A recent escalation in the GlassWorm malware campaign has revealed a highly targeted strategy aimed at macOS users, leveraging trojanized extensions within the OpenVSX marketplace to illicitly obtain sensitive data, including financial credentials, cryptocurrency wallet details, and critical developer assets. This latest iteration underscores a growing threat to the software supply chain, specifically targeting the tools and environments relied upon by developers.
The GlassWorm campaign represents a persistent and evolving threat, first emerging in the latter half of October. Early manifestations of the malware primarily focused on exploiting both Microsoft’s official Visual Studio Code marketplace and its open-source counterpart, OpenVSX, by embedding malicious code. Initial attack vectors utilized deceptive techniques, such as concealing malicious payloads within "invisible" Unicode characters, to evade detection while targeting cryptocurrency wallet and developer account credentials. Beyond data theft, these early variants demonstrated capabilities for VNC-based remote access and SOCKS proxying, indicating a broader intent for system control and covert network operations.
Over successive waves, the GlassWorm threat actors have demonstrated a notable capacity for adaptation and refinement of their tactics. Subsequent campaigns broadened their impact across both major VS Code extension platforms, continually refining their stealth and targeting mechanisms. A significant evolutionary leap was observed in a prior campaign that specifically set its sights on macOS environments, showcasing the attackers’ dedication to expanding their operational scope. This particular phase also revealed active development efforts to integrate mechanisms for replacing legitimate cryptocurrency applications, such as Trezor and Ledger, with malicious counterparts, indicating a clear intent to directly intercept and misdirect digital asset transactions. The consistent evolution of GlassWorm highlights a well-resourced and determined adversary, continuously seeking new vulnerabilities and advanced evasion techniques.

The OpenVSX Registry, an open-source alternative to the Visual Studio Code Marketplace, serves as a critical repository for extensions compatible with various IDEs, particularly those not officially supported by Microsoft. Its open nature, while fostering innovation and accessibility, can also present unique security challenges. The recent GlassWorm attack highlights how this open ecosystem can be exploited as a supply chain vector. By compromising a legitimate developer account and injecting malicious code into widely used extensions, attackers can bypass traditional security controls and directly infiltrate the development environments of unsuspecting users. The trust inherent in developer tools makes this attack vector particularly potent, as users often assume the integrity of extensions found in established registries.
The latest campaign, detailed in a recent security assessment, provides a granular look at the attackers’ current modus operandi. The threat actors successfully gained unauthorized access to the account of a verified developer, identified as "oorzc." This compromise enabled them to push malicious updates containing the GlassWorm payload to four extensions that collectively boasted over 22,000 downloads prior to their neutralization. These extensions, which had maintained an innocuous operational history for approximately two years, included oorzc.discord-theme, oorzc.github-theme, oorzc.ssh-tools, and oorzc.spotify-tools. The long period of benign activity for these extensions strongly suggests that the oorzc account itself was compromised, rather than the developer intentionally distributing malware. This account takeover represents a classic supply chain attack, where trust in a legitimate entity is weaponized to distribute malware.
Forensic analysis indicates that the malicious updates were deployed on January 30th. Upon execution, the GlassWorm payload initiated a highly targeted information-stealing operation, exclusively designed for macOS systems. A distinctive feature of this campaign is its command and control (C2) communication mechanism, which leverages Solana transaction memos. This method allows the malware to retrieve instructions from seemingly benign blockchain transactions, providing a highly decentralized, resilient, and stealthy C2 channel that is difficult to detect and block using traditional network monitoring techniques.

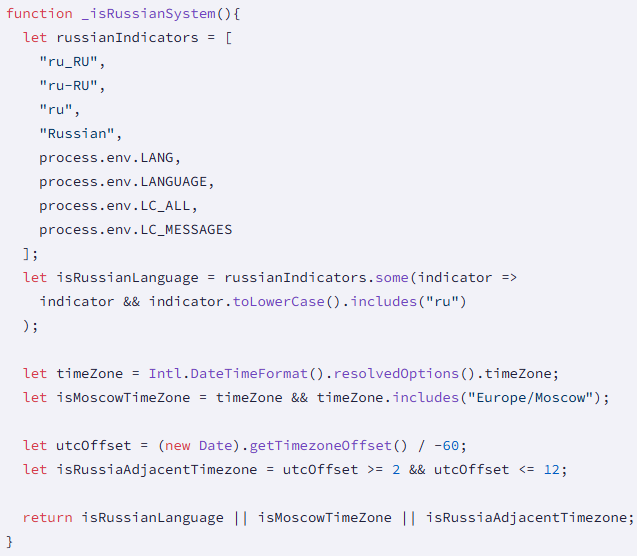
Furthermore, a notable operational directive within the malware explicitly excludes systems configured with a Russian locale from its execution. This geo-fencing characteristic is frequently observed in malware originating from nation-states or criminal groups operating within specific geopolitical boundaries, potentially hinting at the attacker’s origin or their self-imposed operational constraints. Such exclusions are often designed to avoid internal prosecution or to adhere to specific "rules of engagement" set by the threat actor’s handlers or local laws.
