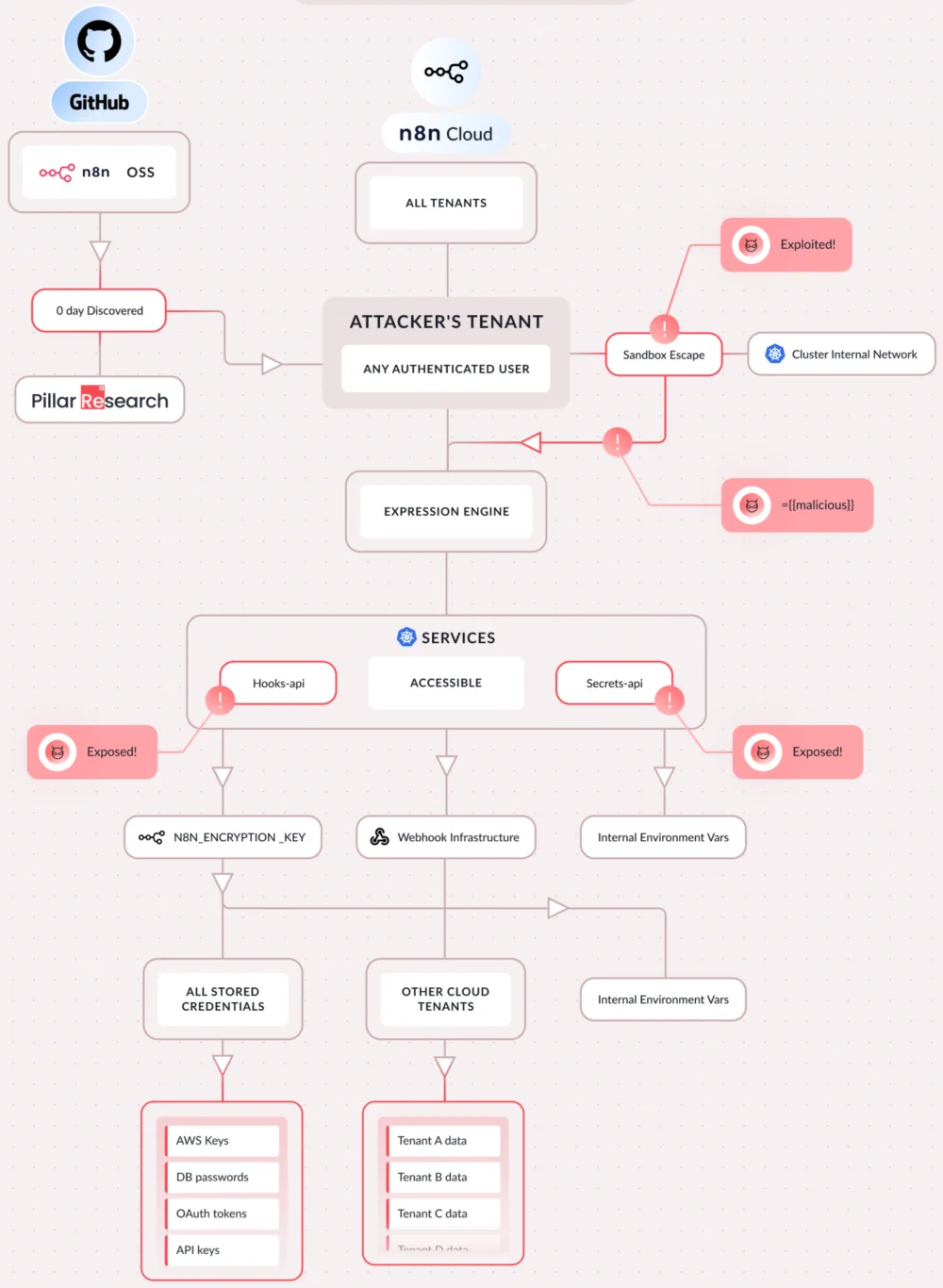
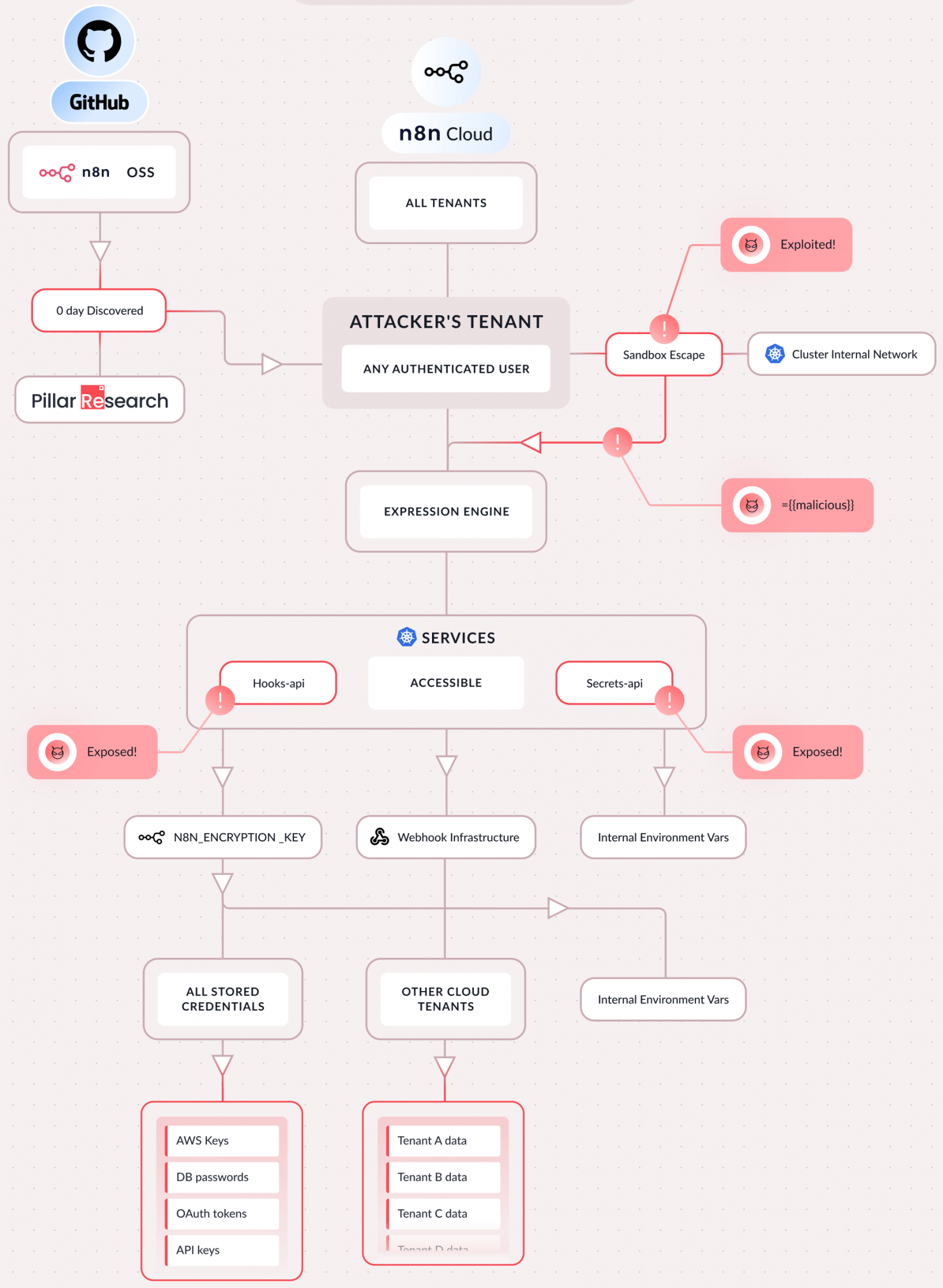
A series of critical security vulnerabilities have been identified within the n8n open-source workflow automation platform, enabling authenticated attackers to bypass security mechanisms, achieve complete remote code execution (RCE) on host servers, and gain unfettered access to sensitive corporate assets. These profound weaknesses, collectively designated CVE-2026-25049, underscore the persistent challenges in securing complex, extensible software environments that facilitate deep system integrations and custom scripting. The disclosure is accompanied by the availability of public exploit proofs-of-concept, elevating the immediate risk to organizations utilizing n8n.
