A significant advancement in software supply chain security has arrived with the introduction of Betterleaks, an innovative open-source platform engineered to meticulously identify and validate sensitive information across diverse digital repositories. Positioned as a comprehensive evolution in the field of secrets detection, this new utility aims to establish a more robust standard for safeguarding proprietary credentials and sensitive data that often inadvertently make their way into development ecosystems.
The Pervasive Threat of Leaked Secrets
The digital landscape of modern software development is fraught with vulnerabilities, none more insidious and persistent than the accidental exposure of sensitive information, commonly referred to as "secrets." These include, but are not limited to, API keys, database credentials, cryptographic private keys, access tokens, and configuration parameters that grant elevated privileges or access to critical systems. Developers, under immense pressure to deliver features rapidly, can inadvertently commit these secrets directly into version control systems, local files, or even publicly accessible repositories. This seemingly innocuous oversight transforms a private asset into a potential weapon for malicious actors.
Threat intelligence consistently demonstrates that attackers actively scan public code repositories, cloud storage buckets, and configuration files for these leaked secrets. The motivation is clear: a single exposed API key can grant unauthorized access to an entire cloud environment, a database password can lead to massive data breaches, and a private key can compromise the integrity of an application or infrastructure. The financial and reputational ramifications of such breaches are staggering, often leading to prolonged recovery efforts, regulatory penalties, and a significant erosion of customer trust. Consequently, the proactive identification and remediation of these exposures have become an indispensable component of any robust cybersecurity strategy, emphasizing the critical role of specialized secret scanning utilities within the DevSecOps pipeline.
From Gitleaks to Betterleaks: A New Paradigm
For years, tools like Gitleaks have served as a cornerstone in the open-source community for addressing this critical security challenge. Developed by Zach Rice, a prominent figure in the domain of secrets scanning, Gitleaks gained widespread adoption, boasting millions of downloads and container pulls across various platforms. Its effectiveness in helping organizations "shift left" security – embedding security practices earlier in the development lifecycle – was undeniable. However, as the complexity of software development and the sophistication of attack vectors evolved, the need for a more expansive, performant, and intelligent scanning solution became increasingly apparent.
