A highly sophisticated campaign attributed to state-sponsored North Korean cyber operatives has been meticulously designed to exploit vulnerabilities within the cryptocurrency ecosystem, deploying a novel arsenal of macOS-specific malware through an elaborate blend of artificial intelligence-generated content and intricate social engineering tactics. This ongoing offensive underscores a significant escalation in the digital threat landscape, particularly for entities operating in the decentralized finance and digital asset sectors, signaling a persistent and evolving financial imperative for the aggressors.
The core objective of these operations is unequivocally financial enrichment, aligning with well-documented patterns of state-sponsored cyber activities aimed at circumventing international sanctions and funding illicit programs. Investigations conducted by leading cybersecurity researchers into an incident at a prominent fintech firm have unearthed a multi-pronged attack methodology, revealing the deployment of no fewer than seven distinct macOS malware families. This extensive toolkit highlights a dedicated focus and significant investment in developing specialized capabilities against Apple’s operating system, challenging the conventional perception that macOS environments are less frequently targeted by advanced persistent threat (APT) groups. The identified threat group, designated UNC1069 by intelligence analysts, has been under continuous surveillance since 2018, demonstrating a consistent track record of adaptability and strategic targeting.
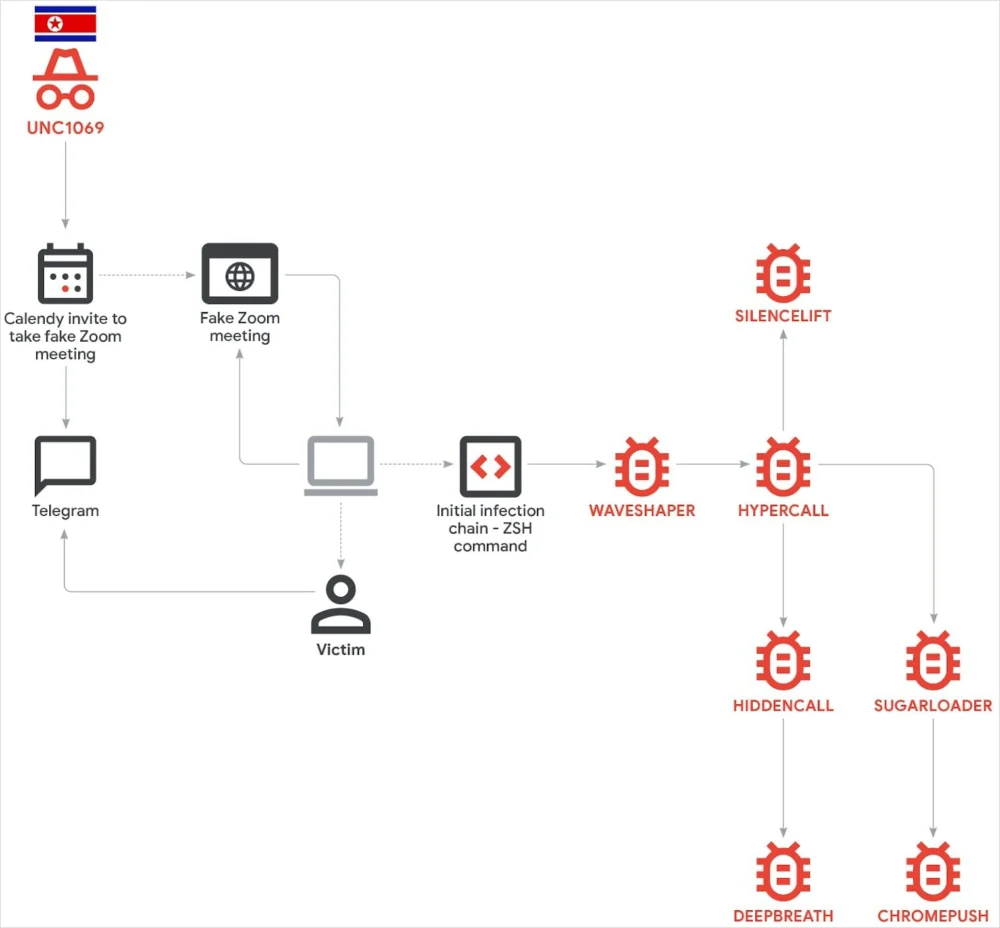
The initial vector of compromise in these attacks is rooted in highly refined social engineering, leveraging human psychology and trust to breach robust digital defenses. Victims are typically engaged via popular messaging platforms such as Telegram, often through accounts previously compromised from high-ranking executives within legitimate cryptocurrency companies. This initial point of contact establishes a false sense of security and legitimacy, allowing the attackers to build rapport over a period, meticulously crafting their narrative. This phase is crucial for softening the target, making them more receptive to subsequent malicious prompts.

Following the establishment of trust, the attackers pivot to a more technical phase, directing victims to a seemingly innocuous Calendly link. This link, however, serves as a sophisticated trap, redirecting users to a meticulously crafted, spoofed Zoom meeting page hosted on the adversary’s infrastructure. This tactic, known as "ClickFix," is designed to exploit the victim’s expectation of a legitimate virtual meeting environment. The sophistication escalates dramatically once the victim "joins" the purported meeting. Here, the attackers employ deepfake technology, presenting an AI-generated video impersonating a CEO from another reputable cryptocurrency firm. This use of synthetic media is a critical innovation, adding an unprecedented layer of authenticity to the deception, making it exceedingly difficult for victims to discern the fraudulent nature of the interaction.
