A sophisticated and persistent cyber espionage campaign, meticulously linked to state-sponsored actors operating out of China, has been systematically compromising critical telecommunications service providers across South America since early 2024, employing a newly identified arsenal of multi-platform malware to infiltrate Windows, Linux, and crucial network-edge devices.
The strategic importance of telecommunications networks in the modern global landscape cannot be overstated. These foundational digital arteries facilitate national and international communication, underpin economic activity, and are indispensable to governmental and military operations. Consequently, they represent prime targets for nation-state adversaries engaged in intelligence gathering, pre-positioning for future disruptive actions, or seeking to exert geopolitical influence. For years, cyber warfare and espionage units affiliated with the People’s Republic of China have been recognized as prolific actors in this domain, consistently demonstrating advanced capabilities and a broad scope of targeting. The recent revelations concerning the activity cluster designated as UAT-9244 further underscore this persistent threat, highlighting a concerted effort to establish persistent footholds within the digital infrastructure of South American nations.
Analysis by leading cybersecurity researchers has attributed the UAT-9244 campaign with high confidence to entities closely aligned with known Chinese advanced persistent threat (APT) groups, specifically FamousSparrow and Tropic Trooper. While distinct in its operational tracking, the observed commonalities in tooling, tactical approaches, procedural methodologies (TTPs), and victim profiles establish a compelling nexus between UAT-9244 and these previously documented state-sponsored operations. This strong correlation suggests either a shared development lineage, a common command and control infrastructure, or a collaborative operational framework among these distinct but related threat clusters. The precise motivations for segmenting these operations into separate clusters, despite clear overlaps, could range from compartmentalization for resilience to obfuscating the full scope of a larger, coordinated strategic objective. While sharing a similar targeting emphasis with another notable Chinese APT, Salt Typhoon, researchers have not yet definitively established a direct operational link between UAT-9244 and that particular group, indicating the complex and often layered nature of state-sponsored cyber campaigns.
The operational scope of UAT-9244 is particularly noteworthy due to its comprehensive targeting of diverse operating environments prevalent within telecommunication infrastructures. This multi-platform approach, encompassing Windows workstations and servers, Linux-based systems often found in backend operations and specialized network equipment, and critical network-edge devices, demonstrates a meticulous understanding of modern IT and operational technology (OT) landscapes within the telecommunications sector. By compromising these varied systems, the actors aim to achieve deep network penetration, enable lateral movement, exfiltrate sensitive data, and potentially establish persistent access for future exploitation or disruption. The focus on South American telecommunication providers is strategically significant, potentially allowing for intelligence collection on regional communications, access to proprietary network designs, or the ability to monitor or interfere with data flows, which could have profound geopolitical implications.
Central to UAT-9244’s success is its sophisticated and previously undocumented malware toolkit, meticulously designed for stealth and persistence across various environments. This arsenal comprises three primary components: TernDoor, a robust Windows backdoor; PeerTime, an innovative Linux backdoor leveraging the BitTorrent protocol; and BruteEntry, a brute-force scanner engineered to construct proxy infrastructure.

TernDoor: The Windows Backdoor
TernDoor exemplifies a highly capable Windows backdoor, deployed with a degree of sophistication aimed at evading conventional detection mechanisms. Its initial infection vector involves dynamic-link library (DLL) side-loading, a common but effective technique where a malicious DLL is placed in a legitimate application’s search path, causing the application to load the attacker’s code instead of the intended library. In this instance, the legitimate executable wsprint.exe is hijacked to load BugSplatRc64.dll, which then decrypts and injects the final TernDoor payload directly into memory, typically within msiexec.exe, further obscuring its presence.
Beyond its stealthy deployment, TernDoor incorporates an embedded Windows driver, WSPrint.sys. The inclusion of a kernel-mode driver grants the malware elevated privileges, enabling it to perform highly sensitive operations such as terminating, suspending, and resuming processes. Such capabilities are invaluable for maintaining control, disrupting security software, or preparing the environment for further malicious actions. Persistence is ingeniously achieved through a combination of scheduled tasks and modifications to the Windows Registry, with additional registry alterations specifically designed to obfuscate the presence of the scheduled tasks, making detection and removal more challenging for defenders. Functionally, TernDoor is a comprehensive remote access tool, capable of executing arbitrary commands via a remote shell, launching new processes, performing extensive file system operations (reading, writing, modifying), collecting detailed system information, and possessing a self-uninstall mechanism for clean exit or evasion.
PeerTime: The Multi-Architecture Linux Backdoor with P2P C2
PeerTime represents a particularly innovative component of the UAT-9244 toolkit, specifically engineered to target the diverse Linux ecosystem prevalent in telecommunications networks, including embedded systems and specialized network devices. This ELF (Executable and Linkable Format) Linux backdoor supports multiple architectures, including ARM, AARCH, PPC, and MIPS, underscoring its design intent to compromise a vast array of devices beyond conventional x86/x64 servers. This multi-architecture compatibility is a critical indicator of a threat actor aiming for deep and broad penetration into specialized network hardware.

Two distinct versions of PeerTime have been identified: one developed in C/C++ and another leveraging the Rust programming language. The use of Rust, a modern language known for its memory safety and performance, indicates a sophisticated development capability and a desire to produce robust, efficient, and potentially harder-to-analyze malware. A crucial attribution indicator surfaced during analysis: the presence of Simplified Chinese debug strings within the instrumentor binary, providing a strong linguistic clue to its origin. Similar to TernDoor, PeerTime’s payload is decrypted and loaded directly into memory, with its process subsequently renamed to mimic legitimate system processes, thereby enhancing its stealth.
