A sophisticated information-stealing malware, dubbed Arkanix Stealer, emerged and swiftly vanished in late 2025, leaving behind a compelling narrative of potential artificial intelligence assistance in its rapid development and deployment. This short-lived operation, observed to operate for merely two months, featured a robust architecture designed for extensive data exfiltration, raising critical questions about the evolving landscape of cyber threats fueled by advanced technological experimentation. The sudden appearance and disappearance of Arkanix underscore a concerning trend where malicious actors leverage cutting-edge tools to rapidly prototype and deploy cyber weapons, challenging conventional detection and attribution methodologies.
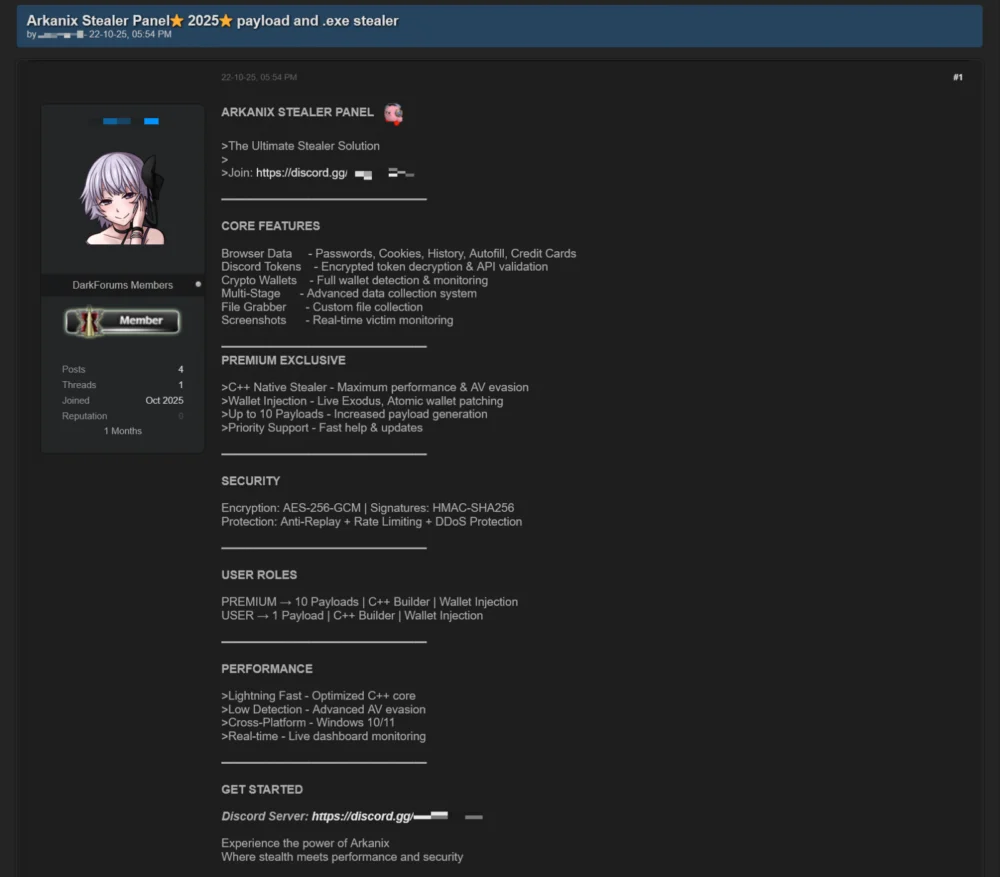
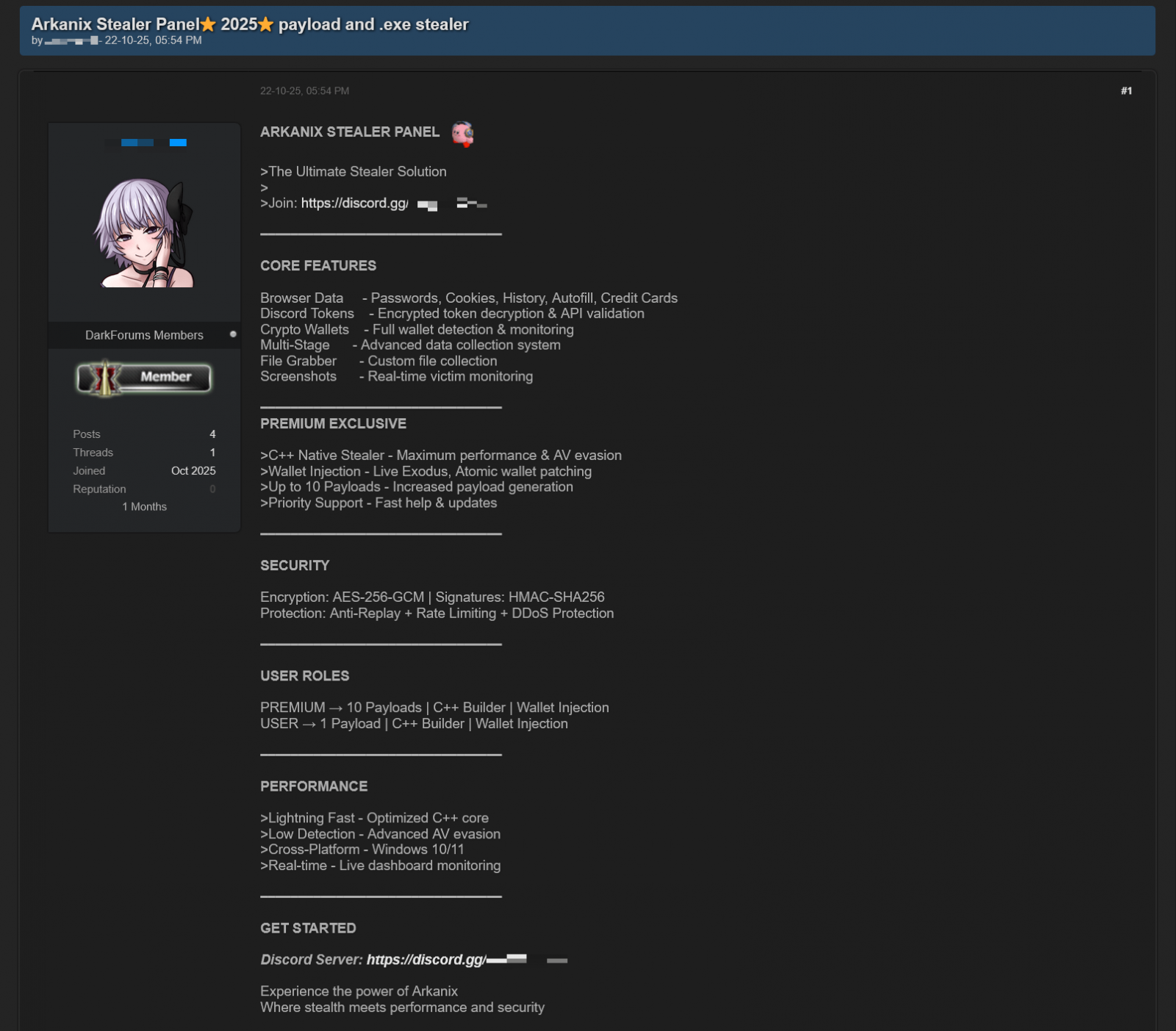
The emergence of Arkanix on prominent dark web forums in October 2025 was marked by an aggressive promotional campaign. Unlike many one-off malicious tools, Arkanix was presented as a refined service, indicating a level of organizational intent beyond a simple individual project. Its developers offered prospective cybercriminals a tiered access model, a common strategy in the burgeoning malware-as-a-service (MaaS) ecosystem. This model allowed for scalability and catered to a diverse range of illicit operations, from low-level data harvesting to more targeted and evasive attacks. The basic offering provided a Python-based implementation, presumably easier to modify and deploy for less technically proficient actors. For those seeking enhanced capabilities and stealth, a "premium" tier was made available, featuring a natively compiled C++ payload. This advanced variant incorporated sophisticated protection mechanisms such as VMProtect, designed to thwart reverse engineering and evade antivirus detection, alongside features like cryptocurrency wallet injection, signaling a focus on direct financial exploitation.

