
A sophisticated and coordinated cyber campaign has emerged, leveraging the allure of new employment opportunities to ensnare software developers, deploying insidious Next.js projects embedded with backdoors designed for remote code execution and comprehensive data exfiltration from compromised development environments. This insidious strategy targets the very heart of the software development lifecycle, aiming to compromise the tools and intellectual property of highly skilled professionals.
The digital landscape is increasingly fraught with advanced persistent threats, and this particular campaign exemplifies a growing trend of attackers focusing on the software supply chain by targeting its most critical human element: the developers themselves. By masquerading as legitimate technical assessments or coding challenges within a seemingly benign job interview process, the perpetrators exploit the inherent trust and collaborative nature of the development community. The chosen vector, Next.js, a widely adopted JavaScript framework for building robust web applications, provides an ideal camouflage, as developers are accustomed to cloning and interacting with new repositories daily.
The Anatomy of Deception: Exploiting Developer Workflows

At the core of this operation lies a meticulously crafted social engineering scheme. Attackers initiate contact with developers, often through professional networking platforms or direct outreach, presenting fictitious job opportunities. Once interest is piqued, the victim is provided with a link to what appears to be a standard coding project or technical assessment. These malicious repositories, identified across platforms like Bitbucket, are engineered to mimic authentic Next.js applications, complete with plausible file structures and seemingly innocuous code.
The critical vector of compromise capitalizes on routine developer workflows. When a targeted developer clones the provided repository and proceeds to set up the project locally – a standard first step for any technical assessment or new project onboarding – they inadvertently trigger the initial stages of the attack. Modern development environments often include automated scripts or pre-configured execution commands within project files (e.g., package.json scripts in Node.js projects) that run upon opening or building an application. The attackers have skillfully weaponized these mechanisms.
Upon the developer’s execution of the project, a hidden malicious JavaScript payload is automatically invoked. This initial script is designed for stealth and persistence. Its primary function is to establish a covert channel, downloading further malicious code – a sophisticated JavaScript backdoor – directly into the system’s memory. Executing in memory, rather than writing to disk, significantly reduces the footprint and makes detection by traditional endpoint security solutions more challenging. This in-memory execution within the context of a running Node.js process grants the attackers remote code execution capabilities, effectively handing over control of the developer’s machine.
Multi-faceted Infiltration: Ensuring Success

To maximize the success rate of their attacks, the threat actors have embedded multiple execution triggers within these malicious repositories. This redundancy ensures that even if one method of activation fails or is detected, other pathways can still lead to compromise. This multi-layered approach underscores the sophistication and persistent intent of the campaign.
The infection process unfolds in two distinct stages:
-
Stage 1 Payload (Host Profiling and C2 Registration): The initial JavaScript payload, once triggered, is not immediately designed for destructive action. Instead, its first task is to meticulously profile the compromised host. This involves gathering a comprehensive inventory of system information, including operating system details, network configurations, installed software, running processes, and potentially even user account details. Following this reconnaissance, the payload establishes a connection with a designated Command-and-Control (C2) endpoint. This C2 server acts as the central nervous system for the operation, allowing the attackers to register the newly compromised machine and initiate periodic polling intervals, awaiting further instructions. The data collected during this profiling phase is invaluable for attackers, enabling them to tailor subsequent attacks or prioritize targets based on the potential value of the compromised environment.
-
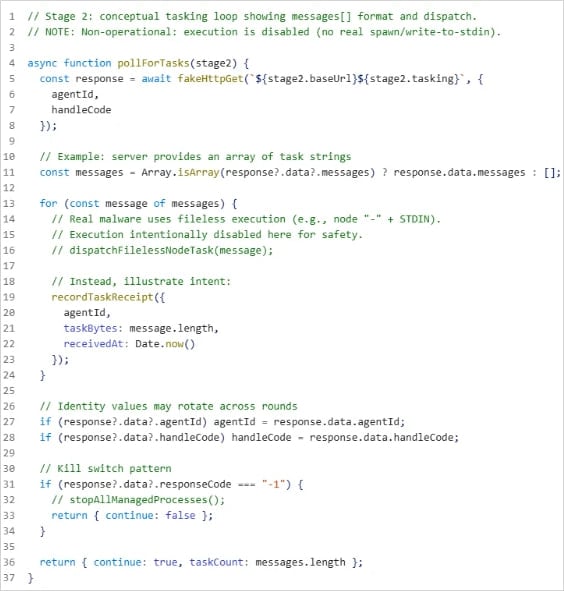
Stage 2 Payload (Tasking Controller and Data Exfiltration): Upon successful registration and profiling, the infection escalates to Stage 2. This involves the deployment of a more advanced tasking controller, which connects to a separate, often more robust, C2 server. This controller is designed to periodically check for specific tasks or commands issued by the attackers. These commands can range from executing arbitrary JavaScript code directly in memory to more elaborate operations. The Stage 2 payload demonstrates advanced capabilities, including comprehensive file enumeration (listing all files and directories on the system), directory browsing, and staged file exfiltration. The ability to execute arbitrary JavaScript in memory allows for dynamic and versatile post-exploitation activities, while staged exfiltration ensures that large volumes of sensitive data can be siphoned off the compromised machine without triggering immediate network anomalies. This could include source code, intellectual property, credentials, API keys, and internal documentation belonging to the developer’s employer.
.jpg)
Microsoft Defender’s analysis revealed consistent patterns across multiple identified repositories, including shared code structures, identical loader logic, and similar naming conventions. These commonalities strongly indicate a coordinated, rather than opportunistic, effort. Such indicators point to a well-organized threat group with specific objectives beyond mere individual machine compromise, suggesting a potential focus on corporate espionage or broader supply chain infiltration.
