
A sophisticated, AI-augmented cyber campaign, attributed to a Russian-speaking threat actor, has successfully compromised over 600 Fortinet FortiGate firewalls across 55 nations within a mere five-week period, signaling a significant evolution in the landscape of digital intrusions facilitated by advanced artificial intelligence.
This alarming development, detailed in a recent report by Amazon’s CISO, CJ Moses, underscores a critical shift in adversary tactics where generative AI services are leveraged not for zero-day exploits, but to amplify the efficiency and reach of more conventional attack vectors. Between January 11 and February 18, 2026, the attacker systematically targeted FortiGate management interfaces exposed to the internet, exploiting weak credentials and the absence of multi-factor authentication (MFA) to gain initial access. The campaign’s rapid execution and extensive global footprint, spanning regions such as South Asia, Latin America, the Caribbean, West Africa, Northern Europe, and Southeast Asia, highlight the unprecedented scale achievable when even moderately skilled actors are empowered by AI automation.
Unlike many high-profile breaches that rely on undisclosed vulnerabilities, this operation distinguished itself by focusing on fundamental security hygiene failures. The threat actor initiated their assault by methodically scanning for FortiGate management interfaces accessible on common ports (443, 8443, 10443, and 4443). Rather than deploying complex exploits, the group opted for brute-force attacks, testing common passwords against these exposed interfaces. This approach, while seemingly unsophisticated, proved devastatingly effective against organizations that had neglected basic security protocols, revealing a widespread vulnerability to readily preventable attacks. The FortiGate firewalls, critical network perimeter devices, became gateways into sensitive internal networks, demonstrating that even advanced security hardware is only as strong as its weakest authentication link.

Upon successful breach, the adversary swiftly extracted comprehensive configuration settings from the compromised devices. These critical files contained a treasure trove of sensitive information, including VPN configurations, user credentials, encrypted passwords, and intricate network topology details. The ability to parse and decrypt these complex configuration files was significantly accelerated through the use of custom Python and Go tools, which, according to Amazon’s analysis, bore clear hallmarks of AI-assisted development. The code exhibited characteristics such as redundant comments, simplistic architecture, and rudimentary JSON parsing, suggesting rapid generation with minimal human refinement. While lacking the robustness of meticulously crafted code, these tools were demonstrably functional for the attacker’s specific objectives, showcasing AI’s utility in quickly generating operational software.
The campaign then transitioned into an AI-powered reconnaissance phase. The custom Go and Python tools were deployed to automate network mapping and target identification within the victim environments. This involved analyzing routing tables, classifying networks by size, conducting extensive port scans using tools like the open-source gogo scanner, identifying SMB hosts and domain controllers, and leveraging Nuclei for HTTP service enumeration. The efficiency gained from AI in this phase allowed the threat actor to rapidly understand the compromised network’s architecture, identify high-value assets, and pinpoint pathways for deeper infiltration, a process that would traditionally require significant manual effort and specialized expertise.
