In a pivotal move to bolster cybersecurity across its ecosystem, Microsoft has declared its intention to systematically disable the Network Technology LAN Manager (NTLM) authentication protocol by default in forthcoming Windows releases, signaling a definitive shift away from the three-decade-old mechanism plagued by persistent security vulnerabilities. This strategic decision underscores a broader industry imperative to phase out outdated authentication methods in favor of more robust, modern alternatives capable of withstanding contemporary cyber threats. The NTLM protocol, a relic from the early days of Windows networking, has long served as a critical fallback for authentication within Windows environments, yet its inherent weaknesses have rendered countless organizations susceptible to sophisticated attacks, prompting Microsoft to implement a phased, proactive deprecation strategy.
The NTLM protocol traces its origins back to 1993, making its debut with Windows NT 3.1 as the successor to the earlier LAN Manager (LM) protocol. At its inception, NTLM represented a significant advancement in network authentication for the nascent enterprise computing landscape, providing a challenge-response mechanism to verify user identities without transmitting plaintext passwords across the network. For its time, NTLM facilitated essential network access and resource sharing, becoming a foundational component of Windows domain environments. However, the rapid evolution of computing power and cryptographic analysis techniques soon exposed its limitations. With the advent of Windows 2000, Microsoft introduced Kerberos as the default authentication protocol for domain-connected devices, a protocol designed with superior cryptographic strength and a more secure architecture tailored for distributed environments. Despite Kerberos’s ascendancy, NTLM retained its role as a fallback mechanism, a testament to the challenges of migrating large, complex IT infrastructures away from deeply embedded legacy components. This persistence, driven by compatibility needs and specific operational scenarios where Kerberos might not be available or fully configured, inadvertently maintained a significant attack surface that modern adversaries have extensively exploited.
The primary impetus behind NTLM’s deprecation stems from its fundamental security deficiencies. The protocol relies on weak cryptographic algorithms and hashing schemes that are highly susceptible to various forms of attack. Unlike Kerberos, which utilizes symmetric-key cryptography for robust ticket-based authentication, NTLM’s challenge-response mechanism can be vulnerable to offline brute-force attacks against its hashes, especially if users employ weak passwords. This vulnerability is compounded by the fact that NTLM hashes, which are derived from user passwords, can be intercepted or stolen from system memory, even if the original plaintext password is never directly exposed.

Among the most prevalent and dangerous exploits leveraging NTLM’s weaknesses are NTLM relay attacks. In these sophisticated assaults, threat actors intercept an NTLM authentication attempt and "relay" it to another server, often coercing a compromised network device or service to authenticate against an attacker-controlled machine. The attacker then uses this relayed authentication to gain unauthorized access, escalate privileges, and ultimately achieve complete control over the Windows domain. Over the years, numerous high-profile vulnerabilities, such as PetitPotam, ShadowCoerce, DFSCoerce, and RemotePotato0, have emerged, specifically targeting NTLM relay attack mitigations, allowing attackers to bypass existing security controls and compromise critical systems. These exploits underscore the persistent and evolving threat landscape that NTLM enables, making it a lucrative target for malicious actors seeking to penetrate corporate networks.
Another critical attack vector against NTLM is the "pass-the-hash" attack. In this scenario, cybercriminals exploit system vulnerabilities or deploy malicious software to steal NTLM hashes directly from targeted systems. Once these hashed passwords are acquired, attackers can use them to authenticate as the compromised user without needing the actual plaintext password. This technique allows for rapid lateral movement across the network, enabling attackers to access sensitive data, deploy malware, and establish persistence within an organization’s infrastructure, often remaining undetected for extended periods. The ability to authenticate using stolen hashes bypasses many traditional password-based security measures, highlighting the profound risk posed by NTLM’s continued presence.
Microsoft’s formal announcement, made recently, solidifies its long-term strategy to pivot towards a more secure, passwordless, and phishing-resistant authentication paradigm. The decision to disable NTLM by default in the next major Windows Server release and corresponding Windows client versions marks a monumental shift, reinforcing Kerberos as the primary, secure-by-default authentication protocol. This strategic evolution aligns with modern cybersecurity best practices, including zero-trust principles, which advocate for continuous verification and minimal privilege access. The move is not merely about removing an old protocol but about elevating the foundational security posture of Windows environments globally.