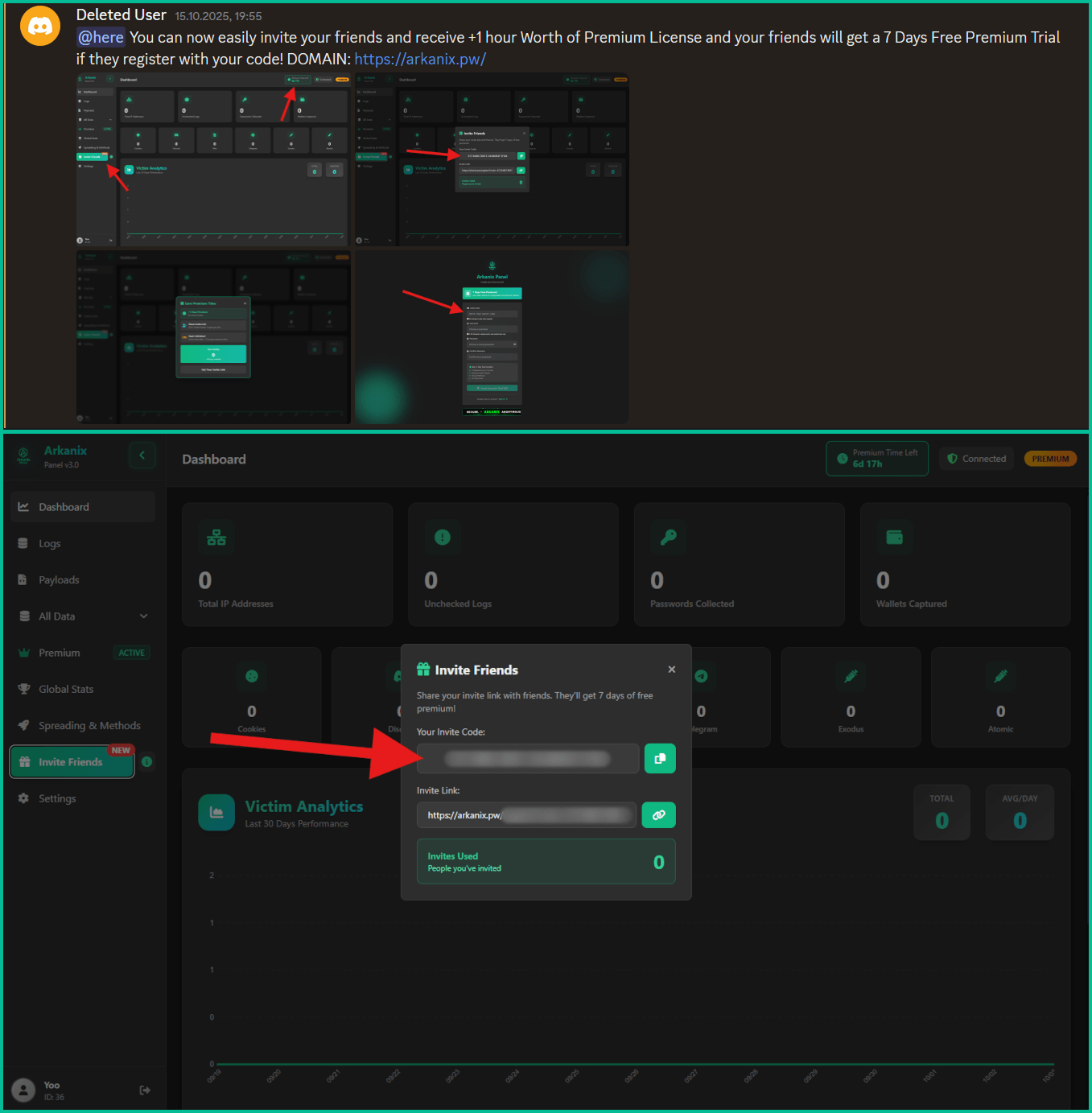
Beyond the technical architecture, the Arkanix operation cultivated a surprisingly structured community around its illicit offering. A dedicated Discord server was established, serving as a central hub for user interaction. This platform facilitated communication channels for providing updates, soliciting feedback on proposed features, and offering technical assistance to subscribers. Such a setup mimics legitimate software development and customer support structures, highlighting the professionalization of cybercrime. To further accelerate its adoption and reach, a referral program was implemented. This incentivized existing users to enlist new customers, offering perks such as additional free premium access, while new sign-ups received a complimentary week of the advanced "premium" version. This aggressive marketing and community-building approach demonstrate a clear strategy to quickly build a user base and disseminate the malware across the cybercriminal underground.
