A sophisticated and rapidly evolving Android malware operation has been uncovered, strategically weaponizing the esteemed Hugging Face platform – a cornerstone for artificial intelligence and machine learning development – to disseminate thousands of dynamically generated malicious application variants designed to illicitly acquire sensitive financial and personal credentials from unsuspecting users. This revelation underscores a growing trend where cyber adversaries exploit highly reputable, open-source platforms, traditionally perceived as secure, to host and distribute their illicit payloads, thereby circumventing conventional security defenses and leveraging the inherent trust associated with such digital ecosystems. The campaign represents a significant escalation in the tactics employed by malicious actors, showcasing a calculated effort to blend into legitimate internet traffic and infrastructure.
The Hugging Face platform, renowned globally for its vast repositories of AI models, datasets, and applications, serves as a critical resource for researchers, developers, and organizations engaged in the burgeoning fields of artificial intelligence, natural language processing (NLP), and machine learning (ML). Its architecture, designed for collaborative model sharing and efficient data distribution, includes robust content delivery networks (CDNs) that ensure rapid access to hosted resources. This operational efficiency and widespread adoption make it an attractive, albeit unconventional, target for cybercriminals. Historically, the platform has faced challenges with malicious actors leveraging its infrastructure, including instances where tainted AI models were hosted to backdoor user machines. The latest incident, however, marks a distinct shift in strategy, focusing on direct Android malware distribution rather than compromised AI models themselves.
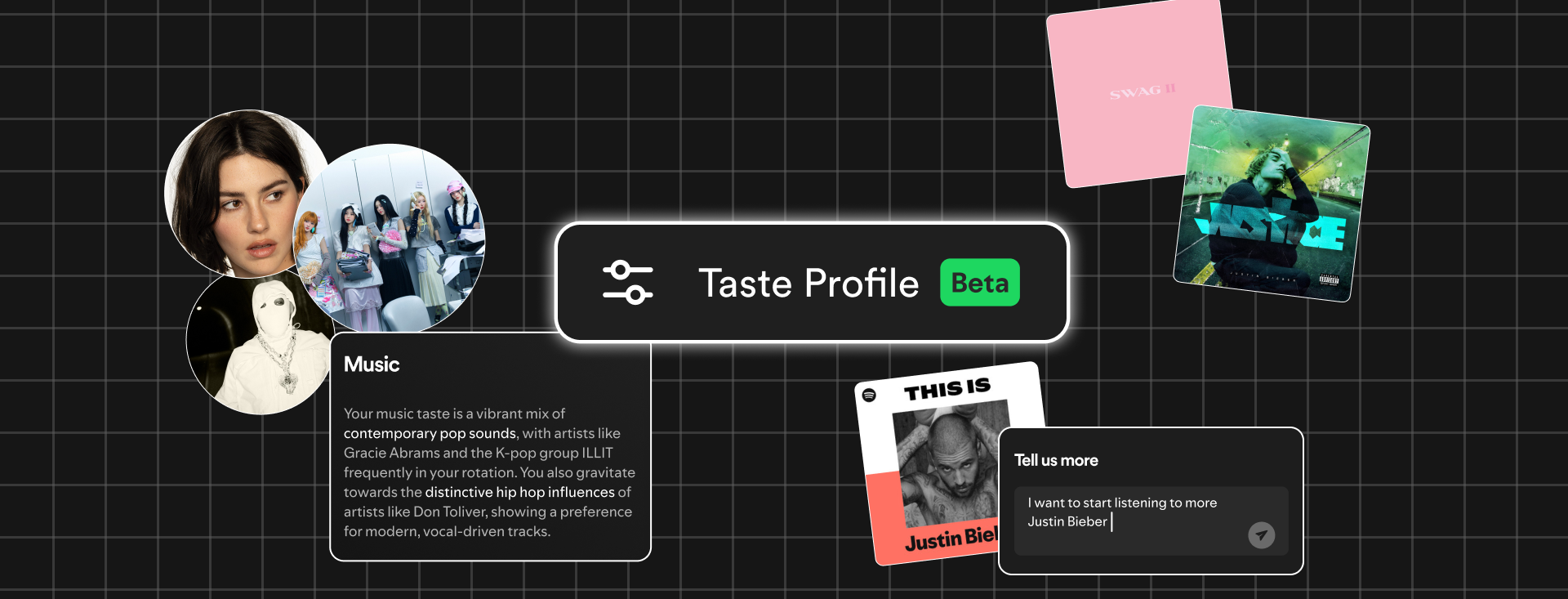
The detailed investigation into this campaign, conducted by leading cybersecurity researchers, illuminates a multi-stage attack methodology engineered for stealth and persistence. The initial phase of the compromise relies heavily on social engineering, luring victims into installing a deceptive application known as "TrustBastion." This dropper app masquerades as a legitimate security utility, employing scareware tactics by displaying alarming messages that falsely claim the target device is infected with various threats, including scams, fraudulent SMS, phishing attempts, and other forms of malware. The psychological manipulation inherent in scareware significantly increases the likelihood of a user installing the fraudulent application, driven by a perceived need for immediate protection.

