
A persistent and highly automated cyber extortion campaign is actively exploiting insecurely configured MongoDB database instances, demanding modest ransoms from organizations to recover compromised data. This recurring threat underscores a critical vulnerability in enterprise data management, as attackers leverage easily discoverable misconfigurations to infiltrate systems, wipe data, and issue standardized ransom notes. Recent investigations confirm that thousands of these vital data repositories remain exposed, with a significant proportion having already fallen victim to these opportunistic attacks, highlighting a widespread and unaddressed security lapse across various sectors.
The current wave of attacks represents a continuation of a long-standing threat pattern targeting publicly accessible and inadequately secured NoSQL databases. Historically, similar campaigns have resulted in the deletion of thousands of databases, sometimes without any financial demand, acting purely as destructive acts. However, the prevailing trend observed by cybersecurity researchers points to a more focused, financially motivated approach, where the primary objective is data extortion. The attackers specifically target "low-hanging fruit"—MongoDB instances configured with default settings or weak access controls that permit unrestricted external connectivity, often without requiring any authentication credentials. This operational efficiency allows a relatively small number of threat actors to compromise a large volume of targets with minimal effort, exploiting a fundamental oversight in database deployment practices.

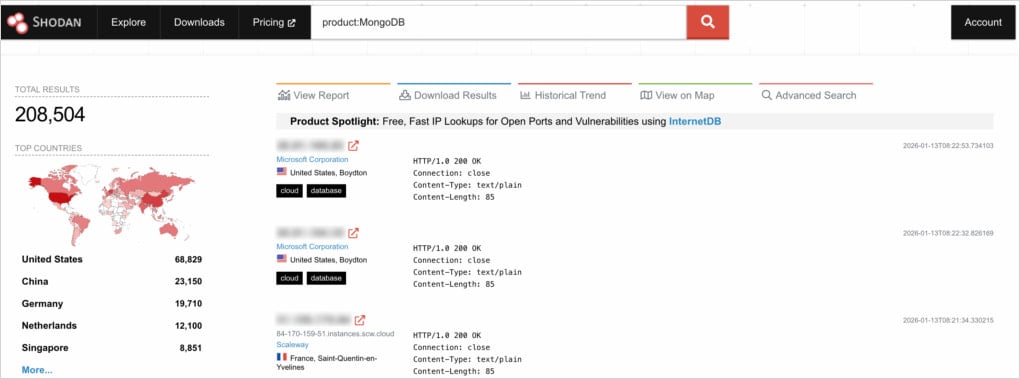
Recent detailed analyses conducted by cybersecurity firms have shed new light on the scale and methodology of these ongoing attacks. Through a comprehensive pentesting exercise, researchers identified over 208,500 publicly exposed MongoDB servers. A concerning subset of these—approximately 100,000—were found to be exposing operational information, indicating live, active deployments rather than test environments. More critically, an alarming 3,100 of these exposed instances could be accessed entirely without authentication, presenting an open invitation for malicious actors. The investigation further revealed that nearly half (45.6%) of these easily accessible, unauthenticated databases had already been compromised, their contents purged and replaced with a ransom demand. This high rate of successful compromise within the most vulnerable segment underscores the aggressive and automated nature of the ongoing campaigns.
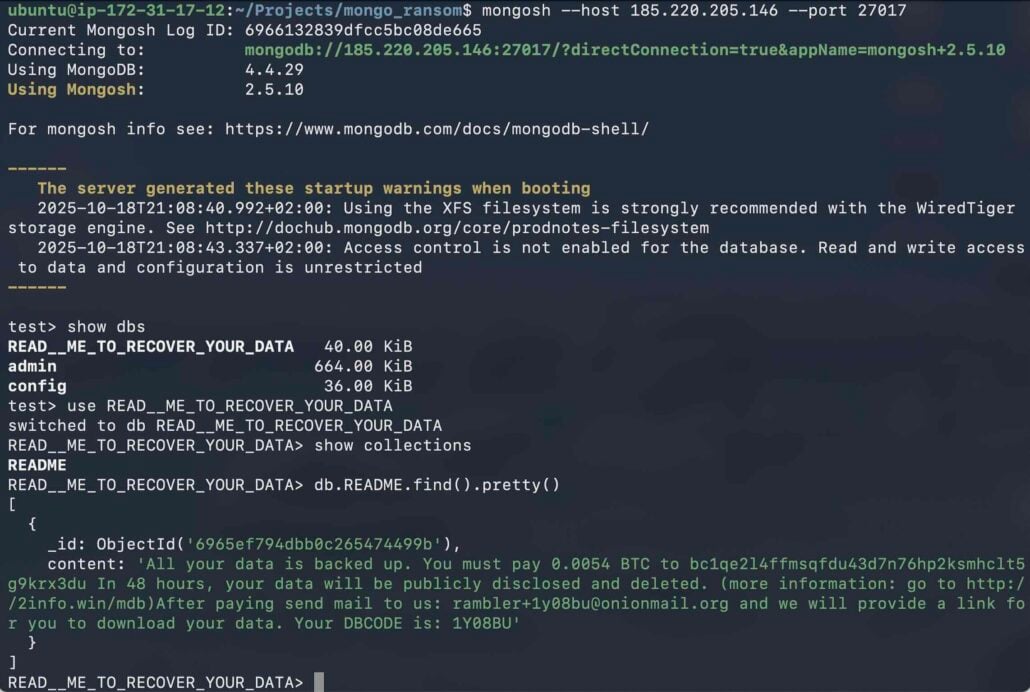
The ransom notes observed across these compromised instances exhibit a striking uniformity, suggesting a centralized, possibly singular, threat operation. Attackers typically demand a payment of 0.005 Bitcoin (BTC), which translates to approximately $500-$600 USD at current exchange rates, to be transferred within a tight 48-hour window. The appeal of such a low ransom figure is a key psychological tactic; it is often perceived by victims as a more manageable cost than the potential expenses and complexities associated with data recovery, forensic investigation, and reputational damage. However, security experts universally caution against paying ransoms, as there is no guarantee that the attackers possess the original data, nor that they will provide a functional recovery mechanism even if payment is made. This inherent lack of trust further complicates the victim’s predicament, as they face the dual risk of financial loss and permanent data irrecoverability.

