In a significant policy shift that reverberates across the technology sector, the United States government, through the Federal Communications Commission (FCC), has implemented a sweeping ban on the importation of consumer networking devices manufactured outside the nation’s borders. This directive, which echoes a similar prohibition enacted for foreign-made drones, aims to address perceived national security risks and bolster the integrity of U.S. digital infrastructure. While existing devices are permitted to remain in use and products with prior FCC authorization can continue to be imported, the ruling effectively bars the introduction of new foreign-made routers and similar consumer-grade networking hardware into the American market.
The FCC’s decision, formally documented in a recent Public Notice, designates specific categories of consumer networking gear as falling under a "Covered List," thereby prohibiting their radio authorization. This action is underpinned by a National Security Determination that articulates grave concerns regarding the potential for foreign-produced devices to compromise national security and the safety of American citizens. The commission asserts that the dominance of foreign manufacturers in the U.S. consumer router market poses unacceptable economic, national security, and cybersecurity vulnerabilities. The justification further cites the alleged involvement of foreign-made routers in significant cyberattacks, including Volt Typhoon, Flax, and Salt Typhoon, which have targeted critical U.S. infrastructure sectors such as communications, energy, transportation, and water.
This decisive move by the FCC signals a strategic pivot in how the U.S. approaches the supply chain for essential digital infrastructure components. The commission’s stance suggests a belief that reliance on foreign manufacturing for devices as fundamental as consumer routers presents an inherent and unavoidable risk. The rationale posits that the very act of producing these devices abroad creates vulnerabilities that can be exploited by adversarial state actors or malicious entities. The statement, "Given the criticality of routers to the successful functioning of our nation’s economy and defense, the United States can no longer depend on foreign nations for router manufacturing," underscores the gravity with which the FCC views this issue.
The implications of this ban are far-reaching, particularly for the consumer electronics market. The vast majority of consumer routers currently available in the U.S. are manufactured in facilities located outside the United States. Consequently, this ruling will necessitate a significant restructuring of the supply chain for these devices. Router manufacturers that rely on overseas production will face a stark choice: either secure a "conditional approval" from the FCC, a process that likely involves demonstrating a commitment to establishing or expanding domestic manufacturing capabilities, or abandon the U.S. market altogether for future product lines. This mirrors the predicament faced by drone manufacturers, with some opting to withdraw from the U.S. market rather than comply with similar import restrictions.
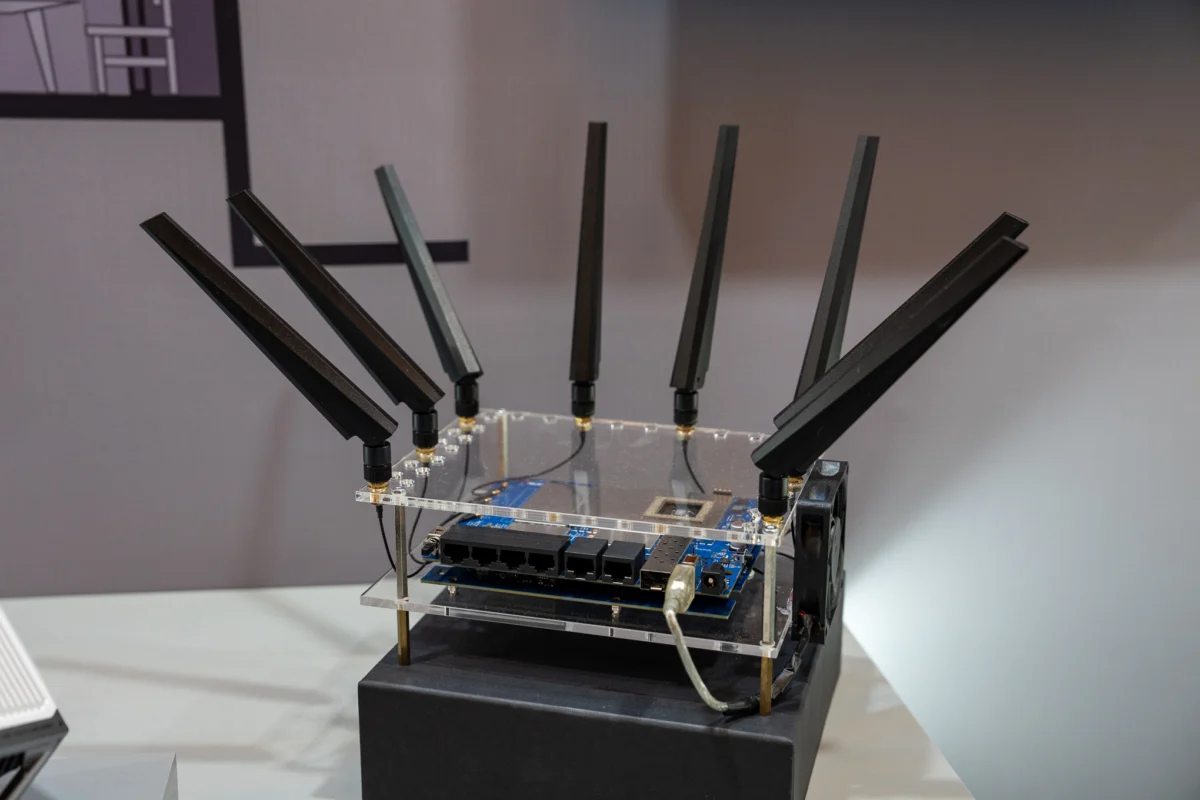
The FCC’s "Covered List" is not a blanket prohibition on all foreign-made routers. Instead, it specifically targets "consumer-grade routers" as defined by NIST Internal Report 8425A. This definition pertains to devices intended for residential use and designed for straightforward installation by the end-user. This targeted approach suggests a focus on the most widely distributed and potentially vulnerable consumer-facing networking equipment, rather than enterprise-level or specialized industrial networking solutions.
