination to trust official communications and to act quickly on security-related prompts. The attackers’ ability to maintain persistence once inside an account — silently monitoring communications, participating in group chats, and sending messages as the compromised user — makes detection incredibly difficult and enables the perpetuation of further phishing attacks from a seemingly legitimate source.
Broader Implications and Future Challenges
The success of these account hijacking operations carries profound implications beyond individual account compromises. For national security, such breaches can lead to the exfiltration of classified information, compromise ongoing operations, and undermine diplomatic efforts. For the targeted individuals, the consequences can range from reputational damage and professional setbacks to personal security risks and the potential exposure of their networks. The very trust that underpins secure communication platforms is eroded when adversaries can so effectively impersonate users.
From a strategic perspective, these attacks highlight the ongoing cat-and-mouse game in cyber warfare. While significant resources are often poured into developing offensive capabilities to exploit zero-day vulnerabilities or directly breach encrypted systems, these campaigns demonstrate the continued efficacy and cost-effectiveness of social engineering. It represents a paradigm where human vigilance, or the lack thereof, becomes the critical battleground. This shift places a greater burden on user education and robust organizational security policies that prioritize human factors alongside technical defenses.
The future outlook suggests a continued evolution of these tactics. As users become more aware of QR code and verification code scams, threat actors will undoubtedly refine their social engineering lures, potentially integrating more sophisticated psychological manipulation techniques or leveraging AI-generated content to enhance realism. The ongoing challenge for cybersecurity professionals and intelligence agencies will be to stay ahead of these adaptive adversaries, disseminating timely and actionable intelligence, and fostering a culture of perpetual skepticism and robust digital hygiene among high-value targets.
Fortifying Defenses: A Multi-Layered Approach
Given the sophisticated nature of these threats, a multi-layered defense strategy is imperative. Basic recommendations, such as remaining suspicious of unexpected messages and never sharing verification codes, form the foundational layer. However, organizations and individuals with high intelligence value must adopt more comprehensive measures:
- Enhanced User Training: Regular, interactive training sessions that simulate real-world phishing scenarios can significantly improve user recognition of malicious attempts. This training should emphasize the specific tactics used in these campaigns, such as impersonating support or requesting QR code scans.
- Robust Multi-Factor Authentication (MFA): While not all CMAs offer enterprise-grade MFA, users should enable the strongest possible authentication methods available, including hardware security keys where supported, to add an additional layer of protection beyond a simple password or verification code.
- Device Security Hygiene: Ensuring all devices accessing CMAs are regularly updated, free of malware, and protected by strong passwords or biometrics is crucial. Attackers who gain access to a device might also gain access to messaging apps.
- Segregation of Communications: High-value individuals should consider segregating their communications, using dedicated devices or platforms for highly sensitive discussions, minimizing the risk of cross-contamination from less secure personal usage.
- Organizational Policies: Enterprises and government agencies must implement clear policies regarding the use of CMAs for official communications, including guidelines for reporting suspicious activity and procedures for handling potential compromises.
- Continuous Threat Intelligence: Staying informed about the latest threat intelligence, particularly from agencies like the FBI and international partners, is vital for proactive defense. This allows for timely adaptation of security protocols and user advisories.
Ultimately, while the promise of end-to-end encryption offers a powerful shield against digital eavesdropping, the human element remains the most vulnerable vector for determined state-sponsored adversaries. The FBI’s direct attribution to Russian intelligence serves as a stark reminder that even the most secure technologies can be undermined by sophisticated psychological manipulation, necessitating an equally sophisticated and adaptive human defense.