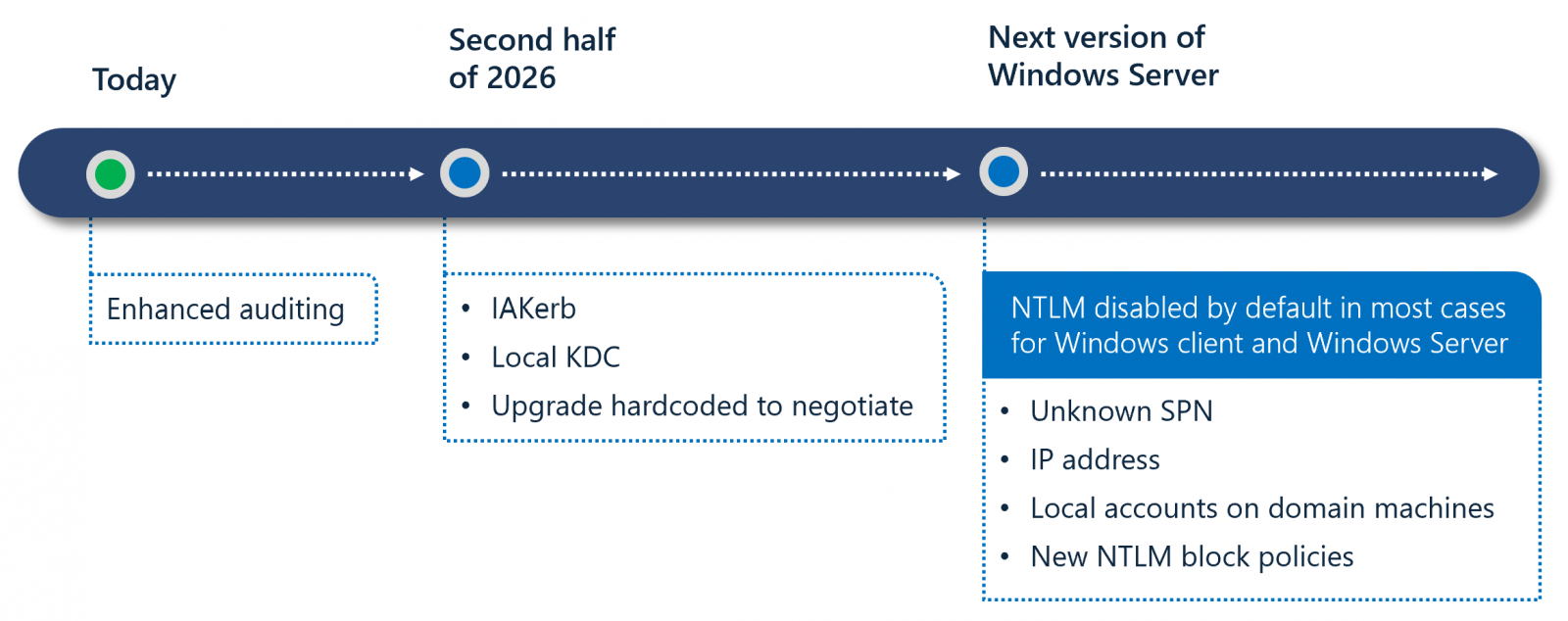
To facilitate a smooth transition and minimize operational disruption, Microsoft has meticulously outlined a comprehensive three-phase plan for NTLM’s retirement. This structured approach acknowledges the deep integration of NTLM within many enterprise environments and aims to provide administrators with the necessary tools and time to adapt.

Phase One, already underway with the availability of Windows 11 24H2 and Windows Server 2025, focuses on enhanced auditing capabilities. This critical initial step empowers IT administrators with advanced tools to meticulously identify where NTLM is still actively being utilized within their networks. Detailed auditing allows organizations to pinpoint legacy applications, devices, or services that rely on NTLM for authentication, providing invaluable data for impact assessment and migration planning. Understanding the extent of NTLM dependency is paramount for developing a robust transition strategy, ensuring that critical business operations remain uninterrupted as the protocol is phased out.
Phase Two, projected for the second half of 2026, will introduce new features designed to address common NTLM fallback scenarios. Key among these innovations are IAKerb and a Local Key Distribution Center (KDC). IAKerb is anticipated to enhance Kerberos functionality, particularly in complex or non-standard environments, potentially improving its reach and reliability where NTLM might previously have been used as a fallback. The introduction of a Local KDC is a significant development, as it aims to provide Kerberos authentication capabilities even in scenarios where direct connectivity to a domain controller’s KDC is intermittent or unavailable. This innovation is crucial for addressing edge cases and specific service accounts that historically relied on NTLM due to network topology or operational constraints, effectively removing the justification for NTLM in many such instances. These enhancements are designed to proactively mitigate the circumstances that currently trigger NTLM’s use, thereby paving the way for its eventual default disablement.
