
The pervasive digital transformation of the modern enterprise has fundamentally reshaped the landscape of cybersecurity, moving beyond traditional network perimeters to center on identity as the primary control point; however, an overreliance on user authentication alone has created a critical blind spot, revealing that while identity may no longer be the weakest link, the conditional integrity of access itself remains a pervasive vulnerability. For years, the foundational premise of workforce security hinged on the ability to reliably confirm a user’s identity, assuming that once validated, access could be granted with an acceptable degree of confidence. This logic, a relic of an era dominated by on-premises networks and corporate-owned devices, no longer reflects the intricate, dynamic reality of contemporary enterprise operations or the sophisticated tactics employed by adversaries.
The modern workforce operates without geographical constraints, spanning multiple locations, diverse network infrastructures, and various time zones. Employees seamlessly transition between corporate-issued laptops, personal mobile devices, and even third-party endpoints, each presenting a unique and often fluctuating security posture. Access to critical resources is no longer anchored to a singular, controlled environment or a uniform device profile. Despite this unprecedented flexibility and dispersion, security teams are tasked with maintaining robust protection without impeding productivity or introducing undue friction. The signals traditionally used to inform access decisions—such as user credentials—have become increasingly fragmented, noisy, and, when viewed in isolation, insufficient to establish true trust. Consequently, identity, originally conceived as a gatekeeper, is now being burdened with a scope of responsibility it was never designed to bear independently. While authentication can definitively confirm who a user purports to be, it inherently lacks the granular insight required to assess the dynamic risk associated with that access once device condition, environmental context, and ongoing behavioral patterns are factored in. In today’s complex digital ecosystems, the core challenge is not a systemic failure of identity verification, but rather an overextended reliance on identity as the sole arbiter of trust.
The Inherent Limitations of Identity in a Dynamic Landscape
The distinction between a legitimate user accessing corporate systems from a fully compliant, secure device and the same user attempting connection from an outdated, unmanaged, or potentially compromised endpoint represents a fundamental divergence in risk profiles. Yet, a significant number of prevailing access models continue to treat these disparate scenarios as functionally equivalent. Such frameworks often prioritize identity validation as the primary determinant for granting access, relegating device condition to a secondary, often static, or entirely overlooked consideration. This approach critically fails to account for the fluid nature of device risk, which can degrade rapidly and unpredictably following initial authentication. Endpoints are not static entities; their security state can shift continuously as configurations drift, necessary security controls are inadvertently or maliciously disabled, critical updates are delayed, or new vulnerabilities emerge – often long after initial access has been provisioned.
When access decisions remain rigidly tied to the conditions observed solely at the moment of login, the initial grant of trust persists, even as the underlying risk posture of the device or environment deteriorates. This creates significant windows of vulnerability. These gaps are particularly pronounced across access pathways that fall outside the purview of modern conditional access frameworks, encompassing legacy protocols, remote access tools (such as Remote Desktop Protocol), and non-browser-based workflows. In these scenarios, access decisions are frequently made with severely limited contextual information, and trust is extended far beyond the point where it can be justifiably maintained.
Sophisticated adversaries have become adept at exploiting these inherent blind spots. Their tactics increasingly pivot towards leveraging misplaced trust rather than expending effort to break robust authentication mechanisms. This often involves the reuse of stolen session tokens, the exploitation of already compromised endpoints, or clever circumvention of multi-factor authentication (MFA) through social engineering or sophisticated phishing techniques. The strategic advantage for attackers is clear: it is often far more efficient and less detectable to log in with valid (though illicitly obtained or leveraged) credentials than to attempt a direct "break-in" against fortified authentication systems. A valid identity presented from a non-compliant or compromised device represents one of the most reliable vectors for bypassing modern security controls and operating stealthily beneath the radar of traditional detection systems.
The Unfulfilled Promise of Zero Trust: The Device Posture Conundrum
The principle of Zero Trust—"never trust, always verify"—has achieved widespread acceptance as a foundational tenet of modern cybersecurity strategy. While significant strides have been made in maturing identity controls within Zero Trust architectures, progress frequently stagnates at the crucial device layer, particularly across access pathways that inherently inherit trust by default, such as those outside modern browser-based or conditional access frameworks.

