A sophisticated and pervasive cyber campaign is actively exploiting the critical role of Virtual Private Networks (VPNs) in modern enterprise infrastructure. Threat actors are deploying highly convincing spoofed VPN client downloads, leveraging advanced search engine optimization (SEO) poisoning techniques to ensnare unsuspecting corporate users. This multi-pronged attack aims to illicitly acquire sensitive login credentials and proprietary network configuration data, thereby establishing a foothold within targeted organizations.
The operation, attributed to a formidable threat entity, meticulously crafts fraudulent websites that mirror the legitimate online presence of leading enterprise VPN providers. By manipulating search engine algorithms for common product queries, these malicious sites are propelled into prominent positions, luring users seeking legitimate software downloads. Upon accessing these deceptive portals, victims are prompted to download what appears to be a genuine VPN client installer. However, this seemingly innocuous package conceals a potent information-stealing malware designed to exfiltrate critical authentication details and system configurations.
The Evolution of a Targeted Attack Vector
The targeting of VPN infrastructure represents a logical, albeit deeply concerning, evolution in cyber offensive strategies. As remote work models have become standard across industries, VPNs serve as the primary conduit for employees to securely access internal corporate resources. This makes them an invaluable target for adversaries seeking to bypass perimeter defenses and gain initial access to an organization’s internal network. Unlike traditional phishing attacks that might target specific individuals, this campaign broadens its scope by weaponizing common user behavior – searching for and downloading essential business software.
Analysis of the campaign’s infrastructure and methodology reveals a high degree of planning and technical execution. The threat actors have demonstrated the capability to rapidly deploy and adapt their spoofed domains, mimicking a broad spectrum of enterprise VPN solutions from prominent vendors including Ivanti, Cisco, Fortinet, Sophos, Sonicwall, Check Point, and WatchGuard. This comprehensive approach indicates an intention to maximize the attack surface and exploit the diverse VPN ecosystems prevalent across the global business landscape.
Unpacking the Attack Chain: From SEO Poisoning to Data Exfiltration
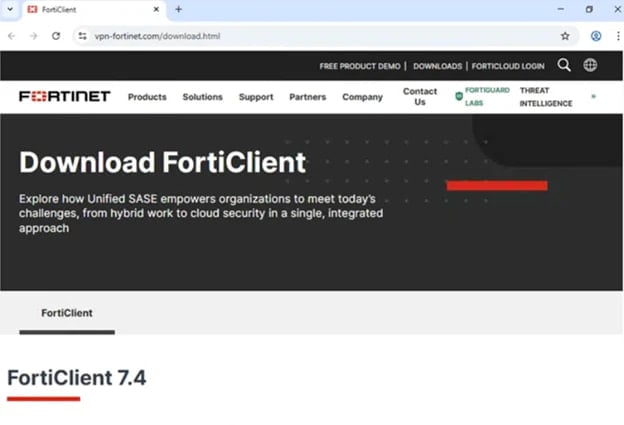
The initial phase of the attack hinges on SEO poisoning. This technique involves manipulating search engine rankings to promote malicious websites. Threat actors achieve this through various means, such as creating numerous backlinks from compromised sites, stuffing keywords, or exploiting vulnerabilities in legitimate websites to inject malicious content that boosts their search ranking. When an employee searches for a term like "Fortinet VPN client download" or "Cisco AnyConnect installer," the spoofed site appears high in the search results, often above or alongside legitimate vendor pages.
Once a user clicks on the deceptive link, they are redirected to a meticulously crafted phishing site. These sites are designed with high fidelity to replicate the branding, layout, and even the user interface of official vendor pages. The goal is to instill a false sense of security, convincing the user that they are interacting with a trusted source. The malicious download is typically presented as a standard installer package, often a compressed archive containing an MSI (Microsoft Installer) file.

In a documented instance, the fake sites linked to a GitHub repository, a seemingly legitimate code-hosting platform, which further lends credibility to the download. This tactic leverages trusted platforms to host malicious payloads, bypassing some traditional web filtering mechanisms that might flag unknown or suspicious domains. Although the specific repository was subsequently identified and taken down, the use of such platforms highlights the attacker’s adaptability and resourcefulness in evading detection.
The Malicious Payload: Hyrax Infostealer and Persistent Compromise
Execution of the fake VPN MSI installer initiates a multi-stage infection process. The primary malicious component observed is a variant of the Hyrax infostealer. This sophisticated malware is designed specifically for credential harvesting and system reconnaissance. Upon installation, the malware establishes persistence by modifying the Windows registry, typically through the RunOnce key, ensuring it automatically restarts with the operating system. This mechanism guarantees that the compromise endures even after system reboots, providing a sustained window for data exfiltration.
A critical aspect of the malware’s operation involves the deployment of various modules, including a loader (e.g., dwmapi.dll) and the infostealer itself (e.g., inspector.dll). These components work in concert to capture sensitive information. The fake VPN client application, while appearing legitimate, is merely a facade. It presents a functional-looking login interface, prompting users to input their corporate VPN credentials. As soon as these details are entered, they are immediately harvested and exfiltrated to the threat actor’s command-and-control (C2) infrastructure.
Beyond direct credential theft, the Hyrax variant also targets existing VPN configuration data. It specifically seeks out files like connectionsstore.dat from the legitimate VPN client’s directory. This file often contains crucial details about VPN servers, connection settings, and even pre-shared keys or other sensitive configuration parameters. Stealing this information provides the attackers with a comprehensive understanding of the organization’s VPN topology, potentially enabling them to craft more targeted attacks or establish direct connections to the corporate network without needing to guess server details.