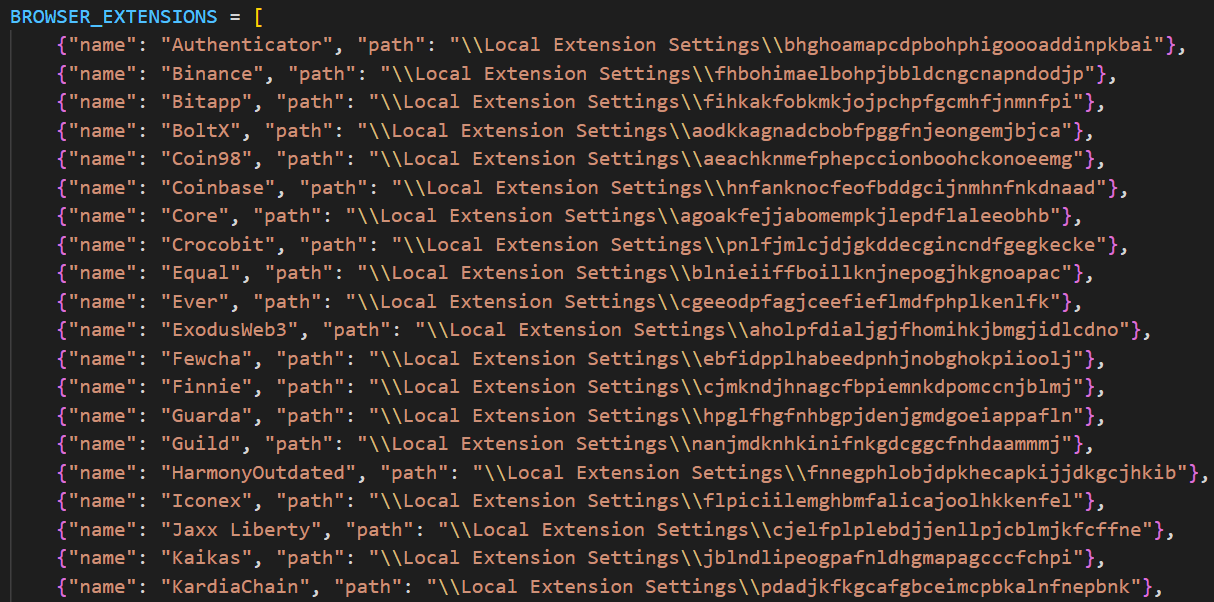
The core functionality of Arkanix revolved around its extensive data-stealing capabilities. The malware was engineered to systematically collect a wide array of sensitive information from compromised systems. This included comprehensive system details, a standard first step for any info-stealer. More critically, Arkanix targeted data stored within web browsers, a treasure trove of personal and financial information. It could exfiltrate browsing history, autofill data, stored cookies, and crucially, saved passwords from an impressive roster of 22 different browsers. Specialized modules were also developed to extract OAuth2 tokens from Chromium-based browsers, which could grant unauthorized access to online accounts without needing direct password credentials.

Beyond browser data, Arkanix extended its reach to communication platforms and virtual private networks. It was capable of pilfering data from Telegram and Discord, including user credentials. Furthermore, the malware exhibited a unique capability to propagate itself through the Discord API, leveraging compromised accounts to send malicious messages to friends and channels, thereby expanding its infection vector. The targeting of VPN credentials for services like Mullvad, NordVPN, ExpressVPN, and ProtonVPN is particularly concerning, as it could compromise users’ perceived anonymity and potentially expose their real identities or online activities. The malware also possessed the ability to archive specific files from the local filesystem, preparing them for asynchronous exfiltration to its command-and-control (C2) servers.