Perhaps the most striking feature of PeerTime is its utilization of the BitTorrent protocol for command-and-control (C2) communications. This peer-to-peer (P2P) C2 mechanism offers significant advantages to attackers, making detection and blocking considerably more challenging. By decentralizing C2 traffic and blending it with legitimate BitTorrent activity, traditional network-based detection methods that rely on identifying specific C2 server IPs or domains become less effective. PeerTime uses this P2P network to download and execute additional payloads from other compromised peers, further distributing its operational resilience. Furthermore, it leverages BusyBox, a common utility suite for embedded Linux systems, to write files onto the compromised host, demonstrating an understanding of the typical toolsets available in targeted environments.
BruteEntry: The Brute-Force Scanner and Proxy Infrastructure Builder
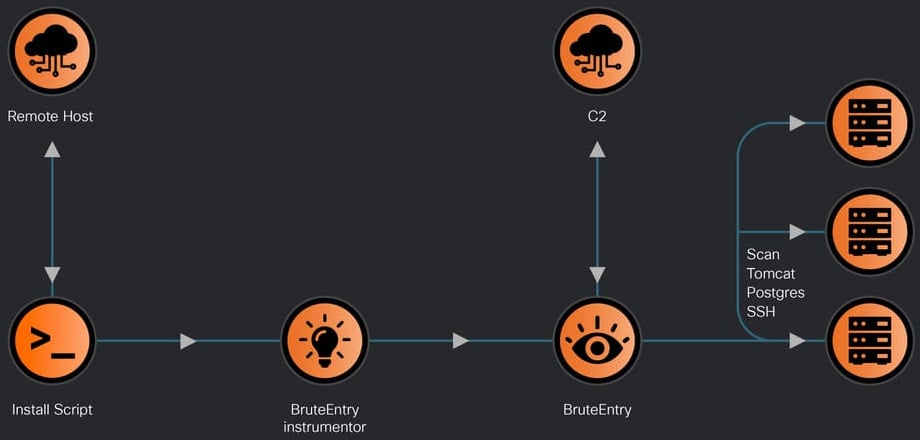
Completing the toolkit is BruteEntry, a two-part system consisting of a Go-based instrumentor binary and a dedicated brute-forcing component. BruteEntry’s primary function is to transform compromised devices into scanning nodes, which researchers refer to as Operational Relay Boxes (ORBs). These ORBs then serve as launchpads for further reconnaissance and brute-force attacks against new targets.
By co-opting compromised machines into a distributed scanning network, the attackers can mask their true origin, distribute the load of scanning, and increase their chances of discovering vulnerable services. BruteEntry systematically attempts to brute-force access to commonly exposed services such as SSH (Secure Shell), Postgres databases, and Tomcat web servers. These services are frequently found in backend systems and development environments, offering potential pathways to sensitive data or further network pivot points. The results of these login attempts, along with task statuses and operational notes, are then meticulously relayed back to the C2 infrastructure, providing the attackers with a continuous feedback loop on their reconnaissance efforts. The use of Go for the instrumentor binary again points to a modern development approach, favoring cross-platform compatibility and efficient execution.
Broader Implications and Defense Strategies
The UAT-9244 campaign signifies a persistent and evolving threat landscape facing global telecommunication infrastructure. The comprehensive nature of the toolkit, targeting multiple operating systems and employing advanced C2 techniques like P2P communication, demonstrates a high level of operational sophistication and resourcefulness. The strategic targeting of South American telcos aligns with broader geopolitical interests often associated with Chinese state-sponsored cyber operations, including intelligence gathering, economic espionage, and the potential for strategic access during times of heightened tension.
For telecommunication providers, these findings underscore the urgent need for robust, multi-layered cybersecurity defenses. Detection and mitigation strategies must extend beyond traditional perimeter security to encompass advanced endpoint detection and response (EDR) capabilities, network traffic analysis (NTA) that can identify anomalous P2P C2 patterns, and continuous threat hunting across Windows, Linux, and specialized network devices. The ability to detect DLL side-loading, identify malicious kernel drivers, and monitor for unusual process injection or scheduled task creation is paramount. Furthermore, stringent access controls, regular patching, multi-factor authentication (MFA) for all administrative interfaces, and proactive vulnerability management are essential hygiene factors that can significantly raise the bar for attackers.
The availability of detailed indicators of compromise (IoCs) associated with UAT-9244 activity is a critical resource for defenders. Incorporating these IoCs into security information and event management (SIEM) systems, intrusion detection/prevention systems (IDS/IPS), and endpoint protection platforms (EPP) can enable early detection and rapid response to ongoing or future attacks. Beyond technical controls, intelligence sharing within the telecommunications sector and with government security agencies is vital to collectively enhance resilience against such well-resourced and persistent state-sponsored threats.
The future outlook suggests a continued escalation in the sophistication of state-sponsored cyber operations targeting critical infrastructure. As defenders enhance their capabilities, adversaries will undoubtedly adapt, leveraging new technologies, developing more evasive malware, and refining their TTPs. The UAT-9244 campaign serves as a stark reminder of the continuous cyber arms race and the enduring strategic value placed on controlling or monitoring the world’s telecommunications networks by nation-state actors. Proactive defense, continuous vigilance, and a deep understanding of evolving threat actor capabilities are indispensable for safeguarding these vital digital lifelines.