Deceptive User Experience and Obfuscation
A hallmark of this campaign’s sophistication lies in its post-compromise deception. To minimize suspicion and prevent immediate detection, the fake VPN client is programmed to display an "installation error" after successfully stealing credentials. This error message serves as a plausible cover, leading the user to believe a technical glitch occurred. Following this simulated error, the user is often redirected to the actual legitimate vendor’s website to download the correct VPN client.
This ingenious maneuver ensures that the victim is likely to attribute the initial failure to a benign technical issue rather than a malicious attack. If the user subsequently downloads and successfully installs the legitimate VPN client, their connection works as expected, leaving them with no discernible indicators of compromise. This seamless transition makes the attack incredibly stealthy from the end-user’s perspective, allowing the infostealer to persist in the background, continuously harvesting data without triggering immediate alarms.
Furthermore, the malware has been observed to be digitally signed with a legitimate, albeit subsequently revoked, certificate issued to a company named Taiyuan Lihua Near Information Technology Co., Ltd. The use of a valid digital certificate, even if later revoked, initially helps the malware bypass basic security checks that flag unsigned executables. This adds another layer of credibility to the malicious installer, making it harder for conventional antivirus solutions to immediately identify it as a threat during the initial download and execution phase. The revocation process, while essential, often has a delay, providing a window for adversaries to exploit.
Profound Implications for Enterprise Security
The implications of this sophisticated credential theft campaign are far-reaching for any organization. Stolen VPN credentials represent a direct gateway into the corporate network, bypassing layers of perimeter security. Once inside, threat actors can:
- Perform Lateral Movement: Navigate through the internal network, identify critical assets, and gain access to sensitive data repositories.
- Deploy Further Malware: Install ransomware, additional infostealers, or remote access Trojans (RATs) to establish more persistent and robust control.
- Exfiltrate Sensitive Data: Steal intellectual property, customer data, financial records, or employee information, leading to severe data breaches and regulatory non-compliance.
- Disrupt Operations: Cause significant operational downtime by encrypting systems or sabotaging critical infrastructure.
- Establish Long-Term Persistence: Create backdoors or compromise legitimate accounts for future access, making remediation significantly more challenging.
The psychological aspect of the attack also poses a challenge. The lack of immediate indicators of compromise for end-users means that victims are unlikely to report any suspicious activity, allowing the breach to go unnoticed for extended periods. This dwell time provides attackers ample opportunity to achieve their objectives.
Comprehensive Mitigation Strategies and Future Outlook
Addressing such a multifaceted threat requires a layered and proactive security posture. Organizations must implement a combination of technical controls, security awareness training, and robust incident response capabilities:
- Enforce Multi-Factor Authentication (MFA): This is perhaps the single most effective defense against credential theft. Even if an attacker obtains a user’s password, MFA prevents unauthorized access unless they also possess the second factor (e.g., a one-time code from an authenticator app, a hardware token). MFA should be mandatory for all VPN access and critical internal systems.
- Advanced Endpoint Protection: Deploying Endpoint Detection and Response (EDR) solutions in conjunction with Next-Generation Antivirus (NGAV) is crucial. EDR systems can detect anomalous behavior, identify the execution of suspicious processes, and block malware even if it attempts to evade traditional signature-based detection. Running EDR in "block mode" can prevent suspicious activities from escalating.
- Security Awareness Training: Regular and targeted training for employees is paramount. Users must be educated on the risks of SEO poisoning, the importance of verifying URLs, and the dangers of downloading software from unofficial sources. They should be trained to scrutinize website certificates, look for discrepancies in branding, and understand that legitimate software is typically downloaded directly from the vendor’s official portal or through an internal IT-managed distribution system.
- Proactive Threat Hunting and Intelligence: Organizations should actively monitor for indicators of compromise (IoCs) associated with known campaigns. This includes monitoring network traffic for connections to suspicious C2 infrastructure, scanning endpoints for known malware hashes, and regularly reviewing logs for unusual activity. Subscribing to threat intelligence feeds provides early warnings of emerging threats and attacker methodologies.
- Robust Web Filtering and DNS Security: Implementing strong web content filtering and DNS security solutions can block access to known malicious domains and prevent users from reaching spoofed websites in the first place. Cloud-delivered protection services, such as Microsoft Defender SmartScreen, offer real-time reputation checks for websites and downloads.
- Software Supply Chain Security: Organizations must establish strict policies for software procurement and deployment. All software, especially critical infrastructure components like VPN clients, should be sourced exclusively from official vendor channels or trusted internal repositories. Regular integrity checks should be performed on installed software.
- Zero Trust Architecture: Adopting Zero Trust principles, where no user or device is inherently trusted, regardless of its location (inside or outside the network), can significantly mitigate the impact of a breach. This involves granular access controls, continuous verification, and least privilege access.
- Certificate Revocation Monitoring: While attackers may use revoked certificates, security systems should be configured to check Certificate Revocation Lists (CRLs) or use the Online Certificate Status Protocol (OCSP) to validate certificate status, even if this can introduce latency.
- Regular Audits and Penetration Testing: Periodically auditing security controls and conducting penetration tests can identify vulnerabilities and weaknesses in defenses before they can be exploited by adversaries.
The ongoing evolution of cyber threats necessitates a dynamic and adaptive security strategy. The campaign leveraging fake enterprise VPN sites underscores the critical importance of a multi-layered defense approach that combines advanced technical controls with robust human awareness. In an era where digital identity is the new perimeter, safeguarding credentials and ensuring the integrity of critical access points like VPNs remains a paramount challenge for cybersecurity professionals worldwide.