
The digital infrastructure underpinning modern society faces persistent and evolving threats, a reality starkly underscored by the recent declaration from the notorious cyber extortion collective, ShinyHunters. This prominent group has publicly asserted responsibility for a significant infiltration into Odido, one of the Netherlands’ largest telecommunications providers, alleging the exfiltration of millions of sensitive user records from compromised internal systems. This incident not only exposes a critical vulnerability within a key national service provider but also highlights the escalating sophistication and audacity of cybercriminal enterprises targeting vast repositories of personal information for illicit gain.
Odido, a cornerstone of Dutch digital connectivity, delivers a comprehensive suite of mobile, broadband, and television services to a substantial segment of the nation’s populace. The company had previously acknowledged a security incident, disclosing on February 12 that unauthorized actors gained access to its customer contact system on February 7. This breach, as initially reported by Odido, led to the download of personal data pertaining to a considerable number of its subscribers. Crucially, Odido’s initial assessment emphasized that specific high-risk data points—such as "Mijn Odido" account passwords, detailed call records, precise location data, comprehensive billing information, or scans of official identity documents—were not compromised during the intrusion.
The scope of the exposed information, according to Odido’s initial findings, varied per individual, potentially encompassing a combination of full names, residential addresses, cities of residence, mobile telephone numbers, unique customer identification numbers, email addresses, International Bank Account Numbers (IBANs), dates of birth, and, in some instances, certain identification details like passport or driver’s license numbers and their validity periods. This amalgamation of personally identifiable information (PII) presents a significant risk profile for affected individuals, opening avenues for various forms of identity theft and financial fraud. At the time of its initial disclosure, Odido informed local media that the breach impacted an estimated 6.2 million customers, acknowledging that the threat actors had already contacted them, asserting possession of millions of user records.
In response to the discovery, Odido initiated a swift and multi-faceted incident response protocol. The telecommunications provider promptly reported the breach to the Dutch Data Protection Authority (Autoriteit Persoonsgegevens), a mandatory step under the stringent General Data Protection Regulation (GDPR) applicable within the European Union. Furthermore, the company successfully blocked the unauthorized access channels utilized by the attackers to its systems and engaged external cybersecurity specialists to bolster its internal teams in managing the incident response, forensic analysis, and comprehensive mitigation efforts. Despite these proactive measures, an Odido spokesperson, citing ongoing investigations, refrained from publicly attributing the attack to a specific threat group or confirming whether a ransom demand had been made, maintaining a discreet posture in line with standard incident handling protocols to avoid prejudicing investigative outcomes.
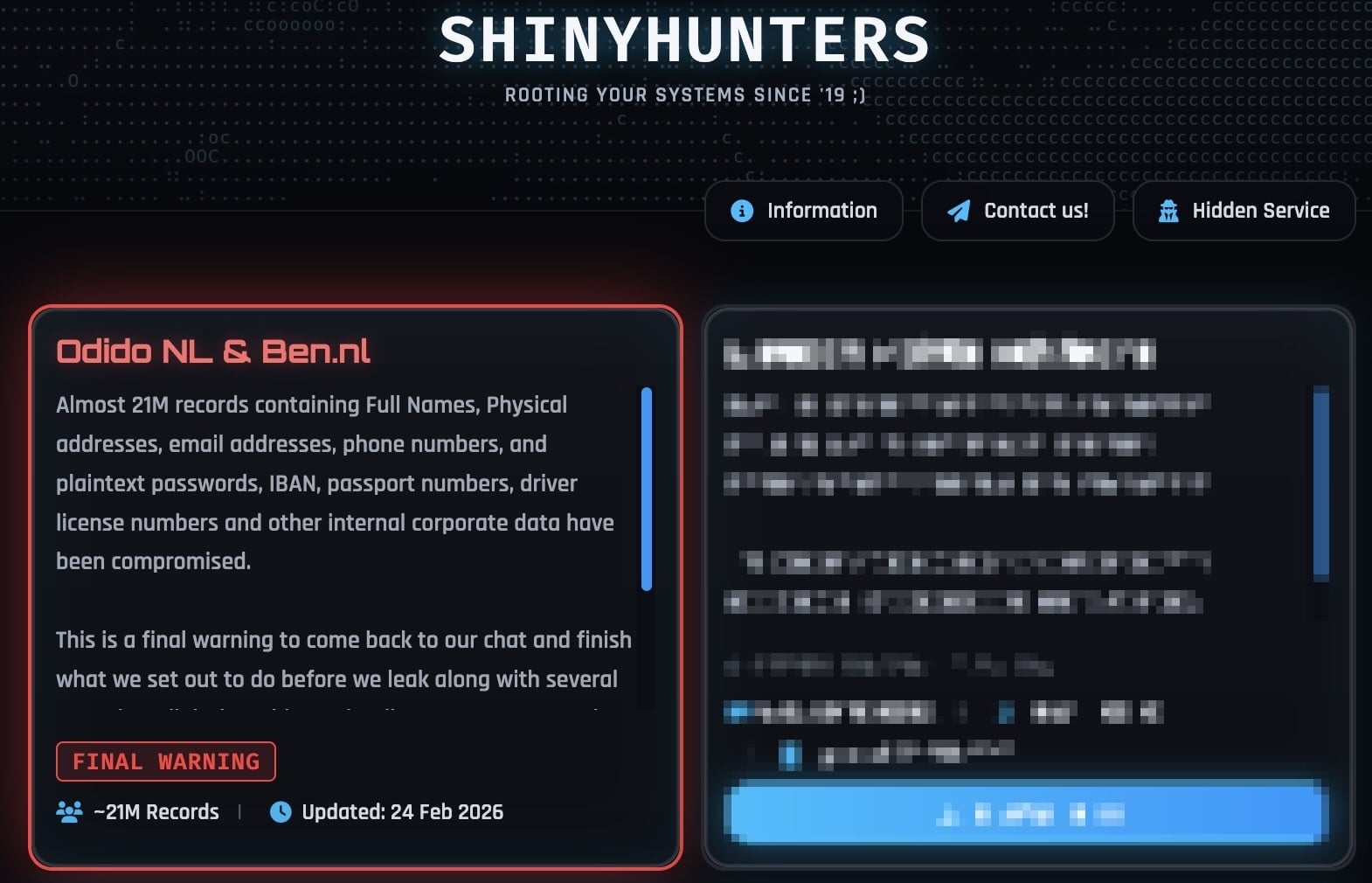