Establishing comprehensive and continuous device trust introduces a layer of complexity that identity verification alone cannot adequately address. Unmanaged and personal devices, a cornerstone of the modern flexible workforce, present formidable challenges in consistent assessment and enforcement. Compliance checks, even when implemented, often remain static, failing to provide ongoing assurance throughout a user session. Furthermore, the efficacy of enforcement mechanisms can vary dramatically depending on the specific method by which access is initiated (e.g., VPN, SaaS application, direct network access).
These intrinsic challenges are further compounded when identity and endpoint signals are managed by disparate security tools that were not originally designed for seamless interoperability. The inevitable outcome is fragmented visibility across the enterprise landscape and inconsistent access decisions, leading to an uneven security posture. Over time, access policies, once established, can become rigid and static, inadvertently creating fertile ground for identity abuse. When access is granted without subsequent, ongoing verification, traditional security controls are inherently slow to detect and respond to evolving risks or malicious behavior emerging post-authentication. This static approach undermines the core tenet of Zero Trust, which demands continuous, adaptive assessment.
Evolving Beyond Static Identity Checks to Continuous Access Verification
Addressing the pervasive limitations of static, identity-centric access controls necessitates the implementation of dynamic mechanisms that remain effective not only after initial authentication but also adapt continuously as contextual conditions change. The paradigm shift required is from a singular "authentication event" to a model of "continuous access verification." This model extends trust decisions beyond mere identity confirmation, integrating real-time insights into device posture, environmental context, and user behavior to maintain enforcement throughout the entire duration of an access session.
Key measures to close common access failure points, without unduly disrupting legitimate user workflows, include:
-
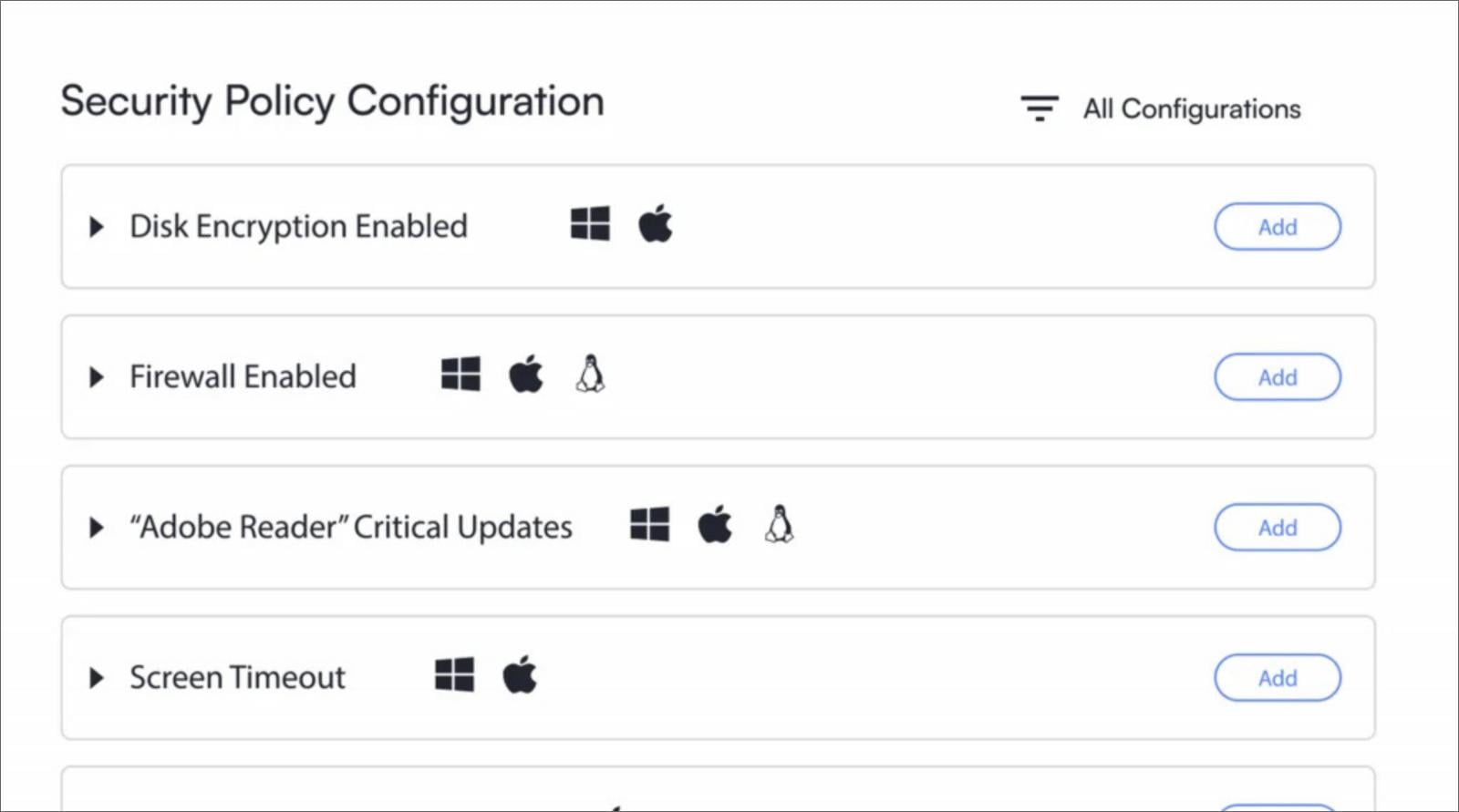
Dynamic Device Posture Assessment: Moving beyond a one-time check at login, this involves continuous monitoring of endpoint health and configuration. This includes verifying operating system and application patch levels, the operational status of security agents (e.g., EDR, antivirus), disk encryption status, adherence to corporate security policies, and the detection of suspicious processes or network connections. Any deviation from a defined baseline automatically triggers a re-evaluation of trust.
-