Betterleaks emerges directly from this lineage, conceived and maintained by the same visionary team, now bolstered by the strategic support of Aikido, a Belgian firm specializing in developer-first security solutions. This transition signifies more than just an incremental update; it represents a fundamental re-imagining of how secrets detection should function in an era of distributed development, diverse data sources, and burgeoning AI integration. The intentional removal of "Git" from the name underscores a strategic pivot: while Git repositories remain a primary focus, Betterleaks is designed to transcend the confines of a single version control system, offering a more universal approach to secret discovery across an ever-expanding array of digital assets.

Architectural Superiority and Performance Benchmarks
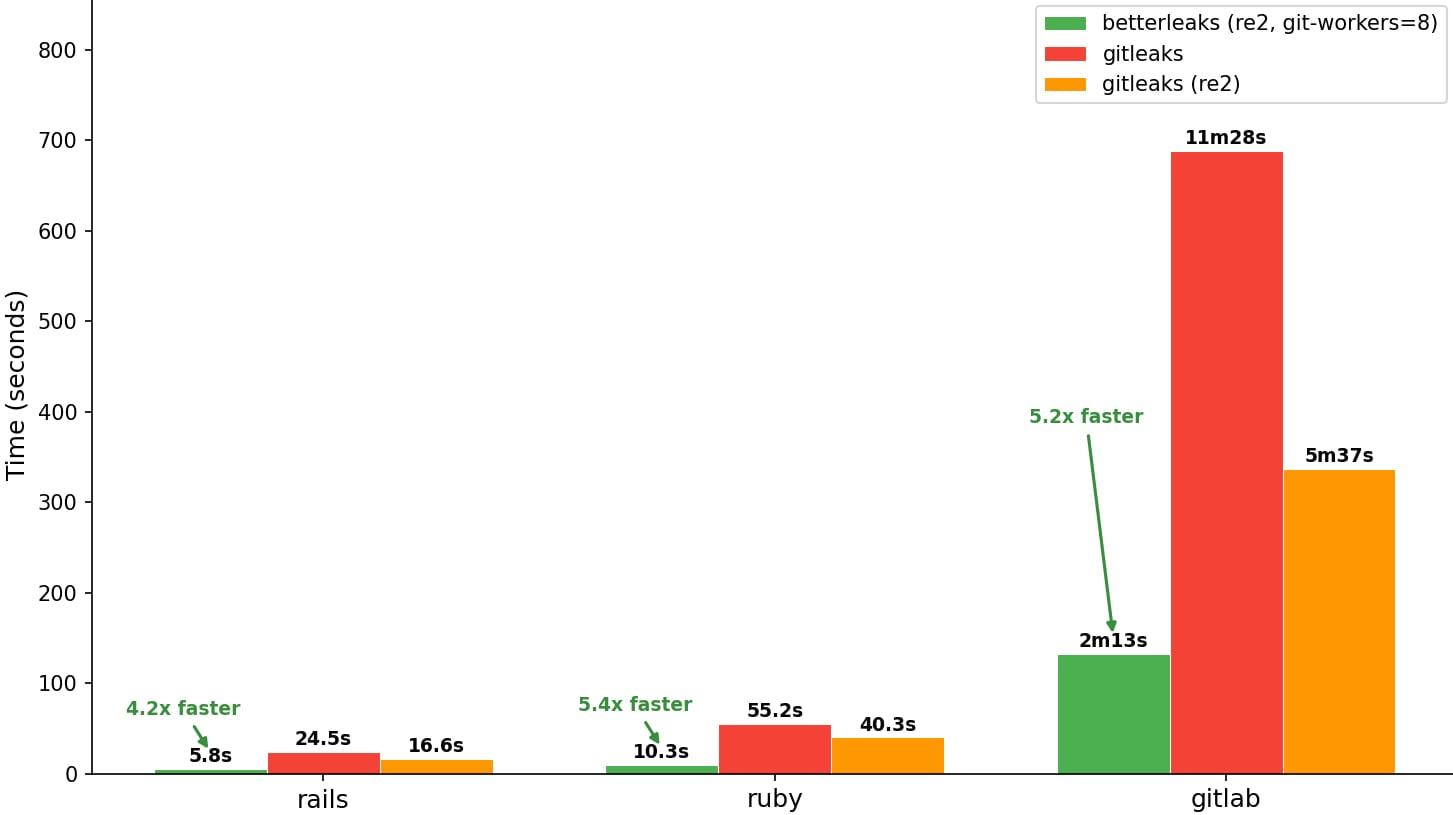
The "better" in Betterleaks is not merely a branding choice; it reflects substantial architectural and algorithmic enhancements designed to deliver superior performance and accuracy. The tool introduces a refined scanning engine that significantly outperforms its predecessors in terms of speed and efficiency. This performance boost is crucial for modern development environments characterized by massive codebases, frequent commits, and continuous integration/continuous deployment (CI/CD) pipelines where rapid feedback is paramount. Organizations can now execute more frequent and comprehensive scans without incurring prohibitive time penalties, thereby reducing the window of vulnerability.
Preliminary performance metrics highlight this advancement, demonstrating a notable reduction in scan times for comparable datasets. This efficiency translates directly into operational benefits: faster scans mean less disruption to developer workflows, quicker identification of newly introduced secrets, and a more agile response capability. For enterprise-level deployments, where terabytes of code may need regular scrutiny, these performance gains are not just advantageous but transformative, enabling a level of continuous monitoring previously impractical.
Enhanced Detection Capabilities and Customization
Betterleaks elevates detection beyond simple pattern matching. While it retains the flexibility of utilizing default rule sets, its architecture is built for extensive customization, allowing security teams to define highly specific rules tailored to their unique technology stacks, internal naming conventions, and proprietary secret formats. This level of granularity is critical for minimizing false positives, which can lead to "alert fatigue" among developers, and for maximizing the detection of legitimate, context-specific secrets that might evade generic scanners.
The tool’s ability to intelligently parse various file types and directory structures, alongside its deep integration with Git repository mechanics, ensures a comprehensive sweep for sensitive data. It moves beyond superficial checks, delving into commit histories, file diffs, and even obscure configuration files where secrets might be hidden. This holistic approach ensures that even cleverly obfuscated or infrequently used credentials are brought to light, significantly strengthening an organization’s defensive posture.
