
A recently identified Linux-based botnet, dubbed SSHStalker, is making waves in the cybersecurity landscape not for its groundbreaking innovation, but for its strategic reversion to the Internet Relay Chat (IRC) protocol for its command and control (C2) communications, a method largely considered a relic of the early internet era. This tactical choice underscores a shift in some threat actor methodologies, prioritizing unparalleled resilience and operational scalability over the stealth and cutting-edge sophistication often associated with modern cyber threats.
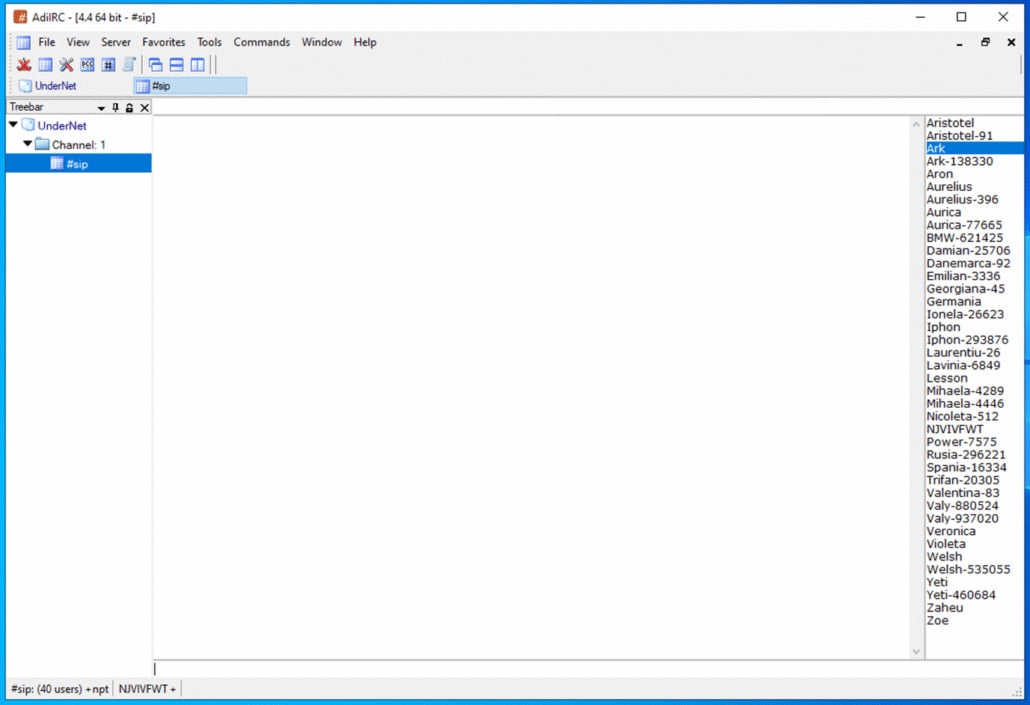
The emergence of SSHStalker highlights a fascinating paradox within contemporary cyber warfare: while the industry often fixates on advanced persistent threats (APTs) employing zero-days and bespoke malware, a significant and highly effective segment of the threat landscape continues to leverage foundational, even archaic, technologies. IRC, conceived in 1988, reached its zenith in the 1990s as the primary text-based instant messaging solution. Despite its decline in mainstream popularity, it has retained a dedicated following within specific technical communities due to its inherent simplicity, robust interoperability, minimal bandwidth requirements, and the absence of a graphical user interface. These very attributes, once appealing to legitimate users, now offer compelling advantages for illicit botnet operations.
SSHStalker’s operational framework leans heavily on classic IRC mechanics, diverging sharply from the complex, bespoke C2 frameworks favored by many modern cybercriminal enterprises. Instead of custom encryption and obfuscation layers, it employs multiple C-based bots and a multi-server/channel redundancy model. This architectural decision consciously sacrifices advanced stealth for superior resilience, broad scalability, and reduced operational costs. According to detailed analyses by threat intelligence experts, this "old-school" philosophy permeates other aspects of SSHStalker’s modus operandi, including its conspicuously noisy SSH scanning techniques, the use of one-minute cron jobs for persistence, and its reliance on a substantial catalog of vulnerabilities, some dating back as far as 15 years. This approach signals a "scale-first" operational strategy, overtly favoring reliability and widespread compromise over intricate evasion tactics.