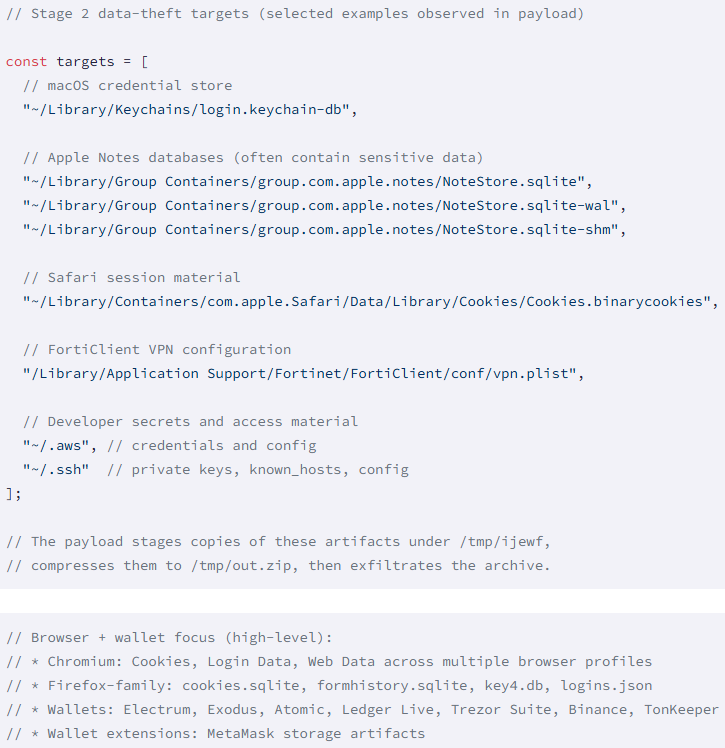
Upon successful infiltration, GlassWorm establishes persistence on the compromised macOS system by deploying a LaunchAgent. This mechanism ensures that the malware executes automatically upon system login, thereby maintaining its presence even after reboots. The primary objective of this persistent foothold is extensive data exfiltration. The malware is engineered to systematically harvest a broad spectrum of highly sensitive information, including:
- Browser Data: Comprehensive harvesting of credentials, browsing history, and cookies from both Firefox and Chromium-based browsers, which are often rich repositories of user authentication data.
- Wallet Data: Targeting of both cryptocurrency browser extensions and standalone desktop wallet applications, a direct continuation of the attacker’s interest in digital assets.
- macOS Keychain Data: Accessing the macOS Keychain, a secure database storing passwords, private keys, and certificates, which can yield an extensive array of user and system credentials.
- Apple Notes Databases: Extracting data from Apple Notes, which frequently contains sensitive personal or professional information, including financial details, project plans, and confidential communications.
- Safari Cookies: Collection of Safari browser cookies, potentially enabling session hijacking and unauthorized access to online accounts.
- Developer Secrets: A particularly critical target, this includes API keys, access tokens, configuration files, and other credentials vital for software development, which could be used to access code repositories, cloud infrastructure, or deploy further malicious code.
- Local Filesystem Documents: Broad exfiltration of documents from the local filesystem, indicating an intent to steal intellectual property, confidential business documents, or any other valuable data stored locally.
All harvested data is then exfiltrated to the attacker’s infrastructure, specifically identified as 45.32.150[.]251. This IP address serves as the central collection point for the vast amounts of sensitive information stolen from compromised macOS developer systems.
The implications of such an attack are profound, extending far beyond individual financial loss. For developers, the compromise of credentials and intellectual property can lead to devastating consequences, including:
- Supply Chain Contamination: Stolen developer credentials can be used to inject malicious code into legitimate software projects, leading to widespread downstream compromise for customers.
- Intellectual Property Theft: The exfiltration of project documents and source code can result in the loss of proprietary information, impacting competitive advantage and long-term business viability.
- Financial Ruin: Theft of cryptocurrency and banking credentials can lead to immediate and substantial financial losses.
- Reputational Damage: Developers and organizations associated with compromised extensions can suffer significant reputational harm, eroding trust within the community.
The broader security landscape faces increasing challenges from supply chain attacks. As software development becomes increasingly reliant on third-party components and open-source contributions, the attack surface expands exponentially. The GlassWorm campaign serves as a stark reminder that even seemingly benign tools like IDE extensions can become vectors for sophisticated malware, underscoring the critical need for enhanced security measures throughout the software development lifecycle.
Upon discovery, Socket’s security team promptly reported the malicious packages to the Eclipse Foundation, the governing body of the OpenVSX platform. Their swift response was crucial in mitigating the ongoing threat. The Eclipse Foundation’s security team confirmed unauthorized publishing access, subsequently revoking the compromised tokens and systematically removing the malicious releases from the registry. A notable exception was oorzc.ssh-tools, which, due to the discovery of multiple malicious releases over time, was completely purged from OpenVSX, reflecting the severe nature of its compromise.
Currently, all affected extensions available on the OpenVSX marketplace are verified as clean. However, the transient nature of such attacks means that developers who downloaded and installed the malicious versions during the active period remain at risk. For any developer who may have installed these compromised extensions between January 30th and their removal, immediate and decisive action is imperative. This includes conducting a thorough system clean-up to eradicate any lingering malware components and, critically, rotating all passwords, API keys, and other sensitive secrets. Given the malware’s comprehensive data exfiltration capabilities, assuming a full compromise of all accessible credentials is the safest course of action.
Looking forward, the GlassWorm campaign epitomizes the evolving sophistication of adversaries targeting the developer ecosystem. The shift towards macOS, the use of blockchain for C2, and the continuous refinement of data exfiltration techniques highlight a persistent threat that demands proactive and adaptive defensive strategies. Organizations and individual developers must adopt a security-first mindset, implementing measures such as multi-factor authentication for all developer accounts, rigorous code review processes, continuous monitoring of development environments for anomalous activity, and the principle of least privilege. Furthermore, platforms like OpenVSX must continue to enhance their security frameworks, including more robust developer verification processes and automated scanning for malicious code within submitted extensions, to fortify the software supply chain against such insidious attacks. The ongoing battle against malware like GlassWorm necessitates a collaborative and vigilant approach from all stakeholders in the software development community.