
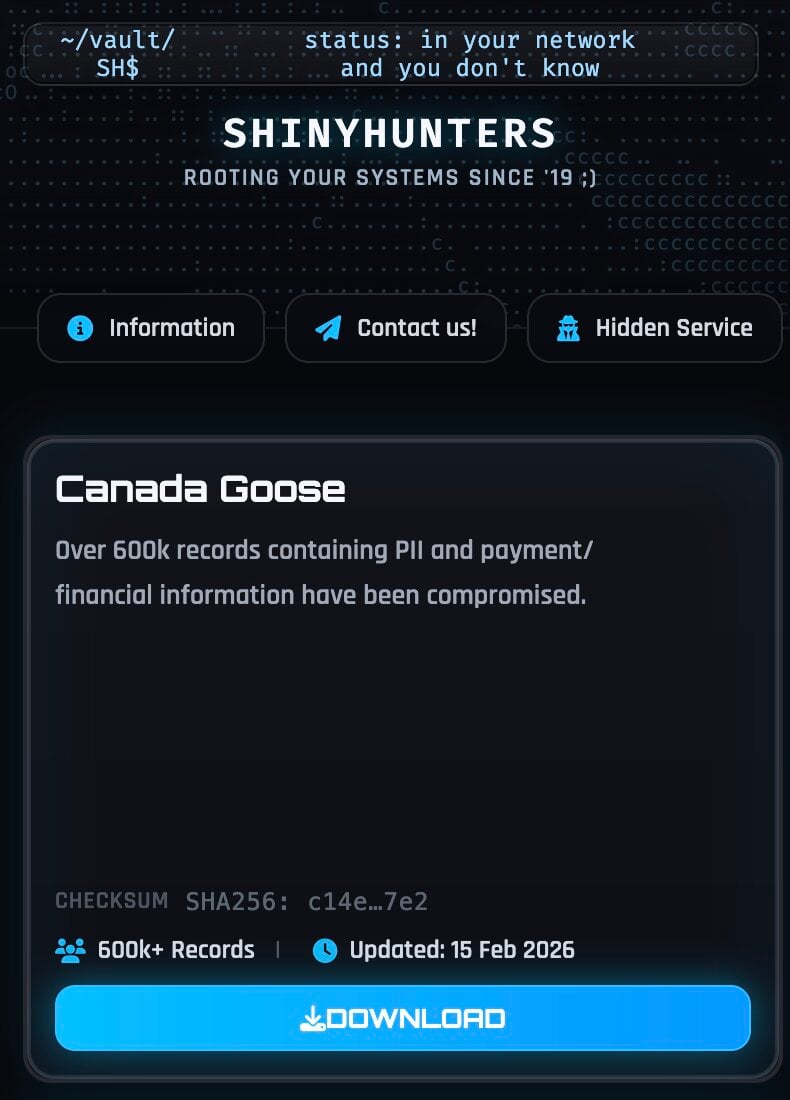
A significant cybersecurity incident has emerged, involving luxury outerwear brand Canada Goose, as a prominent data extortion collective, ShinyHunters, publicly asserts the acquisition and subsequent leak of over 600,000 customer records containing sensitive personal and transactional details. This revelation has triggered an internal investigation by the Toronto-based company, which, while acknowledging the authenticity of a historical dataset, maintains that its proprietary systems show no evidence of a direct breach, pointing instead to a potential compromise within a third-party service provider.
The incident underscores the intricate challenges modern enterprises face in securing expansive digital ecosystems, particularly those relying on a myriad of external vendors for critical operations such as payment processing and e-commerce functionalities. For a brand synonymous with premium quality and exclusivity like Canada Goose, founded in 1957 and boasting a substantial global retail presence with nearly 4,000 employees, such an exposure carries considerable implications for customer trust and brand integrity.
The Nature of the Compromised Data
The data archive, made public by ShinyHunters on its dedicated leak platform, is reported to encompass a substantial 1.67 gigabytes of information, meticulously organized in JSON format. Forensic examination of sample records indicates a comprehensive array of e-commerce transactional data. This includes, but is not limited to, full customer names, associated email addresses, telephone numbers, precise billing and shipping addresses, internet protocol (IP) addresses used during transactions, and detailed historical purchase records.
Crucially, the dataset also contains partial payment card information. While full, unmasked credit card numbers do not appear to be present, the leaked records include the specific card brand (e.g., Visa, Mastercard), the last four digits of the card number, and in certain instances, the first six digits, known as the Bank Identification Number (BIN). Alongside these fragments, payment authorization metadata is also exposed. This combination, even without complete card details, provides a potent arsenal for malicious actors. The BIN can identify the issuing bank and card type, while the last four digits, when paired with other PII, can be leveraged in verification processes or to bolster the credibility of phishing attempts.
Beyond immediate financial implications, the depth of the exposed data allows for sophisticated profiling of customers. Information such as purchase history, the value of past orders, and even technical details like device and browser information used during transactions, empowers attackers to identify high-value targets. This granular insight can facilitate highly personalized and therefore more effective phishing campaigns, social engineering schemes, and various forms of identity fraud, far surpassing the effectiveness of generic, untargeted attacks.