However, the veil of discretion was partially lifted when the ShinyHunters extortion gang officially listed Odido on its dark web leak site. This public claim unequivocally attributed the breach to their operations, with the group asserting that they had stolen an astonishing nearly 21 million records. The data allegedly exfiltrated, according to ShinyHunters, largely mirrors the categories Odido had already acknowledged as exposed, but with a critical and disputed addition: the gang explicitly claimed to possess internal corporate data and, more alarmingly, plaintext passwords. This assertion directly contradicts Odido’s repeated statements that no passwords were compromised. The gang’s message on their leak site served as a stark warning, stating, "This is a final warning to come back to our chat and finish what we set out to do before we leak along with several annoying (digital) problems that’ll come your way. Make the right decision, don’t be the next headline. You know where to find us." This aggressive posturing is characteristic of extortion gangs, designed to exert maximum pressure on victims to comply with their demands.

In response to ShinyHunters’ more expansive claims, an Odido spokesperson firmly reiterated their earlier position, denying the involvement of passwords, call details, social security numbers, or billing data in the breach. This ongoing discrepancy between the attacker’s claims and the victim’s official statements is a common feature in the aftermath of major cyber incidents, often making it challenging for the public and affected parties to ascertain the full extent of the damage with absolute certainty.
The ShinyHunters collective has rapidly emerged as one of the most prolific and audacious cyber extortion groups in the current threat landscape. Their modus operandi frequently involves exploiting vulnerabilities to exfiltrate vast quantities of sensitive data, which they then leverage for extortion, threatening to publicize or sell the stolen information if their demands are not met. In recent weeks alone, the group has taken credit for a series of high-profile security breaches affecting a diverse array of global enterprises. These include the significant compromise of Panera Bread, impacting millions of customer accounts; a data breach at the fintech firm Betterment; the extensive exposure of user data from SoundCloud; the infiltration of luxury outerwear retailer Canada Goose; a controversial breach affecting PornHub, reportedly involving premium member activity data; and a major intrusion into the online dating behemoth Match Group, which oversees popular platforms such as Tinder, Hinge, Meetic, Match.com, and OkCupid.
A recurring theme in ShinyHunters’ successful attacks involves sophisticated social engineering tactics, particularly voice phishing (vishing) campaigns. These attacks often target single sign-on (SSO) accounts, a critical authentication layer for many organizations. The group has been observed exploiting SSO vulnerabilities at major providers like Google, Microsoft, and Okta. Their method typically involves impersonating IT support staff and contacting employees directly. Through manipulative conversations, they trick employees into divulging credentials and multi-factor authentication (MFA) codes on deceptive phishing sites meticulously crafted to mimic legitimate company login portals. This bypasses what many organizations consider a robust security layer, demonstrating the human element remains a significant vulnerability.
Further illustrating their evolving tactical repertoire, ShinyHunters has also adopted device code vishing. This advanced technique exploits the OAuth 2.0 device authorization grant flow, a standard used for devices with limited input capabilities, to illicitly obtain Microsoft Entra authentication tokens. By abusing this legitimate protocol, threat actors can gain persistent access to corporate resources without directly compromising user passwords. Once they successfully steal credentials and authentication codes, the group is adept at hijacking victims’ SSO accounts. This grants them lateral movement capabilities, allowing them to penetrate and exfiltrate data from a wide array of interconnected enterprise services, including Salesforce, Microsoft 365, Google Workspace, SAP, Slack, Adobe, Atlassian, Zendesk, and Dropbox, among many others, thereby maximizing the potential for data exfiltration and subsequent extortion.
