The United States Cybersecurity and Infrastructure Security Agency (CISA) has issued a stern directive, adding two recently addressed Roundcube Webmail vulnerabilities to its Known Exploited Vulnerabilities (KEV) Catalog, signaling their active exploitation by malicious actors and compelling U.S. federal agencies to implement immediate patches within a stringent three-week timeframe. This action underscores the severe and immediate threat posed by these security flaws to governmental and potentially broader organizational networks relying on the widely deployed web-based email client. The designation in the KEV Catalog signifies that these vulnerabilities are not merely theoretical risks but have been observed in real-world attacks, elevating the urgency for their remediation across all affected systems.
Roundcube Webmail holds a significant position within the internet’s infrastructure, serving as a prevalent web-based email client. Its widespread adoption is partly due to its historical role as the default mail interface for the cPanel web hosting control panel since 2008, making it an integral component for countless hosting providers and their clients globally. This deep integration across a vast ecosystem means that vulnerabilities within Roundcube can have far-reaching implications, affecting a diverse array of organizations from small businesses to large enterprises and government entities. The client’s ubiquity transforms any identified security flaw into a potential avenue for widespread compromise, making the current CISA alert a critical warning for a substantial segment of the digital landscape.
The first of the two vulnerabilities highlighted by CISA is a critical remote code execution (RCE) flaw, identified as CVE-2025-49113. This vulnerability was initially patched in June 2025, but its exploitation began almost immediately thereafter. Security watchdog Shadowserver swiftly observed and reported that over 84,000 Roundcube webmail installations remained unpatched and susceptible to attacks just days after the fix was released. Remote Code Execution vulnerabilities are among the most severe categories of security flaws, as they allow an attacker to execute arbitrary code on a vulnerable system. In the context of a webmail server, this could grant an adversary complete control over the server, enabling them to steal sensitive emails, inject malware, pivot to other systems within the network, or even establish persistent backdoors. The rapid transition from patch release to active exploitation underscores the agility and determination of threat actors to capitalize on newly disclosed weaknesses, often scanning the internet for vulnerable systems within hours or days of a patch’s availability.
The second vulnerability, CVE-2025-68461, was addressed by Roundcube two months prior, in December 2025. This flaw is categorized as a cross-site scripting (XSS) vulnerability, specifically exploitable through low-complexity attacks that leverage the animate tag within SVG (Scalable Vector Graphics) documents. XSS vulnerabilities allow attackers to inject malicious client-side scripts into web pages viewed by other users. While XSS might appear less severe than RCE at first glance, its implications can be profound. An attacker exploiting CVE-2025-68461 could potentially hijack user sessions, steal cookies, deface web content, redirect users to malicious sites, or even execute arbitrary actions on behalf of the compromised user within their Roundcube session. The "low-complexity" aspect of this attack vector is particularly concerning, as it implies that successful exploitation requires minimal technical sophistication, making it accessible to a broader range of threat actors. Roundcube’s security team, upon releasing versions 1.6.12 and 1.5.12 to mitigate this issue, issued a strong recommendation for all productive installations of Roundcube 1.6.x and 1.5.x to update immediately, emphasizing the critical nature of the fix.
The active exploitation status of both CVE-2025-49113 and CVE-2025-68461 significantly escalates their threat level. CISA’s decision to include them in its KEV Catalog is not merely an advisory; it is a direct call to action, particularly for Federal Civilian Executive Branch (FCEB) agencies. This catalog lists vulnerabilities that are known to be actively exploited in the wild, representing a clear and present danger to the federal enterprise. The mandate for FCEB agencies to patch these vulnerabilities by March 13 (a three-week deadline from the alert’s issuance around late February 2026) is enforced by Binding Operational Directive (BOD) 22-01, issued in November 2021. BOD 22-01 establishes specific requirements for federal agencies to remediate known exploited vulnerabilities, reinforcing the critical need for a proactive and aggressive approach to cybersecurity within government infrastructure. Non-compliance with such a directive can lead to severe operational disruptions, data breaches, and compromise of sensitive government information.