Background and Context: A Growing Cybersecurity Landscape
The FCC’s action arrives at a time of heightened awareness and concern regarding cybersecurity threats and the security of the global technology supply chain. Over the years, numerous vulnerabilities have been discovered in consumer routers, making them attractive targets for hackers seeking to build botnets or gain unauthorized access to sensitive data. These devices, often deployed in homes and small businesses, serve as critical gateways to the internet, and their compromise can have cascading effects on individual privacy, network integrity, and even broader infrastructure security.
A notable aspect of this discussion revolves around the market dominance of certain foreign companies. One prominent example is TP-Link, a company with Chinese origins that holds a significant share of the U.S. consumer router market. U.S. authorities have previously explored the possibility of banning TP-Link products, citing national security concerns stemming from its market position and its historical ties to China. In response to these pressures, TP-Link has undertaken efforts to rebrand and restructure its operations, including splitting from its Chinese parent entity, establishing a global headquarters in California, and engaging in legal disputes to counter suggestions of Chinese government infiltration. These maneuvers highlight the complex geopolitical considerations interwoven with the global technology trade.
However, a critical point of contention and analysis emerges when examining the direct link between domestic manufacturing and enhanced security. The very cybersecurity threats the FCC aims to mitigate, such as the Volt Typhoon attacks, have reportedly targeted routers manufactured by U.S. companies like Cisco and Netgear. The Department of Justice has indicated that these attacks primarily exploited vulnerabilities in older, discontinued models for which U.S. manufacturers had ceased providing security updates. This suggests that the issue of router security may be more closely tied to software maintenance, product lifecycle management, and the responsiveness of manufacturers to emerging threats, rather than solely to the geographic location of their manufacturing facilities.
The effectiveness of mandating domestic production as a primary security measure warrants careful consideration. While it is plausible that greater transparency and control over manufacturing processes could be achieved through domestic operations, the technical vulnerabilities inherent in router firmware and design may persist regardless of where the physical assembly takes place. The argument for domestic production often centers on the ability to audit manufacturing processes, control component sourcing, and ensure a more direct line of accountability. However, sophisticated cyber threats can exploit software flaws, supply chain compromises at the component level (even for domestically assembled devices), or vulnerabilities introduced through third-party software integrations, irrespective of the final assembly location.
Implications for the Industry and Consumers
The immediate impact of the FCC’s ruling will be felt by consumers and the companies that supply them with networking equipment. Consumers may experience a reduction in the variety of router models available and potentially higher prices as manufacturers incur the costs associated with establishing or relocating production to the United States. The transition period could also lead to temporary shortages or disruptions in product availability.
For the technology industry, this represents a significant challenge and opportunity. Companies that have already invested in or are capable of establishing domestic manufacturing facilities may gain a competitive advantage. Conversely, those heavily reliant on overseas production will need to undertake substantial strategic and operational adjustments. This could spur innovation in automated manufacturing processes and advanced robotics within the U.S., potentially creating new jobs and fostering domestic technological expertise.
Furthermore, the ruling could catalyze increased investment in cybersecurity research and development within the U.S. As the government emphasizes domestic control over critical infrastructure, there will likely be a greater demand for secure hardware and software solutions developed and produced within the country. This could lead to new partnerships between government agencies, research institutions, and private sector companies focused on bolstering national cybersecurity resilience.
Future Outlook: A Shifting Global Tech Landscape
The FCC’s ban on foreign-made consumer routers is a bold step with potentially transformative consequences for the global technology supply chain. It signals a growing trend towards technological sovereignty and a more protectionist approach to critical digital infrastructure. This policy aligns with broader geopolitical trends where nations are increasingly scrutinizing their reliance on foreign technology and seeking to secure their domestic capabilities.
The long-term success of this initiative will depend on several factors. Firstly, the ability of U.S. manufacturers to meet the demand for affordable, high-quality routers will be crucial. Secondly, the effectiveness of the FCC’s "conditional approval" process and its ability to genuinely enhance security rather than merely shift production locations will be under constant scrutiny. Finally, the ongoing evolution of cybersecurity threats will necessitate continuous adaptation and innovation, regardless of manufacturing origin.
As the U.S. government prioritizes national security and digital resilience, this policy represents a significant assertion of control over a fundamental component of modern connectivity. The reverberations of this decision will undoubtedly shape the future of the consumer electronics market and the broader landscape of global technology manufacturing for years to come. The focus now shifts to the implementation, adaptation, and long-term efficacy of this ambitious policy.




