The Spanish Ministry of Science, Innovation and Universities has initiated a significant partial shutdown of its information technology infrastructure, leading to the suspension of numerous public-facing and institutional services. This decisive action follows an undisclosed "technical incident" that has been subsequently linked to claims of a substantial data breach by a purported cyber-attacker, threatening the integrity of sensitive information entrusted to the governmental body.
The Ministry, formally known as Ministerio de Ciencia, Innovación y Universidades, is a pivotal institution within the Spanish government, tasked with steering national policy across critical domains including scientific research, technological innovation, and higher education. Its operational scope extends to managing intricate administrative systems that are indispensable for a vast network of stakeholders, including academics, research institutions, universities, and students. These platforms are repositories for an extensive array of high-value and personally identifiable information, making their security paramount. The abrupt curtailment of these digital services signals a serious disruption, impacting vital processes from grant applications to academic registrations.
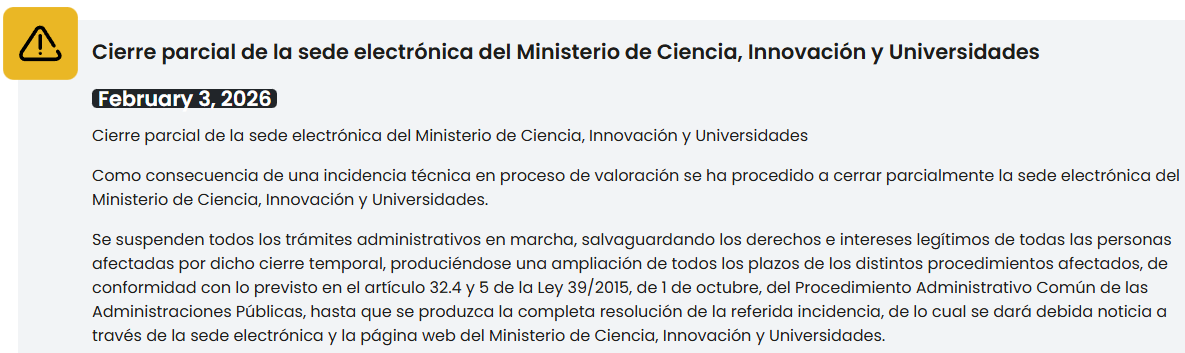
In an official statement disseminated via its primary web portal, the Ministry acknowledged the partial closure of its electronic headquarters, citing an ongoing assessment of the "technical incident." The communication further clarified that all active administrative procedures would be temporarily halted, with assurances that the rights and legitimate interests of all affected individuals would be safeguarded during this period of operational suspension. To mitigate the immediate consequences for applicants and institutions, the Ministry confirmed that all deadlines pertinent to the impacted procedures would be automatically extended, invoking the provisions outlined in Article 32 of Law 39/2015, which governs administrative procedures in Spain. This legislative provision typically allows for the suspension of administrative terms when circumstances beyond the control of the administration or interested parties prevent their normal progression, underscoring the gravity of the disruption.