The deepfake video plays a pivotal role in creating a pretext for the subsequent malware delivery. During the fabricated meeting, the deepfake persona feigns experiencing audio difficulties, creating a plausible scenario for technical troubleshooting. Under this guise, the victim is then instructed to resolve these "audio issues" by executing specific commands provided on a web page. This highly deceptive maneuver effectively tricks the victim into initiating the infection chain themselves. The malicious webpage is intelligently designed, presenting commands tailored for both Windows and macOS operating systems, ensuring broad compatibility with potential target environments. This adaptability underscores the threat actor’s preparedness for diverse target infrastructures and their comprehensive understanding of different operating system command-line interfaces. Such a method was previously documented in mid-2025 by other security researchers, attributing a similar modus operandi to the BlueNoroff group—also known as Sapphire Sleet or TA44—another prominent North Korean adversary known for its focus on macOS systems, albeit utilizing a different suite of payloads. This pattern suggests a potential sharing of successful tactics or a common strategic directive among different state-sponsored groups.
Upon successful execution of the provided commands, the infection chain for macOS systems commences with evidence pointing to AppleScript execution. While the exact contents of the initial AppleScript payload could not be fully recovered by researchers, its role is understood to be the precursor to deploying a malicious Mach-O binary. This binary acts as the primary loader or dropper for the subsequent, more specialized malware components. The discovery of seven distinct malware families on a single compromised host is particularly noteworthy. Among these, SUGARLOADER exhibits the highest detection rate on public scanning platforms like VirusTotal, indicating some level of prior exposure or signature development by security vendors. WAVESHAPER follows, but with significantly fewer detections, suggesting a higher degree of stealth or novelty. Alarmingly, the remaining five malware families exhibit no presence in public malware databases, signifying that they represent entirely new tooling for this threat actor.
Specifically, the newly identified families—SILENCELIFT, DEEPBREATH, and CHROMEPUSH—underscore the continuous evolution of UNC1069’s offensive capabilities. The sheer volume and diversity of malware deployed against a single individual are highly unusual and indicative of a maximalist approach. This strategy confirms two primary objectives: aggressive cryptocurrency theft and the exfiltration of extensive victim data to fuel future, even more sophisticated social engineering campaigns. By leveraging a victim’s identity and collected data, the threat actor can establish deeper trust with subsequent targets, making their future attacks even more potent and harder to detect. This multifaceted approach demonstrates a strategic investment in long-term operational capabilities, moving beyond immediate financial gain to building a robust intelligence-gathering apparatus.

Since its initial tracking in 2018, UNC1069 has consistently demonstrated a remarkable ability to adapt and refine its techniques and tools. This adaptability is a hallmark of well-resourced state-sponsored actors. Initially targeting broader financial services, the group shifted its focus in 2023 to the burgeoning Web3 industry, specifically concentrating on centralized exchanges, blockchain developers, and venture capital funds. This strategic pivot reflects the growing liquidity and perceived vulnerability within the decentralized finance space. More recently, the threat actor has expanded its scope to encompass critical infrastructure within the cryptocurrency sector, including payment processors, brokerage services, and digital wallet providers. These targets offer direct access to substantial digital assets and critical operational data, making them prime objectives for financially motivated state-sponsored cyber operations.
The broader context of North Korean state-sponsored cyber activity reveals a consistent and escalating reliance on digital theft as a primary means of revenue generation to circumvent international sanctions. Groups like Lazarus Group, Kimsuky, and BlueNoroff operate under a similar strategic directive, often exhibiting overlapping tactics, techniques, and procedures (TTPs), or even sharing intelligence and resources. The sophistication of these campaigns, particularly the integration of AI-generated content and highly customized malware, highlights a significant investment by the DPRK into its cyber warfare capabilities. This is not merely about opportunistic theft but about systematic, large-scale financial extraction to sustain state operations, including weapons development programs.
In response to such advanced and evolving threats, organizations within the cryptocurrency and fintech sectors must adopt multi-layered and proactive defensive strategies. Robust security awareness training is paramount, focusing on identifying sophisticated social engineering tactics, recognizing deepfake technology, and exercising extreme caution with unsolicited communications or links. Implementing multi-factor authentication (MFA) across all critical systems and accounts is a fundamental defense. Advanced endpoint detection and response (EDR) solutions are crucial for detecting and responding to novel malware families that may evade traditional signature-based antivirus. Comprehensive threat intelligence sharing among industry peers and with government agencies can provide early warnings and insights into emerging TTPs.
Furthermore, a critical reevaluation of macOS security in enterprise environments is necessary. While often perceived as less targeted than Windows, this campaign unequivocally demonstrates the growing focus of APTs on Apple’s ecosystem. Strict application whitelisting, regular security audits, and continuous network monitoring for anomalous behavior are indispensable. Organizations must also cultivate an incident response capability that is prepared to handle highly complex, multi-stage attacks involving advanced social engineering and novel malware. The ability to quickly detect, contain, and eradicate sophisticated threats is crucial in minimizing potential financial and reputational damage.
.jpg)
Looking ahead, the integration of artificial intelligence will only become more pervasive in cyber warfare, with deepfake technology evolving to be even more convincing and personalized. The cat-and-mouse game between threat actors and defenders will intensify, demanding continuous innovation in defensive technologies and strategies. The geopolitical pressures on North Korea, particularly severe international sanctions, will likely drive further aggression in its cyber operations, making the cryptocurrency sector an increasingly attractive target. The challenge for the global cybersecurity community will be to anticipate these evolving threats and foster collaborative defenses to protect critical digital assets and infrastructure from increasingly sophisticated state-sponsored adversaries. The current campaign serves as a stark reminder of the enduring and escalating nature of this digital conflict.