Phase Three, slated for future Windows releases, will witness the default disablement of network NTLM. It is crucial to note that this phase does not signify the complete removal of NTLM from the operating system. Instead, Windows will be delivered in a "secure-by-default" configuration where network NTLM authentication is automatically blocked and no longer utilized by the system. However, Microsoft has included a critical provision: the protocol will remain present within the operating system and can be explicitly re-enabled through policy controls if absolutely necessary. This option serves as a crucial failsafe for organizations that encounter unforeseen compatibility issues with highly specialized or deeply embedded legacy systems, allowing for a controlled, albeit less secure, temporary workaround while more permanent solutions are implemented. The explicit re-enablement mechanism underscores Microsoft’s commitment to providing flexibility while strongly encouraging the adoption of more secure alternatives.
This current initiative is not an abrupt shift but rather the culmination of years of warnings and strategic planning. Microsoft initially announced plans to retire the NTLM authentication protocol in October 2023, concurrently signaling its intent to expand management controls to give administrators greater flexibility in monitoring and restricting NTLM usage. Further solidifying this commitment, Microsoft officially deprecated NTLM authentication on Windows and Windows servers in July 2024, explicitly advising developers to transition their applications to Kerberos or Negotiation authentication to prevent future compatibility and security issues. Indeed, Microsoft’s guidance for developers to cease using NTLM in their applications dates back to 2010. For over a decade, the company has also been advising Windows administrators to either disable NTLM outright or configure their servers to block NTLM relay attacks using robust measures such as Active Directory Certificate Services (AD CS). This long-standing campaign underscores the critical security imperative driving the current deprecation effort.
The implications of this policy change for enterprises are profound and multifaceted. On the positive side, disabling NTLM by default will significantly enhance the overall security posture of Windows environments. It will dramatically reduce the attack surface for a wide array of well-known and persistently exploited vulnerabilities, making it considerably harder for attackers to execute NTLM relay and pass-the-hash attacks. This move aligns Windows authentication with modern security best practices and pushes organizations towards a more robust, future-proof identity management strategy.
However, the transition presents notable challenges. Enterprises, particularly those with complex and heterogeneous IT landscapes, must meticulously identify and address all instances where NTLM is currently in use. Legacy applications, outdated devices, or bespoke services that solely rely on NTLM for authentication will require significant attention. This could involve updating software, reconfiguring services, or, in some cases, replacing older hardware. The migration effort will necessitate thorough planning, extensive testing to ensure business continuity, and potentially a substantial allocation of IT resources. Administrator burden will increase initially as organizations navigate the auditing phase, plan the migration, and implement the necessary changes. Large, distributed enterprises with diverse systems will find this process particularly intricate, requiring a coordinated effort across various IT departments.
To navigate this transition successfully, organizations are strongly advised to leverage the enhanced auditing tools immediately available in Windows 11 24H2 and Windows Server 2025. Proactive identification of NTLM dependencies is the first and most crucial step. Subsequently, prioritizing the migration of identified services and applications to Kerberos or other modern, secure protocols should become a critical security initiative. Developing a comprehensive transition plan, leveraging Microsoft’s new capabilities like IAKerb and Local KDC as they become available, and engaging with software vendors to ensure application compatibility will be essential for a seamless and secure shift away from NTLM.
Looking ahead, Microsoft’s aggressive stance on NTLM deprecation is a clear indicator of the industry’s trajectory towards a truly passwordless and inherently more secure authentication ecosystem. While Kerberos will remain the cornerstone for domain-joined environments, the ongoing innovations in identity and access management, including multi-factor authentication, FIDO2 security keys, and Windows Hello for Business, represent the future of secure authentication. This move by Microsoft is not just about patching a vulnerability; it’s a strategic foundational shift that will significantly uplift the baseline security of Windows, forcing organizations to modernize their authentication practices and ultimately fortifying defenses against an ever-evolving landscape of sophisticated cyber threats. The retirement of NTLM marks a critical milestone in the continuous battle for digital security, ushering in an era of more resilient and robust authentication for the world’s most widely used operating system.