A deeper forensic examination of the digital footprint left by these attackers revealed a significant operational consolidation. Across all analyzed ransom notes, only five distinct Bitcoin wallet addresses were identified. Remarkably, one particular wallet address was prevalent in approximately 98% of all observed cases. This strong concentration suggests the involvement of a highly organized, likely singular, threat actor or a very tightly coordinated group operating these automated extortion schemes. Such consolidation allows for greater efficiency in managing campaigns, tracking payments, and potentially scaling operations, making the actor a formidable and persistent adversary for organizations with lax security postures.
Intriguingly, the research also posited a hypothesis regarding the remaining exposed instances that had not yet shown signs of compromise despite their vulnerability: they may have already paid a ransom. This theory highlights the opaque nature of the cyber underground and the silent compliance of some victims, who opt to pay rather than report or publicly acknowledge a breach. This silent payment cycle further emboldens attackers, reinforcing the viability of their low-ransom, high-volume model and making it harder for the broader security community to accurately assess the full scope of successful attacks.

Beyond simple misconfiguration, a significant proportion of exposed MongoDB instances are also running outdated software versions, compounding their vulnerability. Nearly 95,000 of the internet-exposed MongoDB servers were found to be operating on older builds, many of which contain known N-day vulnerabilities. While a substantial number of these vulnerabilities might primarily lead to denial-of-service (DoS) attacks rather than direct remote code execution, their presence still poses a severe risk. DoS attacks, even without data exfiltration, can severely disrupt business operations, leading to costly downtime and service unavailability. In an extortion scenario, the threat of a DoS attack can be used as additional leverage, pressuring victims to comply with ransom demands to restore service continuity. The lack of patching on such a large scale points to systemic issues in IT asset management and update hygiene within many organizations.
The implications of these ongoing attacks extend far beyond the immediate financial cost of a ransom. For affected organizations, the potential for significant data loss can be catastrophic, impacting operational continuity, customer trust, and regulatory compliance. Depending on the nature of the lost data, businesses could face substantial fines under data protection regulations such as GDPR, alongside severe reputational damage that can erode market confidence and customer loyalty. The recovery process itself can be arduous and expensive, involving forensic investigations, data restoration from backups (if available and intact), and the implementation of robust new security measures. This underscores the critical need for proactive security measures rather than reactive responses to breaches.
To effectively mitigate these pervasive threats, MongoDB administrators and IT security teams must adopt a multi-layered, rigorous security posture. Foremost, instances should never be exposed to the public internet unless absolutely essential, and even then, access must be tightly restricted. This involves implementing stringent firewall rules, leveraging virtual private networks (VPNs), and configuring Kubernetes network policies to allow only trusted connections from authorized sources. Strong authentication mechanisms, including complex, unique passwords and multi-factor authentication (MFA), are non-negotiable requirements. The principle of least privilege should be enforced, ensuring users and applications only have access to the data and functionalities strictly necessary for their roles.
Furthermore, continuous vigilance and proactive maintenance are paramount. MongoDB instances must be regularly updated to the latest stable versions to patch known vulnerabilities and benefit from enhanced security features. Deployment configurations should be meticulously reviewed, avoiding generic setup guides that often prioritize ease of use over security, and instead adhering to industry best practices and vendor-recommended secure configurations. Automated tools for continuous monitoring of database exposure, configuration drifts, and unauthorized access attempts are indispensable. In the event of a suspected compromise, immediate actions include rotating all credentials, conducting a thorough audit of logs for any anomalous activity, and isolating the affected instance to prevent further spread or damage. Comprehensive data backup and recovery strategies are also fundamental, providing a critical last line of defense against data loss.
Looking ahead, the landscape of automated data extortion is likely to continue evolving. The success of the low-ransom, high-volume model suggests it will remain a prevalent tactic for opportunistic attackers. Organizations must anticipate increasingly sophisticated automated scanning and exploitation techniques. The shift towards cloud-native databases and managed database services offers some relief by offloading security responsibilities to providers, but misconfiguration risks can still persist at the application layer or through inadequate access control settings. Ultimately, the enduring challenge lies in addressing human error and oversight in configuration management. As the digital attack surface expands, robust cybersecurity intelligence, proactive threat hunting, and a culture of continuous security improvement will be essential for organizations to safeguard their critical data assets against these persistent and automated threats. The ongoing MongoDB incidents serve as a stark reminder that fundamental security hygiene remains the cornerstone of defense in an increasingly hostile digital environment.







