A sophisticated and deeply concerning wave of physical phishing attacks has emerged, specifically designed to compromise the digital assets of cryptocurrency hardware wallet owners by impersonating leading manufacturers Trezor and Ledger through postal mail. These elaborate schemes exploit both psychological vulnerabilities and potentially compromised personal data, guiding unsuspecting recipients toward malicious online platforms engineered to illicitly acquire their critical recovery phrases.
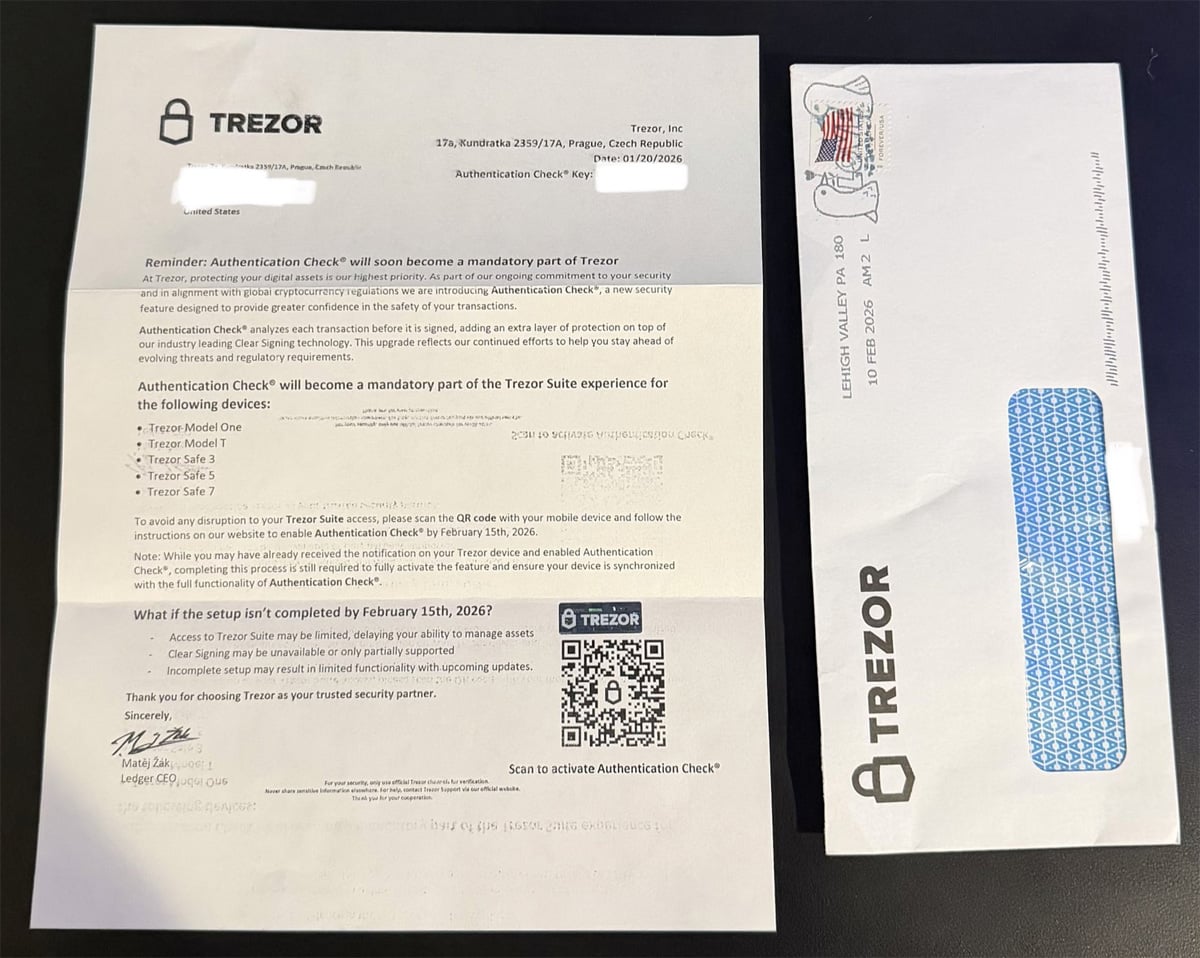
The innovative shift from purely digital attack vectors to tangible, physical mail represents a calculated escalation in cybercrime methodology. Threat actors are meticulously crafting letters that mimic official communications from Trezor and Ledger’s security and compliance departments. These documents are printed on what appears to be authentic letterhead, bearing hallmarks of legitimate corporate correspondence. The primary objective is to instil a sense of urgency and obligation, compelling users to undertake a purported "Authentication Check" or "Transaction Check" to avert the disabling of their wallet functionalities or loss of access to their funds. A critical component of this deception is the inclusion of QR codes, which serve as a deceptive bridge, seamlessly transporting victims from the physical letter into a meticulously constructed digital trap.