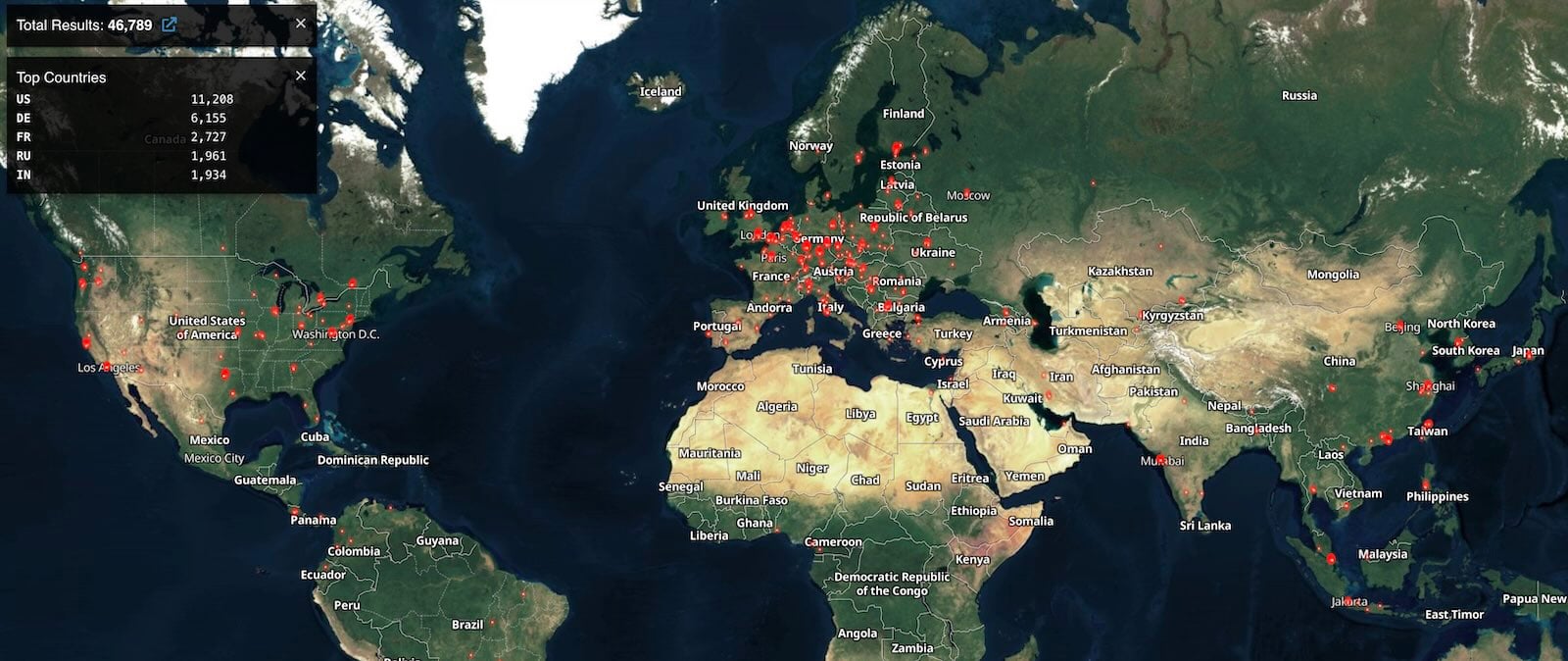
The scale of potential exposure for these vulnerabilities remains a significant concern. While the internet scanning service Shodan currently identifies over 46,000 Roundcube instances accessible on the public internet, the exact number of these installations vulnerable to CVE-2025-49113 or CVE-2025-68461 remains undetermined. This lack of precise vulnerability telemetry poses a challenge for comprehensive risk assessment and targeted mitigation efforts. The discrepancy between the number of known vulnerable instances (84,000 reported by Shadowserver for CVE-2025-49113) and the currently accessible instances (46,000 by Shodan) highlights the dynamic nature of internet-facing services and the continuous need for monitoring and patching. Even a subset of these instances, if vulnerable and compromised, could lead to a cascading effect of cyber incidents across various sectors.
