
Sophisticated commercial surveillance technology, known as Predator spyware, has demonstrated an alarming capability to bypass Apple’s fundamental iOS privacy indicators, allowing it to surreptitiously record and transmit audio and visual feeds from compromised devices without any visible user alerts. This advanced malware, developed by the US-sanctioned Intellexa consortium, leverages previously established kernel-level access to manipulate core system processes, effectively neutralizing the visual cues designed to inform users when their device’s microphone or camera is actively engaged. The revelation underscores the escalating threat posed by state-of-the-art spyware to digital privacy and security, highlighting a critical vulnerability in the perceived transparency of mobile operating systems.
Apple introduced the prominent green and orange dots in iOS 14, displayed on the status bar, as a cornerstone of its privacy architecture. These indicators were engineered to provide clear, real-time alerts: a green dot signifies camera activation, while an orange dot signals microphone use. The intent was to empower users with immediate awareness of sensor activity, thereby safeguarding against unauthorized recording by malicious applications. However, the latest analysis of Predator spyware samples reveals a cunning methodology that subverts this protective mechanism, transforming a supposed transparency feature into a false sense of security for unsuspecting iPhone users.
Intellexa, a firm that has garnered international notoriety and faced sanctions from the United States government for its involvement in the proliferation of surveillance tools, is responsible for the creation and deployment of Predator. This commercial spyware has been implicated in a series of highly targeted attacks, often exploiting zero-day vulnerabilities within Apple’s iOS and Google Chrome, and employing "zero-click" infection vectors that require no user interaction to compromise a device. While the general ability of Predator to suppress recording indicators has been acknowledged within cybersecurity circles, the precise technical mechanics behind this stealth operation remained largely undocumented until recent in-depth research shed light on its sophisticated workings.
Unpacking the Technical Evasion: How Predator Silences Privacy Alerts
Detailed forensic analysis conducted by mobile device management experts has meticulously mapped the intricate process Predator employs to achieve its covert surveillance capabilities. The core of this evasion lies within SpringBoard, the fundamental application responsible for managing the iOS user interface, including the status bar and the display of privacy indicators.
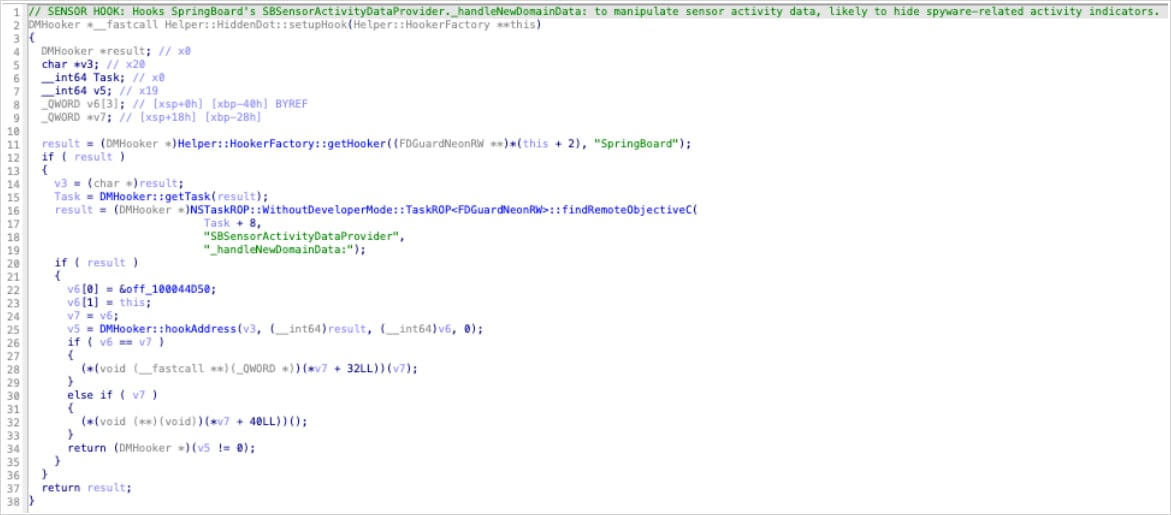
Predator’s strategy hinges on injecting a single, potent hook function, aptly named HiddenDot::setupHook(), directly into SpringBoard. This function is strategically invoked whenever there is a change in sensor activity – specifically, upon the activation of the camera or microphone. By intercepting these critical sensor activity updates at a foundational level, Predator ensures that they never reach the user interface layer, thereby preventing the green or orange privacy dots from illuminating.

The specific target of this hook is a method within SpringBoard known as _handleNewDomainData:. This method is the central conduit through which iOS communicates any changes in sensor status, such as when a camera begins streaming or a microphone starts recording. By establishing an intercept at this crucial juncture, Predator effectively reroutes or neutralizes these communications before they can trigger the visual indicators.
Further technical scrutiny reveals that Predator achieves this by nullifying the SBSensorActivityDataProvider object within SpringBoard. This object is the aggregated source of all sensor activity data within the operating system. In Objective-C, the programming language predominantly used for iOS development, calls made to a null object are silently ignored. Consequently, when Predator nullifies SBSensorActivityDataProvider, SpringBoard ceases to receive and process any information regarding camera or microphone activations. This results in the complete suppression of the corresponding privacy indicators, rendering the device seemingly inactive to the user, even as covert recording is underway.
A significant aspect of this design is its efficiency: because SBSensorActivityDataProvider consolidates all sensor activity, a singular hook is sufficient to disable both camera and microphone indicators simultaneously. Researchers also uncovered remnants of "dead code" within Predator samples, which appeared to be an earlier, abandoned attempt to directly hook SBRecordingIndicatorManager. This suggests a developmental evolution, where the spyware’s architects ultimately opted for the more upstream and comprehensive approach of intercepting sensor data at its source, proving to be a more robust and effective method for stealth.
The module responsible for VoIP (Voice over Internet Protocol) recordings, also supported by Predator, lacks an independent indicator-suppression mechanism. This means it relies entirely on the HiddenDot function for its stealth operations, underscoring the centrality of this single hook to Predator’s overall covert functionality.
Beyond indicator suppression, Predator’s sophisticated architecture extends to its method of gaining camera access. This is achieved through a separate module that employs advanced techniques such as ARM64 instruction pattern matching to locate internal camera functions and Pointer Authentication Code (PAC) redirection to bypass stringent camera permission checks. This multi-layered approach ensures not only stealth but also unauthorized access to sensitive device functionalities.