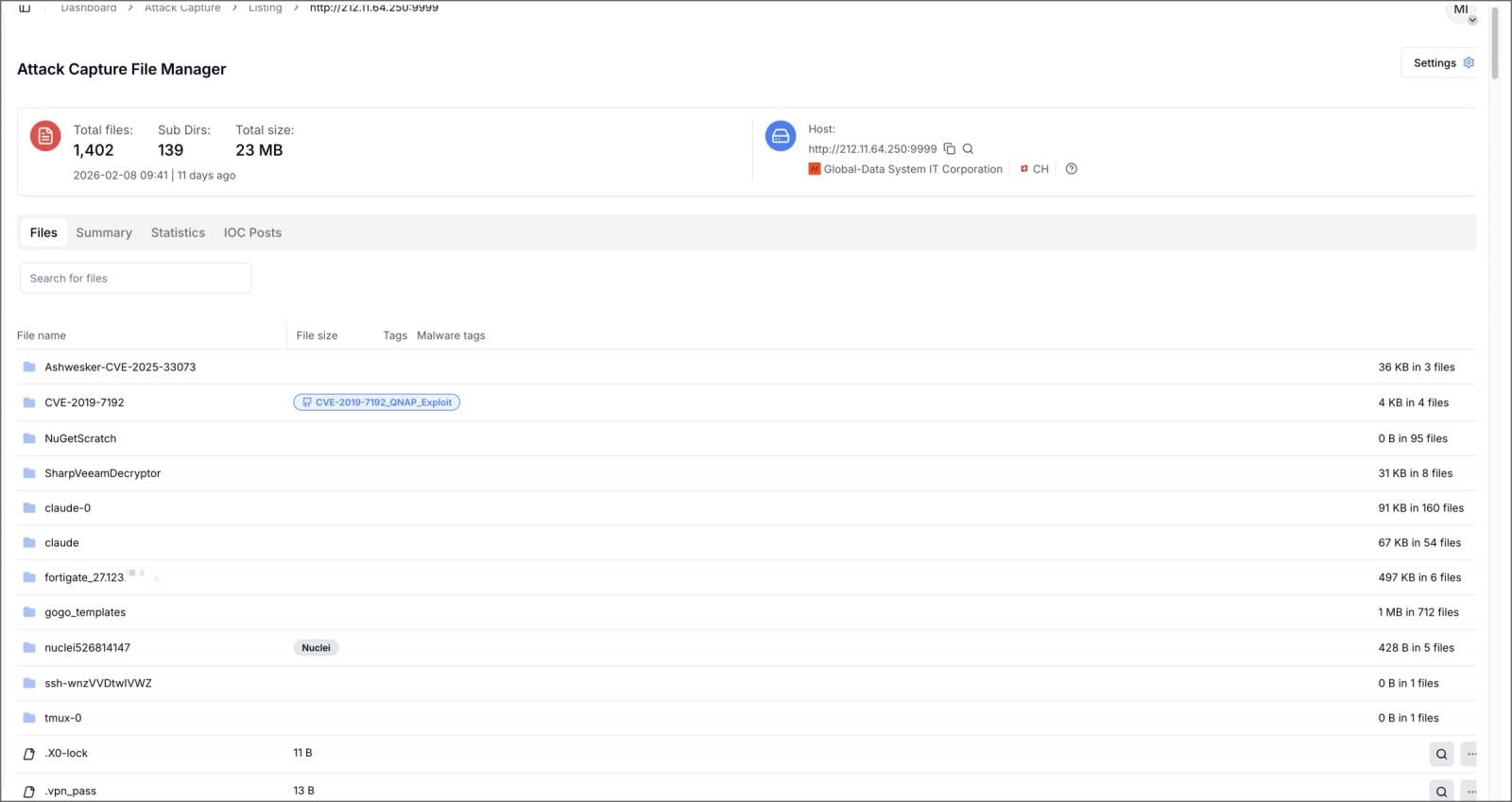
Further technical insights from the Cyber and Ramen security blog, corroborated by Amazon’s findings, paint a detailed picture of the AI’s direct integration into the kill chain. A misconfigured server (212.11.64.250) linked to the threat actor exposed over 1,400 files, including a wealth of stolen FortiGate configurations, Active Directory mapping data, credential dumps, and detailed attack planning documents. Crucially, this server hosted a custom Model Context Protocol (MCP) server named ARXON. This ARXON framework acted as an intelligent intermediary, ingesting reconnaissance data from breached FortiGate appliances and internal networks, feeding it into commercial large language models such as DeepSeek and Claude, and then translating the AI-generated outputs into actionable, structured attack plans.
These AI-generated attack plans were remarkably comprehensive, offering step-by-step instructions for achieving Domain Admin privileges, suggesting optimal locations for credential harvesting, outlining recommended exploitation sequences, and providing guidance on effective lateral movement strategies within the compromised networks. In a particularly concerning development, Claude Code was configured in some instances to autonomously execute offensive tools, including Impacket scripts, Metasploit modules, and hashcat, without requiring explicit human approval for each command. This level of AI autonomy signifies a dangerous progression, transforming generative AI from a mere assistant into an active participant in the offensive cyber lifecycle.

