
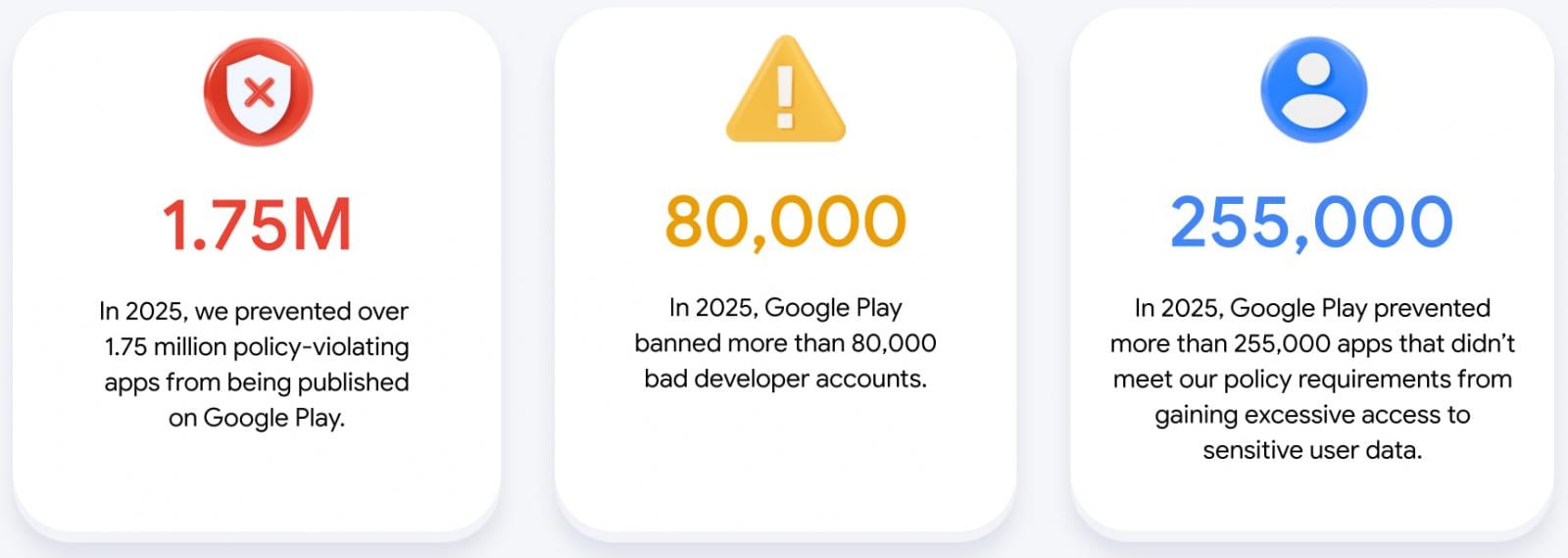
The digital landscape of mobile applications faces persistent threats from malicious actors, prompting platform custodians like Google to deploy advanced safeguards; in 2025 alone, the company successfully prevented over 1.75 million potentially harmful applications from reaching the Google Play Store, simultaneously blocking more than 255,000 attempts by existing apps to illicitly access sensitive user information. This extensive intervention underscores the scale of the ongoing battle against digital malfeasance and the critical role of robust security frameworks in maintaining a trustworthy mobile ecosystem.
The sheer volume of applications submitted to the Google Play Store annually presents an unprecedented challenge for content moderation and security vetting. With billions of active Android devices globally, the platform serves as a primary distribution channel for software, making it an attractive target for individuals and organizations seeking to exploit users for financial gain, data theft, or other nefarious purposes. Google’s latest annual security review provides a comprehensive look into its multifaceted approach to combating these threats, highlighting the escalating sophistication of both the attacks and the defensive mechanisms deployed. The core objective remains to foster an environment where developers can innovate responsibly, and users can download applications with confidence, shielded from privacy intrusions and security vulnerabilities.
A cornerstone of Google’s defensive strategy involves the continuous refinement and enforcement of stringent developer policies. These policies serve as the foundational rules governing app behavior, data handling, and content standards. In 2025, the application of these policies resulted in the detection and rejection of over 1.75 million submissions that failed to meet the required compliance thresholds. This figure is not merely a statistic; it represents a proactive neutralization of potential threats that could have otherwise impacted millions of users. Violations can range from deceptive advertising practices and hidden functionalities to the inclusion of malware or the infringement of intellectual property. The ability to identify and block such a massive quantity of non-compliant apps at the submission stage is a testament to the effectiveness of Google’s pre-publication vetting processes, preventing harm before it can propagate across the vast Android user base.

Beyond initial submission, a critical focus remains on safeguarding user data privacy. The report indicates that over 255,000 applications were specifically prevented from obtaining excessive or unauthorized access to sensitive user data throughout 2025. This area of protection is paramount in an era where personal information, such as location history, contact lists, photos, and financial details, is highly prized by malicious entities. Apps often attempt to gain such access through misleading permission requests, exploiting vulnerabilities, or embedding covert data collection mechanisms. Google’s protective measures in this domain involve rigorous scrutiny of app permissions, behavioral analysis to detect suspicious data transmission patterns, and the enforcement of granular access controls. The proactive denial of these access attempts reinforces user trust and aligns with global data protection regulations, mitigating the risk of widespread data breaches and privacy compromises.
The operational backbone of this extensive security apparatus relies heavily on a combination of advanced technological solutions and human expertise. Google’s implementation of over 10,000 distinct safety checks on published applications demonstrates the depth of its continuous monitoring efforts. These checks encompass a broad spectrum of analyses, from automated code scanning for known malware signatures and suspicious libraries to behavioral sandboxing that simulates app execution in a controlled environment to detect covert activities. This layered approach ensures that even after an app is published, it remains under surveillance for any emergent threats or policy deviations.