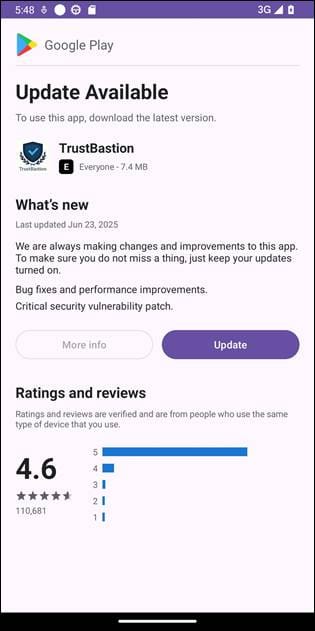
Upon successful installation, "TrustBastion" immediately presents a seemingly mandatory update notification, meticulously crafted to mimic the visual aesthetics and user interface elements of Google Play, Android’s official application store. This critical step in the infection chain is designed to lower the victim’s guard, leveraging the familiarity and trust associated with legitimate software updates. Instead of delivering a benign update, however, this prompt initiates a more nefarious process. The dropper app establishes communication with a command-and-control (C2) server, identified by the domain trustbastion[.]com. This server does not directly host the final malicious payload; rather, it acts as a redirector, providing the dropper with a URL that points to a specific dataset repository on the Hugging Face platform.
This strategic redirection is a cornerstone of the campaign’s evasive capabilities. By hosting the ultimate payload on Hugging Face’s infrastructure and delivering it via its content distribution network, the threat actors effectively bypass many conventional network-level security warnings and blocklists. Traffic originating from Hugging Face is generally considered benign and legitimate, making it less likely to trigger automated security alerts that would typically flag downloads from unknown or suspicious domains. The final malicious Android Package Kit (APK) is thus downloaded directly from a trusted, high-reputation source, adding a layer of legitimacy to the attack that is difficult for both users and some security systems to discern.
A hallmark of this particular campaign is the sophisticated use of server-side polymorphism. To actively evade detection signatures, the threat actors implemented a system that generates new, unique variants of the payload every 15 minutes. This rapid mutation rate ensures that traditional signature-based antivirus solutions struggle to keep pace, as new hashes and code structures are constantly introduced. During the investigative period, the repository was active for approximately 29 days and had amassed over 6,000 commits, underscoring the relentless pace of variant generation. This dynamic approach significantly complicates static analysis and allows the malware to maintain a high degree of stealth, increasing its chances of successful deployment and operation across a wider range of devices.

The resilience of the threat actors was further demonstrated when the initial payload-serving repository was identified and subsequently taken down. Rather than abandoning the operation, the attackers swiftly resurfaced under a new alias, "Premium Club," adopting new visual icons and branding elements while retaining the identical, malicious underlying code. This rapid re-establishment of operations highlights the adaptive nature and determination of the perpetrators, indicating a well-resourced and persistent threat group capable of quickly circumventing defensive measures. Such adaptability poses a continuous challenge for cybersecurity professionals tasked with neutralizing these threats.