The threat actor’s operational documentation, written in Russian, further elucidated their post-compromise objectives. These notes detailed the use of tools like Meterpreter and Mimikatz for conducting DCSync attacks against Windows domain controllers, aimed at extracting NTLM password hashes from Active Directory databases. A significant focus was also placed on targeting Veeam Backup & Replication servers, a common pre-ransomware tactic to neutralize recovery options. Custom PowerShell scripts, compiled credential-extraction tools, and attempts to exploit known Veeam vulnerabilities (CVE-2023-27532 and CVE-2024-40711) were part of this strategy. The campaign also sought to exploit CVE-2019-7192, a remote code execution vulnerability in QNAP devices, illustrating a broad scope of opportunistic targeting.
Amazon’s assessment categorized the threat actor’s inherent skill set as low-to-medium. However, this foundational skill level was dramatically amplified by the strategic deployment of AI. The campaign’s progression, from initially relying on open-source MCP frameworks like HexStrike to developing the custom ARXON system, indicates a continuous evolution in integrating AI for greater automation and efficacy. The use of a Docker-based orchestrator, CHECKER2, for parallel scanning of thousands of VPN targets across over 100 countries further underscores the industrial scale and efficiency achieved through AI-driven automation. This ability to quickly pivot from hardened targets to easier prey, rather than persisting in futile attempts, is another hallmark of an operation optimized for efficiency and scale.
The implications of this campaign are profound for global cybersecurity. It definitively demonstrates how commercial AI services are democratizing sophisticated cyberattacks, lowering the barrier to entry for less skilled actors and enabling them to execute campaigns that would typically require significant expertise and resources. The submission of sensitive victim network topologies, including IP addresses, hostnames, credentials, and known services, directly to commercial AI services for attack planning raises serious concerns about data privacy, intellectual property, and the ethical responsibilities of AI providers.
From a defensive perspective, this trend presents new challenges. Traditional security measures, while still essential, must be augmented to detect and respond to attacks that blend automated efficiency with adaptable, AI-driven decision-making. The sheer volume and speed of AI-assisted reconnaissance and attack planning can overwhelm conventional defensive systems, demanding a shift towards more proactive, intelligence-led defense strategies. Organizations must not only focus on robust technical controls but also on enhancing their threat intelligence capabilities to anticipate and counter evolving AI-powered tactics.
To mitigate these escalating threats, Amazon and other cybersecurity experts emphasize several critical recommendations. Foremost among these is the imperative to eliminate public exposure of FortiGate management interfaces. Where remote access is indispensable, stringent access controls, including strong multi-factor authentication, must be universally enforced. VPN passwords should be unique and distinct from Active Directory account credentials to prevent lateral movement following an initial breach. Furthermore, hardening backup infrastructure, isolating it from production networks, and regularly auditing its security posture is paramount to safeguard against ransomware preparation tactics. The broader industry trend, echoed by Google’s observations regarding threat actors abusing Gemini AI across all stages of cyberattacks, indicates that this FortiGate campaign is not an isolated incident but rather a harbinger of the future of cyber warfare.
As AI technologies become more accessible and powerful, the cybersecurity community faces an urgent imperative to adapt. This includes not only developing AI-powered defensive tools but also fostering a deeper understanding of how adversaries are exploiting AI to enhance their capabilities. The rapid evolution from basic AI assistance to autonomous execution of offensive tools within weeks underscores the dynamic nature of this threat landscape. Protecting critical infrastructure and sensitive data in this new era will require a concerted effort across organizations, technology providers, and policymakers to establish robust defenses, ethical guidelines, and proactive intelligence-sharing mechanisms to counter the burgeoning threat of AI-augmented cybercrime.