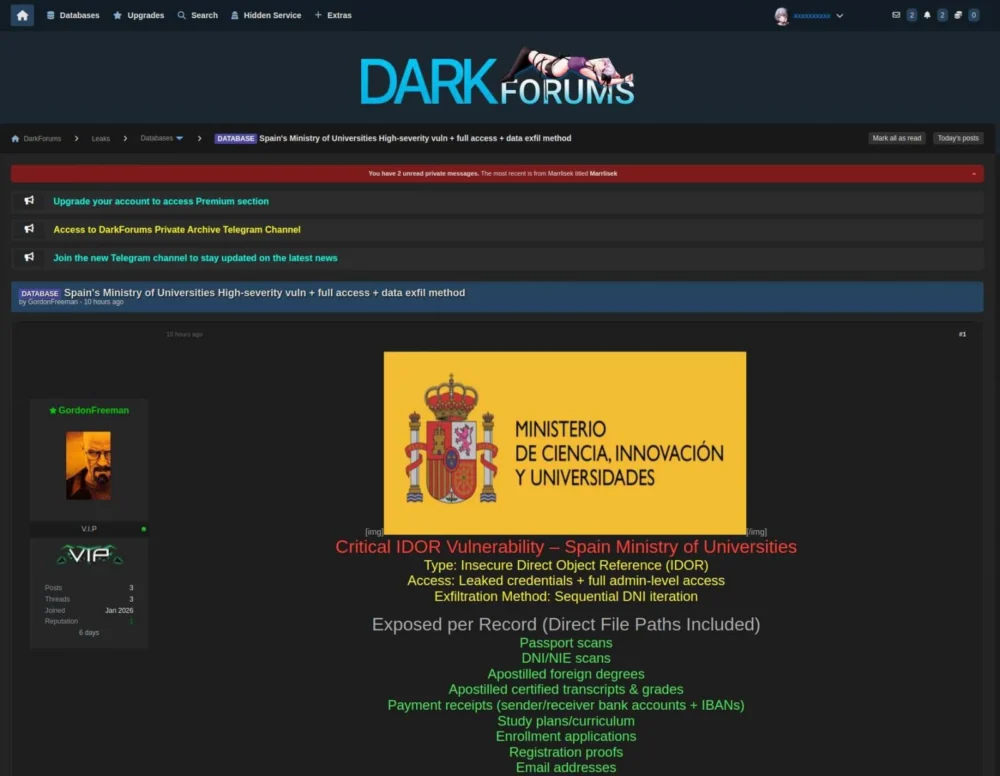
Concurrently with the Ministry’s official, albeit circumspect, announcement, an individual operating under the pseudonym "GordonFreeman," a reference to the protagonist of the popular Half-Life video game series, surfaced on underground digital forums. This individual asserted responsibility for an intrusion into the Spanish Ministry’s systems and proceeded to disseminate samples of data purportedly exfiltrated during the alleged cyberattack. The leaked samples, presented as irrefutable evidence of the breach, reportedly encompass a range of highly sensitive information. This includes personal records, electronic mail addresses, application forms for various enrollments, and visual documentation in the form of screenshots depicting internal documents and other official governmental paperwork. The nature of these samples, if authenticated, suggests a compromise of significant depth, potentially exposing a wide spectrum of personal and institutional data.

The self-proclaimed perpetrator detailed the methodology employed for the alleged infiltration, asserting that the breach was facilitated by exploiting a critical Insecure Direct Object Reference (IDOR) vulnerability. According to "GordonFreeman," this specific weakness granted them "full-admin-level access" to the Ministry’s systems. An IDOR vulnerability arises when an application exposes a direct reference to an internal implementation object, such as a file, directory, or database record, without adequately verifying user authorization. If exploited, an attacker can manipulate these references to access or modify resources they are not permitted to view, potentially leading to unauthorized data exposure or administrative control, as claimed in this instance. The assertion of "full-admin-level access" implies a comprehensive compromise, allowing for widespread data exfiltration and potentially deeper system manipulation.
However, the digital footprint of the threat actor’s claims has shown volatility. Reports indicate that the specific forum where "GordonFreeman" initially published the alleged stolen data and claims has since gone offline. As of now, the purported data has not yet reappeared on alternative illicit platforms, introducing a layer of uncertainty regarding the attacker’s intentions and the full scope of the alleged compromise. While the visual integrity of the leaked images appears credible, independent verification of their authenticity, as well as the attacker’s broader claims regarding the extent of the breach and the method of exploitation, remains challenging. Official confirmation from the Ministry regarding these specific allegations was not immediately forthcoming, reflecting the cautious and often protracted nature of governmental incident response. Nevertheless, media outlets within Spain have cited Ministry spokespersons who have reportedly affirmed that the ongoing IT system disruption is indeed a direct consequence of a cyberattack, thereby lending credence to the threat actor’s claims despite the lack of granular official details.