The Modus Operandi: Snail Mail as a Gateway to Crypto Theft

Reports from hardware wallet users detail the receipt of these highly deceptive physical letters. The professionalism of the print, the careful formatting, and the use of official-sounding departmental names are all designed to disarm recipients and lend an air of legitimacy to the fraudulent demands. This tactical choice to leverage physical mail bypasses many of the automated spam filters and security protocols that typically intercept email-based phishing attempts, granting these campaigns a unique avenue directly into the homes and hands of potential victims.
While the precise criteria for target selection remain subject to ongoing analysis, cybersecurity experts strongly postulate a connection to previous data breaches experienced by both Trezor and Ledger. Trezor, for instance, reported a breach affecting its support site, which exposed personal data of approximately 66,000 customers. Similarly, Ledger has faced multiple incidents, including the leakage of physical addresses for hundreds of thousands of owners on hacker forums, and further impact from a third-party data breach involving Global-e. These past compromises provide a critical foundation for the current physical phishing wave, enabling threat actors to target individuals whose postal addresses and association with these hardware wallet brands are already known, thus significantly increasing the perceived credibility of the unsolicited mail.
Detailed examination of these fraudulent communications reveals a consistent pattern. One letter, impersonating Trezor and intercepted by cybersecurity expert Dmitry Smilyanets, explicitly states that an "Authentication Check" is slated to become a mandatory feature. It warns recipients of impending functional limitations if the process is not completed by a specified date, such as February 15, 2026. The text instructs users to scan a provided QR code with a mobile device and follow subsequent instructions on a designated website. Adding another layer of deception, the letter even preemptively addresses potential confusion, stating, "Note: While you may have already received the notification on your Trezor device and enabled Authentication Check, completing this process is still required to fully activate the feature and ensure your device is synchronized with the full functionality of Authentication Check." This foresight aims to mitigate skepticism from users who might recall having already performed similar legitimate procedures.
A parallel Ledger-themed letter, widely disseminated and shared on platforms like X (formerly Twitter), echoed this deceptive strategy. It announced a mandatory "Transaction Check" and similarly urged users to scan a QR code by a specific deadline, such as October 15, 2025, to avoid service disruptions.

The Digital Trap: From QR Code to Recovery Phrase Exfiltration
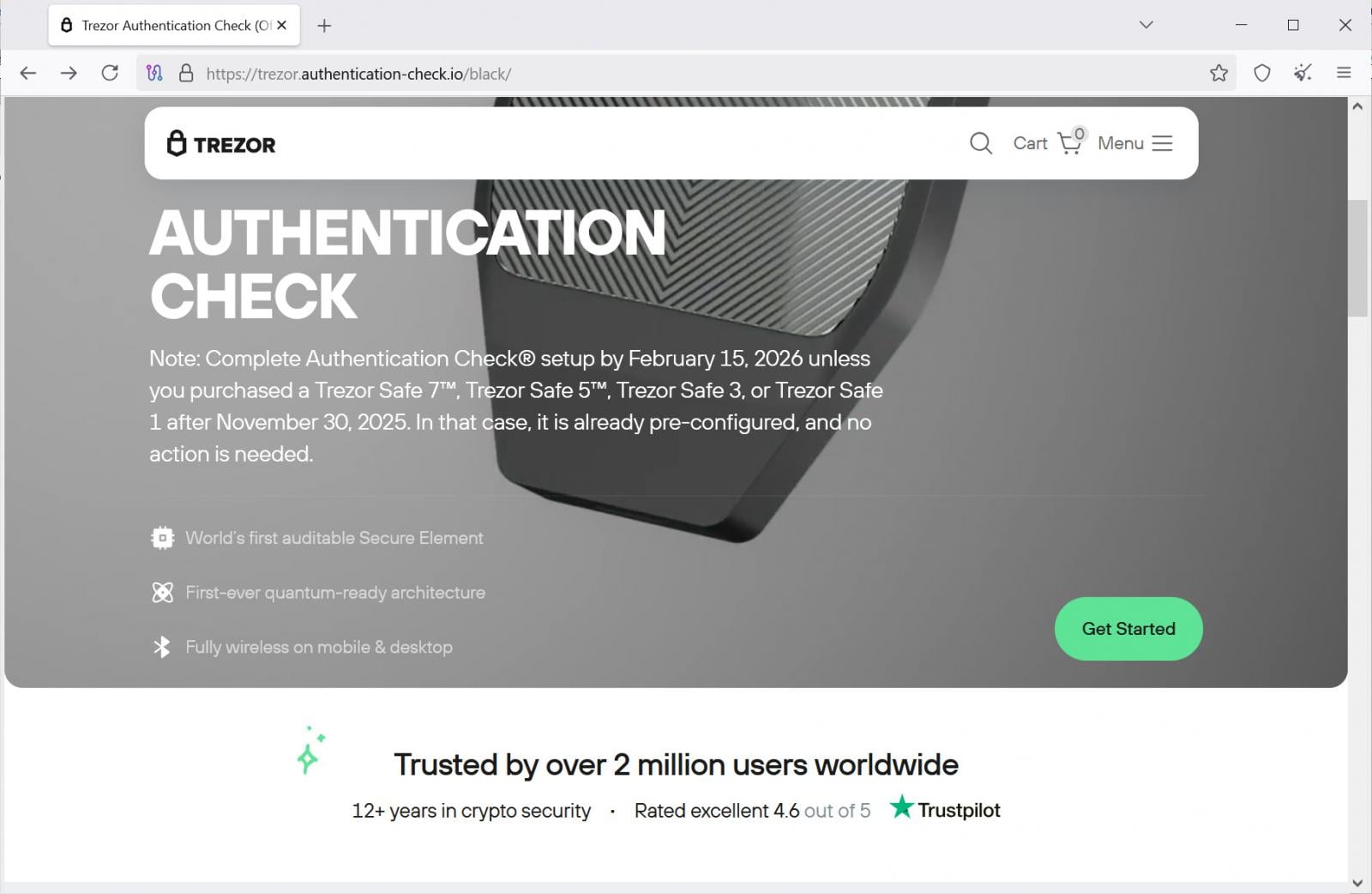
The critical phase of these attacks begins once a user scans the QR code. This action redirects the victim to a meticulously crafted phishing website, expertly designed to mimic the authentic setup or verification pages of Trezor or Ledger. At the time of this analysis, while one Ledger phishing domain had been taken offline, a corresponding Trezor phishing site remained active, albeit flagged by Cloudflare as a known phishing vector.