Beyond these two specific flaws, CISA’s KEV Catalog already tracks ten additional Roundcube Webmail vulnerabilities that have either been actively exploited in the past or continue to be targeted. This historical pattern underscores Roundcube’s consistent attractiveness as a target for a wide array of cyber threat actors, including sophisticated state-sponsored groups and financially motivated cybercriminals. Webmail clients, by their very nature, process and store vast amounts of sensitive communication, making them high-value targets. Compromising a webmail server can provide access to organizational communications, credentials, intellectual property, and often serves as an initial foothold for broader network penetration.

A notable example of such exploitation occurred with a stored cross-site scripting (XSS) vulnerability, CVE-2023-5631. This flaw was leveraged in zero-day attacks by the Russian hacking group Winter Vivern (also known as TA473) to target European government entities, demonstrating the severe impact that even an XSS vulnerability can have when exploited by advanced persistent threat (APT) groups. Furthermore, the notorious Russian APT28 cyber-espionage group also exploited Roundcube vulnerabilities to breach Ukrainian government email systems, illustrating the strategic importance of webmail compromise in geopolitical cyber warfare. These incidents serve as a stark reminder that vulnerabilities in widely used software like Roundcube are actively sought out and weaponized by some of the most capable adversaries in the cyber domain.
The implications of these ongoing threats extend far beyond federal agencies. Private sector organizations, educational institutions, and any entity utilizing Roundcube Webmail are equally, if not more, susceptible to these active exploits. The CISA alert, while directly mandating federal action, serves as an implicit warning to all sectors to review their cybersecurity posture concerning Roundcube installations. Organizations must prioritize immediate patching, implement robust vulnerability management programs, and continuously monitor their systems for signs of compromise. The widespread adoption of cPanel, which historically bundles Roundcube, means that even organizations not directly managing their webmail server may be exposed through their hosting providers. This necessitates clear communication and coordination between hosting clients and providers to ensure timely application of security updates.
From a broader cybersecurity perspective, the persistent targeting of webmail platforms highlights a critical attack surface. Email remains a primary communication channel, making its integrity and confidentiality paramount. Attackers understand that compromising email access can yield credentials, sensitive documents, and insights into organizational operations, facilitating further malicious activities like phishing campaigns, business email compromise (BEC) schemes, and data exfiltration. The "low-complexity" nature of some of these exploits further lowers the barrier to entry for less sophisticated threat actors, expanding the pool of potential attackers.
The future outlook for webmail security demands continuous vigilance and adaptation. Software developers like Roundcube must maintain rigorous security development lifecycles, respond swiftly to reported vulnerabilities, and issue clear, actionable guidance to their user base. Organizations, in turn, must invest in proactive threat intelligence, automated patching solutions, and comprehensive security audits. The role of internet security watchdogs and scanning services like Shadowserver and Shodan will continue to be crucial in identifying exposed and vulnerable systems, providing vital data for defensive strategies. Furthermore, the development of secure alternatives or enhancements to traditional webmail, possibly leveraging stronger authentication methods and end-to-end encryption, may become increasingly important in mitigating future risks.
In conclusion, CISA’s recent action regarding the actively exploited Roundcube vulnerabilities, CVE-2025-49113 and CVE-2025-68461, represents a critical alert for the entire cybersecurity community. The federal mandate for immediate patching underscores the severe and immediate threat these flaws pose. Given Roundcube’s extensive deployment across web hosting environments, the potential for widespread compromise is substantial. Organizations globally must heed this warning, prioritize the remediation of these vulnerabilities, and adopt a more proactive and robust approach to webmail security to safeguard their digital assets against an evolving and persistent threat landscape. The historical context of Roundcube being a favored target for sophisticated state-sponsored groups further amplifies the imperative for immediate and comprehensive defensive measures.