A significant advancement in the 2025 security landscape was the deeper integration of Google’s generative artificial intelligence (AI) models into the app review process. This strategic enhancement has profoundly bolstered detection capabilities. Generative AI excels at identifying complex and evolving malicious patterns that might evade traditional rule-based systems. By analyzing vast datasets of app code, metadata, user reviews, and behavioral telemetry, these AI models can predict emerging threat vectors, spot subtle anomalies indicative of malicious intent, and rapidly flag suspicious submissions. The synergy between AI and human reviewers is crucial: AI handles the immense scale of initial triage and pattern recognition, while human experts provide nuanced judgment for intricate cases, refine AI models, and address edge scenarios that require deeper contextual understanding. This collaboration significantly increases both the speed and accuracy of identifying sophisticated threats, enabling Google to stay ahead of increasingly clever adversaries.
The fight against digital fraud extends beyond malware and data exploitation to the manipulation of public perception. Spam ratings and inauthentic reviews pose a substantial risk, as they can artificially inflate or deflate an app’s reputation, influencing user decisions and distorting the competitive landscape. In 2025, Google’s systems successfully blocked an impressive 160 million fraudulent ratings and reviews. This proactive defense prevented an average 0.5-star drop in ratings for applications targeted by "review bombing" campaigns, where malicious actors flood an app with negative reviews to damage its standing. The methods employed to counter this include sophisticated algorithms that analyze review content for suspicious language, detect bot-like activity patterns, identify clusters of coordinated reviews, and scrutinize reviewer account histories for authenticity. By maintaining the integrity of the review system, Google ensures that user feedback remains a reliable indicator of app quality and trustworthiness.

Beyond the confines of the Play Store, Google’s comprehensive security suite, Play Protect, serves as a vital shield for Android users, scanning an astounding 350 billion applications every single day across billions of devices. This omnipresent guardian is particularly critical for safeguarding against threats from "sideloaded" applications—those installed from sources outside the official Play Store, which inherently bypass Google’s rigorous pre-publication vetting. In 2025, Play Protect identified over 27 million malicious applications that users attempted to install from external sources, effectively alerting users and often preventing installation.
The "enhanced fraud protection" feature within Play Protect saw significant expansion, now covering over 2.8 billion Android devices across 185 markets. This broad deployment underscores Google’s commitment to providing robust, on-device security globally. This feature successfully blocked 266 million installation attempts stemming from 872,000 unique risky applications. Such protection is crucial for combating various forms of mobile fraud, including phishing scams, financial malware, and social engineering attacks that often rely on tricking users into installing malicious software. Play Protect’s continuous, real-time scanning and threat intelligence updates ensure that devices are protected against the latest vulnerabilities and attack vectors, regardless of where the app originated.
For developers seeking to fortify their applications against abuse and unauthorized access, the Play Integrity API offers a powerful set of tools. This service processes more than 20 billion checks daily, enabling developers to verify the authenticity of app interactions and detect instances of tampering, piracy, or bot activity. In 2025, Google further strengthened this API by integrating new hardware-backed signals, which provide a more robust and immutable verification of device and app integrity. Additionally, the introduction of in-app remediation prompts allows developers to guide users through necessary security actions or provide warnings when suspicious activity is detected, fostering a more secure experience directly within the application.
Platform-level security enhancements also played a crucial role in 2025. With the release of Android 16 in June, Google introduced built-in protections against "tapjacking attacks" with minimal effort required from developers. Tapjacking involves malicious apps overlaying transparent, interactive elements on top of legitimate applications, tricking users into tapping hidden buttons or granting permissions they did not intend. These attacks are frequently used for fraudulent financial gains, such as automatically clicking on ads. By embedding robust safeguards directly into the operating system, Android 16 significantly mitigates this threat, preventing hidden windows from loading ads that are then automatically tapped, thereby protecting users from involuntary actions and financial exploitation.
Looking ahead, Google’s strategy for securing the Android ecosystem and the Play Store involves continued investment in several key areas. The commitment to further enhancing AI-driven defenses remains paramount, recognizing the dynamic nature of cyber threats. As malicious actors leverage increasingly sophisticated tactics, including AI, Google must ensure its defensive AI capabilities evolve at an even faster pace, continuously learning and adapting to new attack patterns. Furthermore, the expansion of developer verification processes is a strategic move to enhance accountability and reduce the prevalence of anonymous bad actors who can easily create new accounts after being banned. By implementing more stringent identity verification requirements, Google aims to raise the barrier for entry for malicious entities. Finally, embedding compliance tools directly into development workflows represents a proactive approach to security. By providing developers with tools and guidance to identify and rectify policy violations before an app is published, Google aims to shift security left in the development lifecycle, reducing the burden on post-submission review and fostering a culture of secure by design among the developer community.
In conclusion, the figures from 2025 paint a clear picture of Google’s relentless efforts to safeguard the digital frontier of mobile applications. The prevention of millions of policy-violating app submissions and unauthorized data access attempts, coupled with advanced protections against review fraud and sideloaded malware, demonstrates a comprehensive and proactive security posture. Through the strategic application of advanced AI, continuous policy refinement, ecosystem-wide protection via Play Protect, and developer-centric security tools, Google continues to fortify the Android platform, ensuring a more secure, reliable, and trustworthy experience for billions of users worldwide. The ongoing evolution of these defenses underscores the enduring commitment to fostering an innovative yet secure mobile app ecosystem.