Upon landing on the Trezor phishing page, victims are confronted with a prominent warning about the impending "Authentication Check" deadline. The site presents a carefully worded exception, noting that newer devices (Trezor Safe 7, 5, 3, or 1 purchased after November 30, 2025) might be pre-configured, thereby subtly validating the urgency for older device owners. Clicking a "Get Started" button initiates a sequence of pages, each reinforcing the narrative of mandatory compliance and dire consequences for non-action. These subsequent pages feature escalating warnings, detailing potential outcomes such as limited or blocked access to Trezor services, transaction signing errors, and disruption with future device updates. This psychological manipulation is expertly designed to amplify anxiety and maintain the victim’s commitment to proceeding with the purported "authentication."
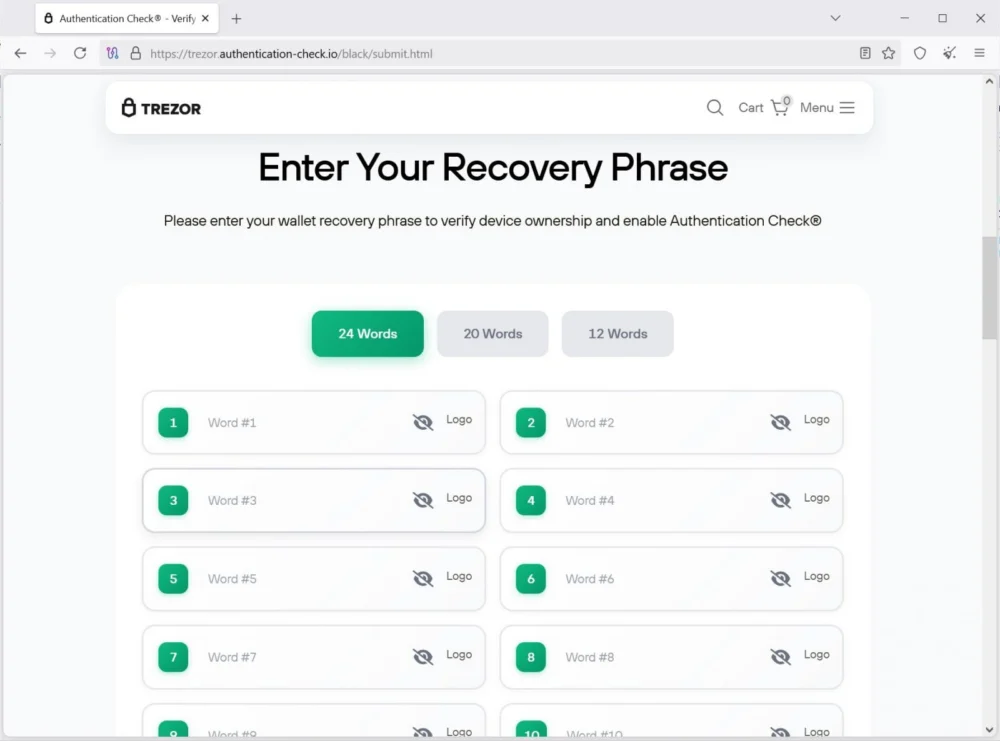
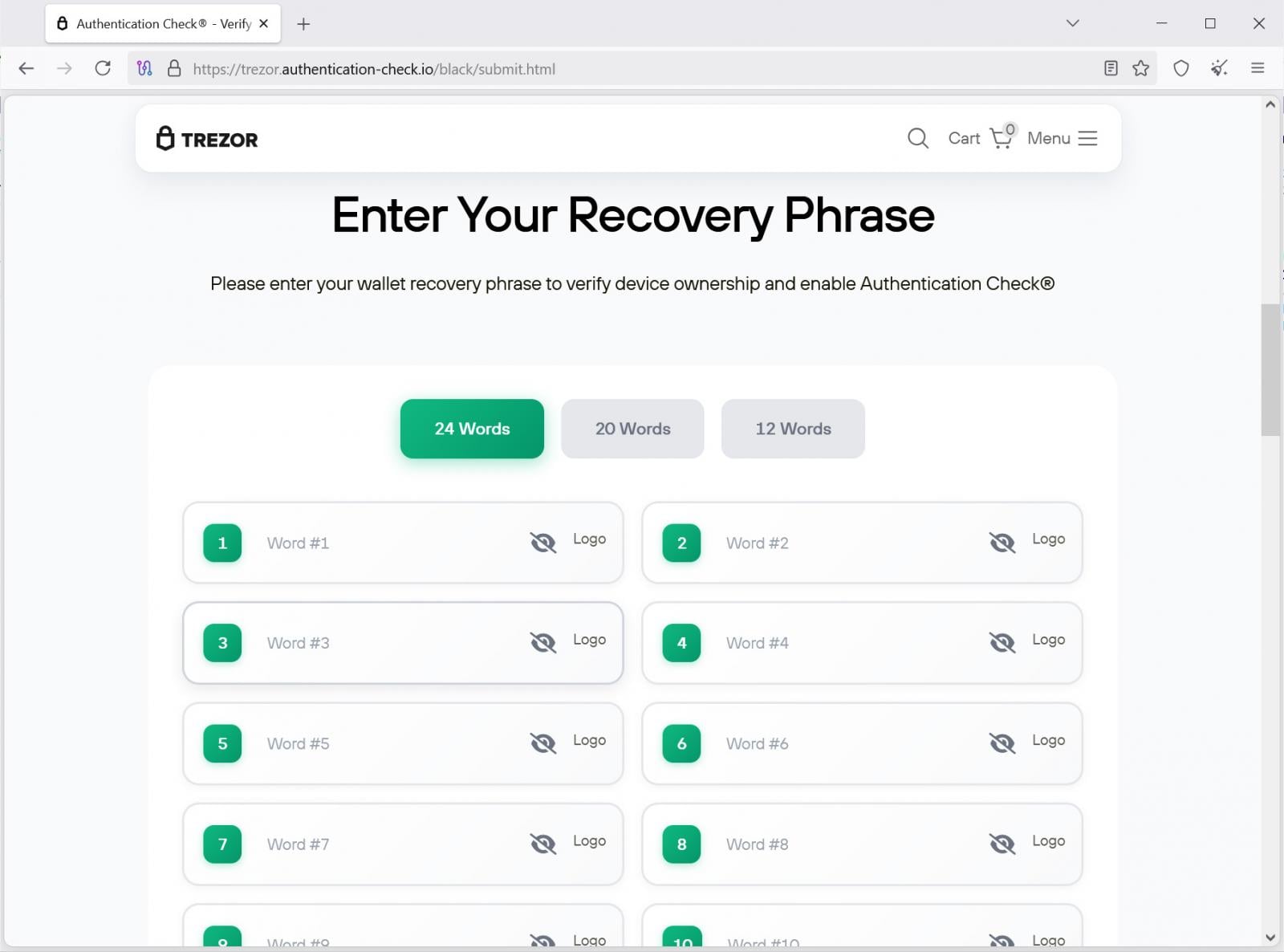
The culmination of this deceptive funnel arrives at a final phishing page, which presents the ultimate objective: a request for the user’s wallet recovery phrase. This page typically offers options for entering 12, 20, or 24-word recovery phrases, falsely asserting that this information is indispensable for verifying device ownership and enabling the new "authentication feature." The moment a victim enters their recovery phrase, this highly sensitive data is immediately transmitted to the threat actor via a backend API endpoint, such as https://trezor.authentication-check[.]io/black/api/send.php. With this phrase in hand, attackers gain complete and irreversible control over the victim’s cryptocurrency wallet, enabling them to swiftly drain all associated funds.