The modular design of Arkanix allowed for dynamic expansion of its capabilities. Additional modules could be downloaded on demand from the C2 infrastructure, catering to specific exploitation needs. These included a dedicated Chrome grabber for enhanced browser data extraction, wallet patchers for popular cryptocurrency clients like Exodus and Atomic, a screenshot utility for visual reconnaissance, a Hidden Virtual Network Computing (HVNC) module for remote control, and stealers specifically designed for FileZilla (FTP client) and Steam (gaming platform) credentials. This modularity provided flexibility and allowed threat actors to customize their attacks based on their targets and objectives.
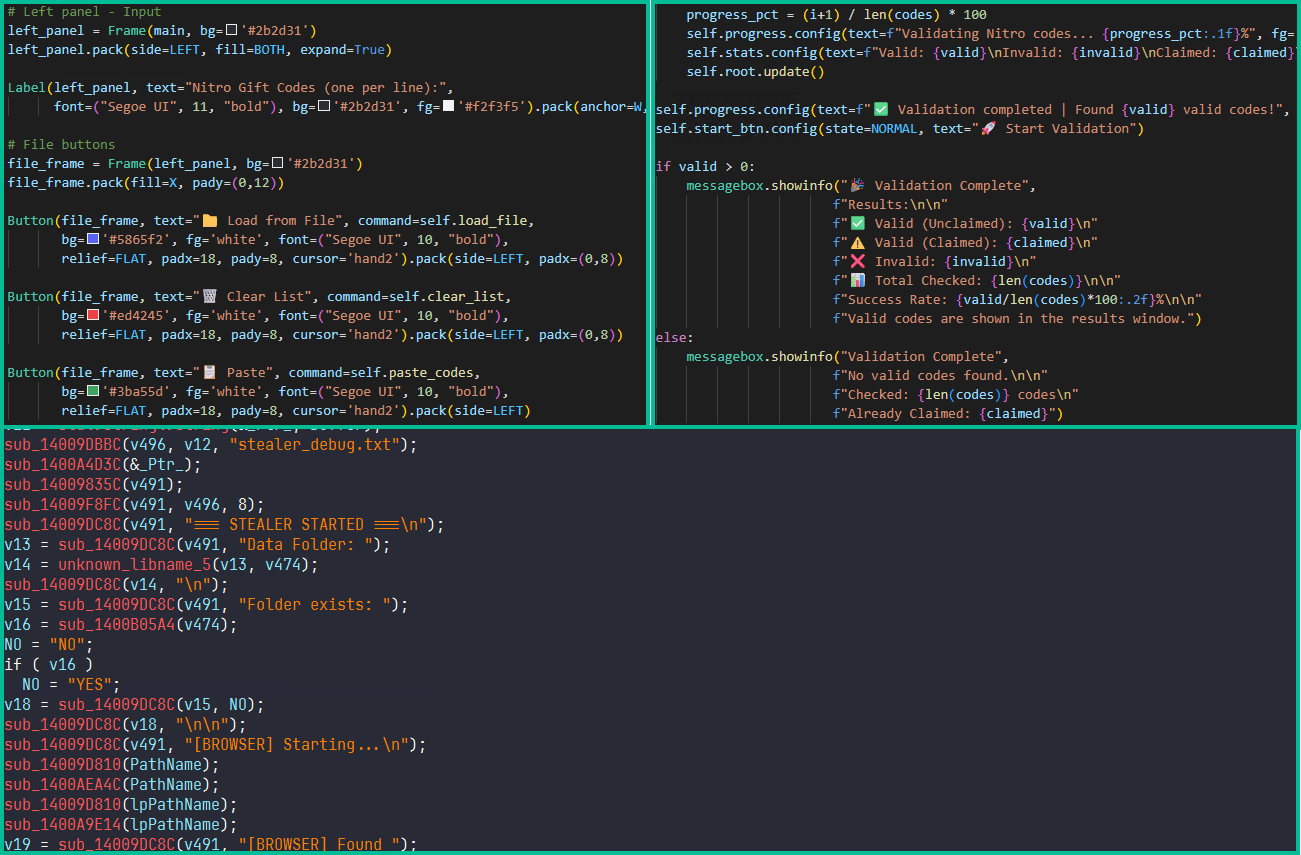
The "premium" C++ variant of Arkanix further amplified its malicious potential. This higher-tier version integrated RDP (Remote Desktop Protocol) credential theft, allowing attackers to gain persistent remote access to compromised machines. It also incorporated advanced anti-sandbox and anti-debugging checks, making it significantly harder for security analysts to analyze its behavior in isolated environments. The premium version leveraged WinAPI for sophisticated screen capturing and expanded its targeting to include popular gaming platforms such as Epic Games, Battle.net, Riot, Unreal Engine, Ubisoft Connect, and GOG. A notable feature of the premium variant was the delivery of the ChromElevator post-exploitation tool. This sophisticated utility injected into suspended browser processes to bypass Google’s App-Bound Encryption (ABE) protection, designed to secure user credentials, thereby enabling unauthorized access to highly sensitive information.