Broader Context and Analytical Perspective
This incident at the Spanish Ministry of Science, Innovation and Universities is not an isolated event but rather indicative of a pervasive and escalating global trend of cyberattacks targeting governmental bodies and academic institutions. These entities represent highly attractive targets for a diverse array of threat actors, including state-sponsored groups, financially motivated cybercriminals, and hacktivists. The allure lies in the vast repositories of valuable data they possess, ranging from intellectual property and cutting-edge research to sensitive personal information of citizens, researchers, and students, all of which can be monetized, exploited for espionage, or leveraged for disruptive political agendas.

The alleged exploitation of an Insecure Direct Object Reference (IDOR) vulnerability to achieve "full-admin-level access" highlights potential systemic weaknesses in the Ministry’s application security posture. Such vulnerabilities often stem from insufficient secure coding practices, inadequate security testing during development lifecycles, and a lack of robust access control mechanisms. For an IDOR to grant full administrative privileges suggests a critical failure in the fundamental design and implementation of the targeted web application, potentially allowing a relatively straightforward manipulation to escalate into a full-scale system compromise. This points to a need for more rigorous security audits, penetration testing, and continuous vulnerability management programs within governmental IT infrastructures.
The implications of such a breach are multi-faceted and severe. For the individuals whose personal records, email addresses, and enrollment applications may have been exposed, the risks include identity theft, sophisticated phishing attacks, and potential financial fraud. The compromise of official documentation further exacerbates these risks, as attackers could leverage verified governmental paperwork for more convincing social engineering schemes or to facilitate further illicit activities.
Beyond individual harm, the institutional ramifications are significant. A data breach of this magnitude can inflict substantial reputational damage on the Ministry and the Spanish government as a whole, eroding public trust in their ability to secure sensitive information. Furthermore, it could trigger investigations by data protection authorities, potentially leading to substantial regulatory fines under frameworks such as the General Data Protection Regulation (GDPR), given the handling of personal data of EU citizens. The disruption to administrative procedures also carries an economic cost, impacting research funding cycles, academic admissions, and various other processes vital to the nation’s scientific and educational advancement.
From a national security perspective, a Ministry of Science is a repository of strategic information. While the precise nature of the compromised data is yet to be fully disclosed, the possibility exists that information pertaining to national research priorities, classified scientific projects, or critical infrastructure-related academic endeavors could have been accessed. Such data could be invaluable to foreign intelligence agencies or industrial competitors, potentially undermining Spain’s competitive edge and national security interests.
Incident Response and Future Outlook
The Ministry’s initial response, involving a partial system shutdown and extension of deadlines, aligns with immediate containment strategies designed to prevent further data exfiltration and mitigate operational disruption. However, a comprehensive incident response plan would typically involve detailed forensic analysis to ascertain the full scope of the breach, identify the precise entry points, and understand the extent of data compromise. This would be followed by eradication of the threat, recovery of affected systems, and a post-incident review to implement lessons learned and strengthen cybersecurity defenses.
This incident will undoubtedly serve as a catalyst for enhanced cybersecurity measures within the Ministry and potentially across other Spanish governmental departments. It underscores the critical need for a proactive and adaptive approach to cyber defense, moving beyond reactive measures to embrace continuous monitoring, threat intelligence integration, and robust employee training programs. The increasing complexity of IT environments, particularly those interconnected with external academic and research networks, presents unique challenges that demand sophisticated security architectures and a culture of cybersecurity awareness.
The long-term consequences of this alleged breach could include sustained monitoring requirements for affected individuals and a prolonged period of rebuilding trust. As cyber threats continue to evolve in sophistication and frequency, governmental institutions worldwide face an ongoing imperative to invest significantly in their digital resilience. The Spanish Ministry of Science, Innovation and Universities now confronts the arduous task of not only recovering from the immediate impact of this incident but also fortifying its defenses against future, inevitably more advanced, cyber adversaries. The resolution of this situation will be closely watched, offering insights into the broader challenges of securing critical national digital infrastructure in an increasingly hostile cyber landscape.