Implications and Ramifications of the Odido Breach

The breach at Odido, irrespective of the precise volume and nature of the data confirmed or disputed, carries profound implications for the company, its millions of customers, and the broader cybersecurity landscape.
For Odido, the immediate fallout includes significant reputational damage. The erosion of customer trust can be long-lasting, potentially leading to customer churn and a tarnished brand image in a competitive market. Financially, the company faces substantial costs associated with forensic investigations, system remediation, enhanced security measures, and potential legal fees. More critically, as a Dutch entity operating under GDPR, Odido could face hefty regulatory fines from the Dutch Data Protection Authority if found to have failed in its data protection obligations. These penalties can be substantial, reaching up to 4% of a company’s annual global turnover.
For the 6.2 million (or potentially more) affected customers, the exposure of PII, especially in combination with IBANs, elevates the risk of various malicious activities. This data can be weaponized for highly convincing phishing, smishing (SMS phishing), and vishing campaigns, as well as direct financial fraud, account takeovers, and identity theft. The long-term consequences of such data exposure can be severe, requiring individuals to remain vigilant for years against unsolicited communications and suspicious financial activities. Even if passwords were not directly compromised, the other exposed data provides attackers with valuable intelligence to craft more effective social engineering attacks.
From a broader industry perspective, the Odido incident serves as a stark reminder for other telecommunications providers and large enterprises about the persistent and evolving threat landscape. It underscores the critical necessity for robust, multi-layered cybersecurity defenses that extend beyond perimeter security to encompass employee training, advanced threat detection, and resilient incident response capabilities. The success of ShinyHunters’ vishing and device code vishing attacks highlights that even seemingly secure SSO and MFA implementations can be bypassed by determined and sophisticated adversaries employing social engineering.
The Evolving Cybersecurity Landscape and Future Outlook
The ShinyHunters’ aggressive campaign, culminating in the Odido claim, exemplifies a significant shift in the cybercrime ecosystem. The focus has increasingly moved from traditional ransomware, which encrypts data, to data exfiltration and extortion, where the threat of public exposure or sale of stolen data is the primary leverage. This model is often less detectable in its initial stages and can inflict greater long-term damage due to the irreversible nature of data theft.
To counter these evolving threats, organizations must adopt a proactive and adaptive security posture. This includes:
- Enhanced Employee Security Awareness: Continuous and sophisticated training programs are essential to educate employees about the latest social engineering tactics, including vishing, phishing, and the dangers of device code manipulation. Employees are often the weakest link, and empowering them with knowledge is paramount.
- Advanced Multi-Factor Authentication (MFA): While MFA is crucial, organizations must implement MFA solutions that are resistant to common bypass techniques. Hardware-based security keys (e.g., FIDO2/WebAuthn) offer superior protection against phishing and vishing compared to SMS or app-based OTPs, which can be intercepted or socially engineered.
- Zero-Trust Architectures: Adopting a "never trust, always verify" approach, where every user, device, and application is authenticated and authorized before granting access to resources, regardless of their location, significantly reduces the impact of compromised credentials.
- Robust Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR): These technologies are vital for detecting and responding to anomalous activities on endpoints and across the entire IT environment, enabling rapid identification and containment of breaches.
- Regular Security Audits and Penetration Testing: Continuous assessment of security controls, including red team exercises that simulate real-world attacks, helps identify and remediate vulnerabilities before they can be exploited by malicious actors.
- Comprehensive Incident Response Planning: Organizations must have well-defined, regularly tested incident response plans to ensure a swift, effective, and coordinated reaction to security breaches, minimizing damage and recovery time.
- Supply Chain Security: Given the interconnected nature of modern IT, organizations must extend their security scrutiny to third-party vendors and partners, particularly those with access to sensitive internal systems or customer data.
The regulatory environment, particularly GDPR, will continue to play a critical role in enforcing data protection standards and holding organizations accountable for lapses. Data protection authorities worldwide are increasingly empowered to levy significant fines, compelling companies to prioritize cybersecurity investments.
Ultimately, the Odido breach serves as a powerful testament to the ongoing and intensifying cyber warfare waged against critical infrastructure and personal data. As threat actors like ShinyHunters continue to innovate their attack methodologies, the onus remains on organizations to fortify their defenses, adapt to new threats, and protect the digital sovereignty of their operations and their customers’ invaluable personal information. The fight for digital security is a continuous endeavor, demanding perpetual vigilance, strategic investment, and a collective commitment to resilience in the face of an ever-evolving threat landscape.