A pivotal aspect of Arkanix’s short but impactful existence lies in the strong indications of Large Language Model (LLM) assistance in its development. Cybersecurity analysts, upon dissecting the malware’s codebase, uncovered clues pointing towards LLM-assisted coding practices. This finding suggests that artificial intelligence tools played a significant role in accelerating the malware’s creation, potentially drastically reducing both development time and associated costs. The hypothesis is that Arkanix was less a long-term, sustained criminal enterprise and more of a proof-of-concept or a short-lived experiment aimed at rapid financial gain or, perhaps, to test the efficacy and speed of AI-driven malware development.
The implications of AI involvement in malware development are profound. Traditionally, creating sophisticated malware requires considerable expertise, time, and resources. LLMs can democratize this process, enabling individuals or smaller groups with less specialized knowledge to generate complex code, including malicious functionalities, much more efficiently. This shifts the threat landscape by lowering the barrier to entry for cybercriminals and potentially accelerating the pace at which new and more evasive malware variants emerge. For Arkanix, the suspected LLM assistance might explain its rapid development cycle, the comprehensive feature set achieved in a short period, and its sudden disappearance – perhaps the "experiment" concluded, or the developers achieved their immediate objectives.
The ephemeral nature of operations like Arkanix poses significant challenges for the cybersecurity community. Short-lived projects are inherently difficult to detect, track, and attribute. By the time security researchers fully analyze and disseminate information about such threats, the operation may have already ceased, leaving behind a trail of compromised victims but no active infrastructure to dismantle. This "hit-and-run" approach maximizes impact while minimizing the risk of sustained counter-operations from law enforcement and security vendors. It also suggests a strategic shift among some threat actors towards agile, disposable malware operations, prioritizing quick returns over long-term persistence.
Arkanix serves as a stark reminder of the accelerating convergence of advanced technology and cybercrime. The project’s architecture, its sophisticated capabilities, and particularly the evidence of AI-assisted development, position it as a critical case study in the evolving threat landscape. It highlights a future where malicious software might be generated, adapted, and deployed with unprecedented speed and efficiency, making the "cat and mouse" game between attackers and defenders even more challenging.
To counter such evolving threats, a multi-faceted approach is imperative. Organizations must prioritize robust security hygiene, including regular software updates, strong password policies, multi-factor authentication, and comprehensive endpoint detection and response (EDR) solutions. Proactive threat intelligence, focusing on emerging trends in AI-assisted malware and dark web discussions, becomes crucial for anticipating future attacks. Network segmentation, principle of least privilege, and regular security audits are also vital defenses against advanced info-stealers. Furthermore, continued research into AI-driven defense mechanisms, capable of detecting and neutralizing AI-generated malicious code, will be essential in the ongoing arms race against cybercriminals.
The Arkanix Stealer, despite its brief operational lifespan, offers invaluable insights into the future trajectory of cybercrime. It underscores a pivotal moment where AI is not merely a tool for defenders but is increasingly becoming an enabler for attackers. The project’s blend of sophisticated technical features, professional marketing, and suspected AI-driven development paints a picture of a more dynamic, adaptable, and challenging threat landscape that demands constant vigilance and innovation from the global cybersecurity community.