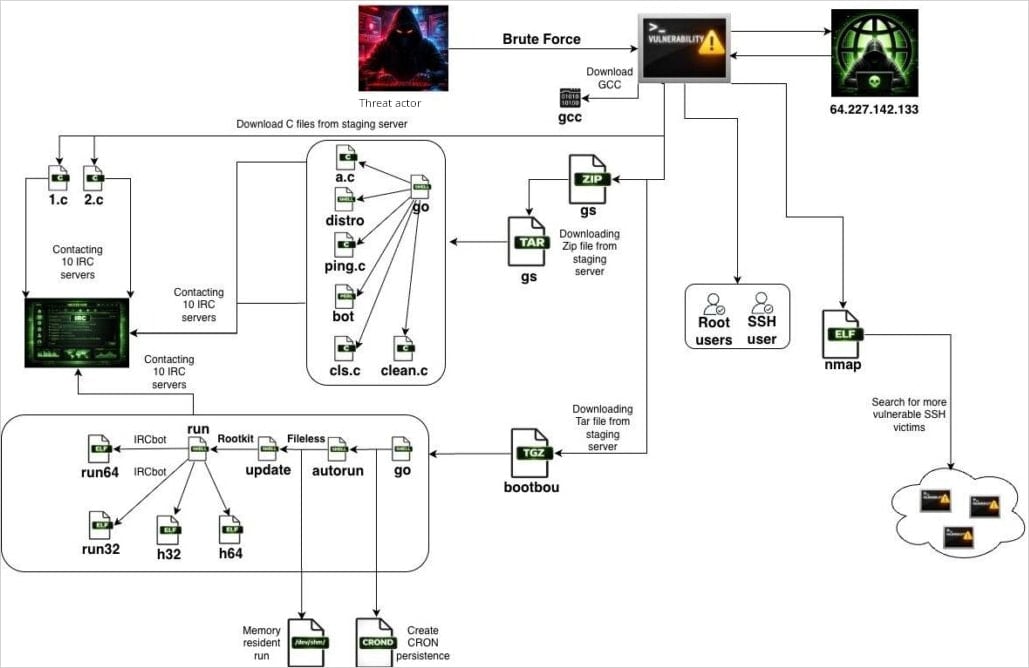
The initial foothold for SSHStalker is typically achieved through automated SSH scanning and brute-force attacks. The botnet utilizes a specially crafted Go binary that cleverly masquerades as nmap, the widely recognized open-source network discovery utility. This deceptive packaging helps it blend into routine network traffic and potentially bypass rudimentary network monitoring systems that might flag unknown executables. Once a host is successfully compromised, it immediately pivots to scanning for additional SSH targets, effectively transforming into a propagation node. This worm-like mechanism allows the botnet to rapidly expand its footprint across vulnerable networks. Initial findings indicate a significant focus on cloud hosting providers, with nearly 7,000 bot scans observed within a single month, predominantly targeting instances within Oracle Cloud infrastructure. This concentration suggests either a strategic targeting of high-value cloud resources or simply a broad sweep of readily accessible public-facing cloud assets.
The infection sequence following initial access is meticulously structured yet pragmatically executed. Upon gaining entry to a victim host, SSHStalker’s primary action is to download the GCC (GNU Compiler Collection) toolchain. This is a critical tactical decision: rather than deploying pre-compiled binaries that might be architecture-specific or easily flagged by signature-based antivirus solutions, the botnet compiles its payloads directly on the victim device. This on-the-fly compilation significantly enhances portability across diverse Linux distributions and kernel versions, while simultaneously complicating detection efforts. The first set of compiled payloads consists of C-based IRC bots, pre-configured with hard-coded C2 server addresses and channel names. These bots are responsible for enrolling the newly compromised host into the botnet’s IRC-based communication infrastructure, establishing a persistent link to the operators.
Following the initial enrollment, the malware proceeds to fetch additional archives, typically named GS and bootbou. These archives contain further bot variants and modules, suggesting a modular architecture designed for orchestration and execution sequencing. This modularity allows the threat actors to dynamically deploy different functionalities or update existing ones without completely re-infecting hosts, providing flexibility in their monetization and attack strategies. Persistence on the compromised system is robustly maintained through cron jobs, scheduled to execute every 60 seconds. This creates a watchdog-style update mechanism, continuously checking for the main bot process. If the process is terminated for any reason—be it manual intervention or system-level detection—the cron job swiftly relaunches it, ensuring the botnet’s presence remains resilient. While effective, the frequent execution of cron jobs from unusual paths is a relatively "noisy" indicator that can be detected by sophisticated monitoring systems.