The core of the problem lies in n8n’s internal sanitization and sandboxing mechanisms, which were found to be insufficient in preventing malicious code execution. Specifically, the vulnerabilities allow any user with privileges to create or modify workflows to break out of the intended execution environment. This critical breach of isolation enables an attacker to execute arbitrary commands directly on the underlying server, thereby bypassing the platform’s security controls and gaining full control over the n8n instance and potentially interconnected systems. This represents a significant security incident for any enterprise relying on n8n for automating critical business processes, especially given the platform’s increasing adoption for integrating disparate services and managing data flows.
Expert security researchers from multiple firms, including Pillar Security, Endor Labs, and SecureLayer7, independently identified and reported these flaws. Their investigations revealed that the vulnerabilities were not merely new exploits but also represented a bypass for a previously patched critical flaw, CVE-2025-68613, which was addressed in late December. This indicates an ongoing struggle to fully contain and mitigate complex security issues within the n8n codebase, particularly those related to user-supplied code execution and data sanitization. The iterative discovery of bypasses highlights the intricate nature of securing environments where user-defined logic directly interacts with system resources.
The potential ramifications of CVE-2026-25049 are extensive and severe. A successful exploitation grants an attacker the ability to compromise the entire n8n instance. This includes, but is not limited to, the theft of all stored credentials, secrets such as API keys and OAuth tokens, and sensitive configuration files essential for system operation. Beyond data exfiltration, attackers can leverage this access to manipulate the filesystem, interact with internal network systems, and pivot into connected cloud accounts. For organizations heavily invested in cloud infrastructure, this presents a direct pathway to broader network compromise, data breaches, and service disruption across their digital estate.

A particularly concerning aspect of this vulnerability for modern enterprises is its impact on artificial intelligence (AI) workflows. Many organizations utilize n8n to orchestrate AI models, handle data ingestion for machine learning, and manage outputs. An attacker exploiting CVE-2026-25049 could hijack these AI workflows, intercepting prompts, modifying responses, and redirecting sensitive data traffic. This could lead to intellectual property theft, data poisoning of AI models, or the injection of malicious instructions, fundamentally undermining the integrity and trustworthiness of AI-driven operations.
Furthermore, n8n often operates in multi-tenant environments, where a single instance serves multiple isolated users or departments. The ability to access internal cluster services through this vulnerability raises the alarming prospect of lateral movement, allowing an attacker to potentially pivot from one compromised tenant’s data to that of other tenants within the same n8n deployment. This magnifies the risk profile for service providers and larger organizations operating shared n8n instances, transforming a single user’s vulnerability into a systemic risk. Pillar Security’s analysis succinctly captured the ease of exploitation, stating that "The attack requires nothing special. If you can create a workflow, you can own the server," underscoring the low bar for a successful compromise by an authenticated user.
The technical underpinnings of the vulnerability stem from what Pillar Security described as "incomplete AST-based sandboxing." This refers to the platform’s weak sandboxing of user-written server-side JavaScript expressions within workflows. Abstract Syntax Tree (AST) analysis is a common technique used to analyze and sanitize code before execution. However, the researchers demonstrated a chained bypass to the n8n team in December, enabling a sandbox escape and direct access to the Node.js global object, which subsequently leads to RCE. Although an initial fix was deployed, Pillar Security’s subsequent analysis revealed its incompleteness, identifying a second escape vector using equivalent operations. This iterative process of discovery and patching highlights the inherent complexity in developing robust sandboxing for dynamic scripting environments.