Broader Implications for the Software Supply Chain
The implications of such a campaign extend far beyond the individual developer. Developers are often privileged users within their organizations, possessing access to critical systems, sensitive repositories, and deployment pipelines. A compromise of a developer’s workstation can serve as a beachhead for a wider attack on an organization’s entire software supply chain.
- Intellectual Property Theft: The most immediate concern is the exfiltration of proprietary source code, design documents, and confidential project plans. This intellectual property is the lifeblood of many companies, and its theft can lead to significant competitive disadvantages and financial losses.
- Supply Chain Contamination: A compromised developer machine could be used to inject malicious code into legitimate software projects, commit tainted code to version control systems, or even sign malicious binaries with legitimate developer credentials. This could lead to a widespread supply chain attack, affecting thousands or millions of end-users who trust the integrity of the software they download.
- Credential Harvesting and Lateral Movement: Developers frequently interact with various internal systems, cloud environments, and third-party services, often caching credentials or having access to sensitive tokens. The attackers could harvest these credentials to gain deeper access into corporate networks, cloud infrastructure, or even other developer accounts, enabling lateral movement and escalating privileges.
- Reputational Damage: For both the targeted individuals and their employers, a security incident of this nature can lead to significant reputational damage, eroding trust among clients, partners, and the broader developer community.
- Economic Espionage: Given the sophisticated nature of the attack and its focus on high-value targets (developers), it is plausible that the campaign is driven by state-sponsored actors or highly organized cybercriminal groups engaged in economic espionage, seeking to gain an unfair advantage in critical technology sectors.
Mitigation and Defensive Strategies: Fortifying the Developer Frontier
Protecting against such sophisticated, human-centric attacks requires a multi-layered approach, encompassing technical controls, robust processes, and continuous developer education. Organizations and individual developers must proactively address the vulnerabilities inherent in modern development workflows.
- Developer Education and Awareness: The first line of defense is an informed developer. Comprehensive training on social engineering tactics, phishing awareness, and the risks associated with unsolicited code or job offers is paramount. Developers must be educated to verify the authenticity of job recruiters and the legitimacy of code repositories through multiple channels before interacting with them.
- Secure Development Environments (SDEs): Organizations should mandate the use of isolated, secure development environments. This can involve virtual machines (VMs) or containerized setups where new, untrusted code can be safely executed and analyzed without posing a risk to the primary workstation or corporate network.
- Strict Code Review and Verification: Even for "interview projects," a skeptical and critical approach is necessary. Organizations should encourage developers to treat all external code with suspicion and subject it to rigorous review, potentially using static application security testing (SAST) tools or manual inspection for suspicious scripts and dependencies.
- Enforcing Integrated Development Environment (IDE) Security Features: Tools like VS Code’s Workspace Trust/Restricted Mode are critical. This feature allows users to declare a workspace as "trusted," granting it full functionality, or "untrusted," which restricts certain capabilities like automatic script execution. Developers should be instructed to operate in Restricted Mode for any new, unverified projects.
- Endpoint Detection and Response (EDR) and Antivirus: Robust EDR solutions and next-generation antivirus software are essential to detect and block malicious payloads, especially those attempting in-memory execution or unusual network communications. These tools can identify anomalous behavior that might indicate a compromise.
- Attack Surface Reduction (ASR) Rules: Implementing ASR rules on developer workstations can prevent common attack techniques, such as preventing executables from running from temporary folders, blocking untrusted processes, or restricting PowerShell scripts. These rules create a more resilient environment against various types of malware.
- Minimizing Secrets and Privileges: Developers should adhere to the principle of least privilege. Secrets (API keys, database credentials, tokens) should be stored in secure vaults or secrets management systems and accessed only when absolutely necessary, using short-lived tokens. Direct storage of sensitive credentials on developer endpoints should be strictly prohibited.
- Identity and Access Management (IAM) with Multi-Factor Authentication (MFA): Strong IAM policies, including mandatory MFA for all corporate systems and development platforms (e.g., Git repositories, cloud consoles), are crucial. Solutions like Microsoft Entra ID Protection can monitor risky sign-ins and unusual user behavior, alerting administrators to potential account compromises.
- Network Segmentation and Monitoring: Isolating developer networks or workstations through segmentation can limit the lateral movement of attackers in case of a breach. Furthermore, continuous network monitoring for suspicious outbound connections or unusual data exfiltration patterns is vital.
- Supply Chain Security Practices: Organizations must adopt comprehensive supply chain security measures, including Software Bill of Materials (SBOMs) to track all components, regular vulnerability scanning of dependencies, and artifact integrity checks to ensure that code has not been tampered with.
The Evolving Threat Landscape
This campaign serves as a stark reminder that cyber adversaries are constantly evolving their tactics, moving beyond purely technical exploits to incorporate sophisticated social engineering. The human element remains the most susceptible link in the security chain, and attackers are increasingly adept at exploiting trust, professional aspirations, and routine workflows.
As the software development ecosystem becomes more interconnected and distributed, the perimeter of security extends to every developer’s workstation. The line between personal and professional computing blurs, especially in remote work environments, creating new attack surfaces. The future will undoubtedly see more such targeted attacks against developers, making their vigilance and organizational security posture paramount in defending the integrity of the global software supply chain. The industry must collectively foster a culture of heightened security awareness and implement robust controls to safeguard against these insidious threats, ensuring that the pursuit of innovation does not inadvertently open the door to compromise.