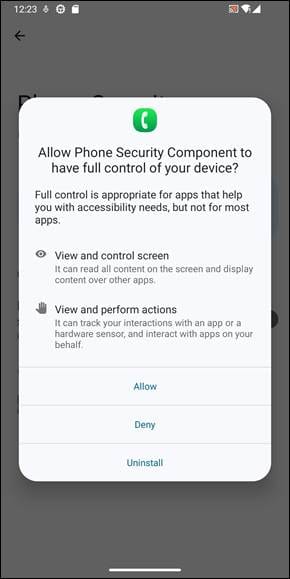
The core malicious component, a sophisticated remote access tool (RAT) lacking a specific public designation, exhibits aggressive exploitation of Android’s Accessibility Services. This critical Android feature, designed to assist users with disabilities by providing enhanced interaction capabilities, is a frequent target for malware due to the extensive privileges it grants. The RAT manipulates users into enabling these services by presenting the request as absolutely "necessary for security reasons," often under the guise of the fake security app. Once granted, the malware gains an alarming array of capabilities, including the ability to serve arbitrary screen overlays, capture the user’s screen content, perform simulated swipes and taps, and even block uninstallation attempts, effectively cementing its presence on the device.
With Accessibility Services compromised, the RAT initiates a comprehensive surveillance and data exfiltration operation. It meticulously monitors user activity, captures screenshots of sensitive interactions, and transmits all collected data to its operators via the persistent C2 connection. Beyond passive data capture, the malware actively engages in credential theft through highly convincing phishing overlays. These overlays impersonate popular financial and payment services, such as Alipay and WeChat, prompting users to enter their login credentials into fake interfaces. The malware also attempts to steal the device’s lock screen code, granting attackers unfettered access to the device itself. The continuous connection to the C2 server not only facilitates data exfiltration and command execution but also allows the operators to push configuration updates and inject fake in-app content into "TrustBastion," further enhancing its illusion of legitimacy.
This campaign presents significant broader implications for digital trust and platform security. The strategic choice of Hugging Face by threat actors underscores a growing concern: the weaponization of legitimate, trusted infrastructure. As AI and ML platforms become more integral to the digital ecosystem, their appeal as distribution channels for malware will likely intensify. This forces platforms like Hugging Face to grapple with the complex challenge of maintaining an open, collaborative environment while simultaneously implementing robust security measures to prevent malicious abuse. The incident highlights the inherent tension between fostering innovation through open access and safeguarding users from sophisticated cyber threats that exploit such openness.
The cybersecurity community’s response to such threats is critical. Following the discovery, researchers promptly informed Hugging Face of the malicious activity, leading to the swift removal of the compromised datasets. Furthermore, a comprehensive set of indicators of compromise (IoCs) related to the dropper application, network infrastructure, and malicious packages was published, enabling other security vendors and organizations to update their detection systems and protect their users. However, the adversary’s rapid adaptation, as seen with the "Premium Club" resurgence, illustrates the ongoing cat-and-mouse game between threat actors and defenders.
For end-users and enterprises, robust mitigation strategies extend beyond basic cyber hygiene. While avoiding third-party app stores and manually reviewing app permissions remain fundamental, a deeper understanding of social engineering tactics and the deceptive use of trusted brands is paramount. Organizations must implement stringent mobile device management (MDM) policies, conduct regular security awareness training, and deploy advanced threat detection solutions capable of behavioral analysis rather than solely relying on signature-based methods. Device manufacturers and operating system developers also bear a responsibility to continuously enhance security features, particularly those susceptible to abuse like Accessibility Services, and to implement faster response mechanisms for identifying and neutralizing malicious applications.
Looking ahead, the threat landscape is poised for continued evolution. The sophistication observed in this campaign, particularly the server-side polymorphism and the rapid adaptation post-takedown, suggests that future Android malware will increasingly leverage similar techniques to evade detection. The integration of AI itself into malware development, potentially enabling more personalized phishing attacks or autonomous payload generation, remains a significant future concern. Therefore, a proactive and collaborative approach involving cybersecurity researchers, platform providers, law enforcement, and end-users is imperative. Enhanced threat intelligence sharing, continuous platform monitoring, and a collective commitment to digital security are essential to mitigate the risks posed by adversaries who continually seek to exploit the fabric of digital trust.