Endor Labs’ research corroborated these findings, specifically pointing to sanitization bypasses. Cristian Staicu from Endor Labs explained that prior to versions 2.5.2 and 1.123.17, the sanitization function incorrectly assumed that keys in property accesses would always be strings within attacker-controlled code. While this assumption might have been reflected in TypeScript typings, it was critically not enforced at runtime. This oversight introduced a type-confusion vulnerability, effectively allowing attackers to circumvent the sanitization controls entirely and achieve arbitrary code execution. Their detailed proof-of-concept (PoC) exploit served as a clear demonstration of this critical flaw.

SecureLayer7’s independent discovery and analysis further enriched the understanding of CVE-2026-25049. Their team uncovered the vulnerability while scrutinizing the fix for the previous CVE-2025-68613. Their report details the precise technical method used to achieve server-side JavaScript execution via the Function constructor, a powerful primitive in JavaScript that allows dynamic code evaluation. Their account of over 150 failed attempts before refining a successful bypass underscores the sophisticated nature of these exploits and the persistence required by security researchers to uncover them. SecureLayer7 also provided a comprehensive PoC exploit, complete with detailed steps for setting up a malicious workflow, further facilitating understanding and remediation efforts.
In response to these critical findings, n8n developers released version 2.4.0 on January 12, 2026, followed by versions 1.123.17 and 2.5.2, specifically designed to address the identified issues. For organizations currently utilizing n8n, immediate updates to the latest stable versions are paramount. Beyond patching, Pillar Security strongly advises rotating the N8N_ENCRYPTION_KEY and all credentials stored within the server environment. This post-patch action is crucial to mitigate any potential compromise that might have occurred before the update, as an attacker could have exfiltrated these sensitive keys and credentials. Additionally, administrators should conduct thorough reviews of existing workflows for any suspicious or anomalous expressions that might indicate prior compromise or the presence of malicious code.
For instances where immediate updating is not feasible, the n8n team has provided a temporary mitigation strategy. This workaround, while offering some protection, does not fully eliminate the risk and should only be considered a stop-gap measure until a full update can be performed. Organizations must recognize that temporary mitigations carry inherent risks and should prioritize applying the official patches as quickly as possible.
The timing of these disclosures is particularly relevant given the increasing attention n8n is receiving from both legitimate users and malicious actors. This is evidenced by recent activities targeting n8n deployments related to another significant vulnerability, the "Ni8mare" flaw (CVE-2026-21858). GreyNoise recently reported a surge in potentially malicious activity targeting exposed n8n endpoints vulnerable to Ni8mare, logging over 33,000 requests between January 27 and February 3. While some of this probing might be attributed to legitimate security research, the scanning for the /proc filesystem indicates a clear interest in post-exploitation opportunities, suggesting that threat actors are actively seeking to exploit n8n vulnerabilities for broader system compromise.
This spate of critical vulnerabilities in n8n underscores a broader trend in cybersecurity: the increasing targeting of workflow automation and integration platforms. These platforms, by their very nature, possess high privileges, extensive access to internal and external services, and often handle sensitive data. Their compromise can therefore yield disproportionately high rewards for attackers. The complexity of these systems, often involving custom code execution, numerous third-party integrations, and dynamic scripting, makes them challenging to secure comprehensively. Robust sandboxing, thorough input sanitization, and continuous security auditing are not just best practices but absolute necessities for such platforms.
The incident also highlights the dual nature of open-source software security. While the open nature allows for community scrutiny and rapid identification of flaws, the widespread adoption of such tools in critical enterprise environments means that discovered vulnerabilities can have far-reaching and immediate impacts. As organizations increasingly automate their operations and integrate AI into their workflows, the security posture of the underlying automation platforms becomes a critical factor in overall enterprise resilience. Moving forward, a proactive and layered security approach, encompassing regular patching, stringent access controls, network segmentation, and continuous monitoring for anomalous activity, will be essential for protecting these powerful yet vulnerable automation engines.