Contextual Access Policies: Policies must incorporate a broader array of contextual factors beyond just user identity. This includes geographical location (e.g., unusual login location), time of access (e.g., outside normal working hours), network characteristics (e.g., untrusted public Wi-Fi), and the sensitivity of the resource being accessed. A user attempting to access highly sensitive data from an unfamiliar location on an unmanaged device would inherently be flagged as higher risk, regardless of successful identity authentication.
-
Behavioral Analytics: Leveraging machine learning and artificial intelligence to establish baselines of normal user and device behavior. Deviations from these baselines—such as unusual data access patterns, atypical application usage, or sudden changes in network activity—can indicate compromise or malicious intent, triggering adaptive access controls.
-
Adaptive Access Control and Remediation: Instead of a binary "allow or deny" decision, access control becomes fluid. If a device’s posture degrades during a session, or if anomalous behavior is detected, the system can automatically implement graduated responses. This might include requesting step-up authentication (e.g., re-MFA), restricting access to sensitive resources, forcing a device scan, or even temporarily terminating the session. Crucially, systems should also provide clear, actionable remediation guidance to users, allowing them to self-correct device compliance issues (e.g., "Please update your operating system" or "Enable your firewall") to restore full access quickly. This reduces helpdesk burden and empowers users.
-
Unified Security Intelligence: The disparate signals from identity providers, endpoint detection and response (EDR) solutions, network access control (NAC), and security information and event management (SIEM) systems must be consolidated and correlated. A central decision engine, informed by this unified intelligence, can make more accurate and adaptive trust decisions, ensuring consistent policy enforcement across all access points and platforms (Windows, macOS, Linux, and mobile environments).
This proactive model of continuous access verification is essential for operationalizing true Zero Trust principles across the entire workforce. It verifies not only users but also the integrity and posture of their devices at every access point and continuously throughout each session. This holistic approach significantly reduces the attack surface, enhances threat detection capabilities, and provides a resilient security framework capable of adapting to the dynamic threat landscape without hindering the agility of the modern enterprise. The future of workforce security lies in this intelligent convergence, moving beyond static checks to a perpetually vigilant, context-aware defense.