Canada Goose’s Official Stance and Attribution Challenges
In response to the public disclosure, Canada Goose issued a statement affirming its awareness of the dataset’s publication, emphasizing its historical nature and its relation to past customer transactions. The company’s internal review, as communicated, has thus far yielded no indication of a direct compromise to its own core systems. This assertion directs the investigative focus towards external points of vulnerability within its operational periphery. The company has committed to a thorough assessment of the newly released data to ascertain its accuracy, full scope, and to determine appropriate subsequent actions. A specific clarification was made that their review currently indicates no involvement of unmasked financial data, reiterating the firm’s commitment to customer information protection.
The potential origin of such a breach from a third-party vendor introduces a layer of complexity to cybersecurity incident response. Modern e-commerce platforms invariably rely on a vast network of service providers for functions ranging from payment gateways and logistics to customer relationship management and data analytics. Each of these external entities represents a potential point of entry for threat actors, and a compromise at any link in this extended digital supply chain can expose sensitive customer data, even if the primary enterprise’s internal defenses remain unbreached. The schema observed in the leaked dataset—featuring field names such as checkout_id, shipping_lines, cart_token, and cancel_reason—strongly aligns with the typical data structures of hosted storefront and payment processing platforms. This technical detail lends credence to ShinyHunters’ claim that the data originated from a third-party payment processor, with the group specifying an alleged breach date of August 2025. This timeframe, appearing to be a forward-dated error, likely indicates August 2023 or 2024.
Profiling ShinyHunters: A Persistent Cyber Threat
The involvement of ShinyHunters immediately elevates the seriousness of this incident. This group has established itself as one of the most prolific and audacious data extortion collectives in the cybercrime landscape. Their operational model typically involves the exfiltration of massive volumes of sensitive customer data from diverse targets, often focusing on e-commerce platforms, Software-as-a-Service (SaaS) providers, and cloud environments.

ShinyHunters’ motivations are primarily financial, leveraging stolen data for extortion, selling it on illicit underground forums, or publicly leaking it on their dedicated dark web sites when victims refuse to comply with ransom demands. Their track record includes numerous high-profile breaches, impacting millions of user accounts and significantly disrupting targeted organizations.
Recent intelligence reports have also linked ShinyHunters to increasingly sophisticated tactics, including vishing (voice phishing) and elaborate social engineering campaigns designed to compromise single sign-on (SSO) accounts and gain unauthorized access to cloud-based corporate data. While the group specifically denied using these advanced SSO attack vectors for the Canada Goose dataset, claiming a third-party payment processor as the source, their general operational shift towards more complex intrusion methods underscores the evolving threat landscape faced by organizations. Their ability to adapt and exploit vulnerabilities across various attack surfaces highlights the persistent and multi-faceted nature of the cyber threats organizations must contend with today.
Broader Implications and Industry Context
The Canada Goose incident serves as a stark reminder of the pervasive risks associated with digital operations, particularly for consumer-facing brands. Beyond the immediate financial costs of forensic investigation and potential legal liabilities, the long-term impact on brand reputation and customer loyalty can be substantial. Consumers entrust luxury brands with their personal information, expecting a commensurate level of security and discretion. A public data leak, regardless of its origin within the supply chain, can erode this trust, making customers hesitant to engage with the brand in the future.
From a regulatory standpoint, such a data exposure could trigger various data protection laws, depending on the geographic distribution of the affected customers. Regulations like Canada’s Personal Information Protection and Electronic Documents Act (PIPEDA), Europe’s General Data Protection Regulation (GDPR), and various U.S. state laws such as the California Consumer Privacy Act (CCPA) mandate strict data security standards, breach notification requirements, and can impose significant penalties for non-compliance. The distinction between a breach of internal systems and a third-party vendor breach, while critical for internal liability assessment, often does not absolve the primary company of its responsibility to protect customer data under these regulatory frameworks.
This incident also highlights a critical area of cybersecurity focus: third-party risk management. Organizations must implement robust vendor assessment programs, conducting thorough due diligence on the security posture of all their service providers. This includes contractual agreements that mandate specific security controls, regular audits, and clear protocols for incident notification and response. The shared responsibility model in cloud and managed services environments necessitates a continuous, collaborative approach to security across the entire digital ecosystem.
Navigating the Aftermath and Future Outlook
For Canada Goose, the immediate priorities involve completing a comprehensive forensic analysis of the leaked dataset to definitively confirm its accuracy, scope, and the number of affected individuals. This will be followed by determining if and how to notify impacted customers, a decision that will likely be guided by legal counsel and regulatory requirements. Proactive and transparent communication will be essential in managing customer expectations and mitigating reputational damage.
For affected customers, vigilance is paramount. They should remain highly skeptical of unsolicited communications, particularly those purporting to be from Canada Goose or financial institutions, as these could be sophisticated phishing attempts leveraging the exposed data. Monitoring financial accounts, credit reports, and considering credit freezes are advisable precautions against potential identity theft and financial fraud.
Looking ahead, this event reinforces several critical lessons for the broader industry. Organizations must prioritize a holistic cybersecurity strategy that extends beyond their own perimeter to encompass their entire supply chain. This includes adopting principles of "zero trust," implementing robust data minimization policies to store only necessary information for the shortest possible duration, and employing advanced threat detection and response capabilities. Regular security audits, penetration testing, and a well-rehearsed incident response plan are no longer optional but fundamental requirements for operating in an increasingly complex and hostile cyber landscape. The battle to secure digital assets against sophisticated threat actors like ShinyHunters is an ongoing endeavor, demanding continuous adaptation, investment, and collaboration across the entire enterprise ecosystem.







