
A concerted campaign by suspected state-aligned cyber adversaries is actively exploiting secure messaging applications, including Signal, to compromise the digital communications of high-profile individuals across Europe, prompting a critical alert from Germany’s principal domestic intelligence and cybersecurity agencies. These sophisticated operations bypass conventional malware deployment and technical vulnerabilities, relying instead on advanced social engineering tactics to gain unauthorized access to private conversations and contact networks. The primary targets encompass a crucial demographic of national security interest, including government officials, senior military personnel, diplomatic staff, and investigative journalists, whose compromised communications could yield significant strategic intelligence.
The Federal Office for the Protection of the Constitution (BfV) and the Federal Office for Information Security (BSI) have jointly issued a comprehensive security advisory, underscoring the gravity of this evolving threat. Their intelligence points to a strategic shift by malicious actors, who are increasingly leveraging the inherent trust in communication platforms and human susceptibility to psychological manipulation. This approach represents a nuanced challenge to conventional cybersecurity defenses, as it sidesteps technical exploits in favor of exploiting user behavior and platform functionalities designed for legitimate use.
The Modus Operandi: Exploiting Trust, Not Code
Central to these attacks is the absence of malicious software or zero-day exploits targeting vulnerabilities within the messaging services themselves. Instead, the threat actors engage directly with their targets, employing deceptive personas that mimic legitimate support functions of the messaging platforms or automated chatbots. The overarching objective is to clandestinely infiltrate one-to-one and group chats, alongside acquiring comprehensive contact lists, effectively turning the victim’s secure communication channel into a surveillance tool.
Two primary variants of this infiltration strategy have been identified, each designed to achieve varying degrees of access and persistence. The first method culminates in a complete account takeover, where the attacker assumes full control, locking the legitimate user out. The second, more subtle approach involves pairing the victim’s account with an attacker-controlled device, enabling discreet monitoring of chat activities without immediately alerting the user to the compromise.

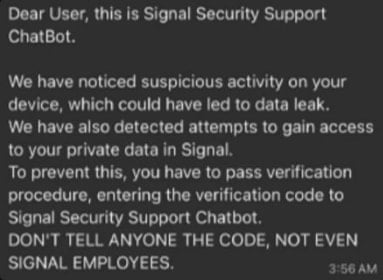
In the account takeover scenario, attackers initiate contact by impersonating Signal’s support service. They transmit fabricated security warnings designed to instill a sense of urgency and panic in the recipient. Under the guise of resolving an imminent security threat, the target is then coerced into divulging their Signal PIN or an SMS verification code. This critical piece of information allows the perpetrators to register the victim’s phone number on their own device, effectively hijacking the account and severing the legitimate user’s access. The speed and psychological pressure applied in these interactions are crucial for their success, as they minimize the window for the victim to scrutinize the legitimacy of the request.
The second variant, characterized by its stealth, leverages Signal’s legitimate linked-device feature. This functionality is intended to allow users to access their account across multiple personal devices, such as computers, tablets, and secondary phones. Attackers craft plausible pretexts to convince targets to scan a QR code presented by the adversary. Upon scanning, the victim unknowingly links their Signal account to a device controlled by the malicious actor. This grants the attacker seamless and persistent access to the victim’s current and historical chats, as well as their entire contact directory, without triggering any overt security alerts or requiring the victim’s PIN. The subtlety of this method makes it particularly insidious, as victims may remain unaware of the breach for extended periods, providing adversaries with a prolonged window for intelligence gathering.
Why Senior Figures Are Prime Targets
The focus on high-ranking individuals—politicians, military officers, diplomats, and investigative journalists—is not coincidental. These individuals frequently possess access to sensitive information, participate in confidential discussions, and maintain networks that are invaluable to state-sponsored intelligence operations. Compromising their secure communication channels offers a direct conduit to classified data, strategic insights, and early warnings of policy shifts or operational plans. For investigative journalists, such access could expose sources, ongoing investigations, or provide leverage for manipulation.
The targeting of these critical demographics underscores the strategic intent behind these attacks. State-sponsored actors, often operating with significant resources and sophisticated intelligence capabilities, prioritize targets whose compromised communications can yield geopolitical advantages, economic espionage opportunities, or enable influence operations. The nature of Signal’s end-to-end encryption makes direct interception of communications extraordinarily difficult, thus pushing adversaries to target the "endpoints"—the users themselves—through social engineering.