Profound Implications for Digital Privacy and Trust
The ability of Predator spyware to circumvent iOS privacy indicators carries profound implications for individual privacy, cybersecurity, and the broader trust in mobile device security. For the average user, the absence of these indicators creates a dangerous illusion of security, making it virtually impossible to detect ongoing surveillance activities. This undermines Apple’s efforts to empower users with transparency and control over their data.
For high-value targets – including journalists, human rights activists, political dissidents, and government officials – this capability represents an existential threat. These individuals are often the primary targets of commercial spyware, and the complete invisibility of Predator’s operations could expose them to severe personal and professional risks, compromising sensitive communications, locations, and personal moments. The data collected could be used for blackmail, political coercion, or even physical harm.
The discovery also highlights the persistent regulatory challenges associated with commercial spyware. Despite sanctions against entities like Intellexa, the market for such tools continues to thrive, driven by nation-state clients willing to pay premium prices for advanced surveillance capabilities. The dual-use nature of this technology – ostensibly developed for legitimate law enforcement and national security purposes – often leads to its misuse against civil society, blurring ethical lines and challenging international norms.
Detection Challenges and Mitigation Strategies
Detecting Predator spyware on an infected iOS device, particularly when its operations are designed to be invisible to the user, presents a significant challenge. For the typical iPhone owner, without any visual cues, the presence of such advanced malware would go entirely unnoticed.
However, forensic analysis reveals that while the visual indicators are suppressed, the malicious processes leave behind discernible technical traces. Researchers have identified several tell-tale signs that can be uncovered through in-depth analysis:

- Unexpected Memory Mappings: The presence of unusual or unauthorized memory regions within SpringBoard and mediaserverd (the process responsible for media handling) can indicate the injection of malicious code.
- Exception Ports: Abnormal exception ports within these core system processes can signal that Predator has altered their normal execution flow.
- Breakpoint-Based Hooks: The use of breakpoints as a mechanism for injecting code and intercepting functions, a common technique in advanced malware, can be identified by specialized debugging tools.
- Unusual Audio File Paths: The writing of audio files by mediaserverd to atypical or unauthorized directories could point to covert recording activities.
These indicators are not visible to the casual user and require sophisticated forensic tools and expertise to uncover. This underscores the need for continuous vigilance by security researchers and the development of more advanced detection methodologies.
From a mitigation standpoint, Apple faces the ongoing challenge of fortifying iOS against such sophisticated threats. This involves patching any underlying vulnerabilities that allow for kernel-level access, strengthening sandboxing mechanisms, and re-evaluating the resilience of privacy indicators to direct manipulation. For users, maintaining diligent device hygiene, including promptly installing iOS updates, exercising extreme caution with unsolicited links or messages, and utilizing advanced security features where available, remains paramount, especially for those at higher risk of targeted attacks.
The Broader Landscape of Commercial Spyware and Future Outlook
The Predator spyware incident is a stark reminder of the burgeoning global market for commercial surveillance tools and the relentless "arms race" between platform developers and sophisticated spyware vendors. This ecosystem is characterized by rapid innovation on the part of malware creators, who continuously seek and exploit new vulnerabilities, pushing the boundaries of what is technically possible in covert surveillance.
The proliferation of these tools, often facilitated by opaque business practices and weak regulatory frameworks, poses a significant threat to global human rights and democratic processes. Nation-states, as primary clients, often employ these tools not only for legitimate security purposes but also for political repression, stifling dissent, and monitoring opponents.
Looking ahead, the evolution of spyware is likely to continue unabated. This necessitates a multi-faceted response:
- Enhanced Platform Security: Operating system developers must invest in more robust, potentially hardware-backed, privacy indicators and security architectures that are inherently more resistant to subversion.
- International Regulation: Greater international cooperation and stronger regulatory frameworks are urgently needed to control the development, sale, and transfer of commercial spyware, ensuring accountability for its misuse.
- Transparency and Accountability: Increased transparency from spyware vendors regarding their clientele and the intended use of their tools, alongside greater accountability for governments that misuse such technology, is crucial.
- Independent Research: Continued investment in independent security research is vital to uncover new threats, expose vulnerabilities, and inform defensive strategies.
In conclusion, Predator spyware’s capacity to invisibly hijack iOS recording indicators represents a significant escalation in the capabilities of commercial surveillance tools. It highlights a critical chink in the armor of mobile operating system privacy features and serves as a potent reminder of the persistent and evolving threat posed by advanced malware to the fundamental rights of privacy and security in the digital age. The cat-and-mouse game between defenders and attackers will undoubtedly continue, demanding continuous innovation and vigilance from all stakeholders.