A key element in SSHStalker’s arsenal for escalating privileges is its reliance on a collection of 16 known Common Vulnerabilities and Exposures (CVEs) specifically targeting Linux kernel versions from the 2009-2010 era. This strategy is particularly effective because, even in an era of rapid software development, a significant number of legacy systems, unpatched servers, and poorly maintained IoT devices continue to operate with outdated kernels. After initially gaining low-privileged user access through SSH brute-forcing, these old, yet still potent, vulnerabilities are exploited to achieve root privileges, granting the attackers complete control over the compromised machine. This highlights a persistent vulnerability landscape where even well-documented flaws remain exploitable years after their discovery, underscoring the critical importance of comprehensive patch management.
Regarding monetization, SSHStalker demonstrates a multi-faceted approach, indicative of a financially motivated threat actor. Researchers have observed the botnet engaging in AWS key harvesting, a highly lucrative activity given the potential for resource abuse, data exfiltration, or further compromise within cloud environments. Website scanning activities also suggest reconnaissance for web-based vulnerabilities or content for potential defacement or data theft. Furthermore, the botnet includes cryptomining kits, specifically the high-performance Ethereum miner PhoenixMiner. This allows the operators to leverage the collective processing power of compromised machines to mine cryptocurrency, generating illicit revenue at the victim’s expense through increased resource consumption and elevated utility or cloud bills.
Beyond these observed activities, SSHStalker also possesses distributed denial-of-service (DDoS) capabilities. While these attacks have not yet been observed in active deployment, the mere presence of such modules indicates a future potential for disruption or extortion. The current idle state of many SSHStalker bots, simply connecting to the C2 and awaiting instructions, suggests a phase of either testing, network expansion, or strategic "access hoarding." This involves building a vast network of compromised machines to be deployed for future campaigns, sold to other cybercriminals, or activated for large-scale attacks at a later date. This strategy maximizes the long-term value of each compromise.
Attribution for SSHStalker remains unconfirmed. While threat intelligence organizations have not definitively linked it to a specific threat group, analyses have noted operational similarities to the Outlaw/Maxlas botnet ecosystem, a long-standing Linux-based cryptomining botnet known for its use of brute-force techniques and older attack methods. Furthermore, certain indicators suggest potential connections to Romanian threat actors or infrastructure, though this is not conclusive proof of origin. The lack of clear attribution is common in the botnet landscape, where shared tools and techniques can obscure the true identity of operators.
In response to the threat posed by SSHStalker and similar "old-school" botnets, organizations must implement robust defensive strategies. Proactive monitoring is paramount: security teams should deploy solutions capable of detecting the installation and execution of compilers like GCC on production servers, as these are highly unusual activities in a hardened environment. Alerts for IRC-style outbound connections are crucial, as legitimate IRC traffic is rare in most corporate networks. Furthermore, cron jobs with short execution cycles, especially those originating from unusual or temporary paths, represent significant red flags requiring immediate investigation.
Mitigation recommendations extend to hardening server configurations and network perimeters. Disabling SSH password authentication in favor of strong SSH key-based authentication with multi-factor authentication (MFA) is a fundamental step to prevent brute-force attacks. Removing compilers and development tools from production server images significantly reduces the ability of attackers to compile payloads on compromised hosts. Enforcing strict egress filtering at the network perimeter can block unusual outbound C2 traffic, including IRC connections, preventing bots from communicating with their masters. Finally, restricting execution from common temporary directories like /dev/shm can thwart attackers who often stage and execute malicious payloads in these locations.
The SSHStalker botnet serves as a potent reminder that the cybersecurity threat landscape is not solely defined by cutting-edge innovations. The effective exploitation of fundamental vulnerabilities, combined with time-tested, resilient communication protocols, can yield a formidable and scalable threat. This "retro revival" approach challenges organizations to re-evaluate their security posture, ensuring that their defenses are robust enough to counter not only the threats of tomorrow but also the enduring, effective tactics of yesteryear. The focus on reliability and scale over stealth, as exemplified by SSHStalker, underscores a pragmatic and financially driven motive that will likely continue to evolve using a blend of the old and the new.