Historical Context and Evolving Tactics
While the current German warning highlights these specific tactics, the underlying methodology of exploiting legitimate features for illicit access is not new. In recent years, similar techniques have been observed and attributed to prominent state-aligned threat groups. Google’s threat researchers previously documented instances where Russian state-aligned groups, notably Sandworm, utilized the QR code pairing technique to compromise Signal accounts. Similarly, Ukraine’s Computer Emergency Response Team (CERT-UA) has attributed comparable attacks, specifically targeting WhatsApp accounts, to Russian state-sponsored actors.
The success of these techniques by nation-state actors has led to their adoption by a broader spectrum of cybercriminals. Campaigns like "GhostPairing" have leveraged WhatsApp’s device linking functionality to hijack accounts for various fraudulent schemes and scams, demonstrating the widespread applicability and effectiveness of these social engineering methods. This evolution signifies a democratization of sophisticated attack vectors, making them accessible to a wider array of malicious entities beyond state-sponsored groups.
Implications for National Security and Digital Trust
The implications of these persistent and sophisticated attacks extend far beyond individual privacy concerns. For national security, the compromise of senior figures’ communications can lead to leaks of classified information, undermine diplomatic negotiations, expose military strategies, and jeopardize intelligence operations. The mere possibility of such compromises can erode trust within governmental and military hierarchies, potentially leading to a chilling effect on open communication, even within secure channels.
From a broader societal perspective, the erosion of trust in secure messaging platforms like Signal, which are designed to protect privacy and facilitate confidential communication, is deeply troubling. These platforms are often seen as a last bastion of secure digital interaction, especially for human rights activists, journalists, and dissidents operating in repressive regimes. If even these highly secure platforms can be effectively subverted through social engineering, it raises profound questions about the viability of truly private digital communication in an era of pervasive surveillance and sophisticated cyber warfare.
Mitigation and Defensive Strategies
In response to these escalating threats, German authorities have issued clear recommendations for enhanced user vigilance and proactive security measures. The foremost advice is to exercise extreme caution regarding unsolicited messages, particularly those claiming to be from messaging platform support services. Users are strongly advised never to respond to such communications, as legitimate messaging platforms, including Signal, do not contact users directly through their messaging interface. Instead, any suspicious account should be immediately blocked and reported.
Beyond reactive measures, proactive security configurations are crucial. Signal offers a "Registration Lock" feature, accessible under "Settings > Account." When activated, this feature requires a user-defined PIN whenever an attempt is made to register the associated phone number with the application on a new device. Without this PIN, registration fails, providing a critical layer of defense against account takeover attempts. Users must, however, ensure they do not lose this PIN, as its loss can result in permanent account access forfeiture.
Furthermore, regular scrutiny of linked devices is a fundamental security practice. Signal users can review all devices currently connected to their account by navigating to "Settings > Linked devices." Any unrecognized or suspicious entries should be immediately removed. This simple audit can detect and neutralize instances where an attacker has surreptitiously paired their device with the victim’s account, thereby revoking their unauthorized access.

The Evolving Threat Landscape and Future Outlook
The current wave of attacks highlights a critical paradigm shift in cyber espionage: the increasing emphasis on the human element as the weakest link. As technical defenses become more robust and encryption technologies more widespread, adversaries are increasingly investing in social engineering and psychological manipulation to achieve their objectives. This trend is likely to intensify, with future attacks potentially incorporating more sophisticated AI-driven impersonations, deepfakes, and highly personalized lures designed to exploit individual vulnerabilities and biases.
For cybersecurity professionals and intelligence agencies, this necessitates a multi-faceted defense strategy that goes beyond technological safeguards. Comprehensive user education and awareness programs are paramount, focusing on recognizing social engineering tactics, understanding platform security features, and cultivating a culture of skepticism towards unsolicited digital interactions. Organizations must also implement robust internal protocols for handling sensitive information, establish clear communication channels for reporting suspicious activities, and regularly conduct simulated phishing and social engineering exercises to bolster employee resilience.
In conclusion, the German intelligence warning serves as a stark reminder of the persistent and evolving nature of cyber threats targeting critical national assets. The sophisticated, malware-free social engineering attacks leveraging legitimate features of secure messaging platforms represent a formidable challenge. Addressing this threat requires a concerted effort spanning technological innovation, robust policy frameworks, and, most critically, an informed and vigilant user base capable of discerning and resisting increasingly deceptive digital stratagems. The ongoing struggle against these insidious forms of digital espionage underscores the imperative for continuous adaptation and resilience in the face of a dynamic and determined adversary.