Evolving Threat Landscape: Beyond Digital Phishing
While digital phishing attacks targeting cryptocurrency users, particularly those impersonating Trezor and Ledger, are a persistent and common threat, the re-emergence of physical mail campaigns signifies a notable evolution in attack strategies. This isn’t an entirely novel concept; in 2021, threat actors famously mailed counterfeit Ledger devices pre-modified to steal recovery phrases during the setup process. Another postal phishing campaign specifically targeting Ledger users was documented in April of the current year. The current wave of QR code-enabled letters represents a sophisticated refinement of these earlier physical tactics, leveraging a hybrid approach that combines the perceived legitimacy of physical mail with the scalable efficiency of digital phishing infrastructure.
The efficacy of physical mail in this context stems from several factors. It circumvents the increasingly robust digital security measures (email filters, browser warnings) that users are accustomed to. The tangible nature of a letter can lend a false sense of authenticity that digital messages sometimes lack. Furthermore, by selectively targeting individuals whose addresses are known (likely from past data breaches), these campaigns achieve a level of precision that enhances their chances of success.
The Immutable Rule: Safeguarding Your Recovery Phrase
At the core of hardware wallet security lies the recovery phrase, often referred to as a seed phrase. This sequence of words serves as the master key to a cryptocurrency wallet, deterministically generating all the private keys that control access to digital assets. Consequently, anyone who possesses a wallet’s recovery phrase gains absolute, unfettered control over the wallet and all its stored funds.
It is an unequivocal and non-negotiable principle that legitimate hardware wallet manufacturers, including Trezor and Ledger, will never solicit a user’s recovery phrase under any circumstances. They will not ask for it via email, phone, physical mail, website forms, or any other digital or verbal medium. The design philosophy of these devices dictates that the recovery phrase should only ever be entered directly onto the hardware wallet device itself, and solely for the purpose of restoring a wallet onto a new or reset device.
Users must adopt a vigilant stance:
- Never share: Under no circumstances should a recovery phrase be entered into a computer, mobile device, or any website.
- Offline Storage: Recovery phrases should be meticulously recorded and stored offline in a secure, private location, ideally away from the hardware wallet itself.
- Verify Communications: Always verify the authenticity of any communication, especially those demanding urgent action or sensitive information, by independently contacting the official support channels of the hardware wallet manufacturer through their verified website, not through links or contact information provided in suspicious mail.
- Skepticism: Treat any unsolicited communication regarding your hardware wallet with extreme skepticism, regardless of its apparent legitimacy.
Broader Implications and Future Outlook
This latest wave of physical phishing campaigns underscores the escalating sophistication and adaptability of cybercriminals in the cryptocurrency ecosystem. As digital security measures improve, threat actors are compelled to explore alternative, often more elaborate, attack vectors. The blending of physical and digital components in these scams presents a significant challenge for user education and cybersecurity awareness, as it requires individuals to be vigilant across multiple dimensions.
For hardware wallet manufacturers, these incidents highlight the continuous imperative to reinforce security communications, educate their user base about never sharing recovery phrases, and actively collaborate with cybersecurity intelligence firms to track and disrupt these evolving threats. The long-term implications of data breaches, specifically the leakage of personal identifiers like physical addresses, will continue to serve as fertile ground for such hybrid attacks, necessitating a holistic approach to data protection and incident response across the industry. As the digital asset landscape matures, the convergence of physical and digital attack surfaces will likely intensify, demanding heightened vigilance and robust security practices from both users and industry stakeholders.