Strategic Vision and Future Innovations
The roadmap for Betterleaks outlines an ambitious trajectory, signaling its intent to remain at the forefront of secrets detection technology. Key planned features underscore a forward-thinking approach, anticipating the evolving challenges of software security:
- Expanded Data Source Support: Beyond traditional Git repositories and local files, future iterations will integrate with a broader spectrum of data sources. This includes cloud storage services (e.g., S3 buckets, Azure Blobs), container images, artifact repositories, and potentially even communication platforms, reflecting the decentralized nature of modern development artifacts.
- LLM-Assisted Analysis for Enhanced Classification: Perhaps one of the most significant upcoming innovations is the integration of Large Language Model (LLM) assisted analysis. This feature aims to move beyond purely deterministic pattern matching by leveraging AI to understand the context and semantic meaning of detected strings. This could dramatically reduce false positives by differentiating between a legitimate secret and a string that merely resembles one (e.g., a test variable named "API_KEY" versus an actual, functional API key). Furthermore, LLMs could identify more subtle forms of secrets, or combinations of data that, while not individually secret, collectively constitute a vulnerability. This represents a leap towards more intelligent and accurate secret classification.
- Advanced Detection Filters: Continuous refinement of detection logic will introduce more sophisticated filters, allowing for even finer-grained control over what constitutes a secret and how it is prioritized.
- Automatic Secret Revocation via Provider APIs: This planned feature is a game-changer for incident response. Upon detection of a valid, exposed secret, Betterleaks could, through integration with various provider APIs (e.g., AWS, GitHub, GCP), automatically initiate the revocation process for that credential. This capability would drastically reduce the mean-time-to-remediation (MTTR) for secret leaks, effectively neutralizing threats almost instantaneously and minimizing the window of exposure that attackers could exploit.
- Permissions Mapping: Understanding what an exposed secret can access is crucial for assessing risk. Permissions mapping would provide context around the scope of an exposed credential, allowing security teams to prioritize remediation efforts based on potential impact.
- Performance Optimizations: The commitment to continuous performance enhancement ensures that Betterleaks will remain efficient and scalable as codebases grow and scanning demands intensify.
Governance, Community, and AI-Driven Workflows
Betterleaks operates under the permissive MIT license, a cornerstone of open-source development that encourages broad adoption and collaborative enhancement. The project’s governance model, extending beyond its primary author to include contributors from major enterprises like the Royal Bank of Canada, Red Hat, and Amazon, underscores its commitment to community-driven development and enterprise-grade reliability. This diverse input ensures that the tool addresses a wide array of real-world security challenges faced by organizations of all sizes.
A particularly salient aspect of Betterleaks’ design philosophy is its dual focus on "human-centric use with accommodation for AI agent workflows." This forward-looking approach acknowledges the increasing role of artificial intelligence in code generation and development processes. As AI copilots and automated development tools become more prevalent, they too can inadvertently introduce secrets. Betterleaks is being engineered with CLI features specifically optimized for integration into automated pipelines and for scanning AI-generated code, ensuring that the security perimeter extends to these emerging development paradigms. This strategic foresight positions Betterleaks as an indispensable tool in an increasingly automated and AI-driven software development landscape.
Implications for the DevSecOps Landscape
The introduction of Betterleaks marks a pivotal moment for DevSecOps practices. For developers, it offers a powerful yet unobtrusive tool that integrates seamlessly into their daily workflows, providing immediate feedback on potential security flaws. For security engineers, it provides enhanced visibility, improved accuracy, and a pathway to automated remediation, thereby freeing up valuable resources for more strategic security initiatives. For organizations, it signifies a stronger defense against one of the most common and impactful attack vectors, contributing to a more resilient software supply chain and bolstering overall cybersecurity posture. By continuously evolving and incorporating cutting-edge technologies like LLM-assisted analysis and automated revocation, Betterleaks is poised to redefine the standard for secrets detection, offering a proactive and intelligent shield against the ever-present threat of exposed credentials.